Google GTIG Reports 90 Zero-Day Vulnerabilities Exploited in 2025, Highlighting Shift Toward Enterprise Targe…
Published on: 2026-03-06
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Google GTIG 90 zero-day flaws exploited in 2025 as enterprise targets grow
1. BLUF (Bottom Line Up Front)
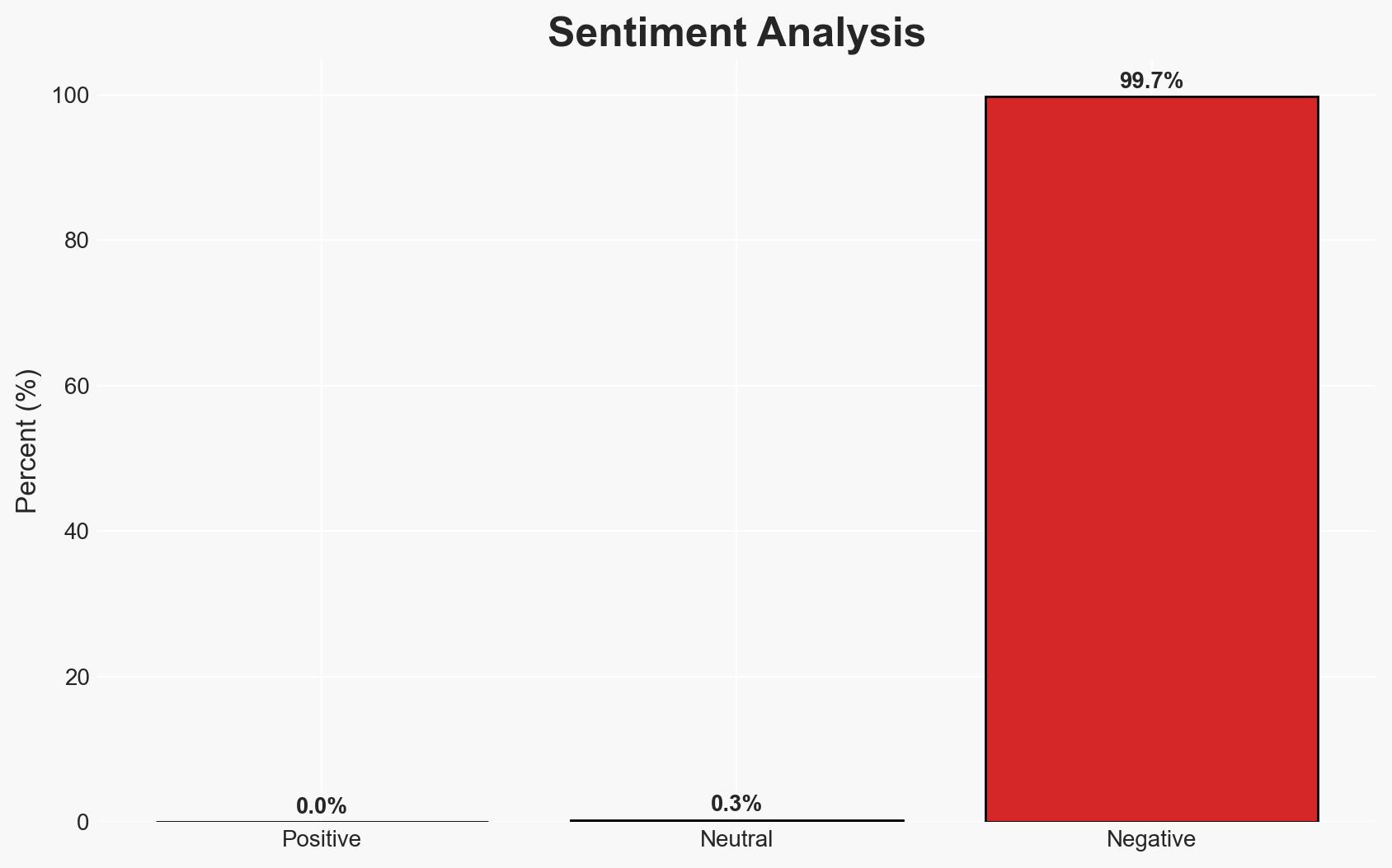
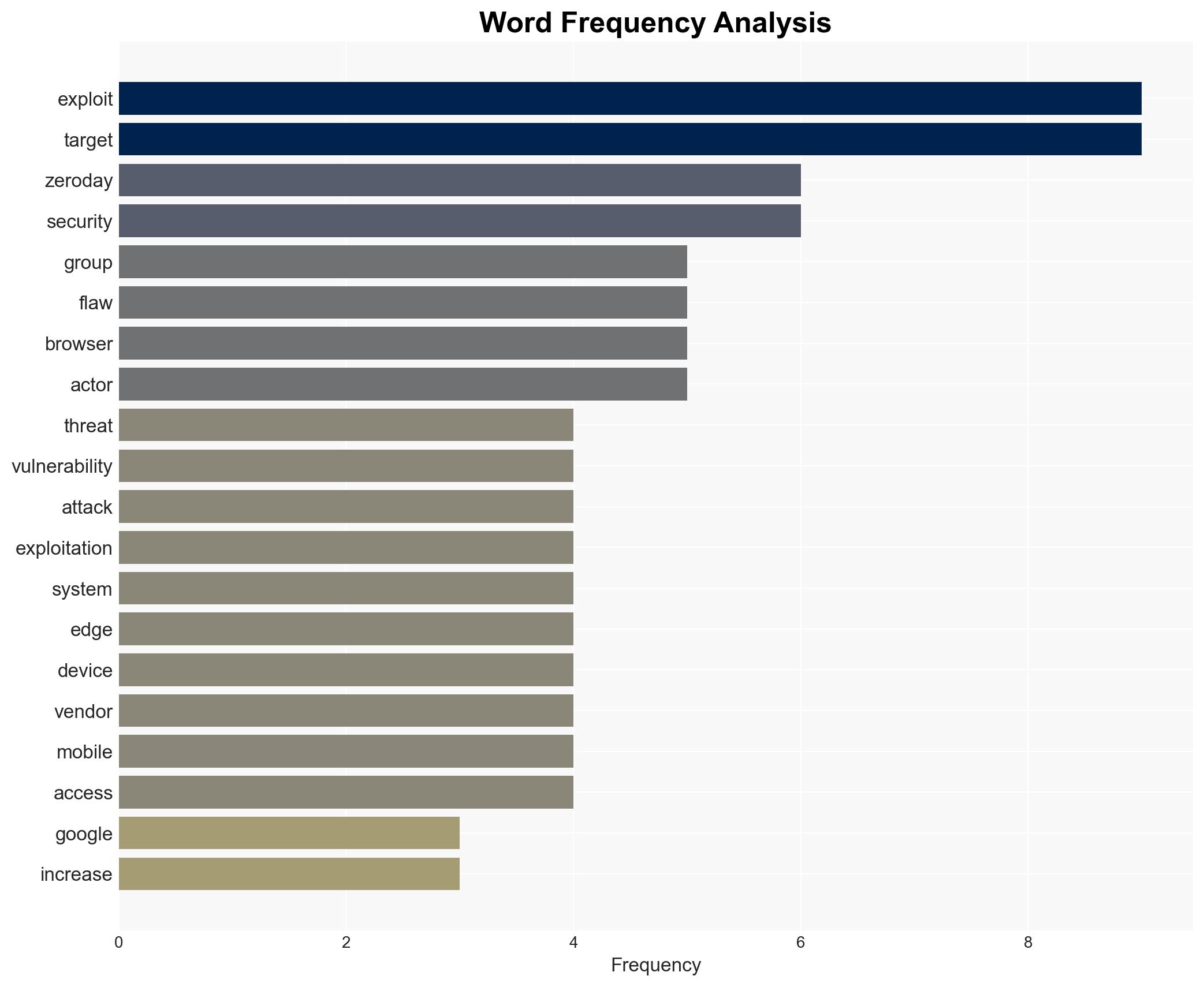
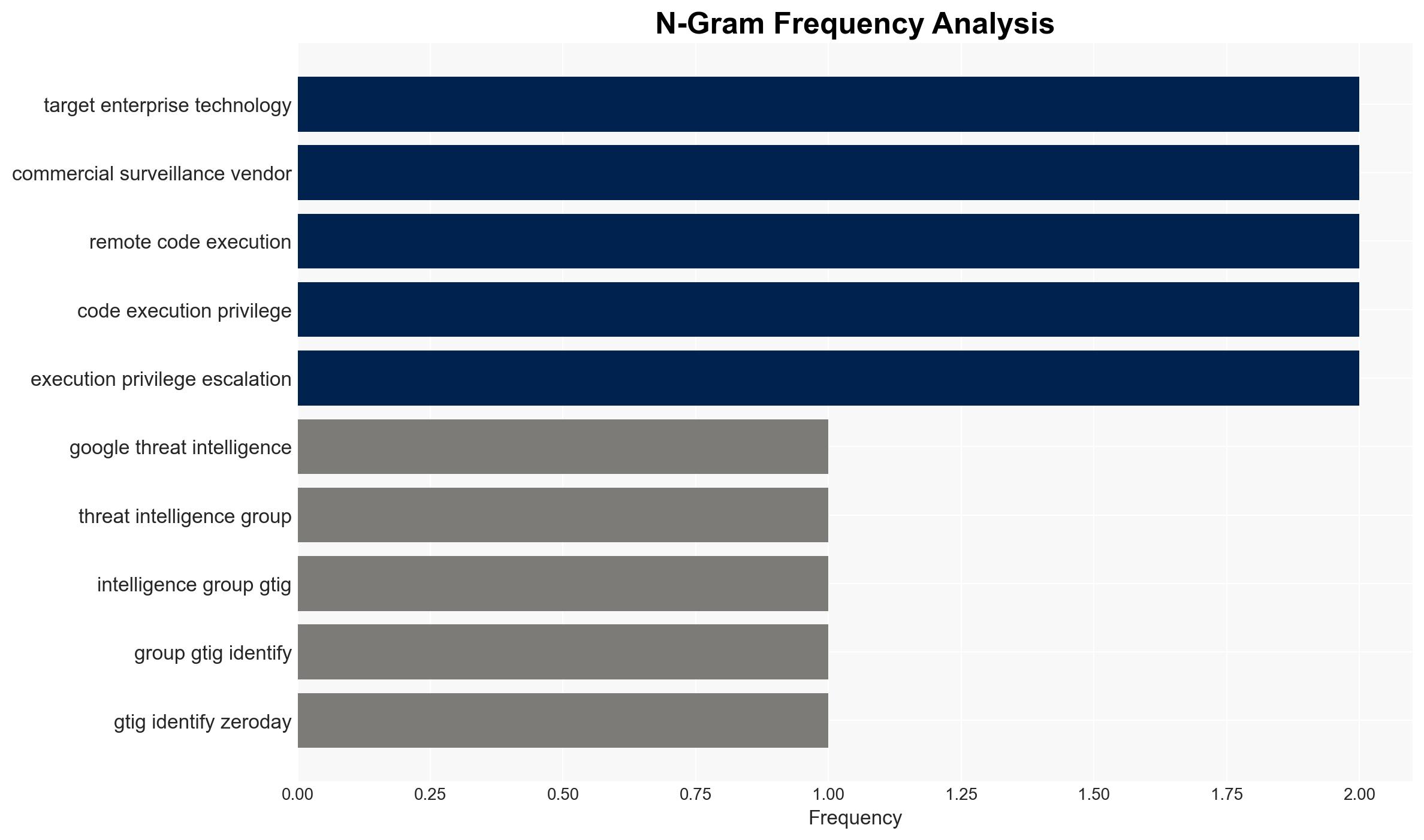
The exploitation of 90 zero-day vulnerabilities in 2025, primarily targeting enterprise technologies, indicates a strategic shift towards corporate infrastructure attacks. The rise in exploits by commercial surveillance vendors surpassing state-sponsored groups marks a significant change in the threat landscape. This development poses heightened risks to major tech vendors and security firms. Overall confidence in this assessment is moderate, given the evolving nature of threat actor tactics and incomplete data on specific exploitations.
2. Competing Hypotheses
- Hypothesis A: The increase in zero-day vulnerabilities targeting enterprises is primarily driven by commercial surveillance vendors seeking to exploit corporate data for financial