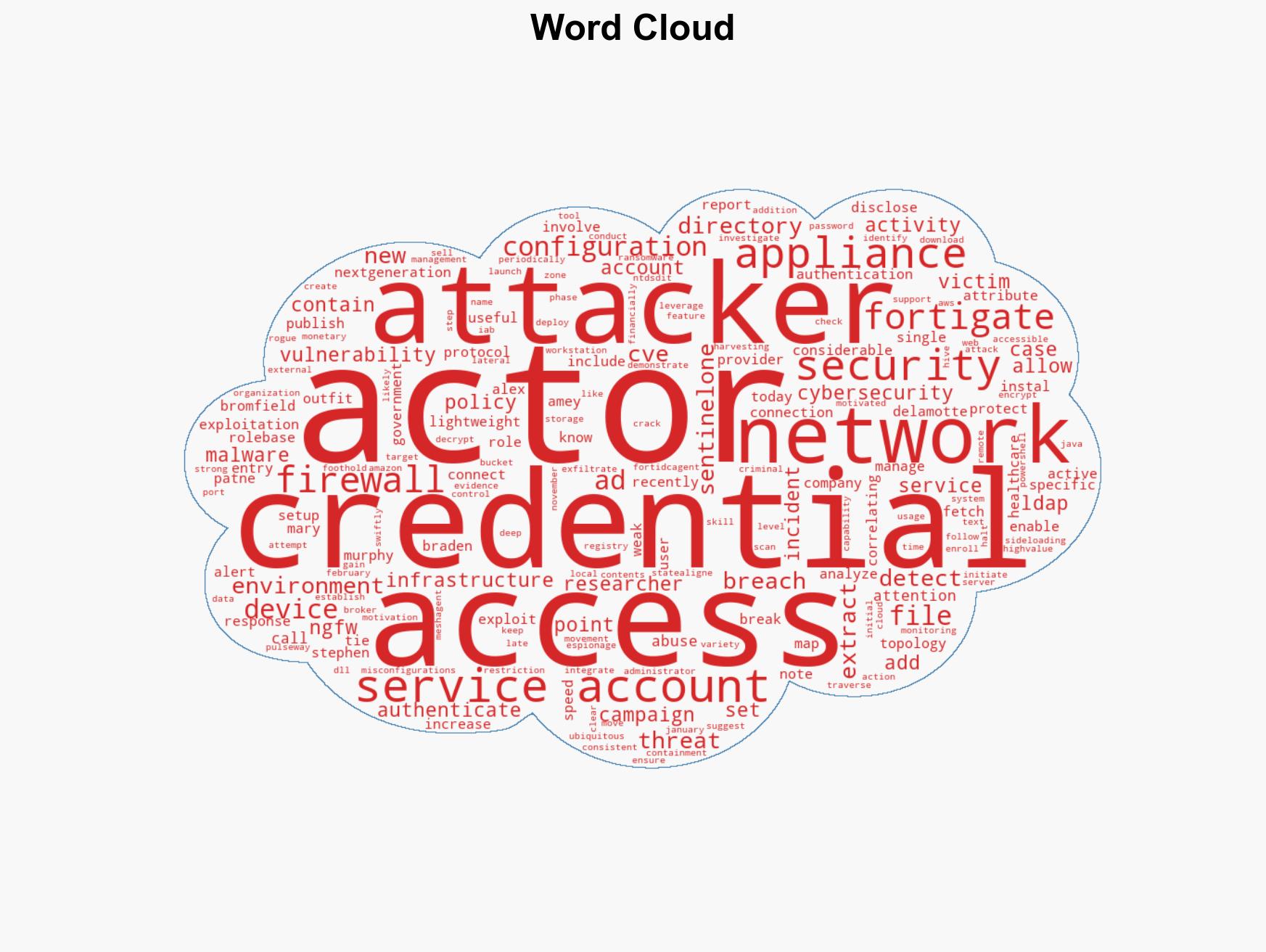
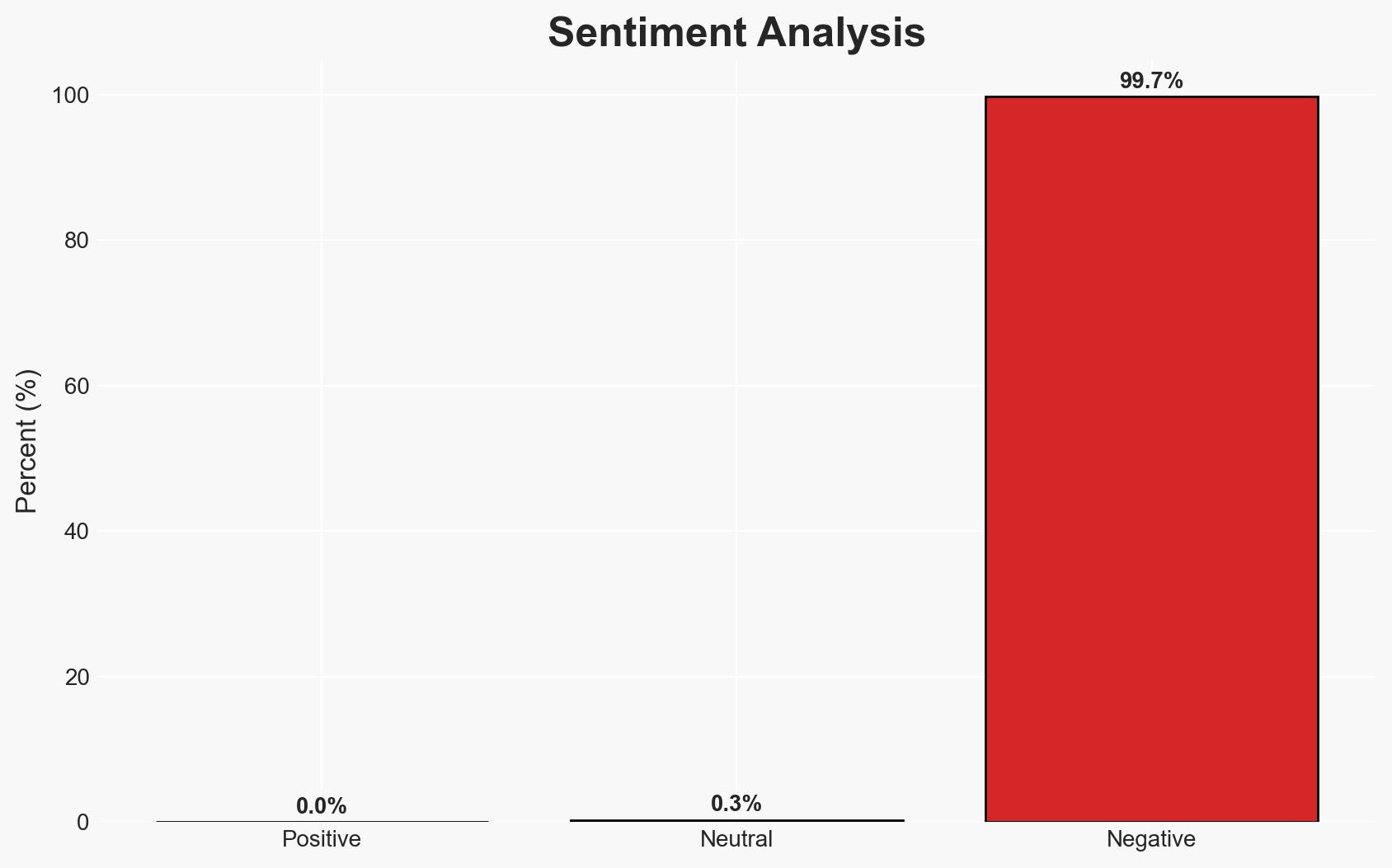
FortiGate Firewalls Targeted in Cyber Attacks to Extract Service Account Credentials and Network Data
Published on: 2026-03-10
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: FortiGate Devices Exploited to Breach Networks and Steal Service Account Credentials
1. BLUF (Bottom Line Up Front)
Threat actors are exploiting FortiGate Next-Generation Firewall vulnerabilities to breach networks and extract sensitive credentials, primarily affecting healthcare, government, and managed service providers. The most likely hypothesis is that these actions are part of a broader campaign by initial access brokers (IABs) to sell network access to other criminal entities. Overall confidence in this assessment is moderate due to limited direct attribution and potential for evolving tactics.
2. Competing Hypotheses
- Hypothesis A: The exploitation of FortiGate devices is primarily conducted by initial access brokers who aim to sell network access to other cybercriminals. This is supported by the creation of unrestricted administrator accounts and periodic checks on device accessibility. Key uncertainties include the full scope of affected entities and the potential involvement of state-sponsored actors.
- Hypothesis B: The breaches are part of a targeted campaign by a specific threat group aiming to extract sensitive information for espionage purposes. While the targeting of healthcare and government sectors supports this, the use of common tools like Pulseway and MeshAgen suggests broader criminal motivations.
- Assessment: Hypothesis A is currently better supported due to the observed behavior consistent with IAB activities, such as creating administrator accounts and selling access. Indicators that could shift this judgment include evidence of data exfiltration for espionage or direct links to state-sponsored entities.
3. Key Assumptions and Red Flags
- Assumptions: FortiGate vulnerabilities are not yet fully patched across all affected networks; threat actors have the capability to decrypt configuration files; the primary motive is financial gain through access sales.
