Google Threat Intel Chief Predicts Global Cyber-Attacks from Iran in Response to US-Israel Strikes
Published on: 2026-03-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Expect Iran to Launch Cyber-Attacks Globally Warns Google Head of Threat Intel
1. BLUF (Bottom Line Up Front)
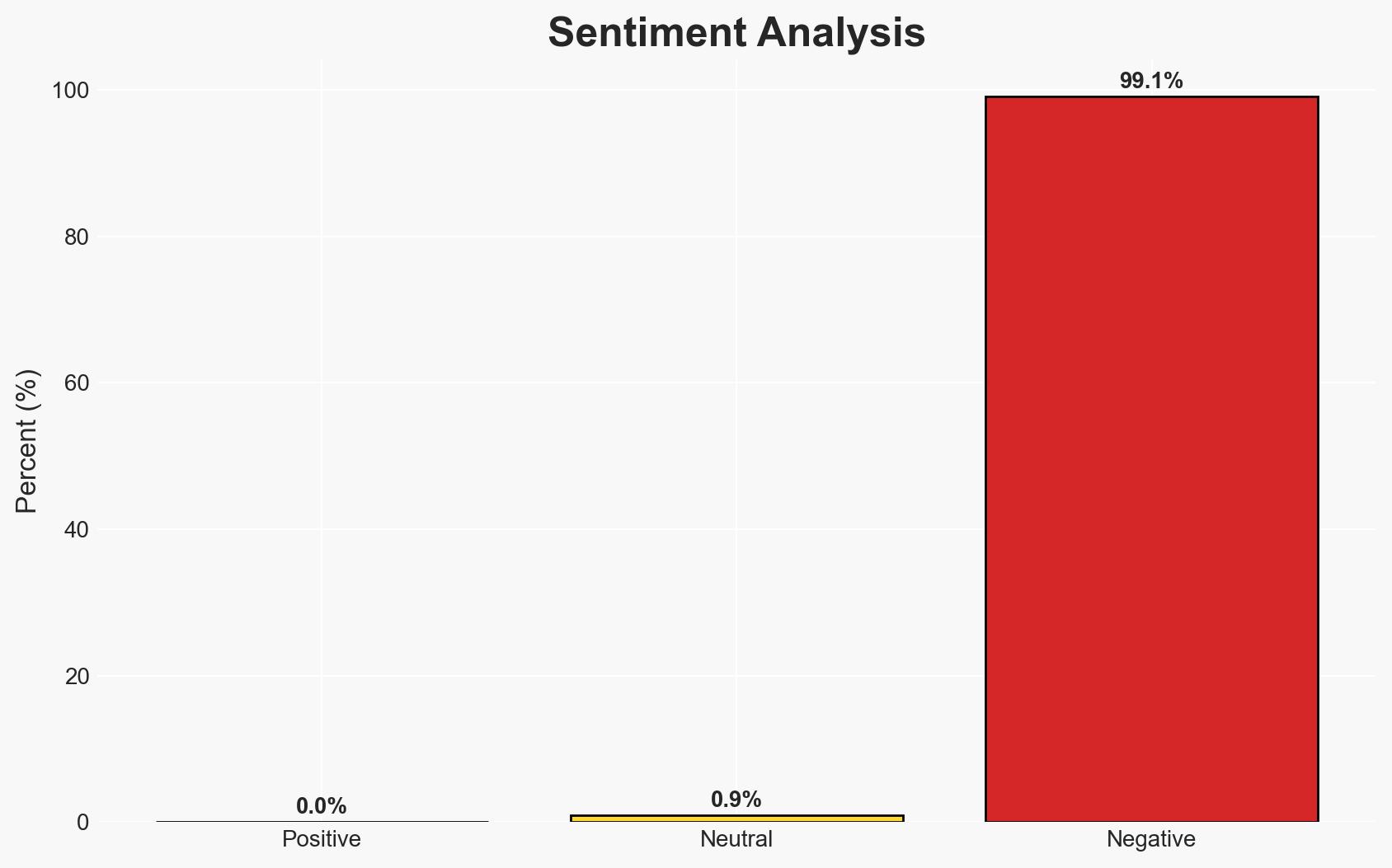
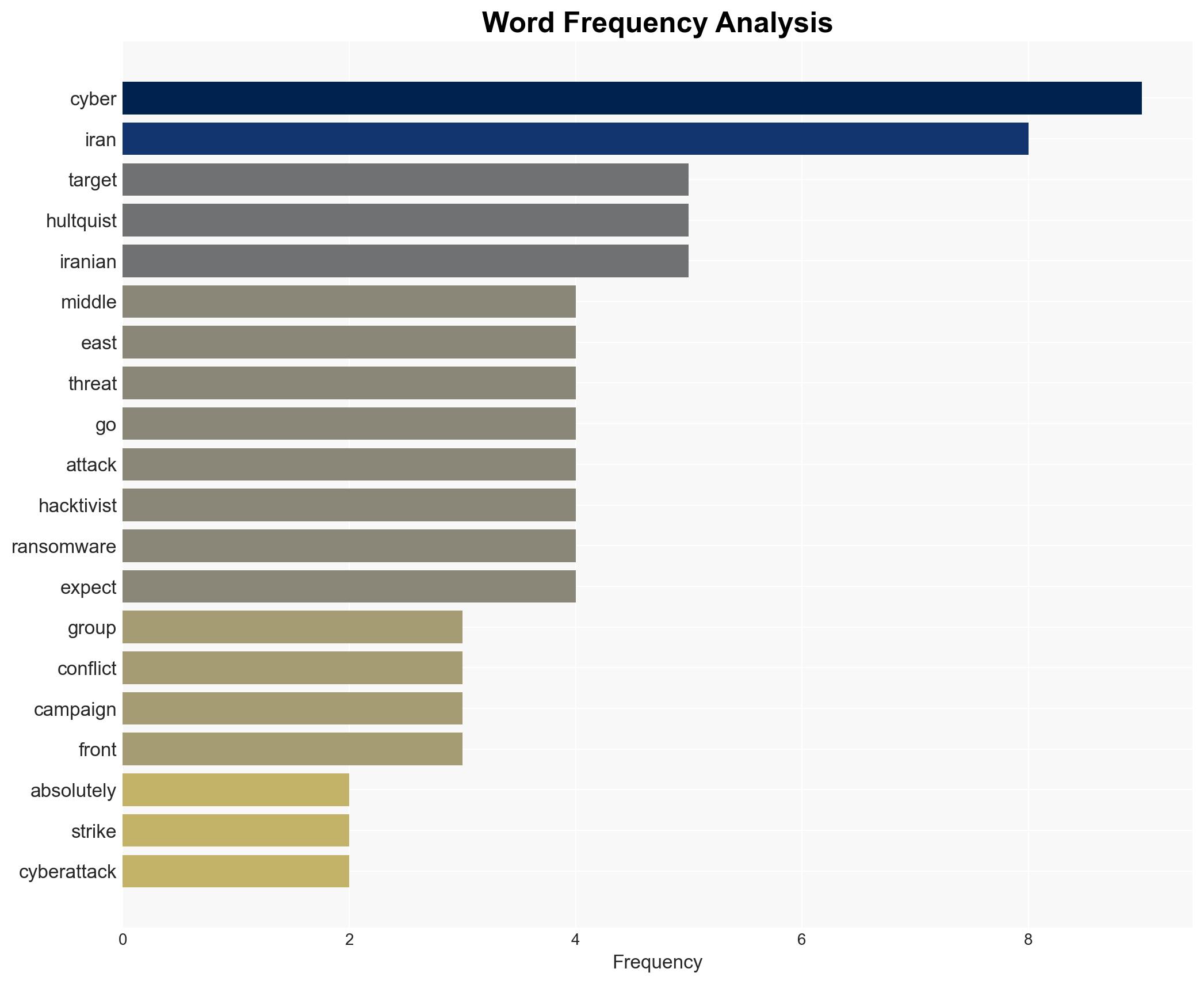
Iran is likely to escalate its cyber operations globally in response to recent US and Israeli military actions, targeting countries with less mature cyber defenses. This assessment is based on historical patterns of Iranian cyber activity and statements by Google’s Threat Intelligence Group. The most likely hypothesis is that Iran will use cyber proxies to conduct these operations, with moderate confidence in this judgment.