gain. Supporting evidence includes the noted rise in CSV activity and their surpassing of nation-state actors. However, the full extent of CSV motivations and targets remains uncertain.
- Hypothesis B: Nation-state actors are the primary drivers behind the increase in enterprise-targeted zero-days, aiming to compromise critical infrastructure for geopolitical advantage. This is supported by the continued activity of China-linked groups targeting edge devices. Contradictory evidence includes the higher activity levels of CSVs in 2025.
- Assessment: Hypothesis A is currently better supported due to the explicit mention of CSVs surpassing state actors in zero-day exploitation. Key indicators that could shift this judgment include new data on state-sponsored group activities or shifts in CSV targeting patterns.
3. Key Assumptions and Red Flags
- Assumptions: CSVs have the capability and intent to exploit zero-days for financial gain; nation-state actors will continue to target critical infrastructure; major tech vendors remain primary targets due to their user base.
- Information Gaps: Detailed attribution of specific zero-day exploits to actors; comprehensive data on the impact of these exploits on targeted enterprises.
- Bias & Deception Risks: Potential bias in reporting from commercial entities; manipulation by threat actors to obscure attribution or intent.
4. Implications and Strategic Risks
The trend of increasing zero-day exploits targeting enterprises could lead to more sophisticated cyber-attacks on critical infrastructure, impacting national security and economic stability. This development may also drive international tensions if state actors are implicated.
- Political / Geopolitical: Escalation of cyber tensions between nation-states, particularly involving China-linked groups.
- Security / Counter-Terrorism: Increased vulnerability of critical infrastructure and potential for disruptive attacks.
- Cyber / Information Space: Enhanced complexity of cyber defense strategies required for enterprises and governments.
- Economic / Social: Potential for economic disruption and loss of consumer trust in major tech vendors.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of enterprise networks for zero-day exploit indicators; collaborate with tech vendors for patch development and deployment.
