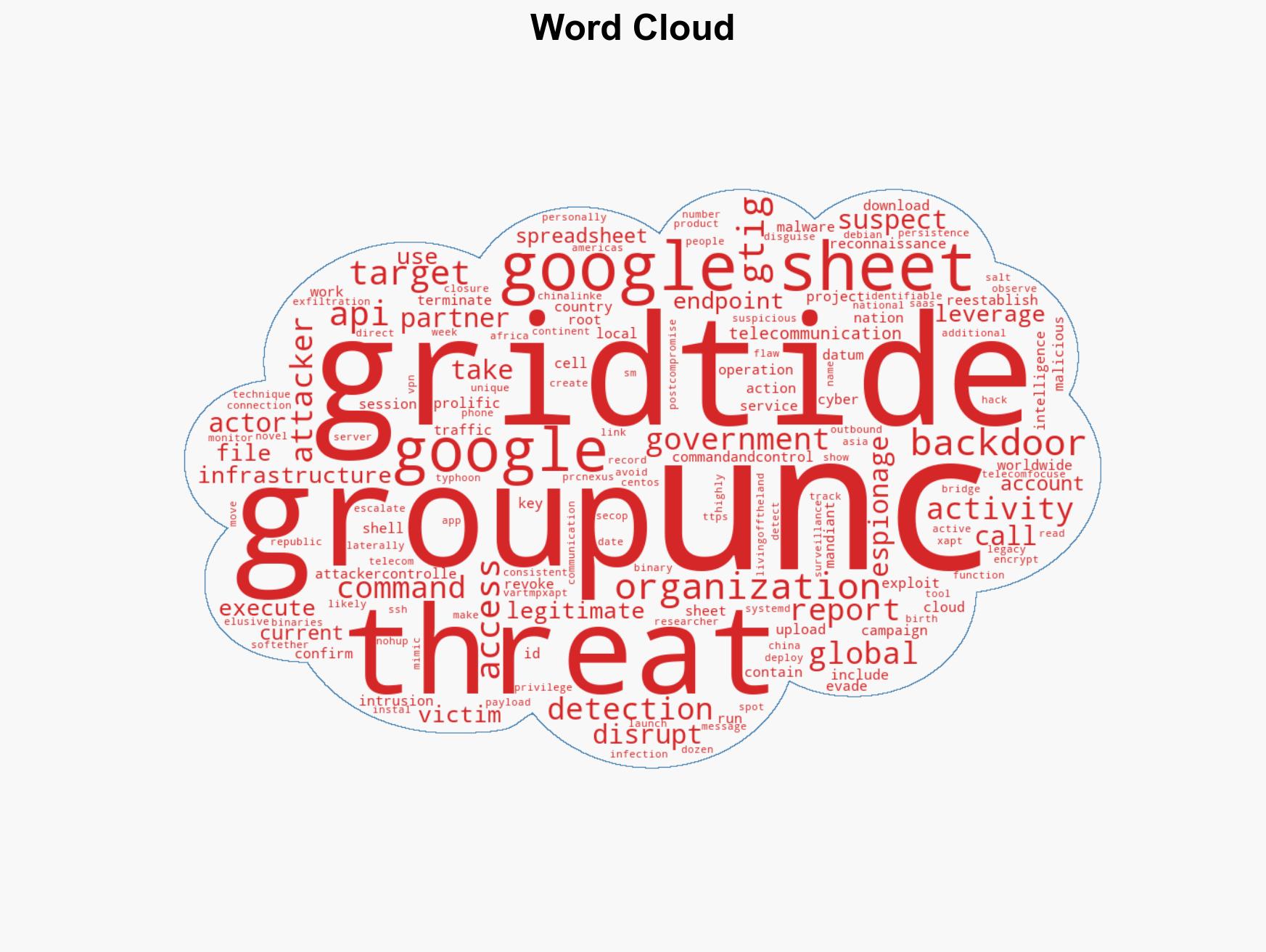
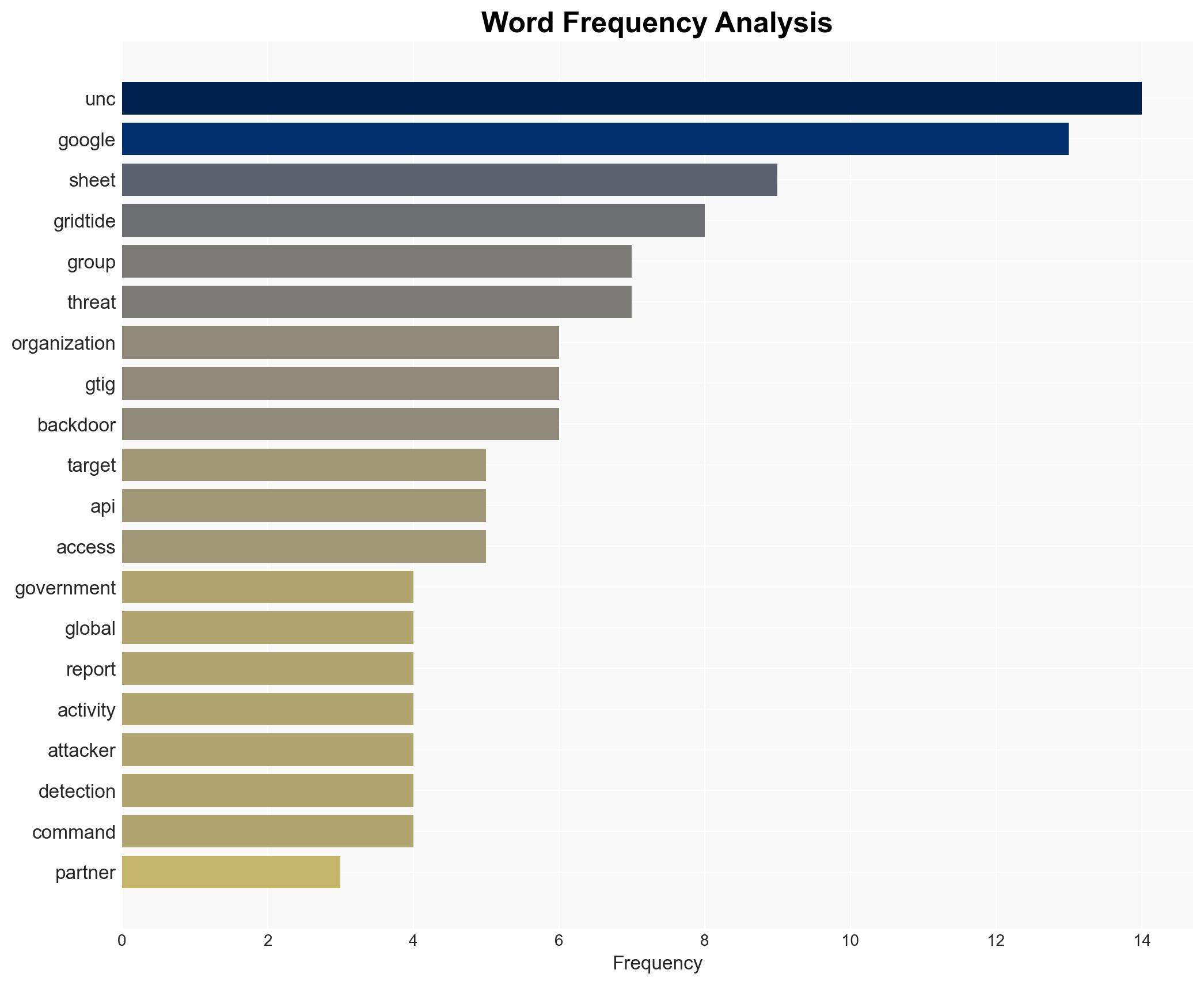
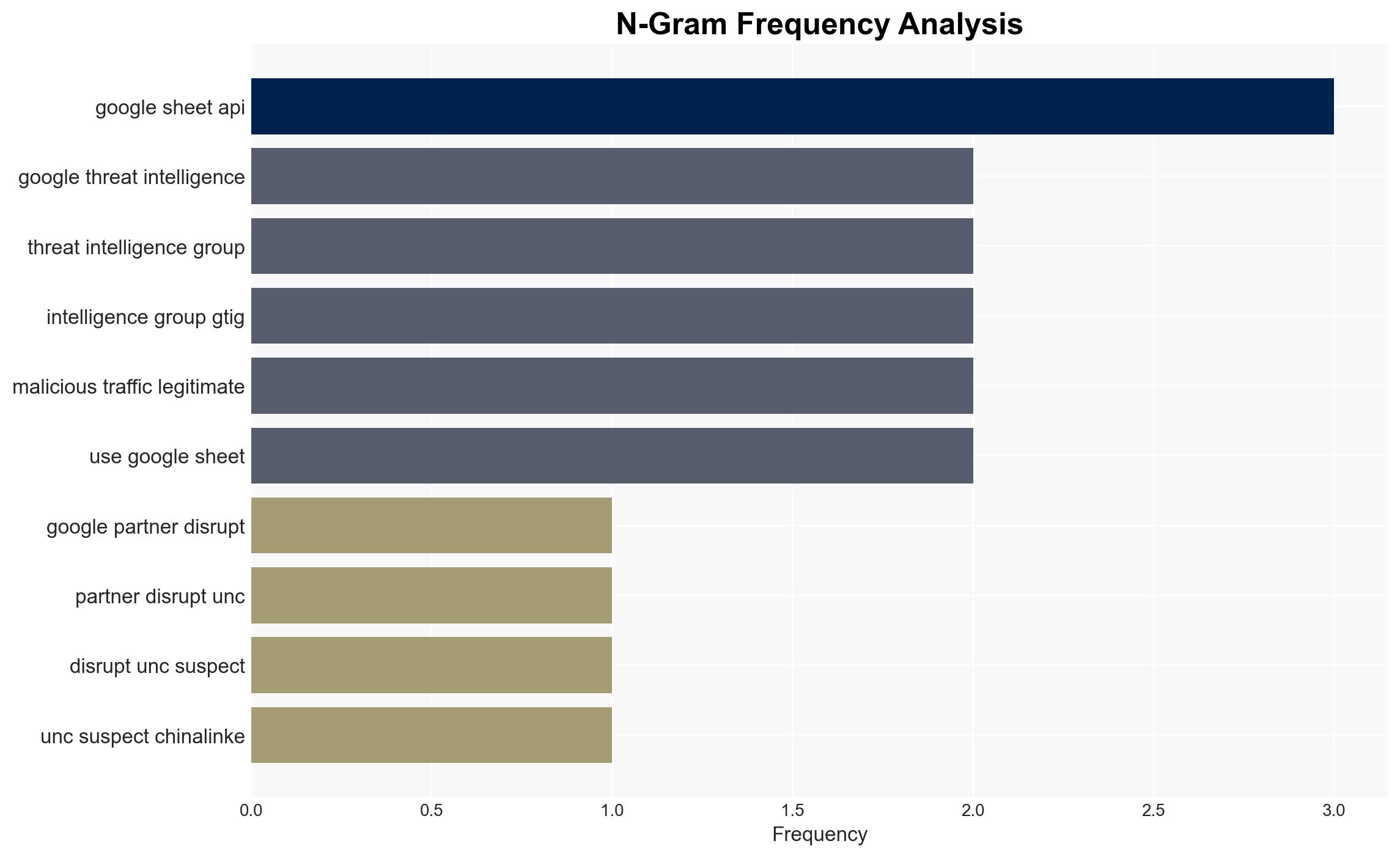
Google GTIG and partners dismantle UNC2814, a China-linked group targeting 53 organizations globally.
Published on: 2026-02-26
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Google GTIG disrupted China-linked APT UNC2814 halting attacks on 53 orgs in 42 countries
1. BLUF (Bottom Line Up Front)
Google GTIG, in collaboration with Mandiant and other partners, successfully disrupted the cyber espionage activities of UNC2814, a suspected China-linked APT group. This group targeted 53 organizations across 42 countries, focusing on government and telecommunications sectors. The most likely hypothesis is that UNC2814 is part of a broader PRC cyber espionage strategy. Overall confidence in this assessment is moderate due to existing information gaps and potential biases.
2. Competing Hypotheses
- Hypothesis A: UNC2814 is a state-sponsored cyber espionage group linked to the PRC, conducting operations to gather intelligence from government and telecom sectors globally. This is supported by the group’s sophisticated techniques and targeting patterns, but lacks direct attribution evidence.
- Hypothesis B: UNC2814 is an independent cybercriminal group using PRC-related tactics for financial gain or other non-state objectives. While the use of advanced techniques suggests state-level capabilities, the absence of direct evidence linking them to the PRC leaves room for alternative motives.
