FBI Warns: Inexpensive Streaming Devices May Facilitate Hacker Access to Home Networks
Published on: 2026-03-29
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Your Streaming Device Could Be Spying For Hackers According To The FBI
1. BLUF (Bottom Line Up Front)
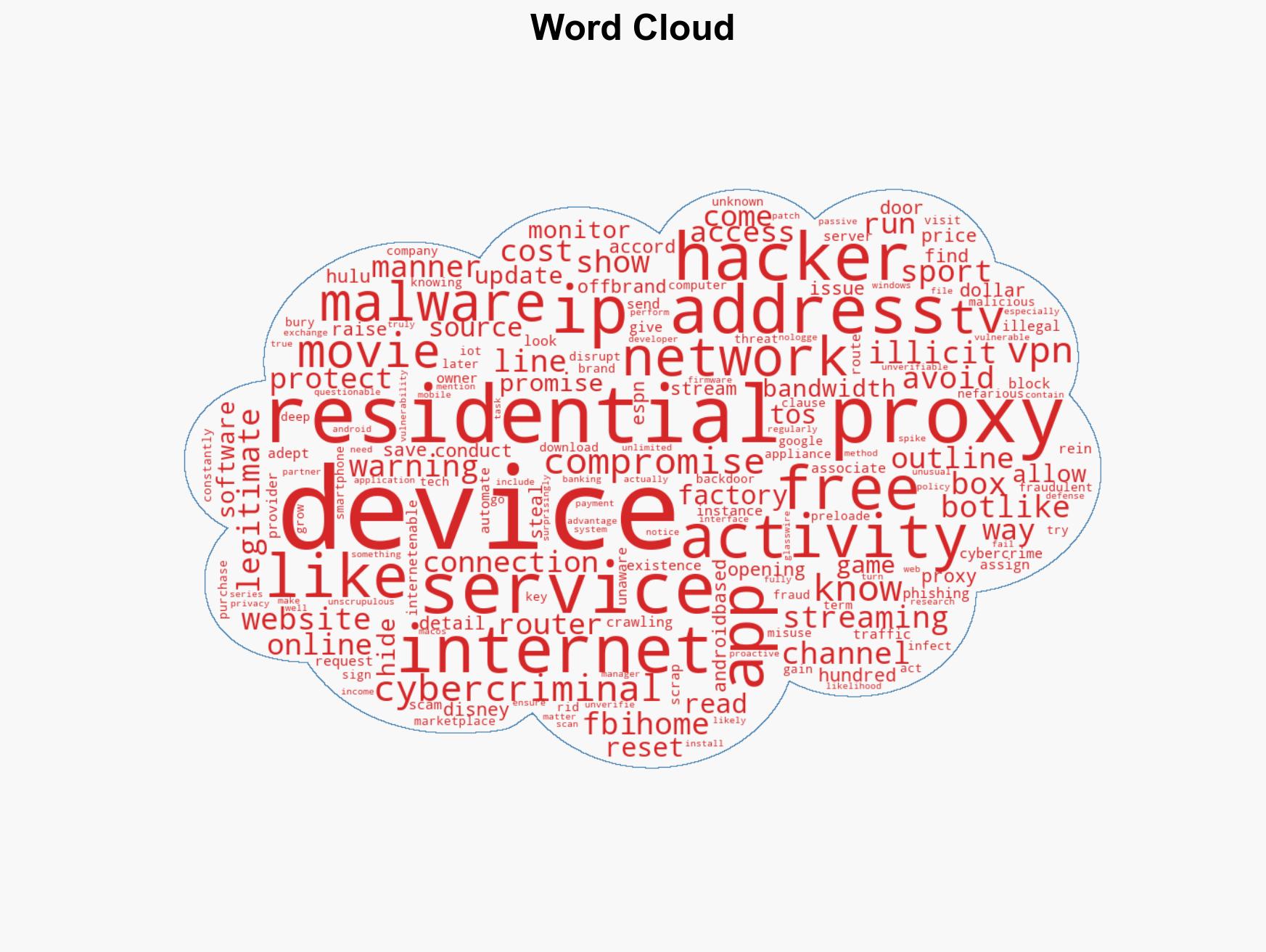
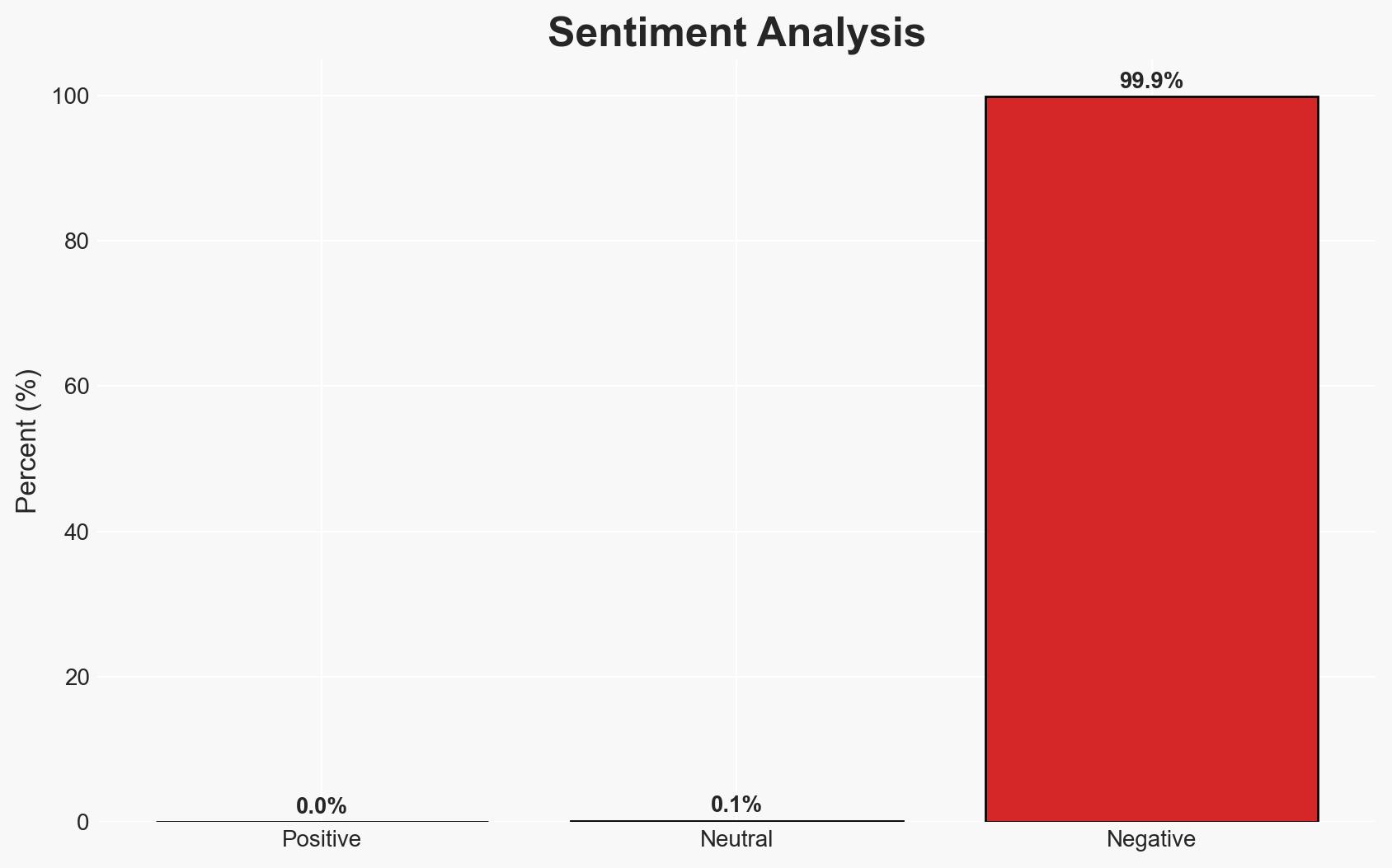
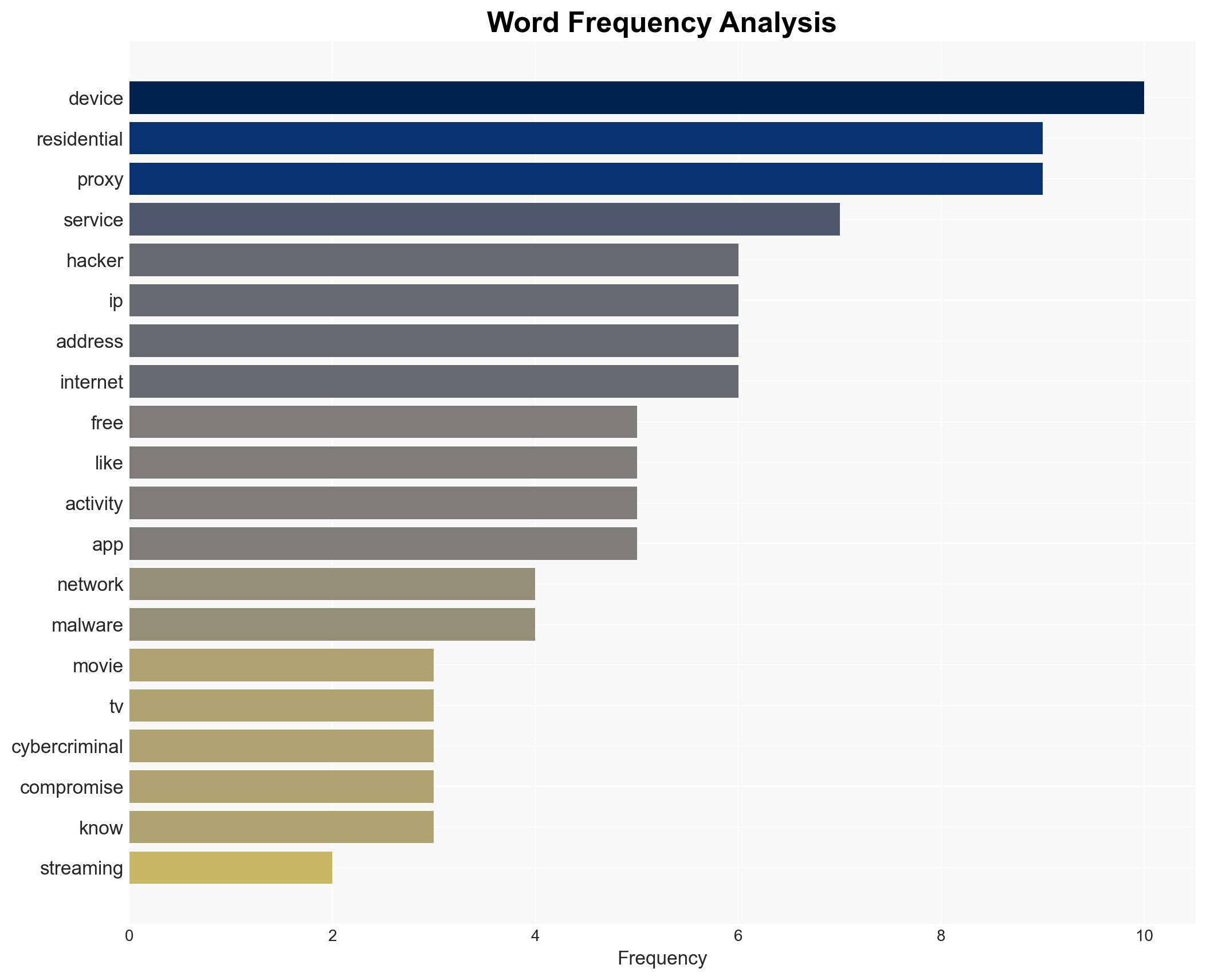
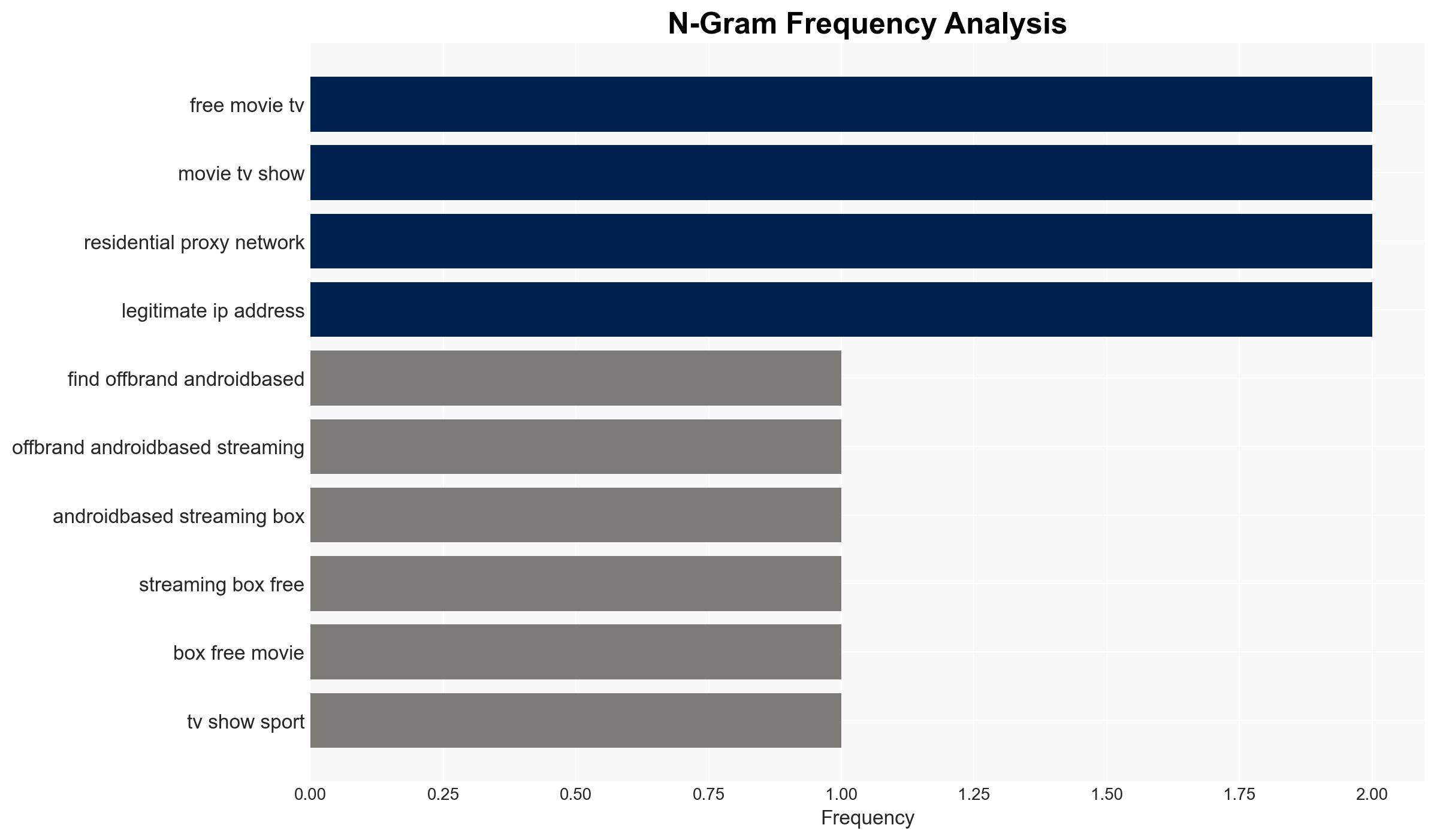
The FBI warns that off-brand streaming devices may be compromised with malware, facilitating their use as residential proxies for cybercriminal activities. This poses significant risks to individual users and broader cybersecurity frameworks. The most likely hypothesis is that these devices are intentionally preloaded with malware to exploit users’ IP addresses, with moderate confidence in this assessment due to the prevalence of such devices and the sophistication of the tactics employed.
2. Competing Hypotheses
