Google alerts that quantum computing could potentially compromise Bitcoin transactions in just nine minutes.
Published on: 2026-04-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Google warns Quantum Computing attack could crack Bitcoin in 9 minutes
1. BLUF (Bottom Line Up Front)
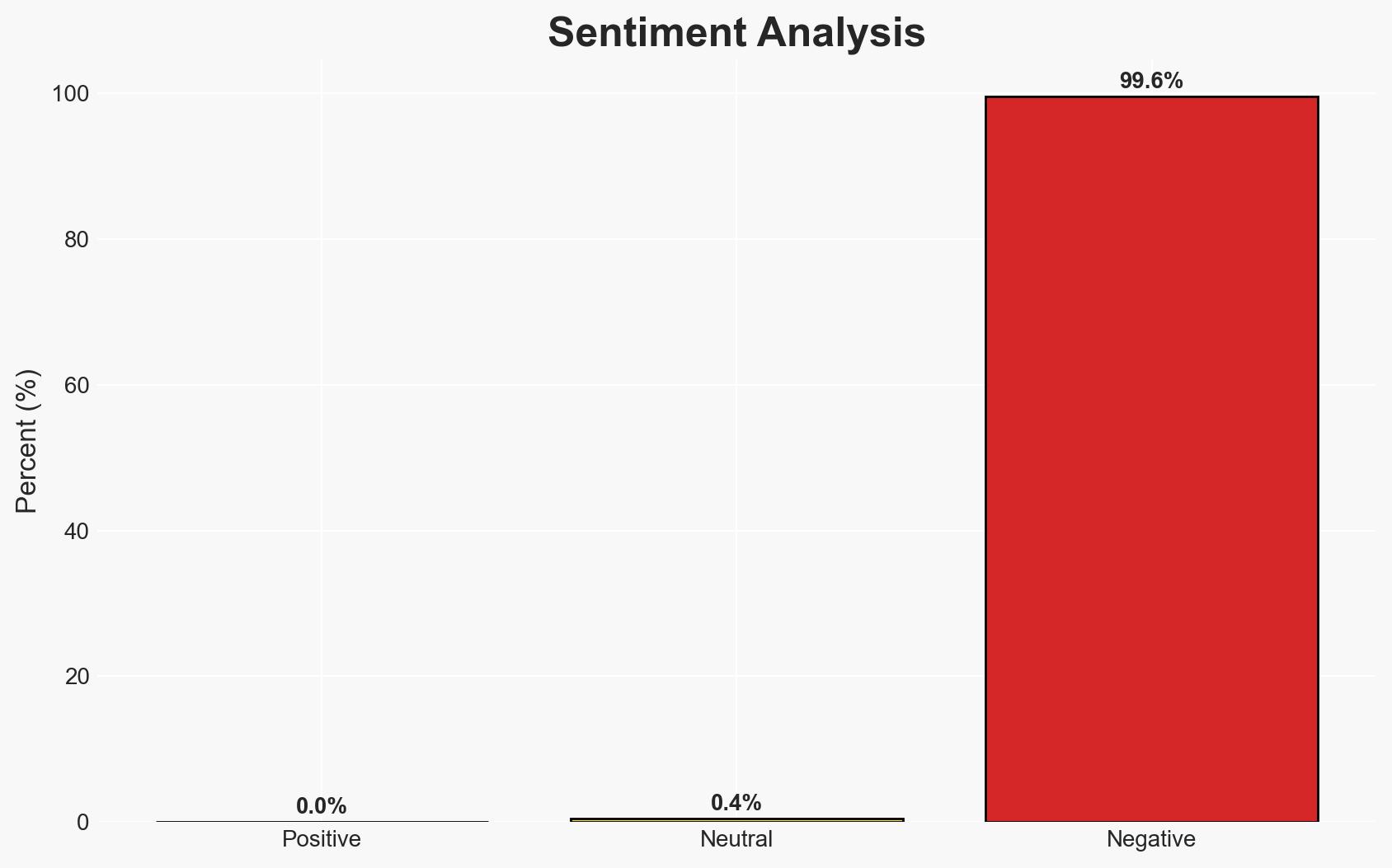
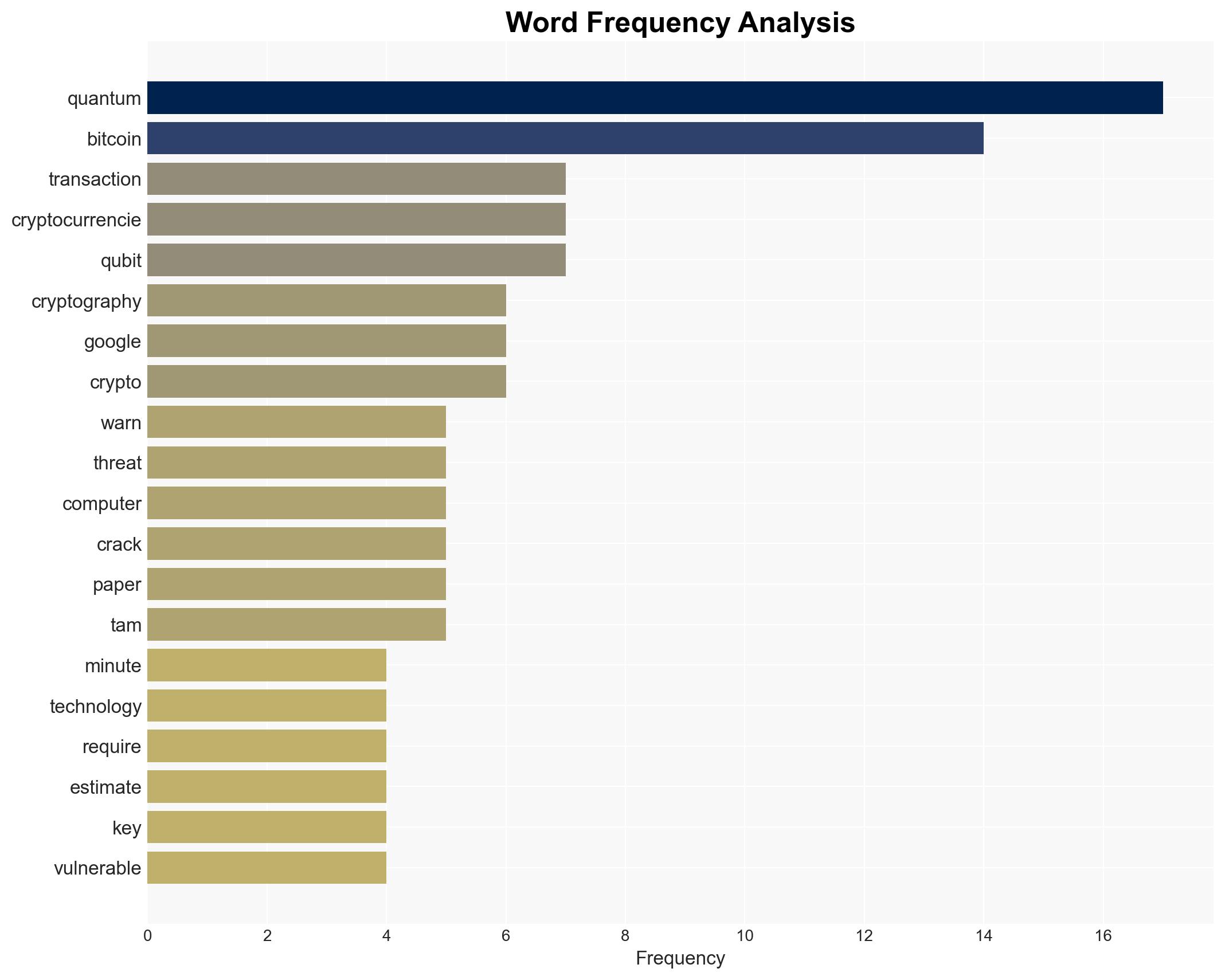
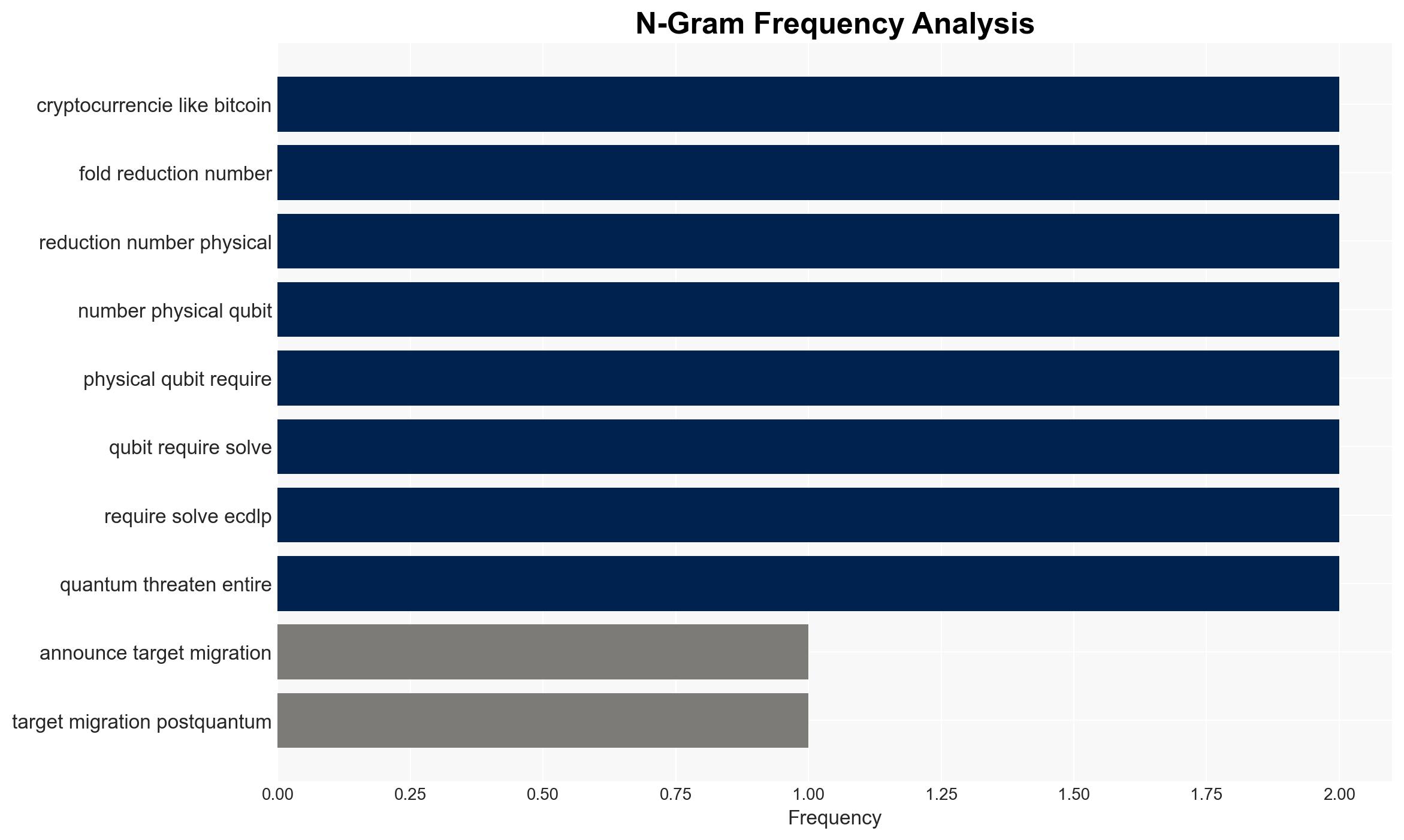
Google’s warning highlights a potential future threat where quantum computing could compromise Bitcoin transactions, potentially within nine minutes. This development, while not immediate, poses significant risks to cryptocurrency security and financial systems globally. The most likely hypothesis is that quantum computing advancements will necessitate a shift to post-quantum cryptography by 2029. Overall confidence in this assessment is moderate, given current technological limitations and timelines.
2. Competing Hypotheses
- Hypothesis A: Quantum computing will advance sufficiently by 2029 to pose a credible threat to Bitcoin and other cryptocurrencies. This hypothesis is supported by Google’s projection and the reduction in qubits required to crack current encryption. However, uncertainties include the pace of quantum computing development and the effectiveness of post-quantum cryptography.