2. Competing Hypotheses
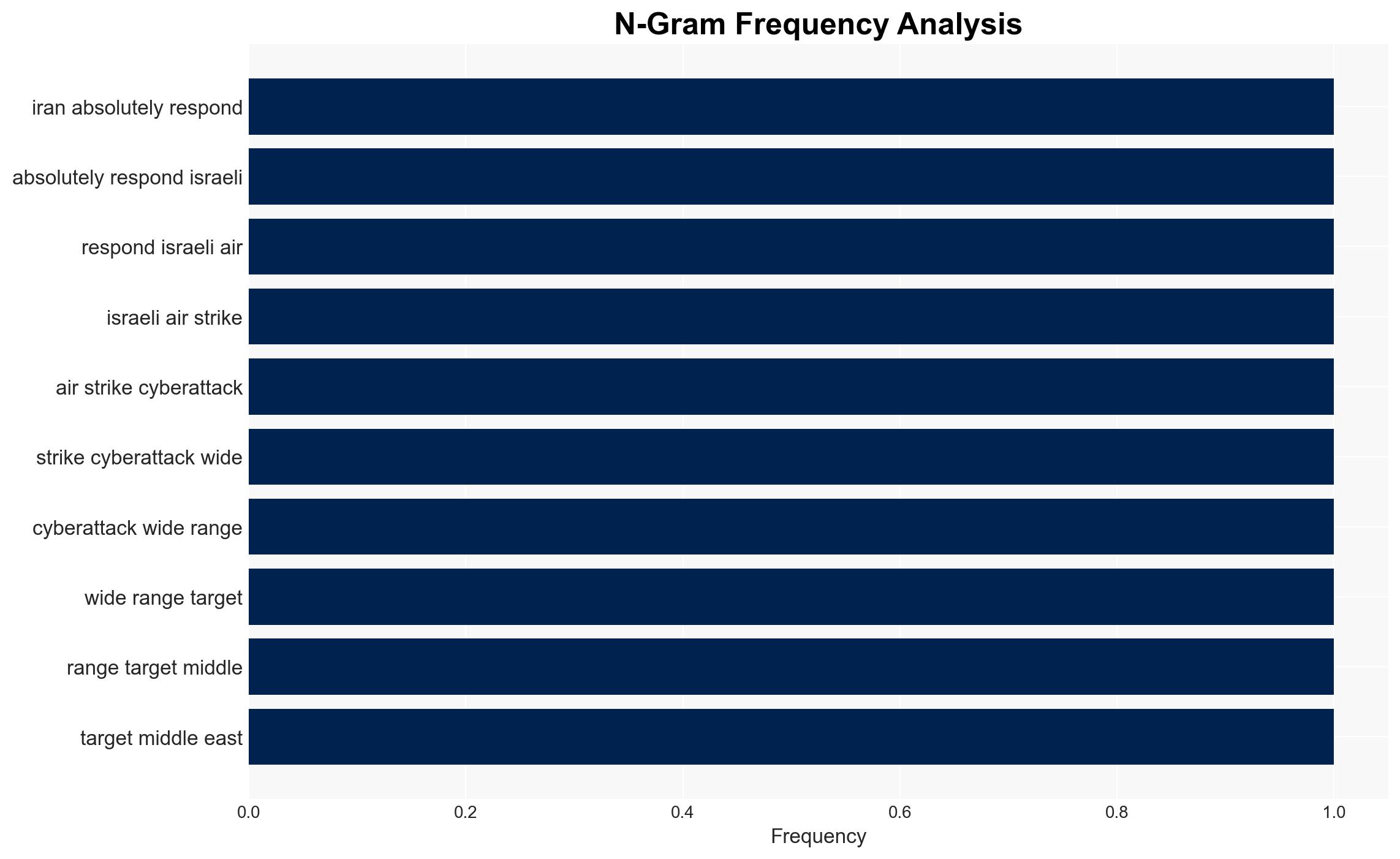
- Hypothesis A: Iran will conduct direct cyber-attacks against US and Israeli interests as retaliation for recent military actions. This is supported by Iran’s history of retaliatory cyber operations. However, the direct attribution risk and potential for escalation may deter such actions.
- Hypothesis B: Iran will utilize cyber proxies, such as hacktivist and ransomware groups, to indirectly target a broader range of countries, including GCC members. This is supported by Iran’s previous use of such tactics and the potential to exploit less defended targets.
- Assessment: Hypothesis B is currently better supported due to Iran’s strategic interest in maintaining plausible deniability while still exerting pressure on its adversaries. Indicators that could shift this judgment include evidence of direct state-sponsored cyber operations or changes in Iran’s geopolitical calculus.
3. Key Assumptions and Red Flags
- Assumptions: Iran will continue to perceive cyber operations as a viable tool for retaliation; GCC countries will remain primary targets due to their hosting of US military bases; Iran’s cyber capabilities remain consistent with past assessments.
- Information Gaps: Detailed intelligence on Iran’s current cyber capabilities and specific targeting intentions; clarity on the extent of coordination between Iranian state actors and cyber proxies.
- Bias & Deception Risks: Potential bias in open-source reporting favoring Western perspectives; risk of Iranian misinformation campaigns to obscure true cyber intentions.
4. Implications and Strategic Risks
This development could lead to increased cyber conflict in the Middle East, potentially drawing in global actors and affecting international cyber norms.
- Political / Geopolitical: Escalation of tensions between Iran and Western-aligned states, potentially impacting diplomatic relations and regional stability.
- Security / Counter-Terrorism: Heightened threat environment for US and allied interests in the Middle East, necessitating increased vigilance and defensive measures.
- Cyber / Information Space: Potential for widespread cyber disruptions affecting critical infrastructure and economic activities in targeted countries.
- Economic / Social: Economic impacts from cyber disruptions, particularly in sectors like finance and energy, could lead to social unrest in affected regions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of Iranian cyber activity, strengthen cyber defenses of critical infrastructure in GCC countries, and increase information sharing among allies.