- Hypothesis A: Off-brand streaming devices are intentionally preloaded with malware to serve as residential proxies for cybercriminals. Supporting evidence includes the FBI’s warning and the technical feasibility of such operations. However, the scale and coordination of this activity remain uncertain.
- Hypothesis B: The proliferation of compromised devices is primarily due to user negligence and lack of awareness, rather than a coordinated effort by malicious actors. This is supported by the commonality of users not reading terms of service or understanding device security. Contradicting evidence includes the sophistication of the malware and its persistence even after factory resets.
- Assessment: Hypothesis A is currently better supported due to the FBI’s direct warning and the technical details provided about the malware’s capabilities. Indicators that could shift this judgment include evidence of large-scale user negligence or new data on the supply chain of these devices.
3. Key Assumptions and Red Flags
- Assumptions: Users are generally unaware of the security risks posed by off-brand devices; Malware is intentionally preloaded on these devices; Cybercriminals have a vested interest in maintaining residential proxy networks.
- Information Gaps: The specific supply chain and distribution networks for these compromised devices; The extent of user awareness and education on device security.
- Bias & Deception Risks: Potential bias from law enforcement sources emphasizing worst-case scenarios; Deception risks from manufacturers or vendors of these devices downplaying security concerns.
4. Implications and Strategic Risks
The use of compromised streaming devices as residential proxies could significantly impact cybersecurity and privacy landscapes, leading to increased scrutiny and regulation of IoT devices.
- Political / Geopolitical: Potential for increased international tensions if state actors are implicated in the distribution of compromised devices.
- Security / Counter-Terrorism: Enhanced threat environment as residential proxies could be used to mask terrorist communications or operations.
- Cyber / Information Space: Increased efforts by tech companies to detect and disrupt proxy networks; potential for new cybersecurity standards.
- Economic / Social: Consumer distrust in IoT devices could lead to economic impacts on tech manufacturers; increased demand for cybersecurity solutions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase public awareness campaigns on the risks of off-brand devices; enhance monitoring of known compromised device networks.
- Medium-Term Posture (1–12 months): Develop partnerships with tech companies to improve detection of residential proxies; advocate for stronger regulatory measures on IoT device security.
- Scenario Outlook:
- Best: Effective public awareness and regulatory measures significantly reduce the prevalence of compromised devices.
- Worst: Widespread use of compromised devices leads to major cybersecurity breaches and loss of consumer trust.
- Most-Likely: Gradual improvement in device security and user awareness, with ongoing challenges in fully eradicating residential proxy networks.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, residential proxies, IoT security, cybercrime, FBI warning, malware, user awareness
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us