- Assessment: Hypothesis A is currently better supported due to the strategic targeting of government and telecom sectors, consistent with state-sponsored espionage objectives. However, confirmation of state sponsorship would require further evidence, such as direct attribution or insider information.
3. Key Assumptions and Red Flags
- Assumptions: UNC2814’s operations are aligned with PRC strategic interests; the use of sophisticated techniques indicates state-level support; disruption efforts will temporarily degrade UNC2814’s capabilities.
- Information Gaps: Direct evidence linking UNC2814 to the PRC government; comprehensive understanding of UNC2814’s full operational scope and objectives.
- Bias & Deception Risks: Potential bias in attributing cyber activities to state actors without conclusive evidence; risk of UNC2814 using deception tactics to mislead attribution efforts.
4. Implications and Strategic Risks
The disruption of UNC2814’s operations may lead to temporary setbacks for PRC-linked cyber espionage efforts, but could also prompt adaptive strategies and increased sophistication in future attacks.
- Political / Geopolitical: Potential escalation in cyber tensions between the PRC and affected nations; increased scrutiny and diplomatic pressure on the PRC.
- Security / Counter-Terrorism: Heightened awareness and improved defenses in targeted sectors; potential for retaliatory cyber actions by the PRC.
- Cyber / Information Space: Evolution of cyber tactics and techniques; increased collaboration among cybersecurity entities to counter similar threats.
- Economic / Social: Potential economic impacts on targeted organizations; increased public awareness and concern over cyber threats.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of telecommunications and government networks; share threat intelligence with international partners; conduct security audits and patch vulnerabilities.
- Medium-Term Posture (1–12 months): Develop resilience measures and incident response capabilities; strengthen international cybersecurity partnerships; invest in threat intelligence and analysis capabilities.
- Scenario Outlook:
- Best: Successful international collaboration leads to sustained disruption of UNC2814 and similar groups.
- Worst: UNC2814 adapts and escalates attacks, causing significant geopolitical tensions and economic damage.
- Most-Likely: UNC2814 regroups and modifies tactics, leading to ongoing but reduced threat levels.
6. Key Individuals and Entities
- Google Threat Intelligence Group (GTIG)
- Mandiant
- UNC2814
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, cyber-espionage, PRC, telecommunications, government, APT, international collaboration
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us