Global Cybercrime Operation Synergia III Results in 45,000 Malicious IPs Disrupted and 94 Arrests Across 72 C…
Published on: 2026-03-14
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Interpol Operation Synergia III leads to 45000 malicious IPs dismantled and 94 arrests worldwide
1. BLUF (Bottom Line Up Front)
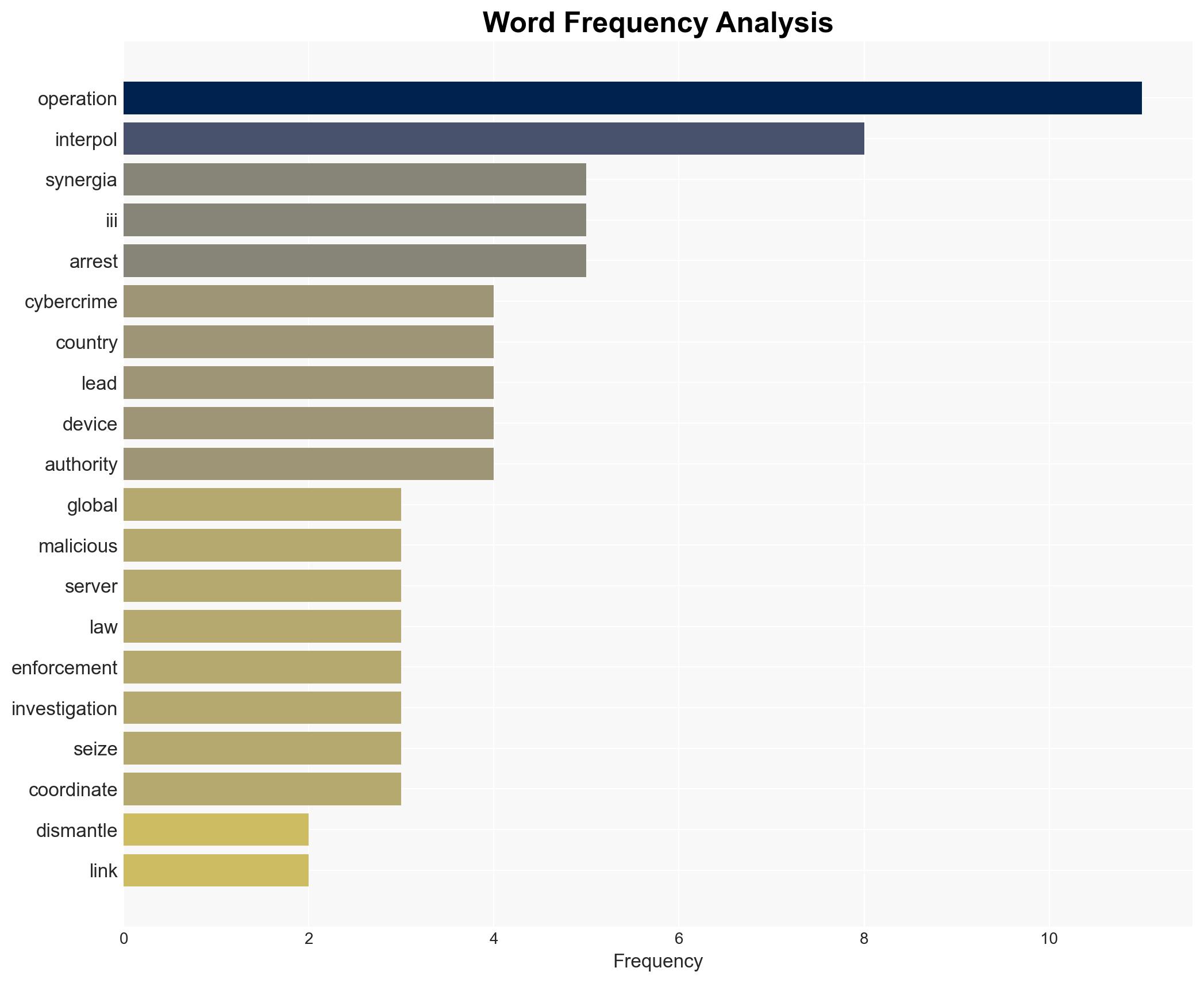
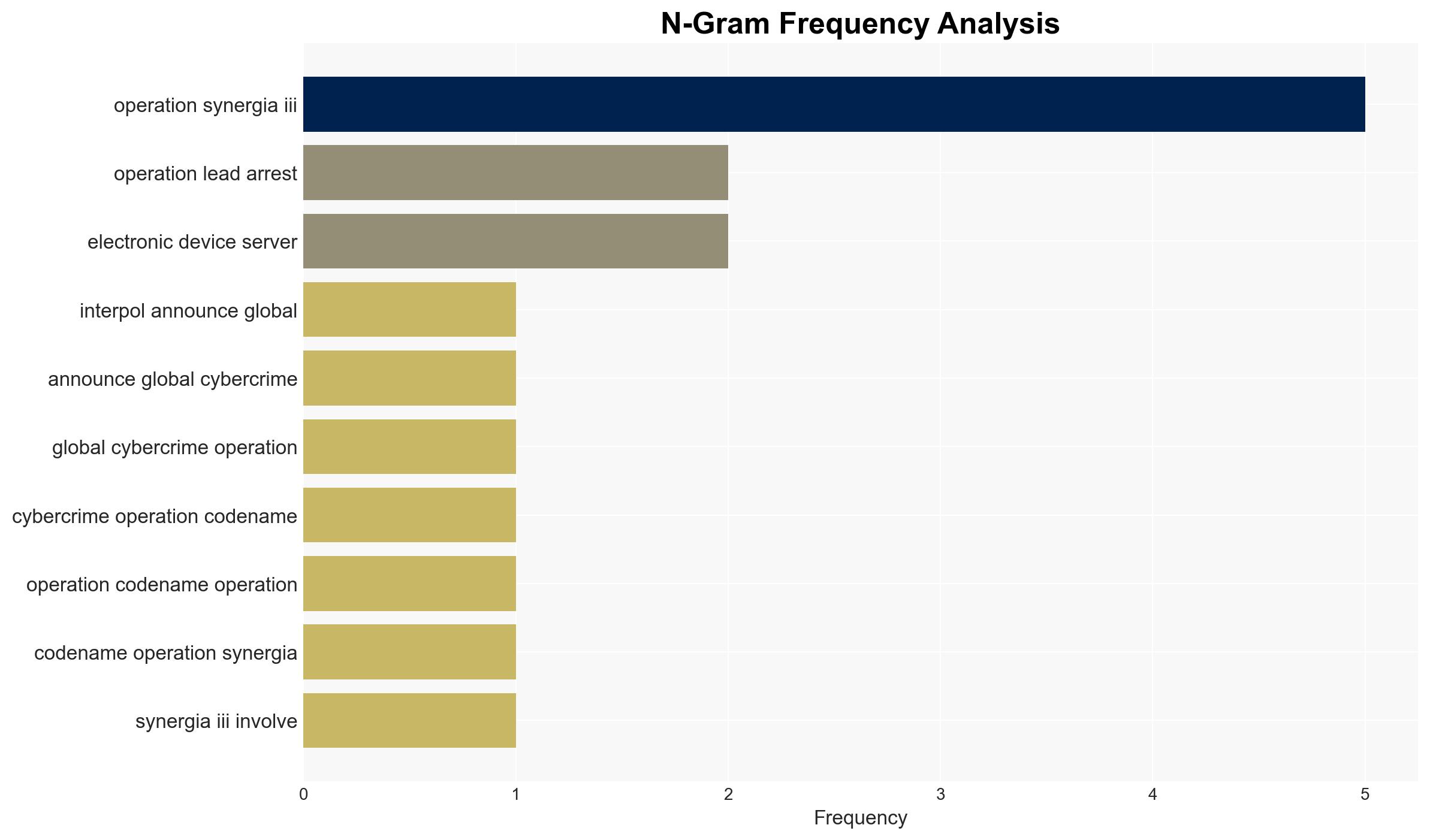
Operation Synergia III, coordinated by INTERPOL, successfully dismantled 45,000 malicious IPs and led to 94 arrests across 72 countries, significantly disrupting global cybercrime networks. The operation highlights the effectiveness of international cooperation in combating sophisticated cyber threats. This assessment is made with moderate confidence, given the scope of the operation and the ongoing investigations.
2. Competing Hypotheses
- Hypothesis A: Operation Synergia III significantly weakened global cybercrime networks by dismantling key infrastructures and arresting high-value targets. This is supported by the large number of dismantled IPs and arrests. However, uncertainties remain regarding the long-term impact on cybercrime activities.
- Hypothesis B: While Operation Synergia III disrupted some cybercrime activities, the decentralized and adaptive nature of cybercriminal networks means they will quickly recover and adapt. This is supported by the historical resilience of such networks, but lacks specific evidence from the operation’s outcomes.
- Assessment: Hypothesis A is currently better supported due to the tangible outcomes of the operation, such as arrests and infrastructure dismantling. Future indicators that could shift this judgment include resurgence in cybercrime activities or new tactics employed by cybercriminals.
3. Key Assumptions and Red Flags
- Assumptions: International cooperation will continue to be effective; dismantled infrastructures were critical to operations; arrested individuals were key operators.
- Information Gaps: Specific roles of arrested individuals, detailed impact on cybercrime operations, and long-term effectiveness of dismantled infrastructures.
- Bias & Deception Risks: Potential overestimation of the operation’s impact due to reporting bias; reliance on data from involved parties may overlook undetected activities.
4. Implications and Strategic Risks
The operation’s success may encourage further international collaboration against cybercrime, but also prompt cybercriminals to innovate and adapt. The dismantling of infrastructures could temporarily reduce cybercrime activities, but may lead to the emergence of more sophisticated methods.
- Political / Geopolitical: Strengthened international law enforcement cooperation; potential diplomatic tensions with countries harboring cybercriminals.
