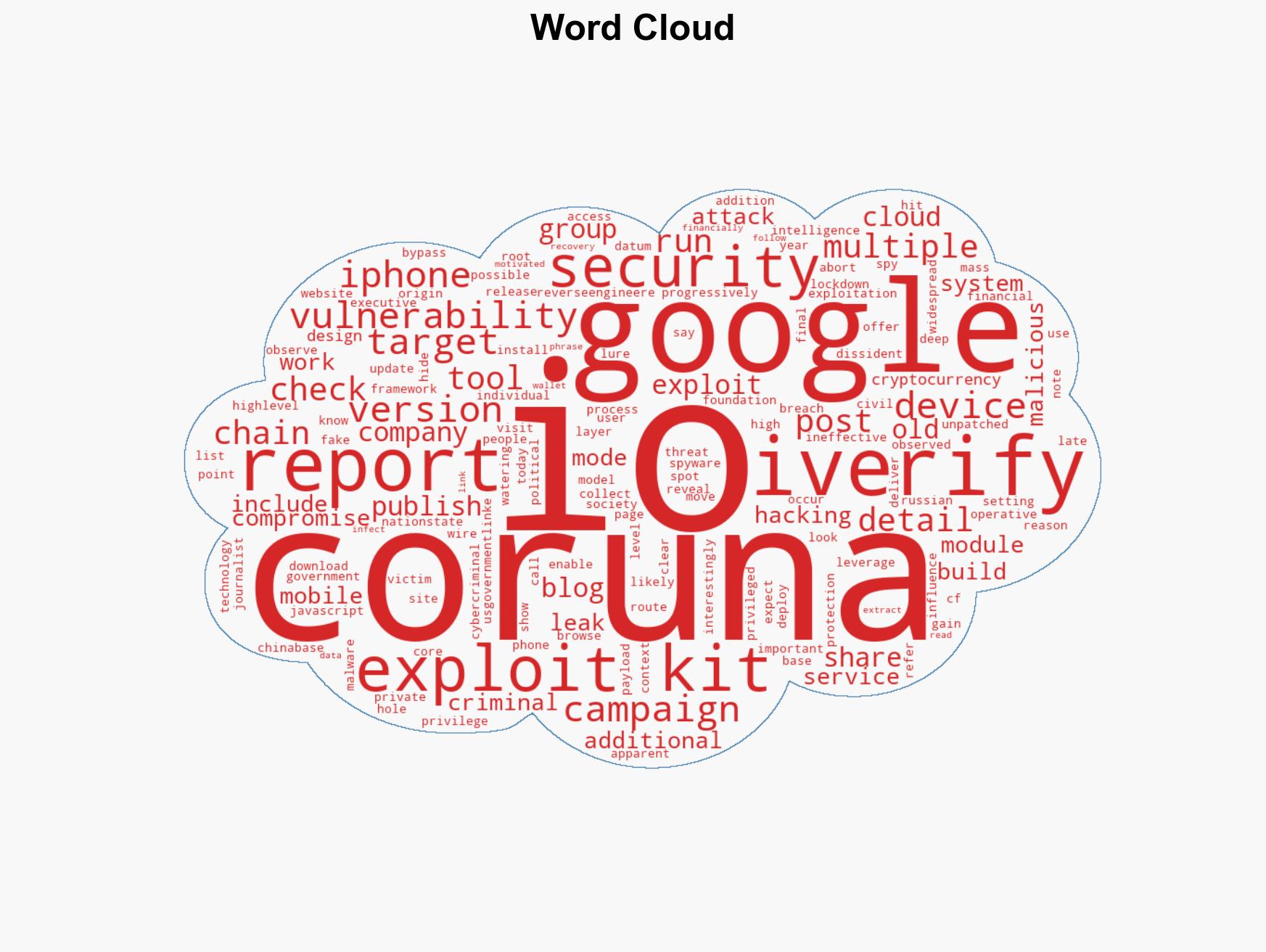
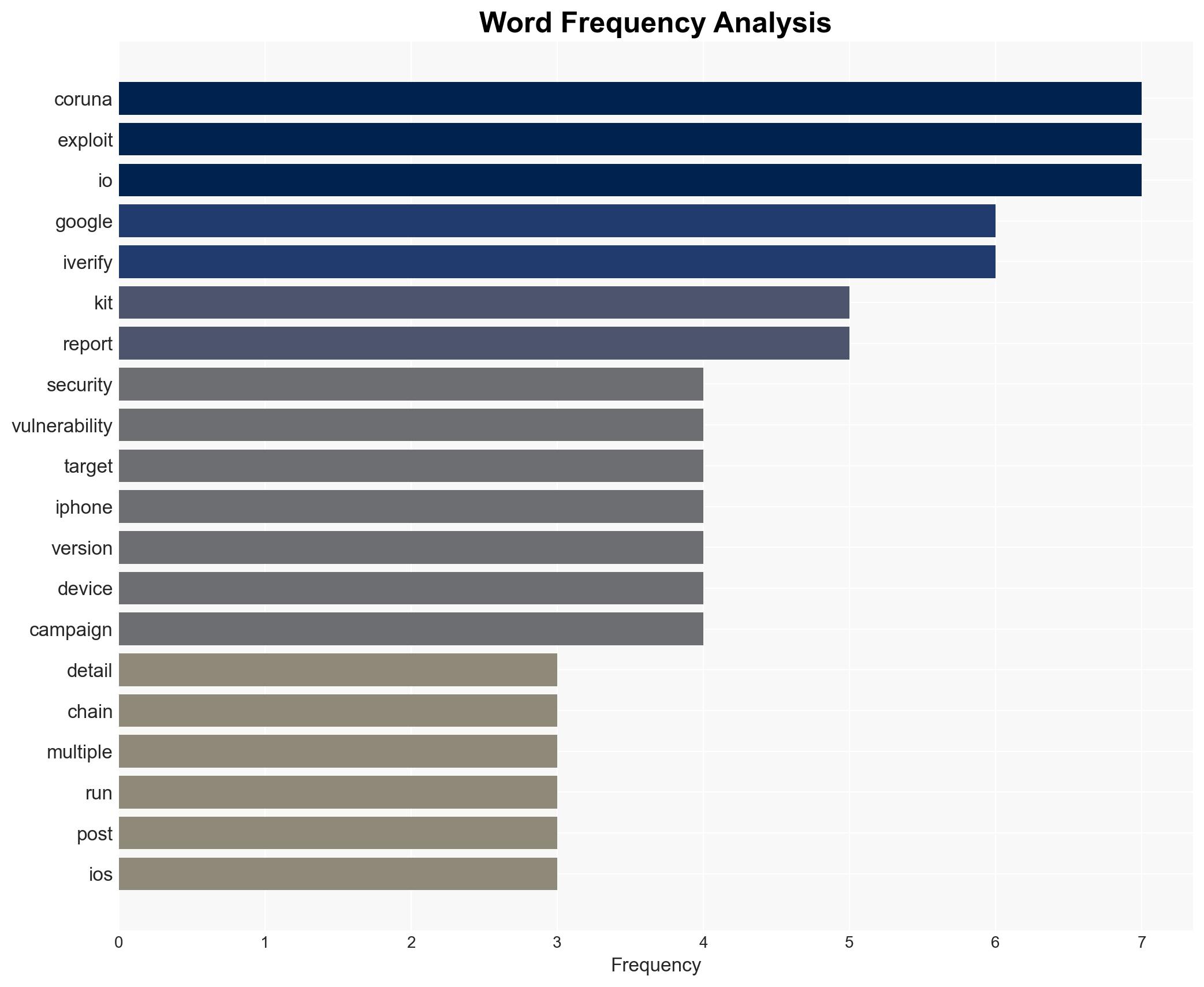
Google and iVerify uncover Coruna exploit kit targeting unpatched iPhones with multiple vulnerabilities
Published on: 2026-03-04
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Google and iVerify reveal government-grade iPhone exploit kit spreading to hackers
1. BLUF (Bottom Line Up Front)
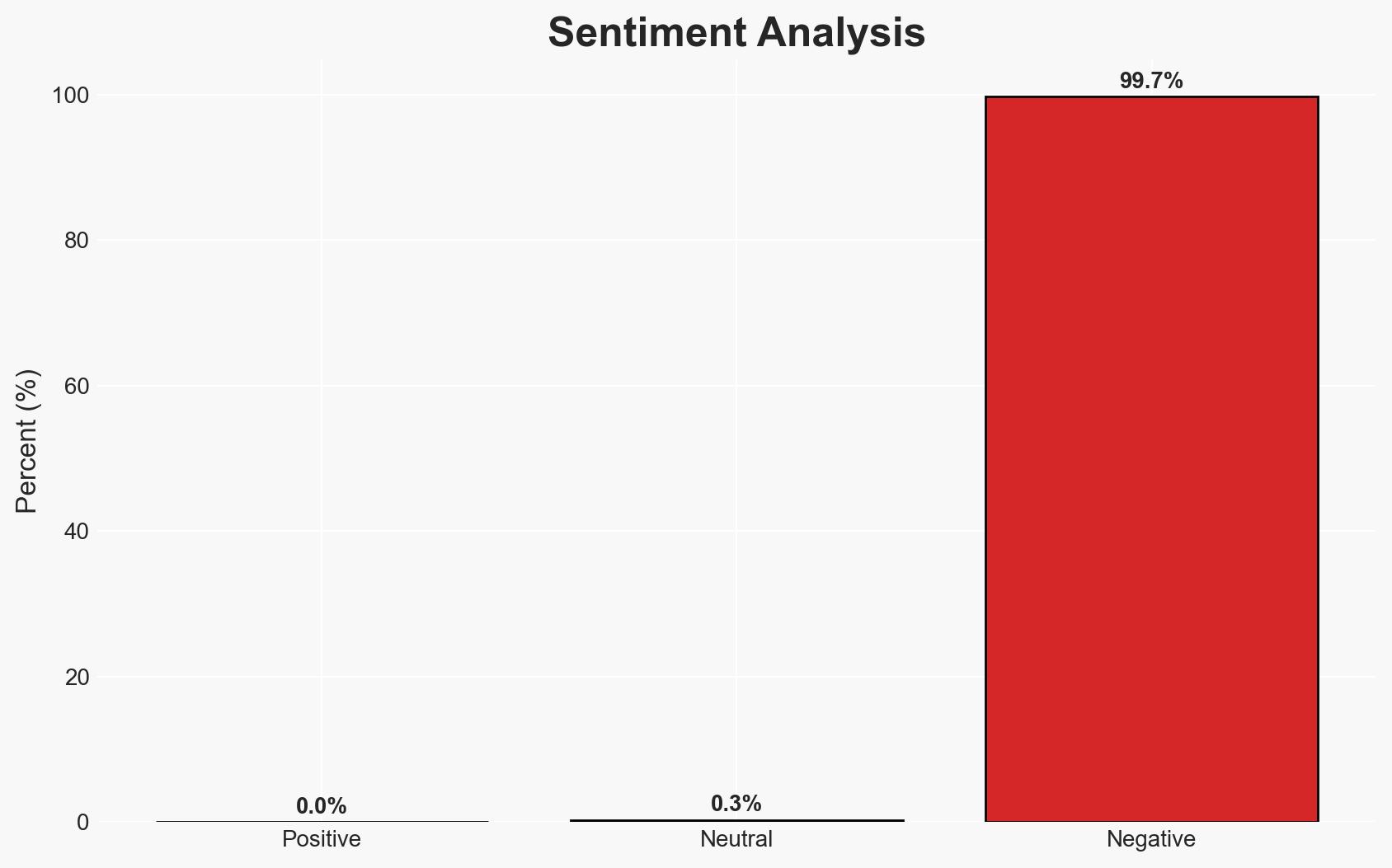
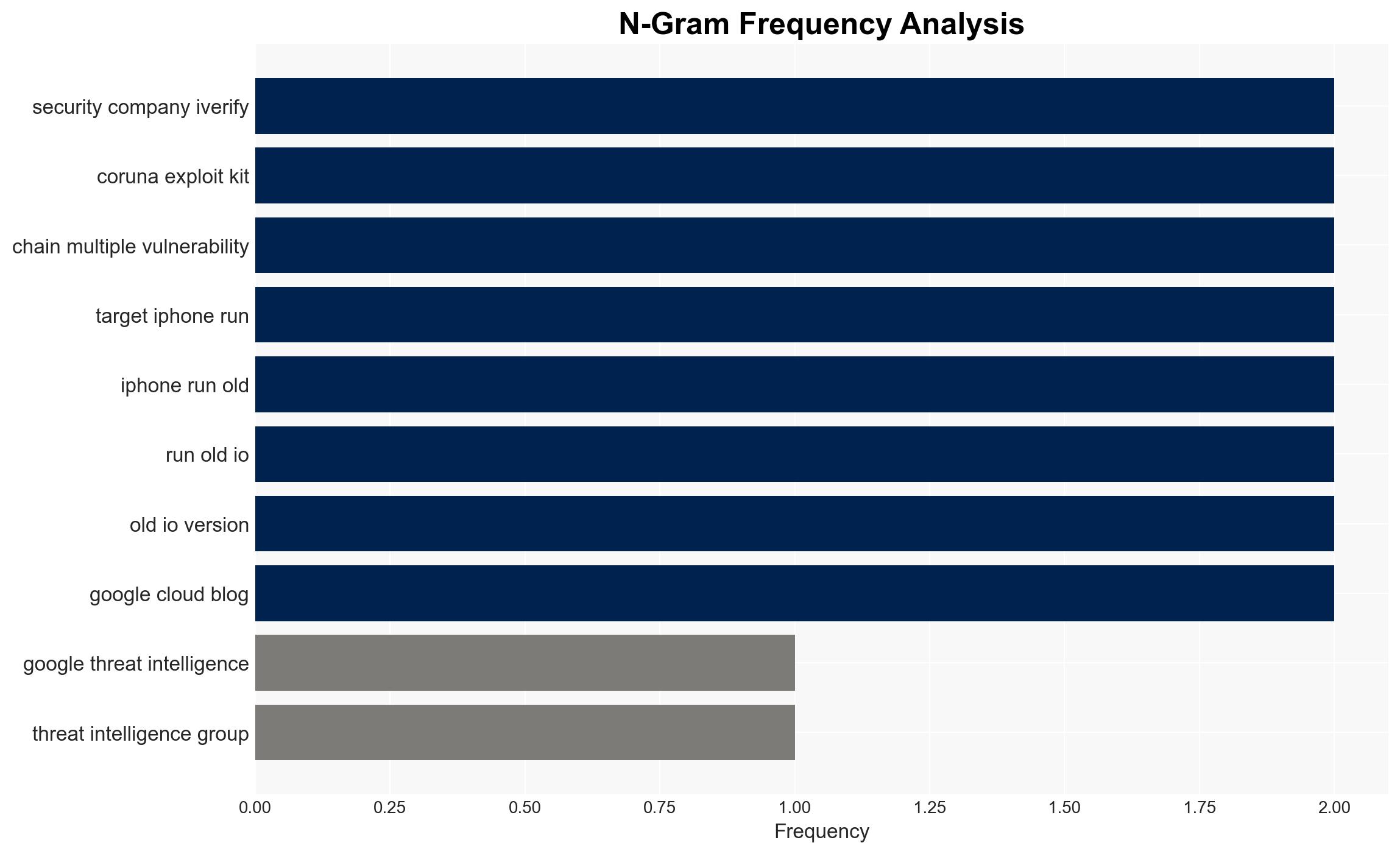
The Coruna exploit kit, leveraging government-grade hacking tools, targets older iOS versions and has been linked to Russian and Chinese cybercriminals. This development poses a significant threat to individuals and organizations using outdated iPhones, with moderate confidence in the assessment. The exploit’s sophistication suggests potential nation-state involvement or influence.
2. Competing Hypotheses
- Hypothesis A: Coruna is primarily a criminal tool developed independently by cybercriminals using leaked government-grade technology. This is supported by its financial motivation and use in widespread campaigns. However, the sophistication and origin of the tools suggest possible state involvement.