- Medium-Term Posture (1–12 months): Develop resilience measures, bolster regional cyber partnerships, and invest in capability development to counter cyber threats.
- Scenario Outlook: Best: De-escalation through diplomatic engagement; Worst: Prolonged cyber conflict with significant disruptions; Most-Likely: Continued low-level cyber skirmishes with intermittent escalations.
6. Key Individuals and Entities
- John Hultquist, Chief Analyst, Google Threat Intelligence Group (GTIG)
- Iranian Revolutionary Guard Corps (IRGC)
- Royal United Services Institute (RUSI)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
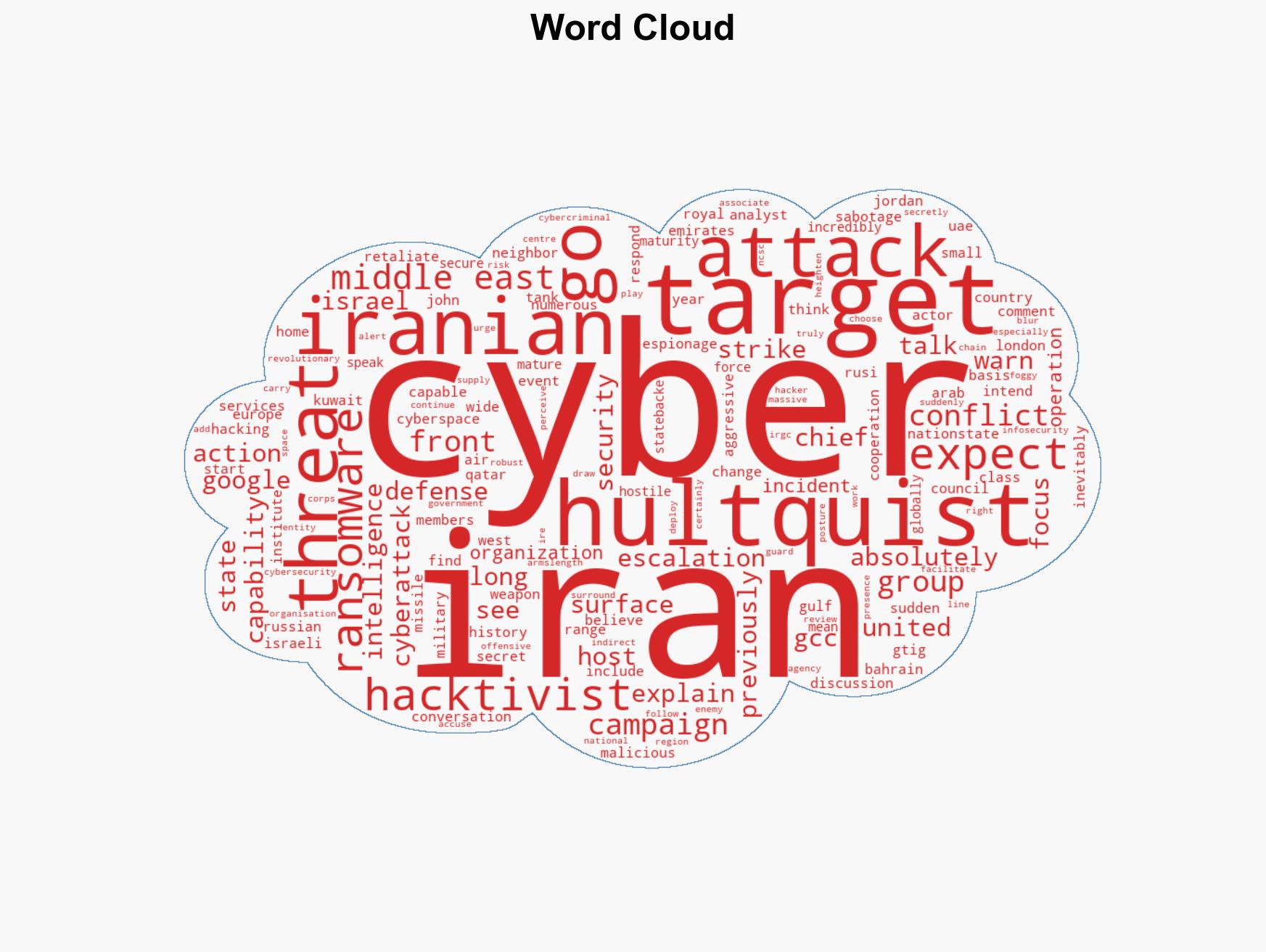
cybersecurity, cyber-attacks, Iranian cyber capabilities, geopolitical tensions, cyber proxies, GCC security, cyber defense, regional stability
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us