- Hypothesis B: Quantum computing will not advance to a level that threatens Bitcoin by 2029, and existing cryptographic measures will remain secure. This is contradicted by Google’s analysis but could be supported by unforeseen technological challenges or breakthroughs in cryptographic defenses.
- Assessment: Hypothesis A is currently better supported due to Google’s detailed analysis and the historical trend of rapid advancements in quantum computing. Key indicators that could shift this judgment include breakthroughs in quantum-resistant cryptography or significant delays in quantum computing development.
3. Key Assumptions and Red Flags
- Assumptions: Quantum computing will continue to progress at its current pace; post-quantum cryptography will be implemented by 2029; current cryptographic methods will remain vulnerable to quantum attacks.
- Information Gaps: Specific timelines for quantum computing advancements and the development of effective post-quantum cryptography solutions.
- Bias & Deception Risks: Potential bias in Google’s projections due to vested interests in promoting post-quantum cryptography; lack of independent verification of quantum computing capabilities.
4. Implications and Strategic Risks
The potential for quantum computing to compromise cryptocurrency security could drive significant changes in financial systems and cybersecurity strategies. This development could influence global economic stability and digital trust.
- Political / Geopolitical: Nations may accelerate quantum research and development to gain strategic advantages, potentially leading to a new technological arms race.
- Security / Counter-Terrorism: Increased vulnerabilities in financial transactions could be exploited by malicious actors, including state-sponsored groups.
- Cyber / Information Space: A shift towards post-quantum cryptography will be necessary, impacting cybersecurity frameworks and digital infrastructure.
- Economic / Social: Potential destabilization of cryptocurrency markets and loss of public trust in digital financial systems.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Initiate monitoring of quantum computing advancements and assess current cryptographic vulnerabilities in critical systems.
