Four Sentenced in Greece’s Wiretapping Scandal Involving Surveillance Software Targeting Officials and Journa…
Published on: 2026-02-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Four convicted over spyware scandal that shook Greece
1. BLUF (Bottom Line Up Front)
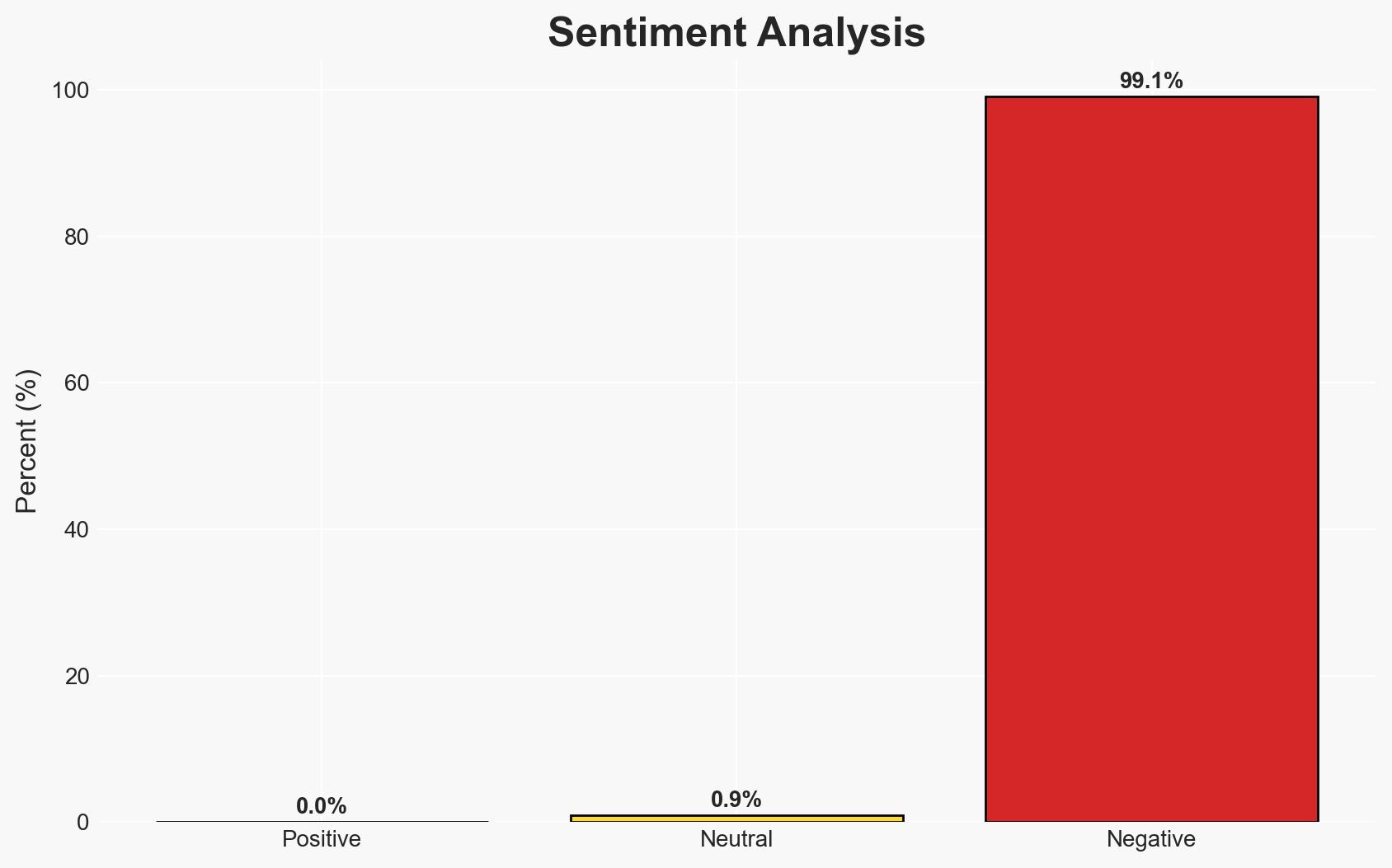
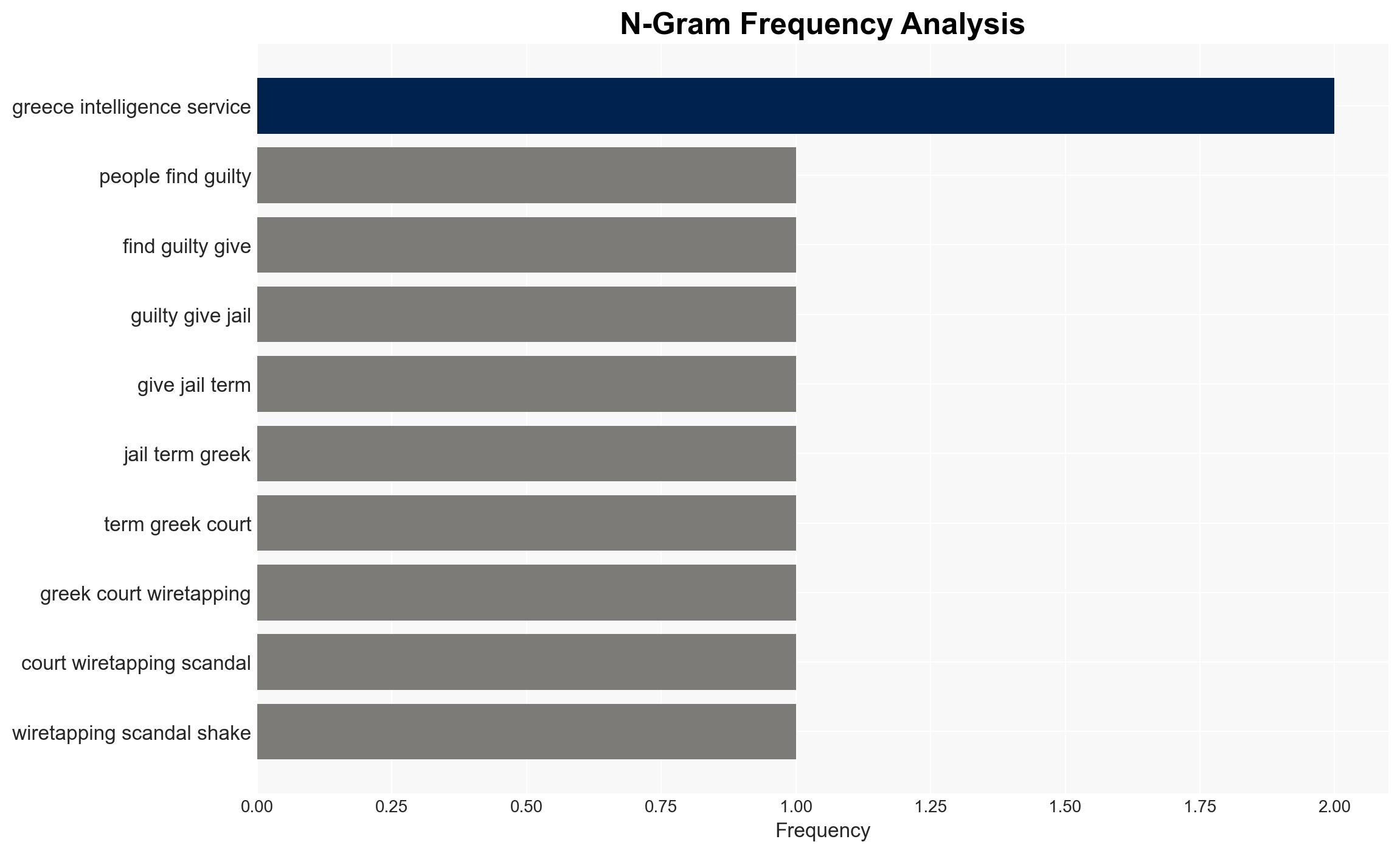
The conviction of four individuals in Greece for their roles in a wiretapping scandal highlights significant vulnerabilities in national security oversight and democratic accountability. The most likely hypothesis is that the scandal involved both domestic and foreign intelligence services, though the full extent remains unclear. This situation affects government credibility and could have broader implications for international relations. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The spyware scandal was primarily orchestrated by private individuals with limited government involvement. Supporting evidence includes the conviction of non-government actors and the absence of charges against government officials. However, the involvement of intelligence services in legal surveillance complicates this narrative.
- Hypothesis B: The scandal involved significant government complicity, potentially with foreign intelligence collaboration. This is supported by the Prime Minister’s direct supervision of the intelligence services and the judge’s mention of “unknown third parties.” Contradicting evidence includes the lack of formal charges against government officials.
- Assessment: Hypothesis B is currently better supported due to the involvement of intelligence services and the potential for unknown third-party involvement. Indicators that could shift this judgment include new evidence of direct government orders or further legal actions against officials.
3. Key Assumptions and Red Flags
- Assumptions: The legal framework in Greece allows for some level of intelligence oversight; the trial was conducted fairly; the convicted individuals acted with some degree of autonomy.
- Information Gaps: Details on the extent of government involvement, the role of foreign intelligence services, and the specific objectives of the surveillance.
- Bias & Deception Risks: Potential bias in Greek judicial proceedings; government narratives may downplay official involvement; media reports could be influenced by political agendas.
