First confirmed drone strike targets commercial data center in UAE, highlighting new risks to global infrastr…
Published on: 2026-03-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
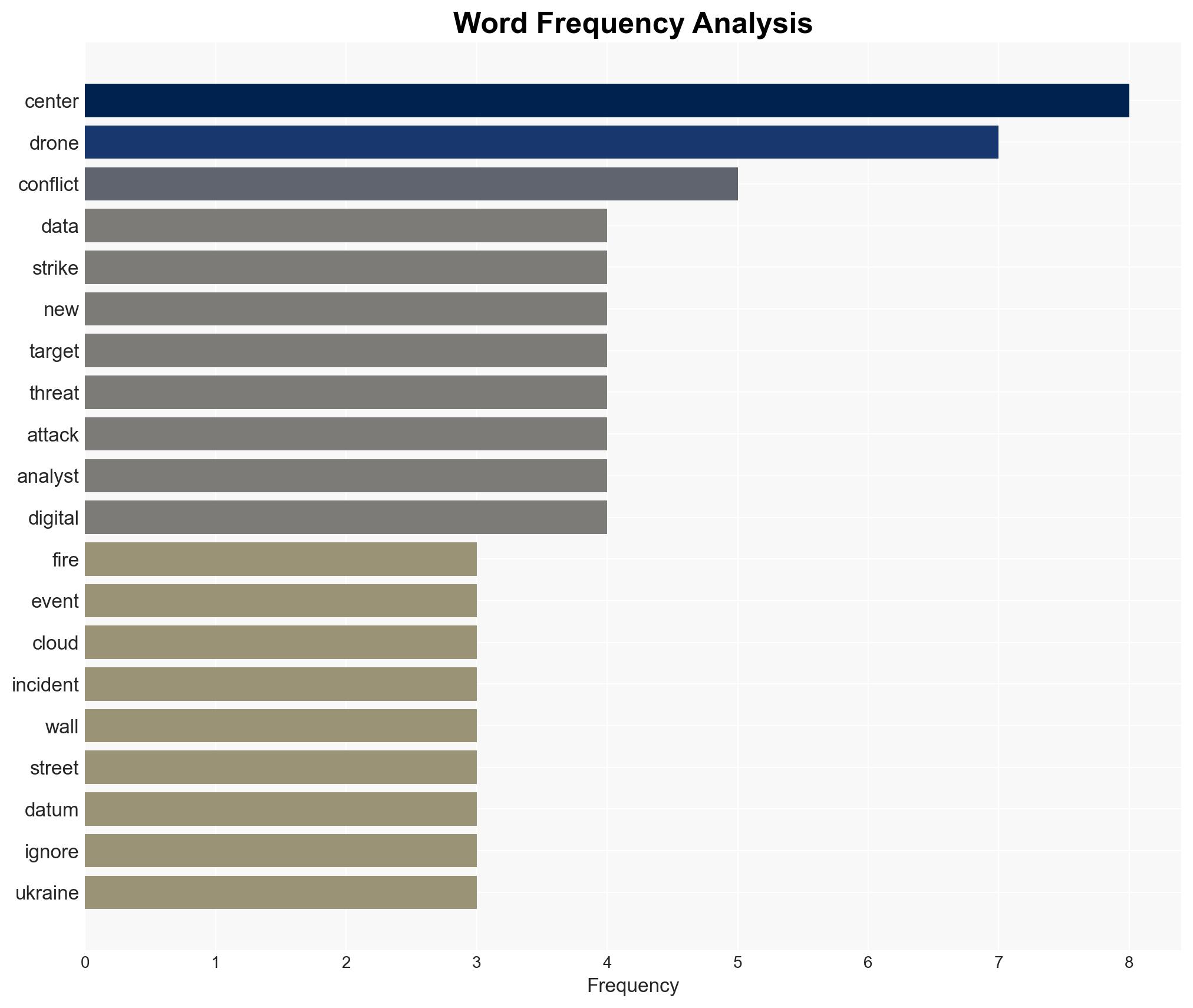
Intelligence Report: The digital battlefield arrives First-ever drone strike on commercial data center occurs in UAE
1. BLUF (Bottom Line Up Front)
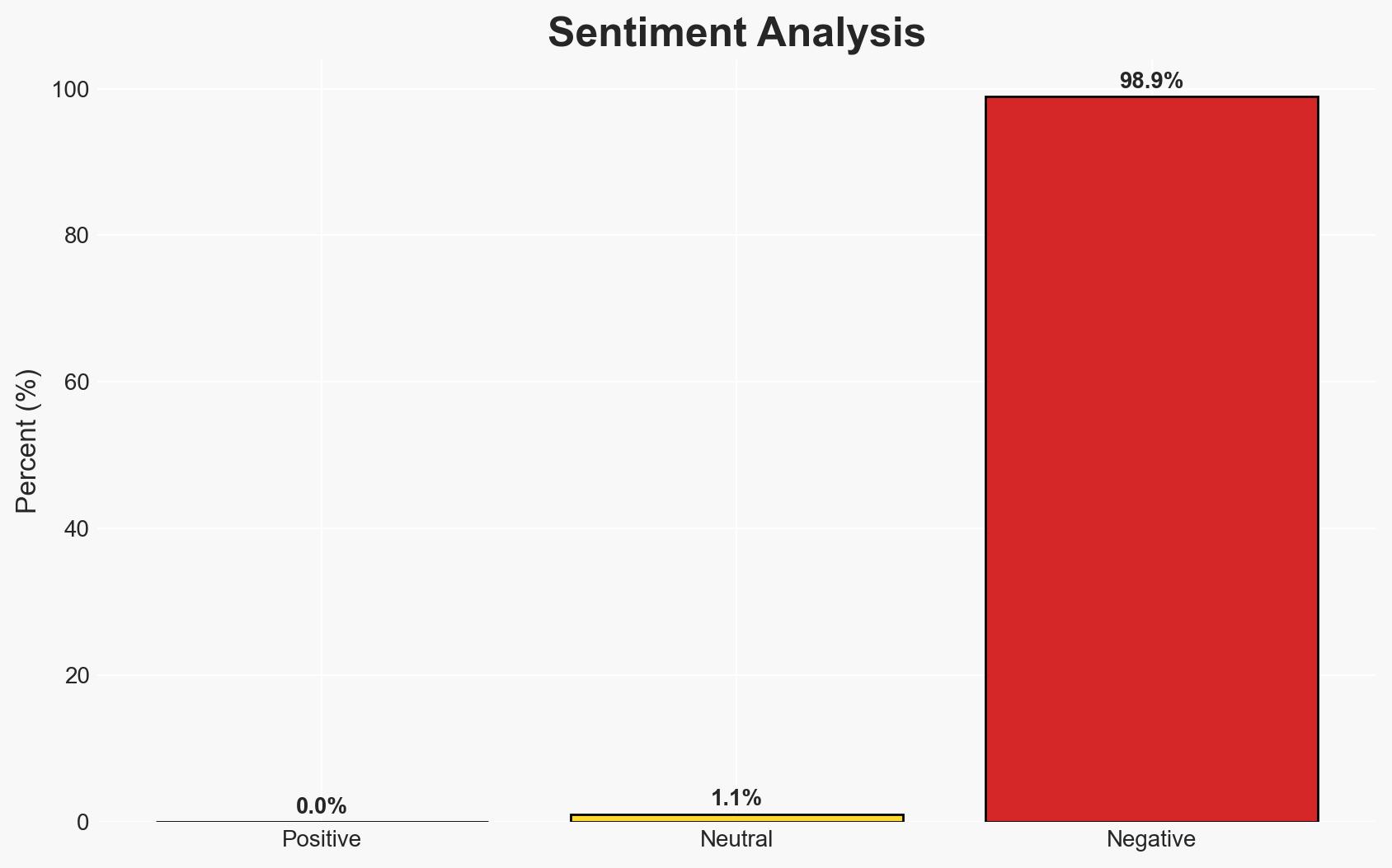
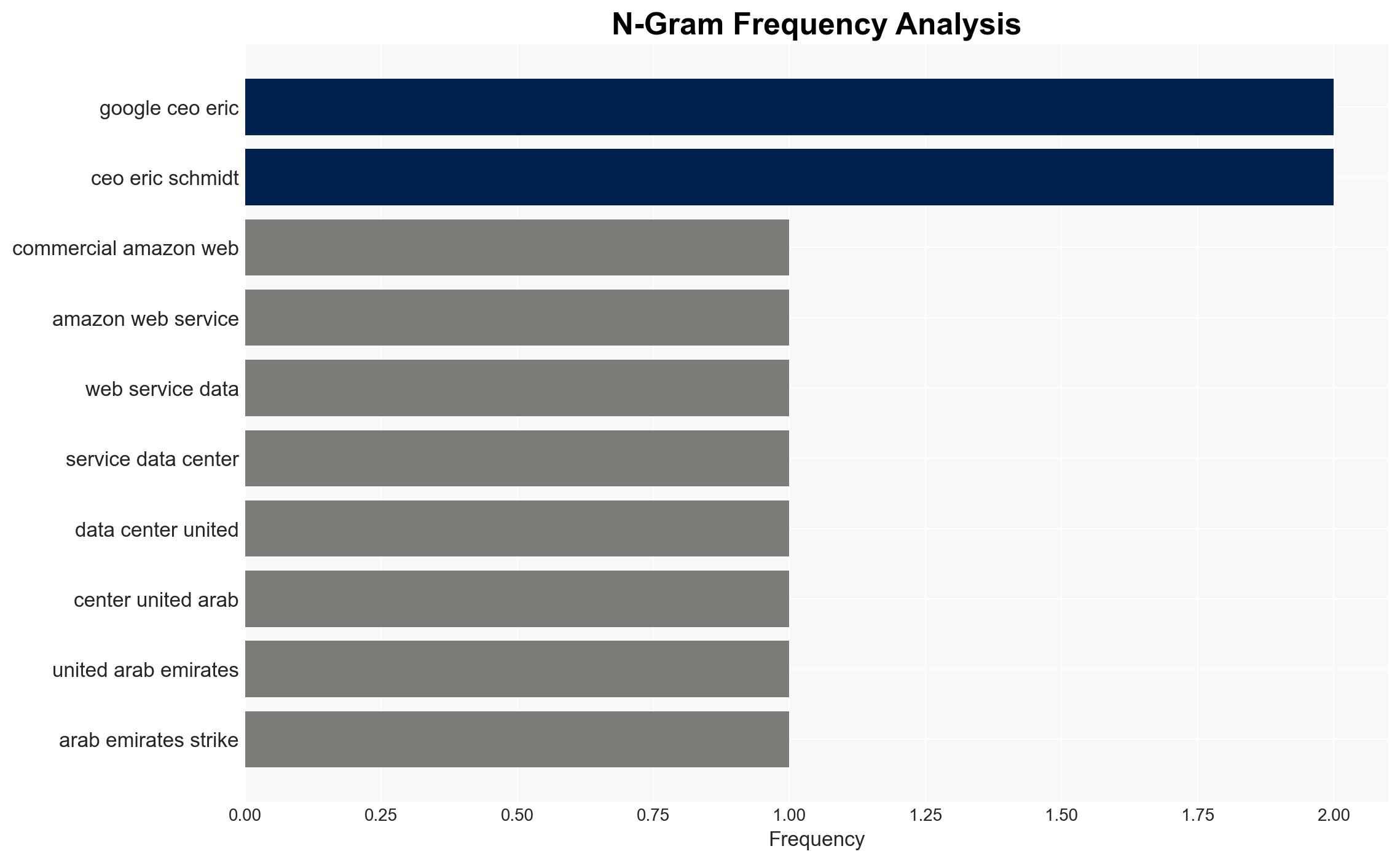
The first-ever drone strike on a commercial data center in the UAE marks a significant escalation in hybrid warfare, targeting critical digital infrastructure. This incident underscores the vulnerability of global cloud services to physical attacks, potentially disrupting economic and communication networks. The most likely hypothesis is that this attack is linked to ongoing regional conflicts involving Iran, with moderate confidence due to the lack of direct attribution.
2. Competing Hypotheses
- Hypothesis A: The drone strike on the AWS data center was a deliberate act by Iranian-aligned forces as part of broader regional hostilities. Supporting evidence includes the timing amidst retaliatory strikes and the use of kamikaze drones, a known tactic in the region. However, uncertainty remains due to the lack of direct claims of responsibility.
