FBI identifies Russian intelligence as source of phishing attacks on Signal and WhatsApp users
Published on: 2026-03-20
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: FBI links Signal phishing attacks to Russian intelligence services
1. BLUF (Bottom Line Up Front)
The FBI has attributed recent phishing attacks targeting encrypted messaging app users to Russian intelligence services, affecting thousands of accounts globally. These attacks exploit social engineering to bypass encryption protections. The primary targets include individuals with access to sensitive information. Overall, there is moderate confidence in this assessment due to corroborating advisories from Dutch and French authorities.
2. Competing Hypotheses
- Hypothesis A: Russian intelligence services are directly orchestrating phishing campaigns targeting Signal users to gain access to sensitive communications. This is supported by the FBI’s public attribution and corroborating reports from Dutch and French cybersecurity agencies. However, the specific methods and full extent of Russian involvement remain uncertain.
- Hypothesis B: Independent cybercriminal groups, possibly with indirect Russian state support, are conducting these phishing operations for financial or strategic gain. This hypothesis is less supported due to the lack of direct evidence linking non-state actors to these sophisticated campaigns.
- Assessment: Hypothesis A is currently better supported due to direct attribution by the FBI and consistent patterns observed by multiple national cybersecurity agencies. Indicators that could shift this judgment include evidence of financial motivations or links to non-state actors.
3. Key Assumptions and Red Flags
- Assumptions: Russian intelligence has the capability and intent to conduct such operations; the phishing techniques are sophisticated enough to bypass user awareness; the primary goal is intelligence gathering.
- Information Gaps: Specific technical details of the phishing methods; confirmation of Russian state directives; the full scope of compromised accounts.
- Bias & Deception Risks: Potential for confirmation bias in attributing cyber activities to state actors; risk of misinformation from adversarial sources aiming to obscure true attribution.
4. Implications and Strategic Risks
This development could escalate tensions between Russia and affected Western nations, potentially leading to diplomatic or cyber countermeasures. The ongoing threat to sensitive communications poses significant security risks.
- Political / Geopolitical: Increased strain on diplomatic relations with Russia; potential for retaliatory actions by affected states.
- Security / Counter-Terrorism: Heightened threat environment for individuals with access to classified information; potential exploitation of compromised accounts for further intelligence operations.
- Cyber / Information Space: Increased focus on securing communication platforms; potential for broader cyber campaigns targeting other critical infrastructure.
- Economic / Social: Possible erosion of trust in digital communication platforms; increased demand for enhanced cybersecurity measures.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of phishing activities; issue targeted advisories to potential high-value targets; collaborate with international partners for intelligence sharing.
- Medium-Term Posture (1–12 months): Develop and deploy advanced user authentication methods; strengthen public-private partnerships for cybersecurity resilience; invest in user education on phishing risks.
- Scenario Outlook:
- Best: Successful mitigation and deterrence reduce attack frequency; improved international cooperation.
- Worst: Escalation to broader cyber conflict; significant data breaches affecting national security.
- Most-Likely: Continued targeted phishing with gradual improvements in defense and detection capabilities.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
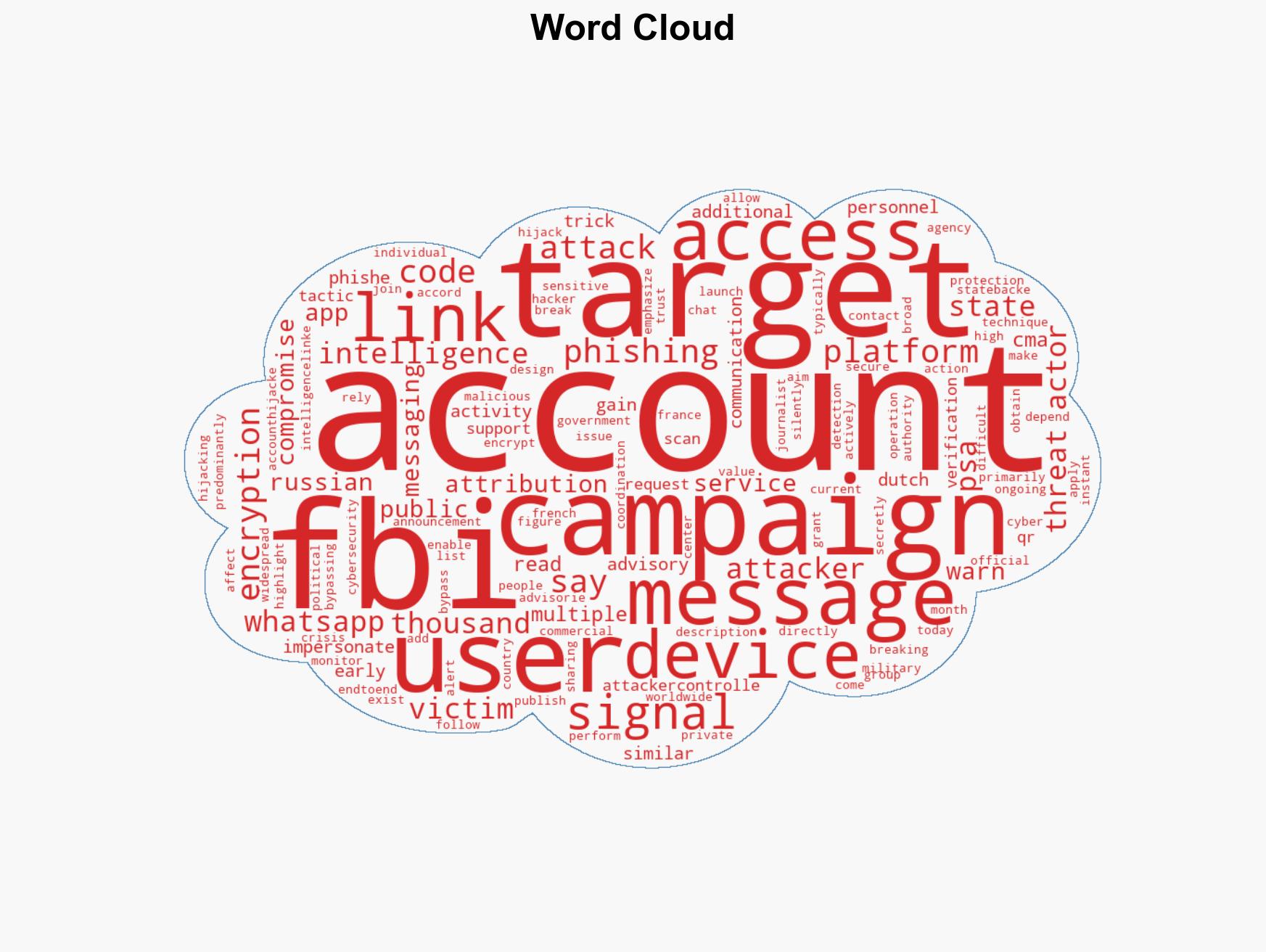
cybersecurity, cyber-espionage, Russian intelligence, phishing attacks, encrypted messaging, national security, information security, international cooperation
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us