Global Cybersecurity Spending Set to Reach $244 Billion Amid Rising Threats from Hostile Nations
Published on: 2026-03-30
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: A 244 Billion Arms Race Is Brewing in Cybersecurity
1. BLUF (Bottom Line Up Front)
The U.S. Intelligence Community’s 2026 Annual Threat Assessment highlights the embedding of hostile nations within America’s critical infrastructure, posing a significant cybersecurity threat. The rapid evolution of AI-driven vulnerabilities and the need for post-quantum cryptography are driving a surge in global cybersecurity spending, projected to reach $244 billion by 2026. This development primarily affects national security and large enterprises. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: Hostile nations have successfully embedded themselves within U.S. critical infrastructure, preparing for potential future conflicts. This is supported by the U.S. Intelligence Community’s findings but lacks specific evidence on the extent and capabilities of these embedded threats.
- Hypothesis B: The threat of hostile nations within U.S. infrastructure is overstated, possibly as a strategic move to increase cybersecurity funding and focus. This hypothesis is less supported due to the alignment of multiple reports indicating genuine vulnerabilities.
- Assessment: Hypothesis A is currently better supported due to the convergence of intelligence assessments and global cybersecurity trends. Indicators such as increased cyber incidents or intelligence leaks could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Hostile nations have the capability to exploit embedded positions; AI-driven vulnerabilities will continue to grow; post-quantum cryptography is essential for future security.