- Security / Counter-Terrorism: Enhanced global cyber resilience; potential for retaliatory cyberattacks by disrupted networks.
- Cyber / Information Space: Temporary reduction in phishing and ransomware activities; possible shift to more covert cybercrime tactics.
- Economic / Social: Short-term economic relief from reduced cybercrime; potential for increased public trust in digital systems.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor for resurgence in cybercrime activities; enhance intelligence sharing among member countries.
- Medium-Term Posture (1–12 months): Develop resilience measures against evolving cyber threats; strengthen partnerships with private cybersecurity firms.
- Scenario Outlook: Best: Sustained reduction in cybercrime; Worst: Rapid adaptation and resurgence of cybercriminal activities; Most-Likely: Temporary disruption with gradual adaptation by cybercriminals.
6. Key Individuals and Entities
- Neal Jetton, INTERPOL’s Director of the Cybercrime Directorate
- Group-IB, Trend Micro, S2W (Cybersecurity firms supporting the operation)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
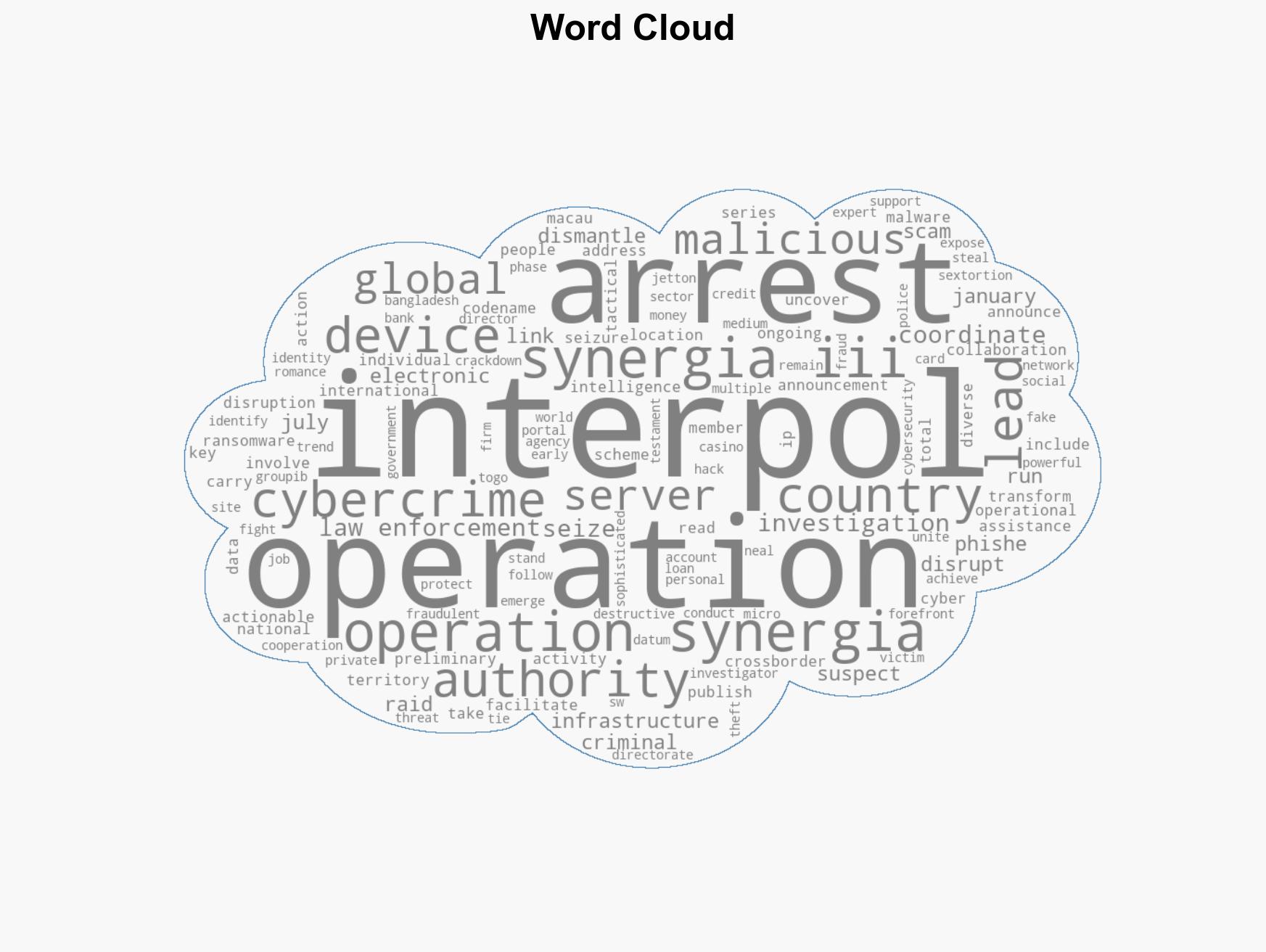
cybersecurity, cybercrime, international cooperation, law enforcement, phishing, ransomware, INTERPOL
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us