- Medium-Term Posture (1–12 months): Develop partnerships with international cyber defense organizations; invest in advanced threat detection and response capabilities.
- Scenario Outlook:
- Best: Successful mitigation of zero-day threats through coordinated international efforts.
- Worst: Major cyber-attack on critical infrastructure leading to significant economic and social disruption.
- Most-Likely: Continued rise in zero-day exploits with incremental improvements in defense mechanisms.
6. Key Individuals and Entities
- Google Threat Intelligence Group (GTIG)
- Intellexa
- Cisco
- Fortinet
- Ivanti
- VMware
- FIN11
- Clop ransomware group
- China-linked cyber-espionage groups
7. Thematic Tags
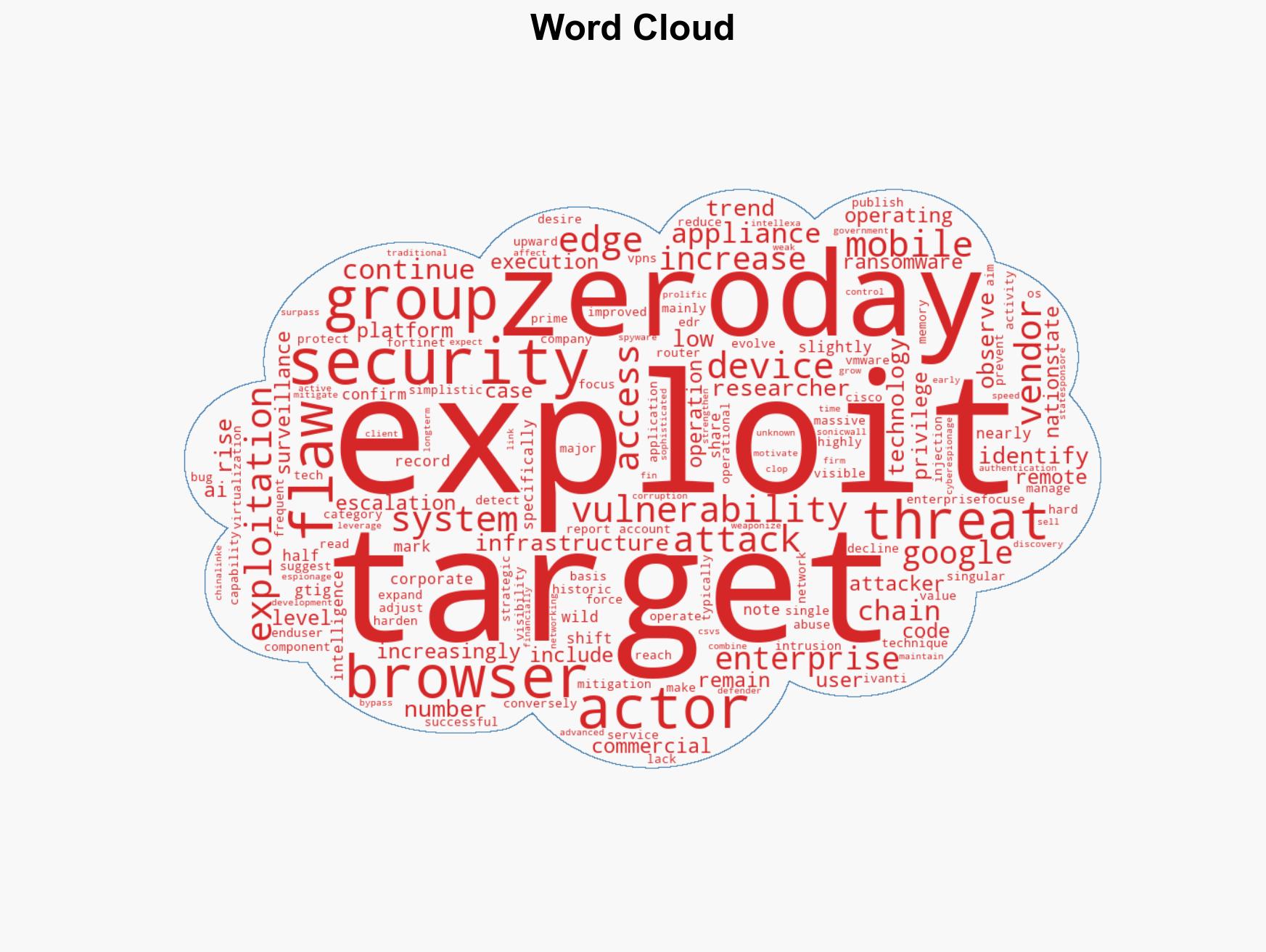
cybersecurity, zero-day vulnerabilities, enterprise security, cyber-espionage, commercial surveillance, critical infrastructure, nation-state actors, cybersecurity strategy
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us