- Information Gaps: Specific details on the identity and capabilities of the hostile nations embedded in U.S. infrastructure are lacking.
- Bias & Deception Risks: Potential bias in threat assessments due to vested interests in increasing cybersecurity budgets; risk of misinformation from hostile actors.
4. Implications and Strategic Risks
The ongoing cybersecurity arms race could lead to increased geopolitical tensions and a reevaluation of international cybersecurity norms.
- Political / Geopolitical: Escalation of cyber warfare capabilities and potential for retaliatory cyber operations.
- Security / Counter-Terrorism: Increased vulnerability of critical infrastructure to cyber-attacks during conflicts.
- Cyber / Information Space: Heightened focus on developing post-quantum cryptography and AI-driven cybersecurity solutions.
- Economic / Social: Significant financial investments required for infrastructure upgrades, impacting economic stability and resource allocation.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of critical infrastructure for signs of embedded threats; prioritize AI vulnerability assessments.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms specializing in post-quantum cryptography; invest in workforce training for emerging cyber threats.
- Scenario Outlook: Best: Successful mitigation of embedded threats and strengthened infrastructure; Worst: Major cyber-attack exploiting vulnerabilities; Most-Likely: Gradual improvement in cybersecurity posture with ongoing challenges.
6. Key Individuals and Entities
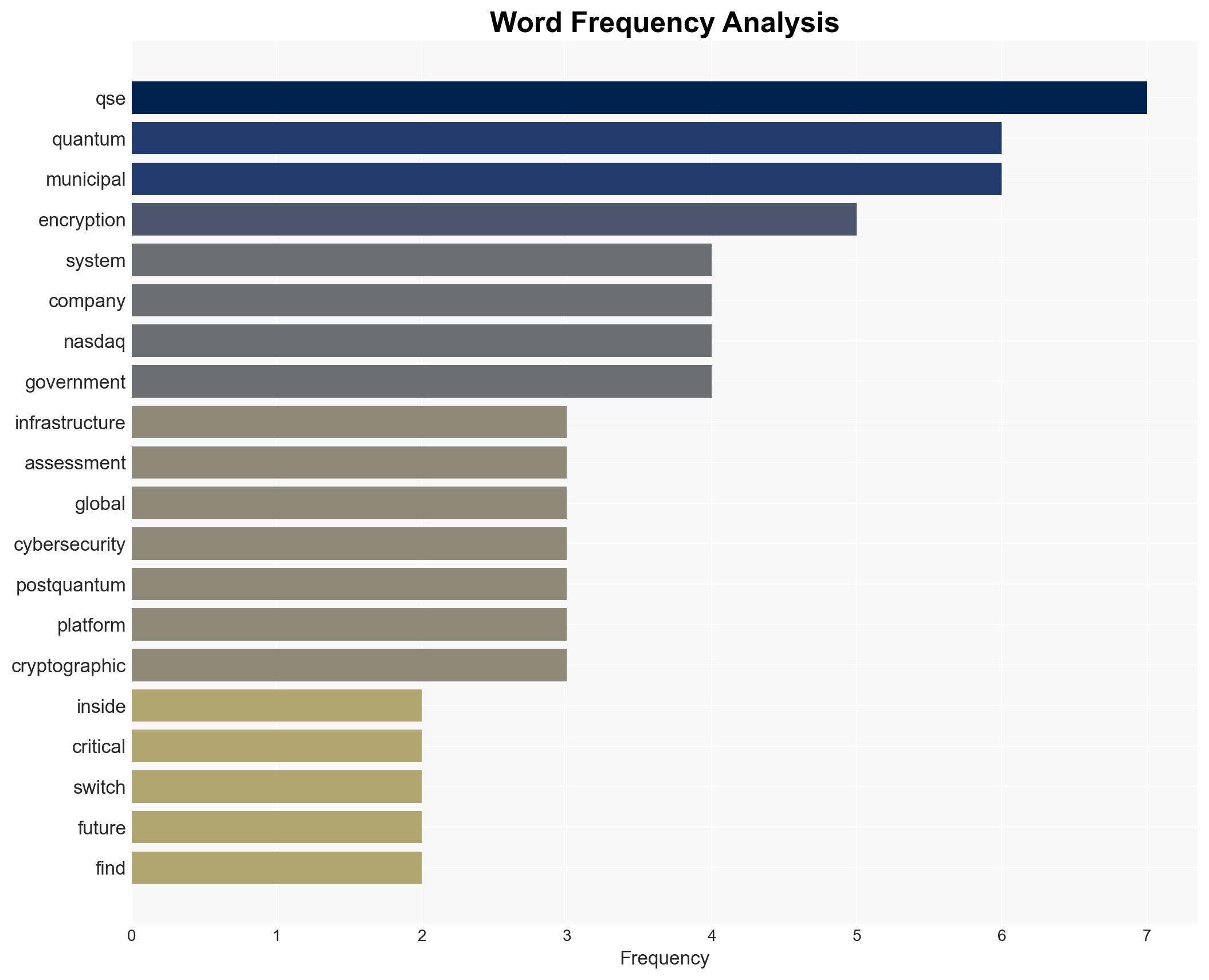
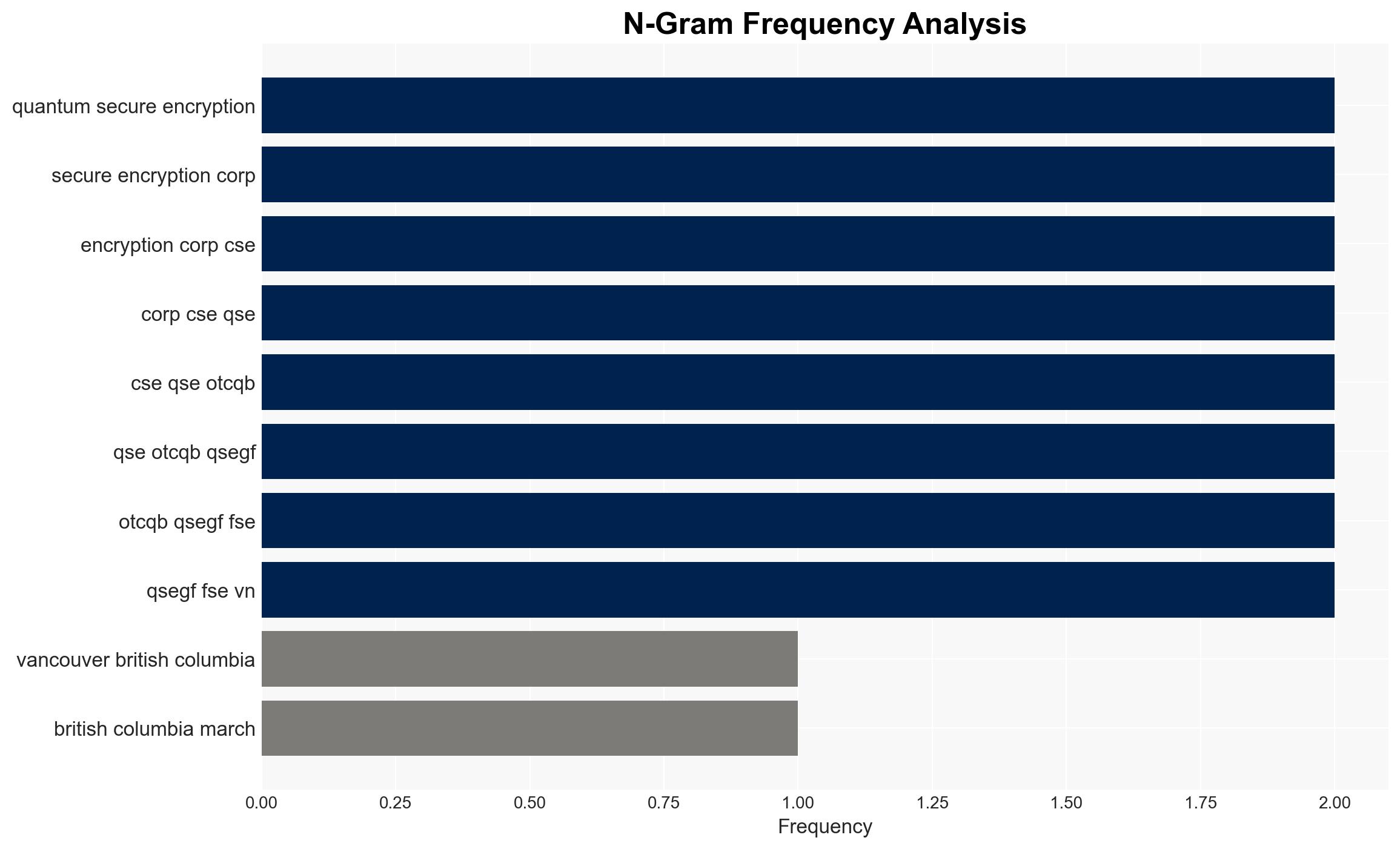
- Quantum Secure Encryption Corp.