4. Implications and Strategic Risks
This development could lead to increased scrutiny of intelligence operations in Greece and potentially strain diplomatic relations if foreign involvement is confirmed. It may also affect public trust in government institutions and lead to calls for reform.
- Political / Geopolitical: Potential diplomatic tensions with countries implicated in the scandal; domestic political fallout for the Greek government.
- Security / Counter-Terrorism: Possible reassessment of intelligence operations and oversight mechanisms.
- Cyber / Information Space: Heightened awareness and regulation of surveillance technologies; potential for increased cyber espionage activities.
- Economic / Social: Erosion of public trust in government could impact social cohesion and economic stability.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor legal proceedings for new developments; engage with Greek authorities to clarify the extent of foreign involvement.
- Medium-Term Posture (1–12 months): Strengthen international partnerships to address spyware proliferation; enhance domestic legal frameworks for intelligence oversight.
- Scenario Outlook:
- Best Case: Comprehensive reforms lead to improved accountability and restored public trust.
- Worst Case: Escalation of diplomatic tensions and internal unrest due to unresolved accountability.
- Most-Likely: Gradual implementation of oversight measures with ongoing political debate.
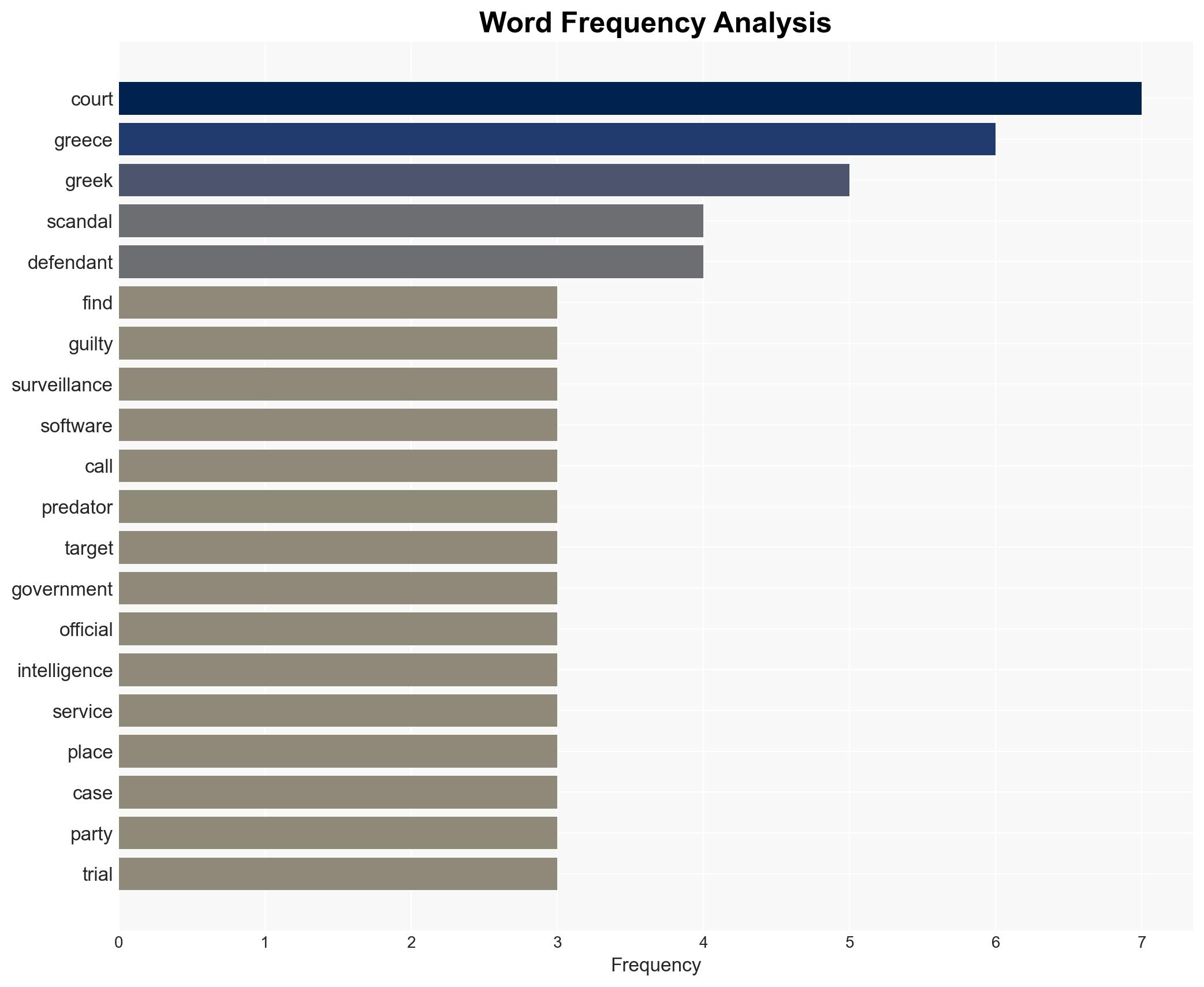
6. Key Individuals and Entities
- Felix Bitzios
- Yiannis Lavranos
- Tal Dilian
- Sara Hamou
- Nikos Androulakis
- Kyriakos Mitsotakis
- Intellexa
7. Thematic Tags
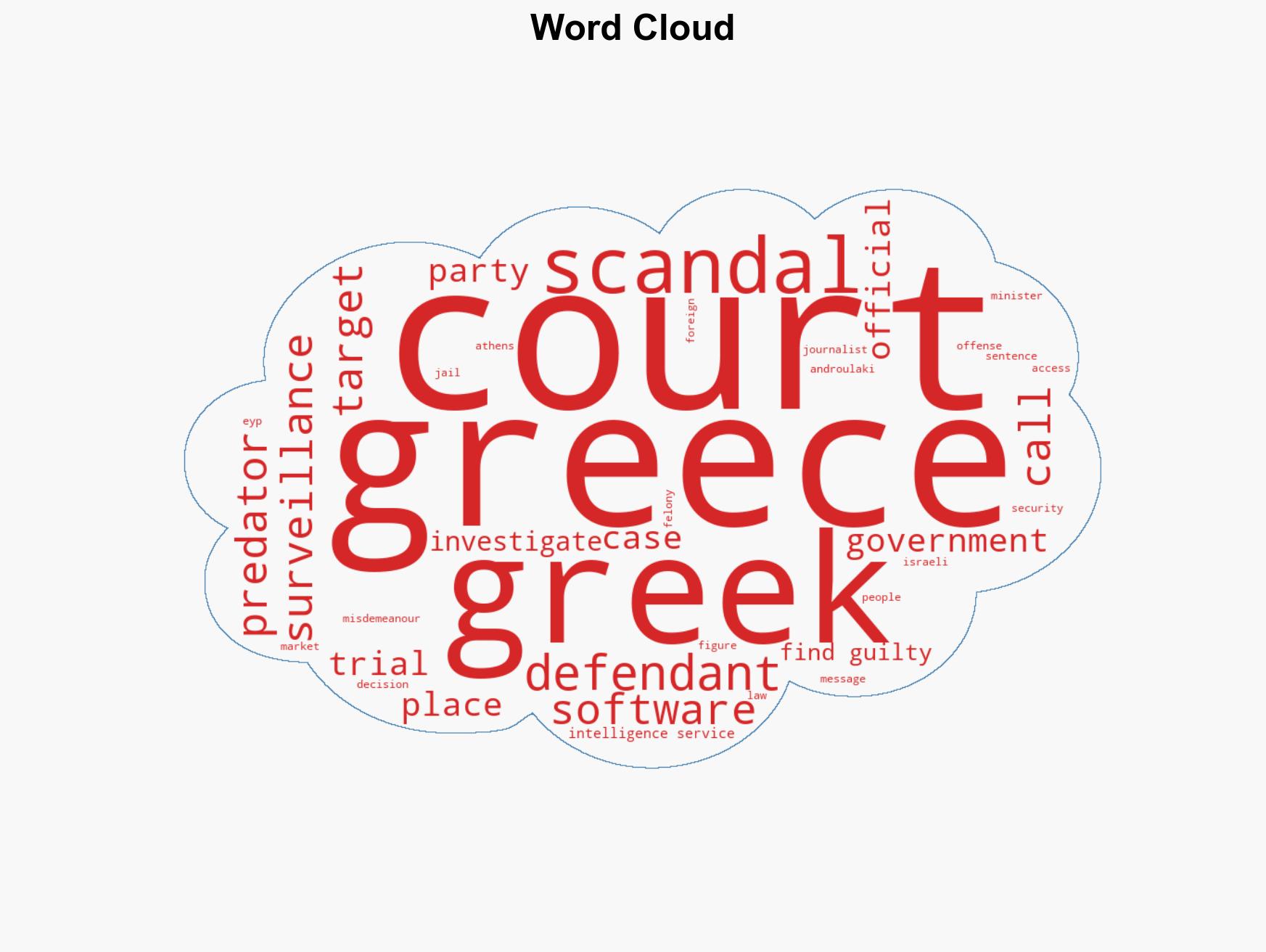
cybersecurity, surveillance, intelligence oversight, spyware, Greece, democratic accountability, cyber-espionage, legal reform
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us