Fortinet FortiClient EMS vulnerability CVE-2026-21643 actively exploited in the wild, patch recommended.
Published on: 2026-03-30
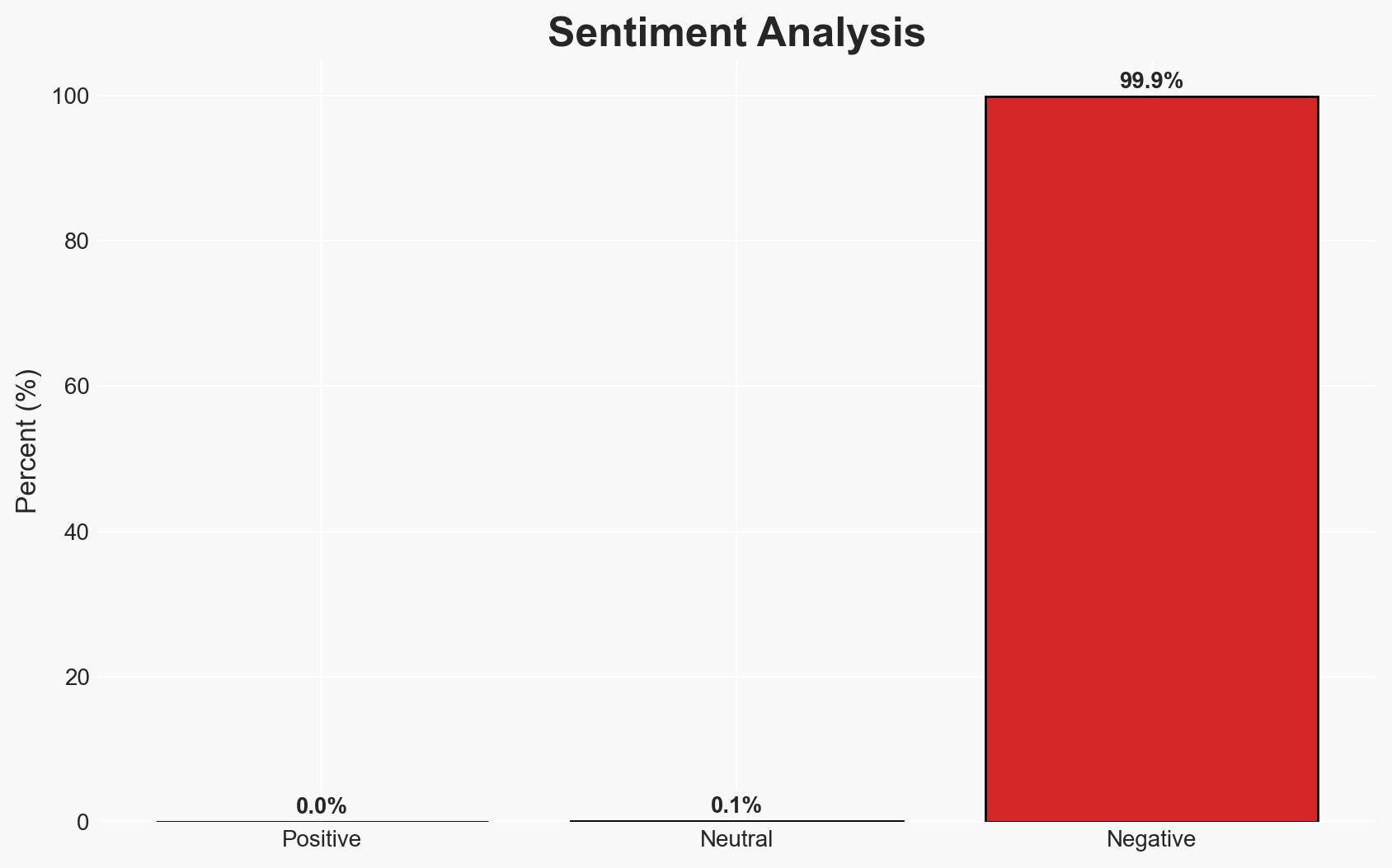
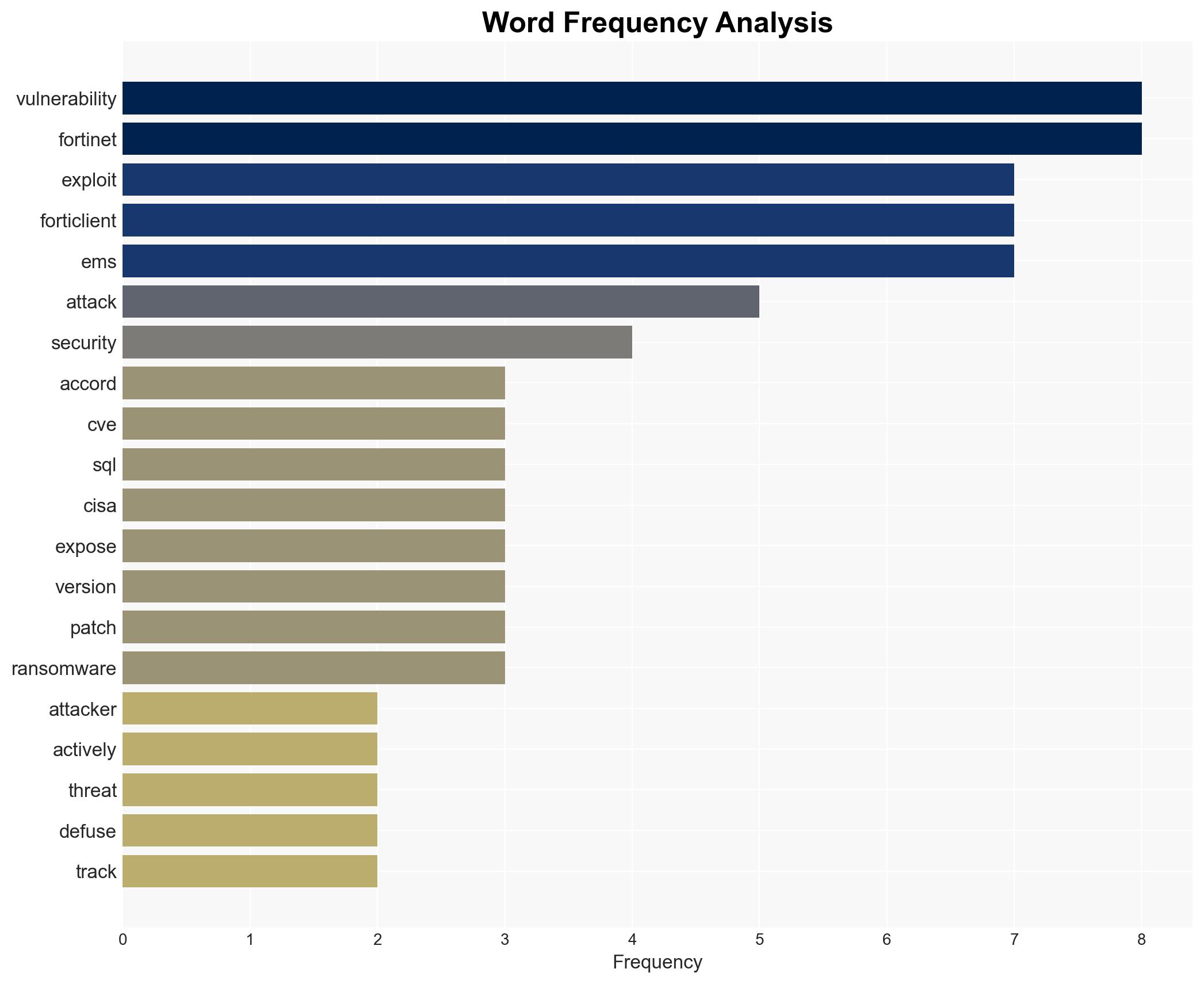
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Critical Fortinet Forticlient EMS flaw now exploited in attacks
1. BLUF (Bottom Line Up Front)
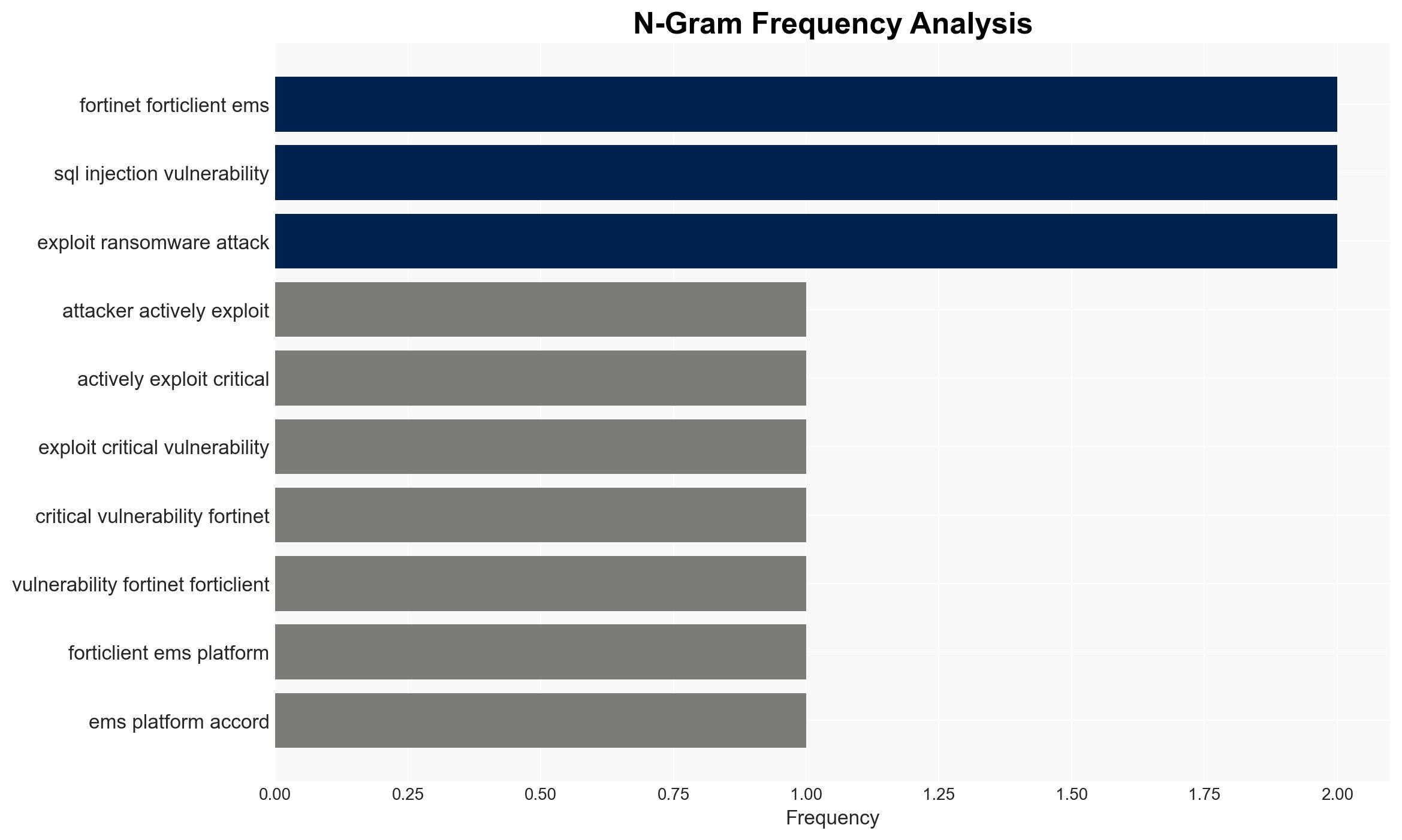
There is a critical vulnerability in Fortinet’s FortiClient EMS platform, CVE-2026-21643, currently being exploited in the wild. This vulnerability allows unauthenticated attackers to execute arbitrary code through SQL injection. The exploitation primarily affects systems in the United States and Europe. We assess with moderate confidence that this vulnerability could lead to increased ransomware attacks and cyber espionage activities if not promptly mitigated.
2. Competing Hypotheses
- Hypothesis A: The exploitation of CVE-2026-21643 is primarily opportunistic, targeting exposed systems for ransomware deployment. Supporting evidence includes the historical use of Fortinet vulnerabilities in ransomware attacks. Contradicting evidence is the lack of immediate confirmation from Fortinet and CISA.