- Rapid7
- NetScout Systems
- Fastly
- Qualys
- Ted Carefoot, CEO of QSE
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
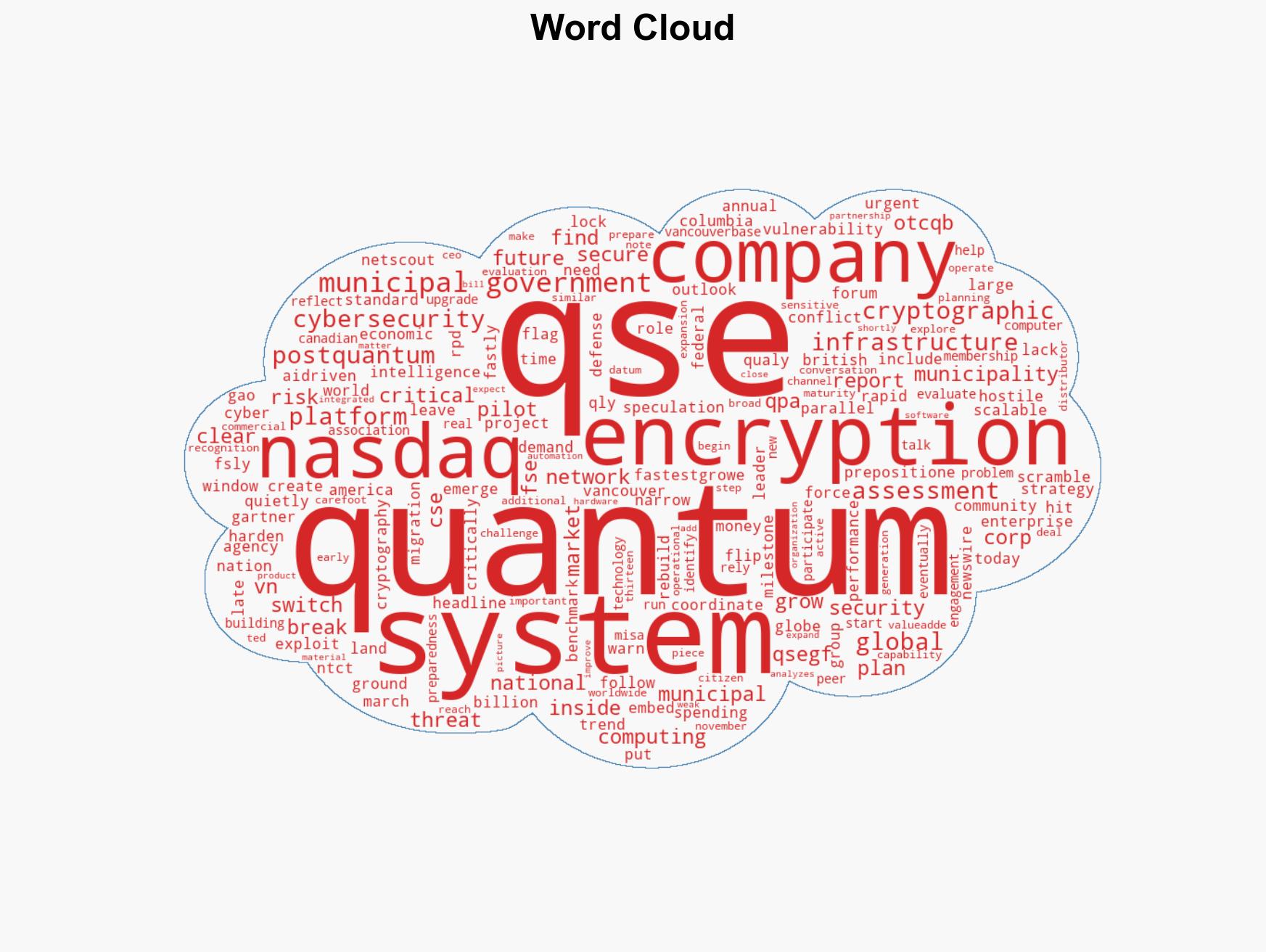
cybersecurity, AI vulnerabilities, post-quantum cryptography, critical infrastructure, national security, cyber arms race, global cybersecurity spending
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us