- Hypothesis B: Coruna is a state-sponsored tool that has been repurposed by cybercriminals. The shared roots with US-government-linked tools and its deployment by Russian and Chinese actors support this hypothesis, but the financial motivation and criminal use suggest otherwise.
- Assessment: Hypothesis B is currently better supported due to the exploit’s complexity and its origins linked to known government tools. Indicators such as further technical analysis or attribution could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The exploit kit’s origins are accurately reported; the vulnerabilities are not patched in older iOS versions; the actors involved have the capability to deploy such sophisticated tools.
- Information Gaps: Specific details on the initial leak of the exploit kit; comprehensive attribution of the actors involved; full technical analysis of the exploit’s capabilities.
- Bias & Deception Risks: Potential bias in attributing the exploit to nation-state actors; risk of misinformation from involved parties to obscure true origins or intentions.
4. Implications and Strategic Risks
The proliferation of government-grade exploits in criminal hands could lead to increased cyber threats against high-value targets, potentially destabilizing economic and political environments. This development could prompt more aggressive cybersecurity measures and international tensions.
- Political / Geopolitical: Potential escalation in cyber warfare tactics and increased tensions between implicated states.
- Security / Counter-Terrorism: Heightened threat landscape for targeted sectors, requiring enhanced security protocols.
- Cyber / Information Space: Increased risk of sophisticated cyber attacks and misinformation campaigns leveraging compromised devices.
- Economic / Social: Potential economic impact on affected industries and increased public concern over digital privacy and security.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Urge users to update iOS devices; monitor for further exploit developments; enhance cybersecurity awareness and training.
- Medium-Term Posture (1–12 months): Develop partnerships for threat intelligence sharing; invest in cybersecurity infrastructure; consider policy measures to address cyber threats.
- Scenario Outlook:
- Best Case: Exploit is contained, and vulnerabilities are patched, reducing threat levels.
- Worst Case: Exploit is further weaponized, leading to widespread cyber incidents.
- Most-Likely: Continued sporadic use of the exploit by criminal groups, with gradual mitigation as awareness and defenses improve.
6. Key Individuals and Entities
- Google Threat Intelligence Group
- iVerify
- Russian cybercriminals
- China-based cybercriminals
- US government (indirectly, through tool origins)
7. Thematic Tags
cybersecurity, cyber-espionage, nation-state threats, iOS vulnerabilities, exploit kits, cybercrime, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us