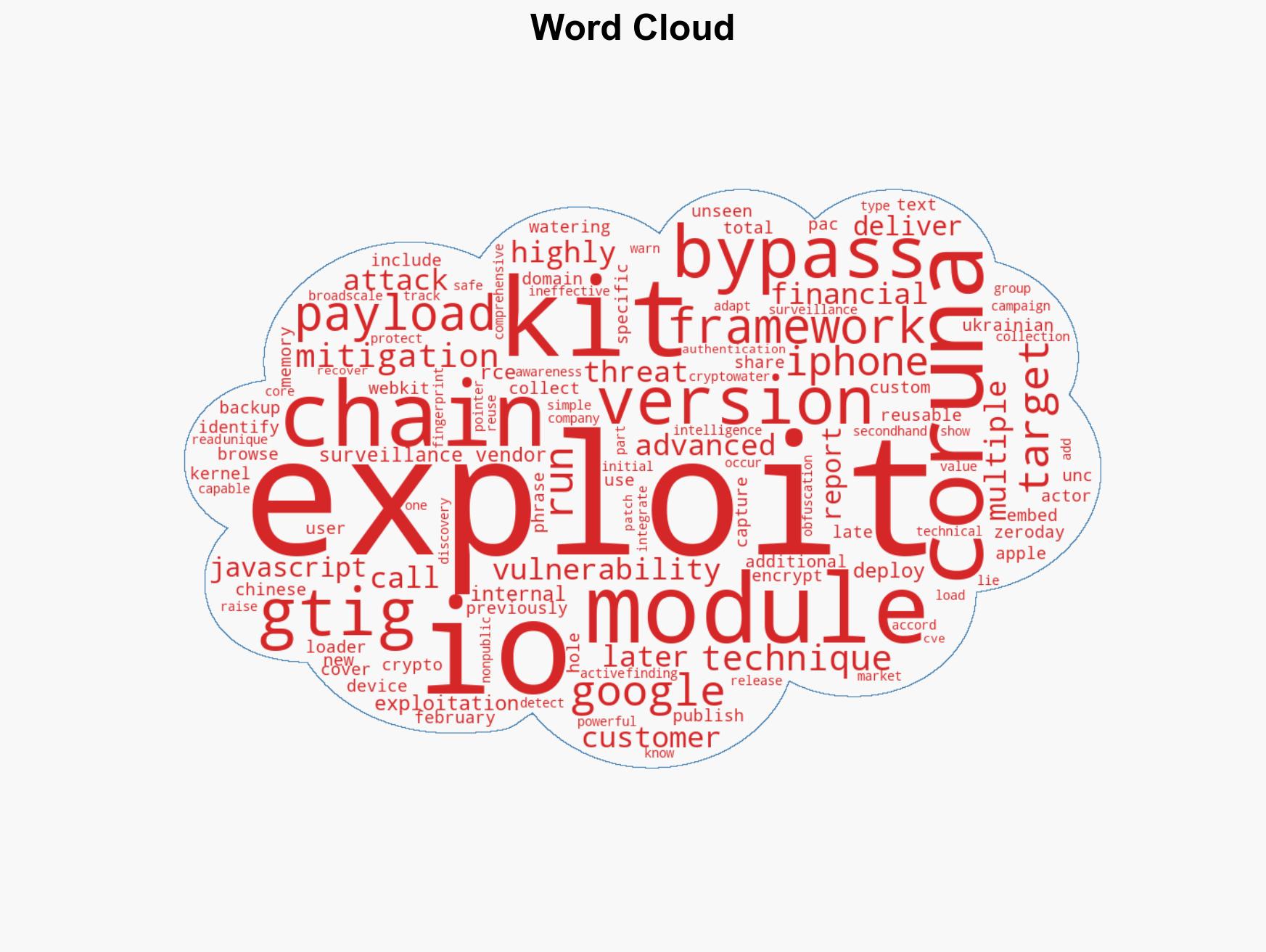
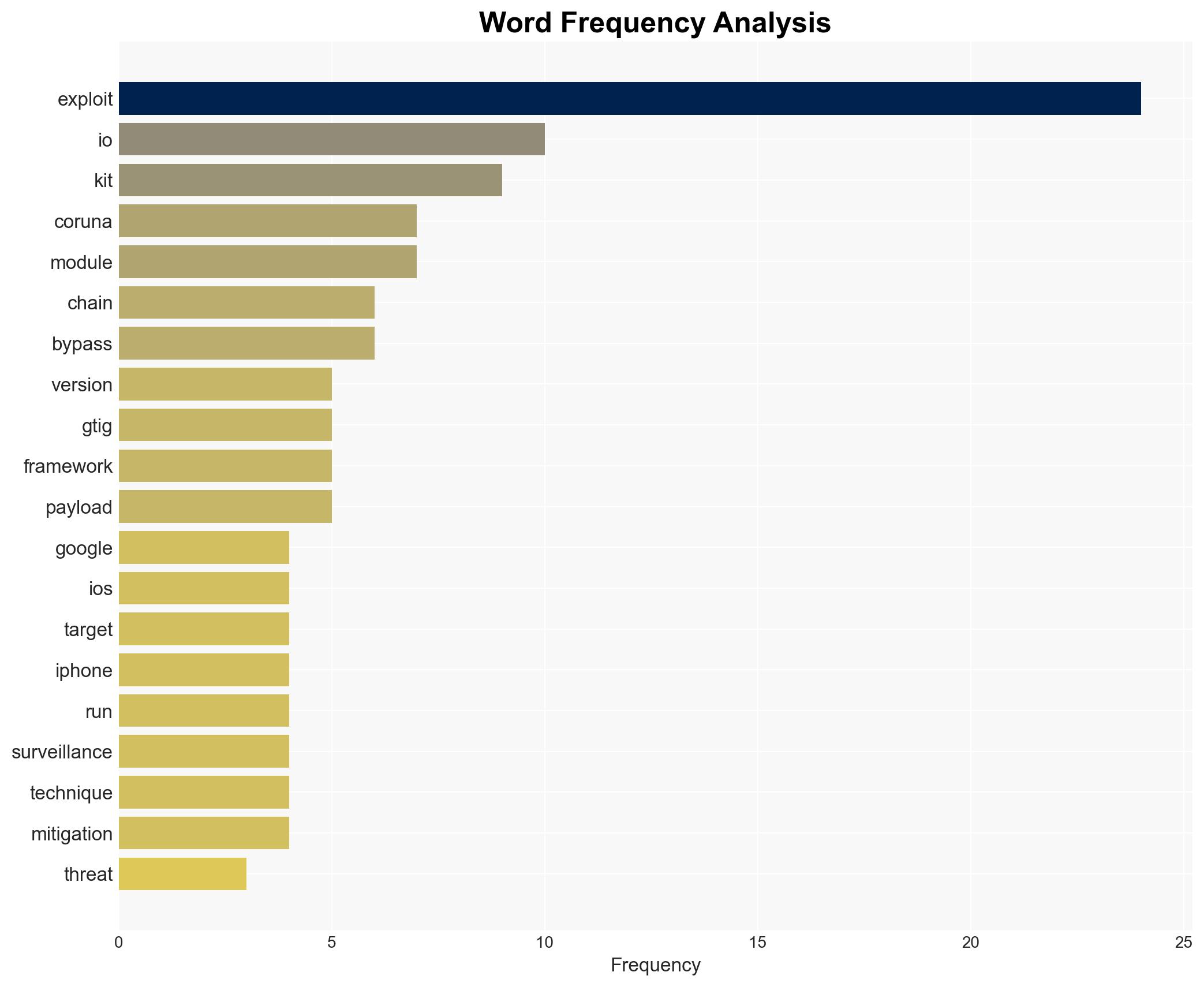
Google identifies Coruna iOS exploit kit targeting iPhones on iOS 13.0 to 17.2.1, excluding latest version.
Published on: 2026-03-05
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Google uncovers Coruna iOS Exploit Kit targeting iOS 131721
1. BLUF (Bottom Line Up Front)
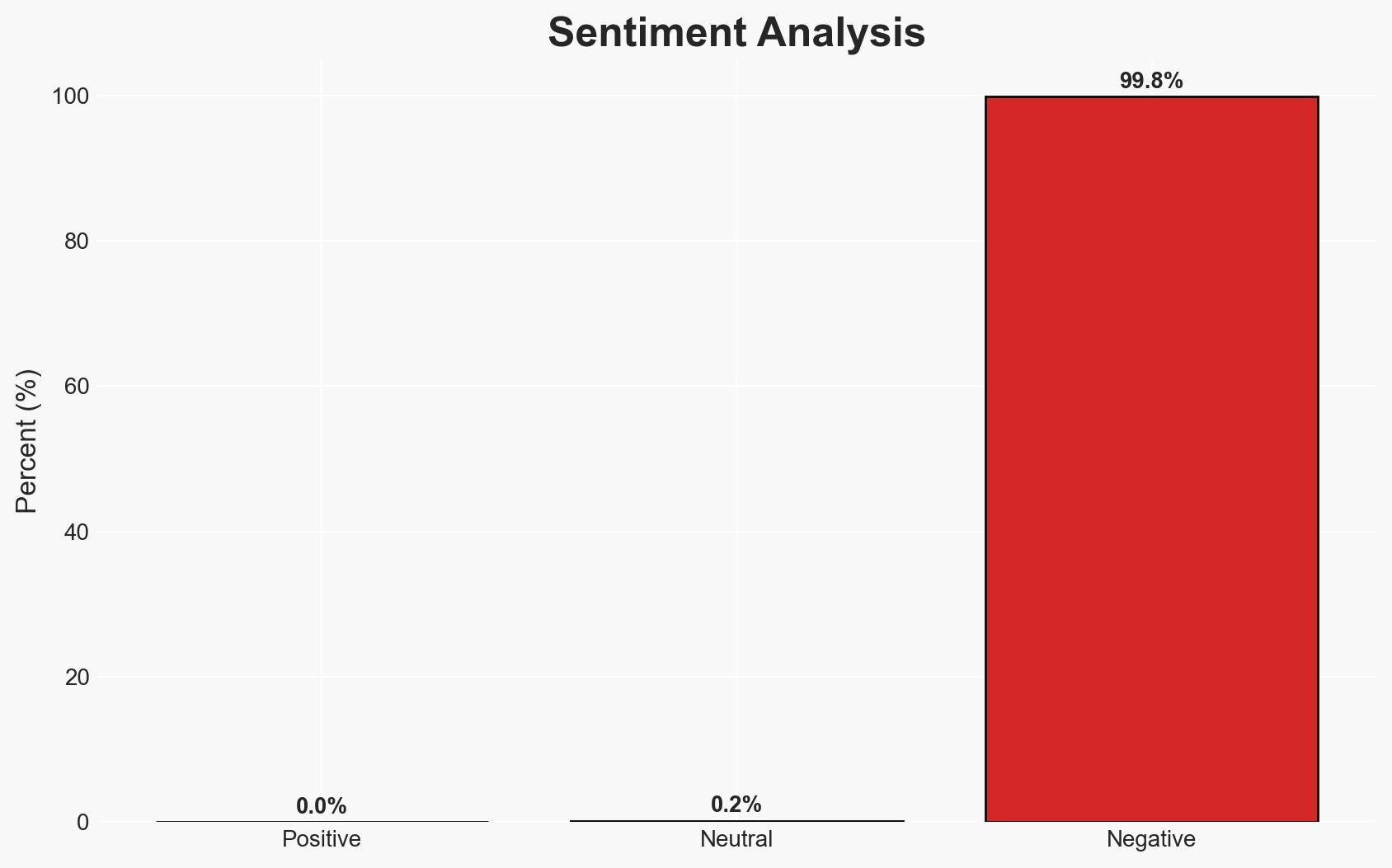
The Coruna iOS exploit kit poses a significant threat to iPhones running iOS 13 through 17.2.1, with evidence of its use by multiple threat actors, including state-backed entities. The kit’s ineffectiveness against the latest iOS version suggests an urgent need for users to update their devices. This assessment is made with moderate confidence due to the detailed technical analysis provided by Google’s Threat Intelligence Group (GTIG).
2. Competing Hypotheses
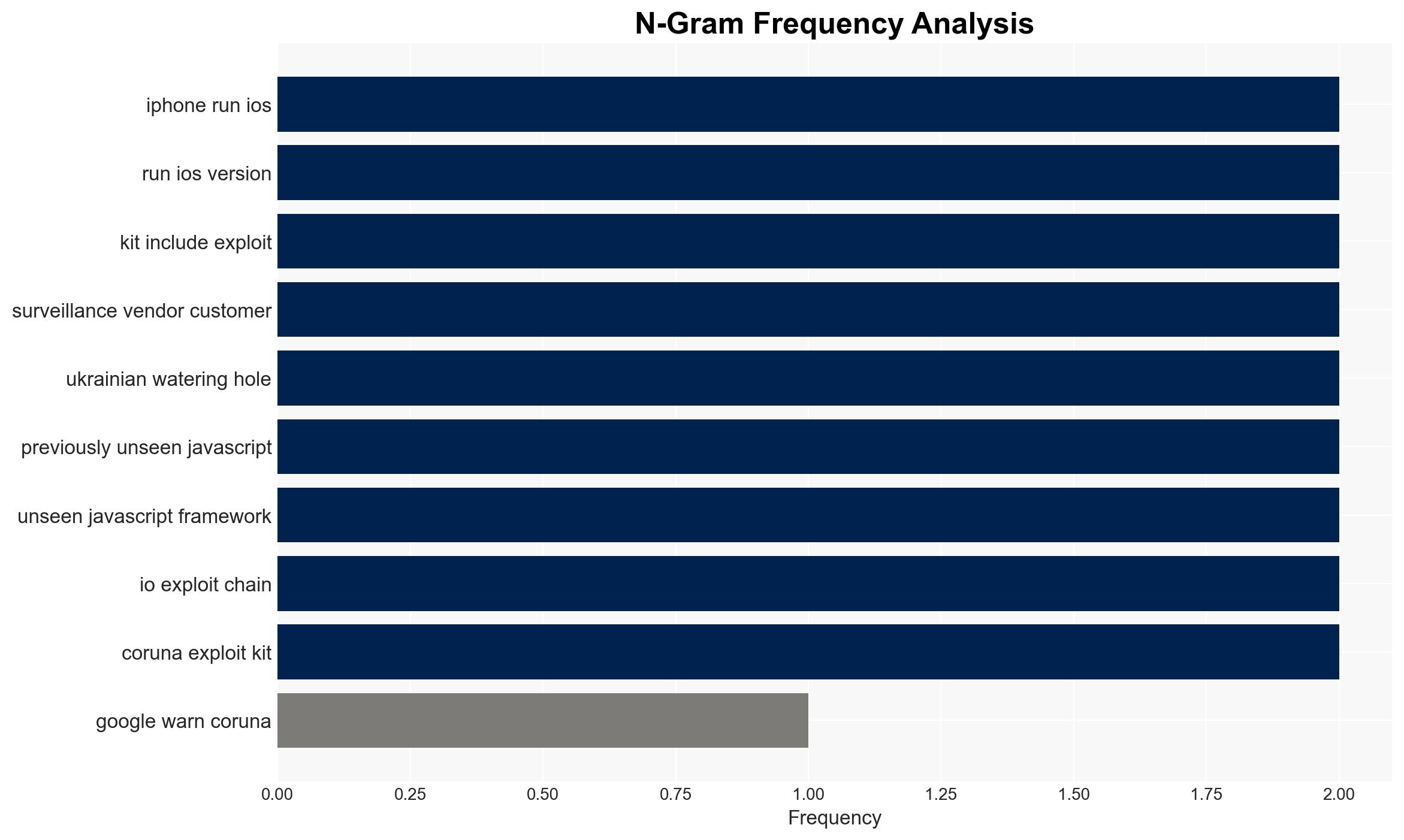
- Hypothesis A: The Coruna exploit kit is primarily used by state-backed actors for targeted surveillance and espionage. This is supported by its use in Ukrainian watering hole attacks and the involvement of a surveillance vendor’s customer. However, the broad-scale deployment by Chinese financial threat actors suggests a wider application.