- Medium-Term Posture (1–12 months): Develop partnerships with technology firms and research institutions to advance post-quantum cryptography solutions.
- Scenario Outlook:
- Best: Quantum computing advances slowly, allowing ample time for cryptographic adaptation.
- Worst: Rapid quantum breakthroughs outpace cryptographic defenses, leading to widespread financial disruption.
- Most-Likely: Gradual progress in quantum computing with parallel development of post-quantum cryptography, mitigating immediate risks.
6. Key Individuals and Entities
- Cryptocurrency developers and stakeholders (e.g., Bitcoin, Ethereum)
- Quantum computing research institutions
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
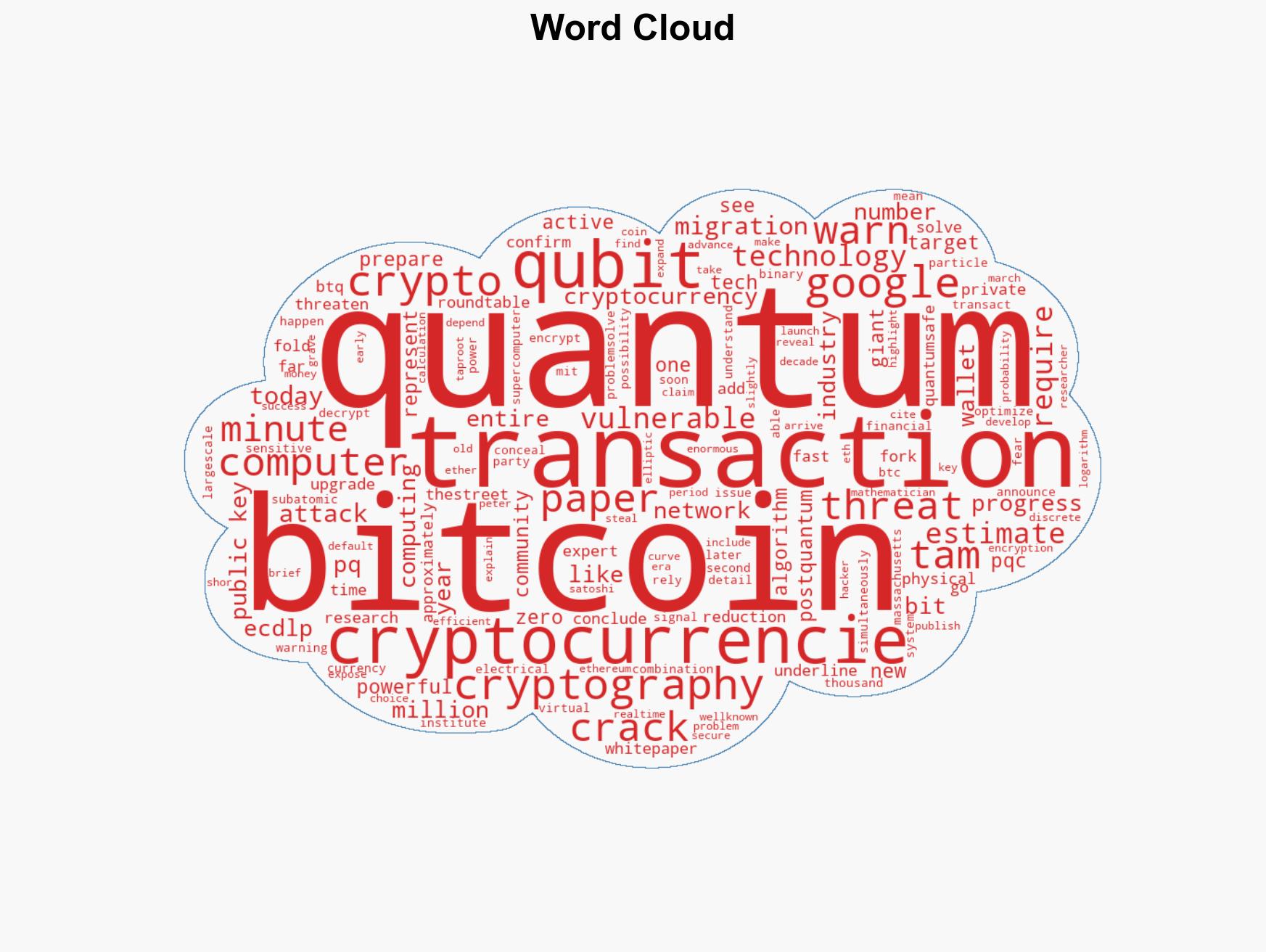
cybersecurity, quantum computing, cryptocurrency security, post-quantum cryptography, financial systems, technological arms race
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us