- Hypothesis B: The exploitation is part of a coordinated cyber espionage campaign by state-sponsored actors. Supporting evidence includes past incidents involving state-sponsored groups exploiting Fortinet vulnerabilities. Contradicting evidence is the current lack of attribution or specific targeting patterns.
- Assessment: Hypothesis A is currently better supported due to the immediate financial incentives for ransomware operators and the historical precedent of similar vulnerabilities being used in such attacks. Indicators that could shift this judgment include attribution to state actors or evidence of targeted espionage activities.
3. Key Assumptions and Red Flags
- Assumptions: Fortinet will update its advisory soon; the vulnerability will be patched by most affected organizations; attackers have limited resources to exploit the vulnerability at scale.
- Information Gaps: Confirmation of exploitation details from Fortinet; specific attribution of the attackers; detailed impact assessments from affected organizations.
- Bias & Deception Risks: Potential bias in threat reporting from Defused; lack of independent verification of exploitation claims; possible misinformation from threat actors to obfuscate true intent.
4. Implications and Strategic Risks
This vulnerability exploitation could lead to significant disruptions if leveraged in widespread ransomware campaigns or targeted espionage operations. The situation could evolve rapidly if not addressed.
- Political / Geopolitical: Potential for increased tensions if state-sponsored involvement is confirmed, especially involving U.S. and European targets.
- Security / Counter-Terrorism: Heightened alert for cybersecurity teams; potential increase in ransomware incidents affecting critical infrastructure.
- Cyber / Information Space: Increased scrutiny on Fortinet’s security practices; potential for further exploitation of similar vulnerabilities.
- Economic / Social: Economic impact on affected organizations, particularly if critical services are disrupted; potential erosion of trust in cybersecurity solutions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urgently patch FortiClient EMS to version 7.4.5 or later; enhance monitoring of network traffic for signs of exploitation; engage with Fortinet for updated advisories.