- Information Gaps: Specific identities of the threat actors; the total number of affected organizations; potential state actor involvement.
- Bias & Deception Risks: Potential bias from cybersecurity firms emphasizing the threat to promote their services; deception indicators include false flag operations to misattribute attacks.
4. Implications and Strategic Risks
This development could lead to increased cyber threat activity as access to critical networks is commodified. The exploitation of FortiGate devices may prompt a reevaluation of network security protocols and vendor trust.
- Political / Geopolitical: Potential for diplomatic tensions if state-sponsored involvement is confirmed.
- Security / Counter-Terrorism: Increased risk of cyber-attacks on critical infrastructure, necessitating enhanced defensive measures.
- Cyber / Information Space: Escalation in cybercrime activities and potential for misinformation campaigns leveraging stolen data.
- Economic / Social: Financial losses for affected organizations and potential public trust erosion in digital security solutions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urgently patch known vulnerabilities in FortiGate devices; increase monitoring of network traffic for signs of unauthorized access.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms for threat intelligence sharing; invest in advanced threat detection and response capabilities.
- Scenario Outlook:
- Best: Rapid patching and awareness campaigns mitigate the threat, reducing successful breaches.
- Worst: Continued exploitation leads to significant breaches in critical sectors, with potential geopolitical fallout.
- Most-Likely: Ongoing exploitation with periodic disruptions as organizations gradually improve defenses.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, network breaches, initial access brokers, FortiGate vulnerabilities, healthcare sector, government networks, managed service providers
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us