- Hypothesis B: The Coruna exploit kit is a commercially available tool used by various actors for both targeted and opportunistic attacks. The reuse and adaptation of the kit by different threat actors, including financial scammers, support this hypothesis, but the initial discovery in a surveillance context complicates the assessment.
- Assessment: Hypothesis B is currently better supported due to the diversity of actors and contexts in which the kit has been deployed. Key indicators that could shift this judgment include further evidence of state sponsorship or exclusive use by government entities.
3. Key Assumptions and Red Flags
- Assumptions: The Coruna kit’s ineffectiveness against the latest iOS version will persist; GTIG’s technical findings are accurate and comprehensive; the identified threat actors are correctly attributed.
- Information Gaps: The full extent of the kit’s distribution and the identities of all actors using it remain unclear. Details on the surveillance vendor’s customer and their objectives are lacking.
- Bias & Deception Risks: Potential bias in attributing attacks to state-backed actors; possible deception by threat actors to obscure true intentions or affiliations.
4. Implications and Strategic Risks
The Coruna exploit kit’s proliferation could lead to increased cyber threats against iOS users, particularly in geopolitical hotspots. Its use by diverse actors suggests a growing market for sophisticated exploits.
- Political / Geopolitical: Potential escalation in cyber tensions, particularly involving state-backed actors targeting adversaries.
- Security / Counter-Terrorism: Increased risk of surveillance and data breaches, impacting national security and individual privacy.
- Cyber / Information Space: Heightened vulnerability of iOS devices, necessitating rapid patching and awareness campaigns.
- Economic / Social: Potential economic impact from financial scams and loss of consumer trust in device security.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Encourage iOS users to update to the latest version; enhance monitoring of known threat actors; disseminate GTIG’s findings to relevant stakeholders.
- Medium-Term Posture (1–12 months): Develop partnerships with tech companies for rapid threat intelligence sharing; invest in capabilities to detect and mitigate similar threats.
- Scenario Outlook:
- Best: Rapid patching and awareness reduce the kit’s effectiveness, deterring further use.
- Worst: Exploit kit evolves to target newer iOS versions, increasing the threat landscape.
- Most-Likely: Continued use by diverse actors, with periodic updates to exploit newer vulnerabilities.
6. Key Individuals and Entities
- Google’s Threat Intelligence Group (GTIG)
- UNC6353 (Ukrainian watering hole campaign)
- UNC6691 (Chinese financial threat actor)
- Not clearly identifiable from open sources in this snippet for the surveillance vendor’s customer
7. Thematic Tags
cybersecurity, iOS vulnerabilities, state-sponsored threats, surveillance, financial scams, exploit kits, threat intelligence
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us