- Hypothesis B: The attack was conducted by non-state actors or rogue elements exploiting regional instability to target critical infrastructure for economic disruption. This is supported by the proliferation of cheap, AI-guided drones accessible to various actors. Contradicting this is the absence of any group claiming responsibility, which is atypical for non-state actors seeking recognition.
- Assessment: Hypothesis A is currently better supported due to the geopolitical context and the strategic nature of the target, which aligns with state-level objectives. Key indicators that could shift this judgment include credible claims of responsibility or intelligence linking non-state actors to the attack.
3. Key Assumptions and Red Flags
- Assumptions: The attack was intended to disrupt services rather than cause physical harm; regional tensions are the primary motivator; the use of drones reflects a strategic shift in targeting digital infrastructure.
- Information Gaps: Lack of forensic evidence linking the drones to specific actors; absence of intercepted communications or intelligence confirming intent; unclear extent of damage and service disruption.
- Bias & Deception Risks: Potential bias in attributing the attack to state actors without conclusive evidence; corporate downplaying of the incident may obscure true impact; risk of deception by actors seeking to mislead attribution.
4. Implications and Strategic Risks
This development could lead to increased targeting of digital infrastructure globally, prompting a reassessment of security protocols for data centers. The incident may also exacerbate regional tensions and influence cyber warfare strategies.
- Political / Geopolitical: Potential escalation in regional conflicts; increased pressure on UAE and allies to respond; risk of broader geopolitical instability.
- Security / Counter-Terrorism: Heightened threat environment for critical infrastructure; potential for copycat attacks by other actors.
- Cyber / Information Space: Increased focus on physical security of digital assets; potential for misinformation campaigns exploiting the incident.