- Medium-Term Posture (1–12 months): Develop partnerships for threat intelligence sharing; invest in cybersecurity training and awareness; review and strengthen incident response plans.
- Scenario Outlook:
- Best: Rapid patching mitigates threat, minimal impact.
- Worst: Widespread ransomware attacks lead to significant disruptions.
- Most-Likely: Mixed outcomes with some organizations affected, leading to increased cybersecurity measures.
6. Key Individuals and Entities
- Gwendal Guégniaud (Fortinet Product Security team)
- Defused (Threat intelligence company)
- Fortinet (Cybersecurity company)
- Shadowserver (Internet security watchdog group)
- Not clearly identifiable from open sources in this snippet (Attackers)
7. Thematic Tags
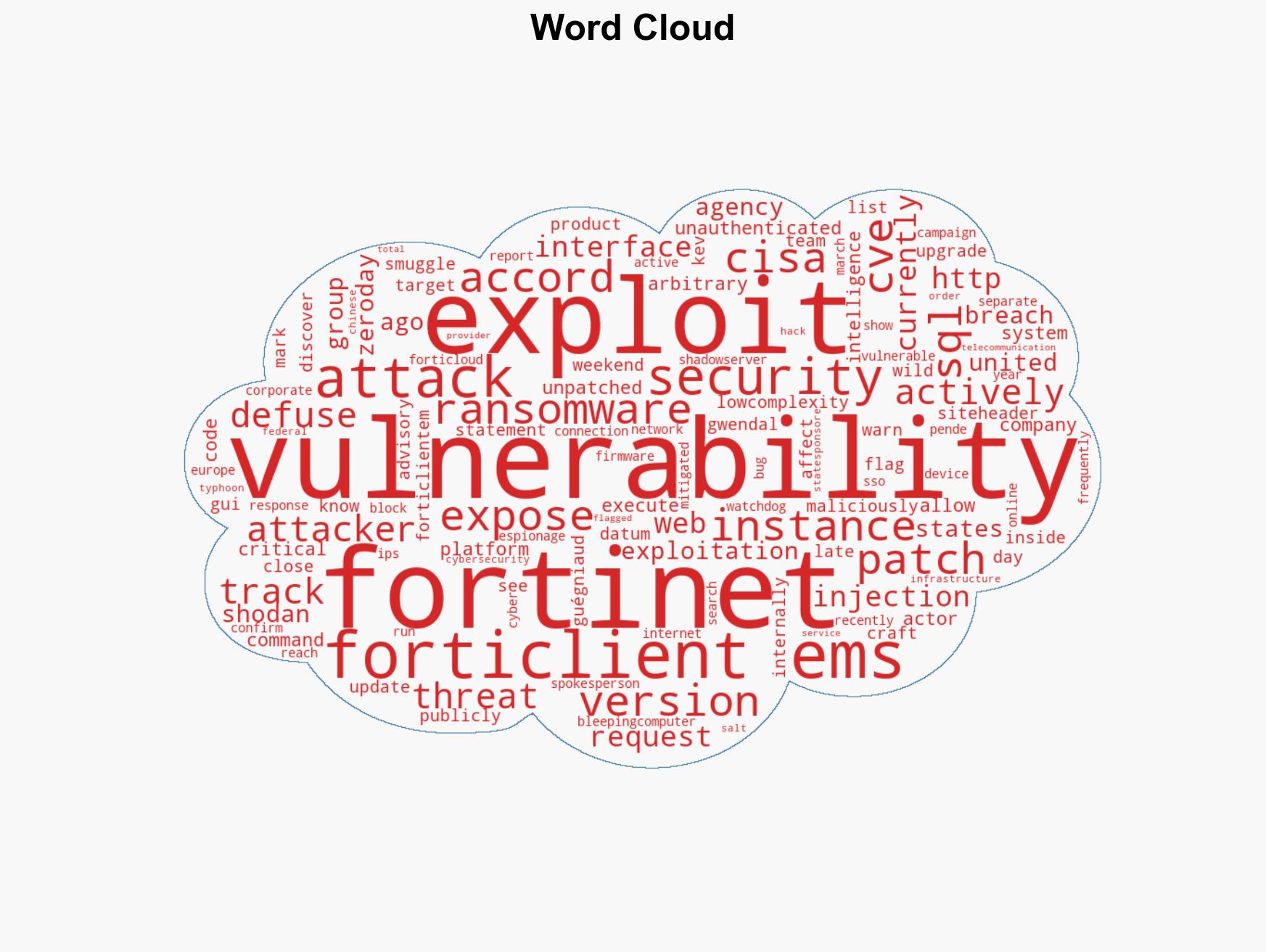
cybersecurity, ransomware, vulnerability management, cyber-espionage, Fortinet, SQL injection
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us