- Economic / Social: Disruption to cloud services could impact global businesses; potential investor reevaluation of risks associated with data center investments.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance physical security measures at data centers; increase intelligence sharing among allies; conduct forensic analysis to identify perpetrators.
- Medium-Term Posture (1–12 months): Develop resilience strategies for digital infrastructure; strengthen partnerships with technology firms for threat intelligence; invest in counter-drone technologies.
- Scenario Outlook:
- Best: Improved security measures deter future attacks; diplomatic efforts reduce regional tensions.
- Worst: Escalation leads to more frequent attacks on infrastructure; significant economic and operational disruptions.
- Most-Likely: Continued sporadic attacks with incremental improvements in defensive measures; ongoing geopolitical tensions.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
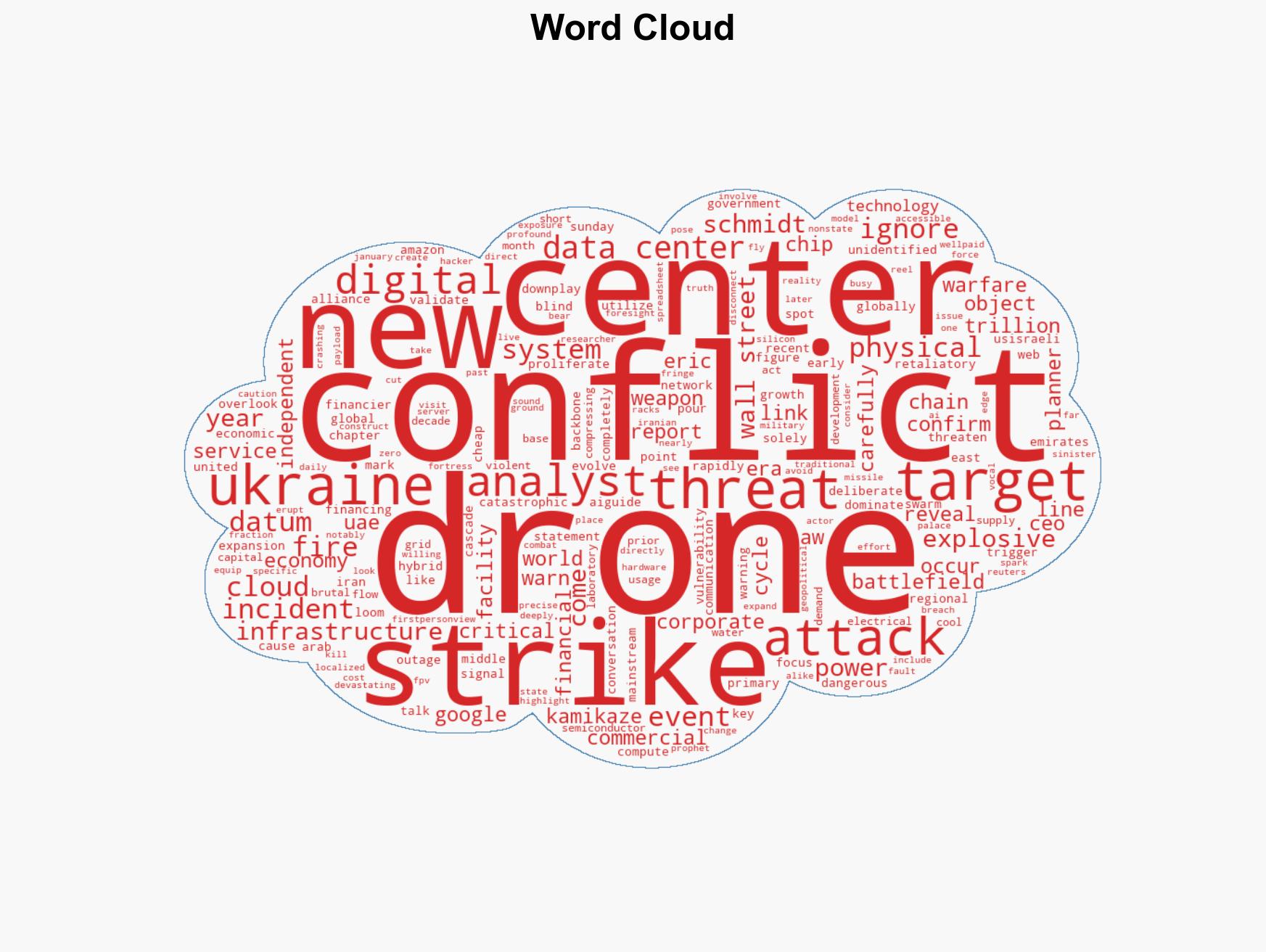
cybersecurity, hybrid warfare, critical infrastructure, drone technology, regional conflict, cyber security, data centers, geopolitical risk
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us