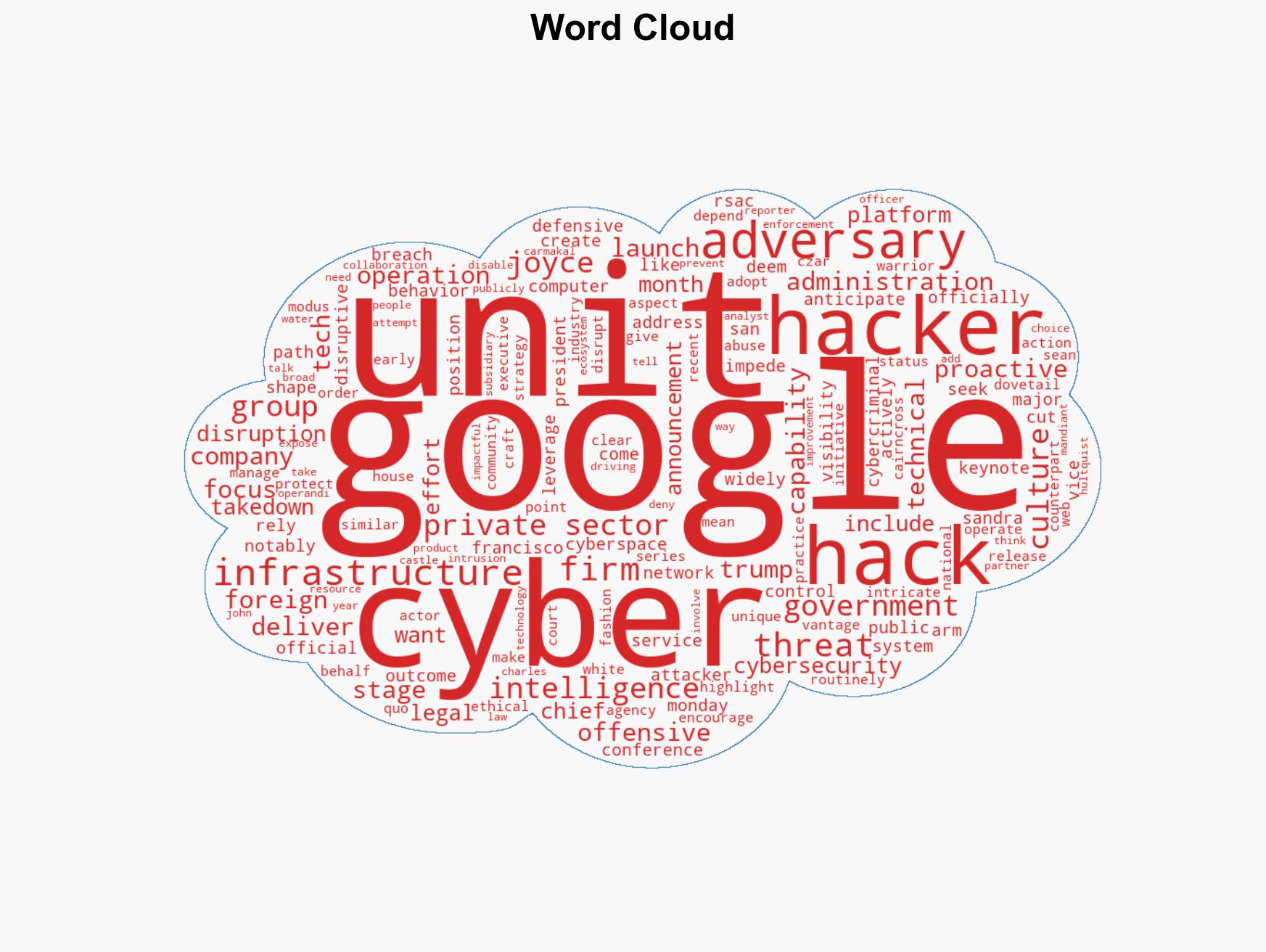
Google unveils cyber disruption unit, emphasizes defensive strategies over offensive tactics
Published on: 2026-03-24
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Google launches threat disruption unit stops short of calling it offensive
1. BLUF (Bottom Line Up Front)
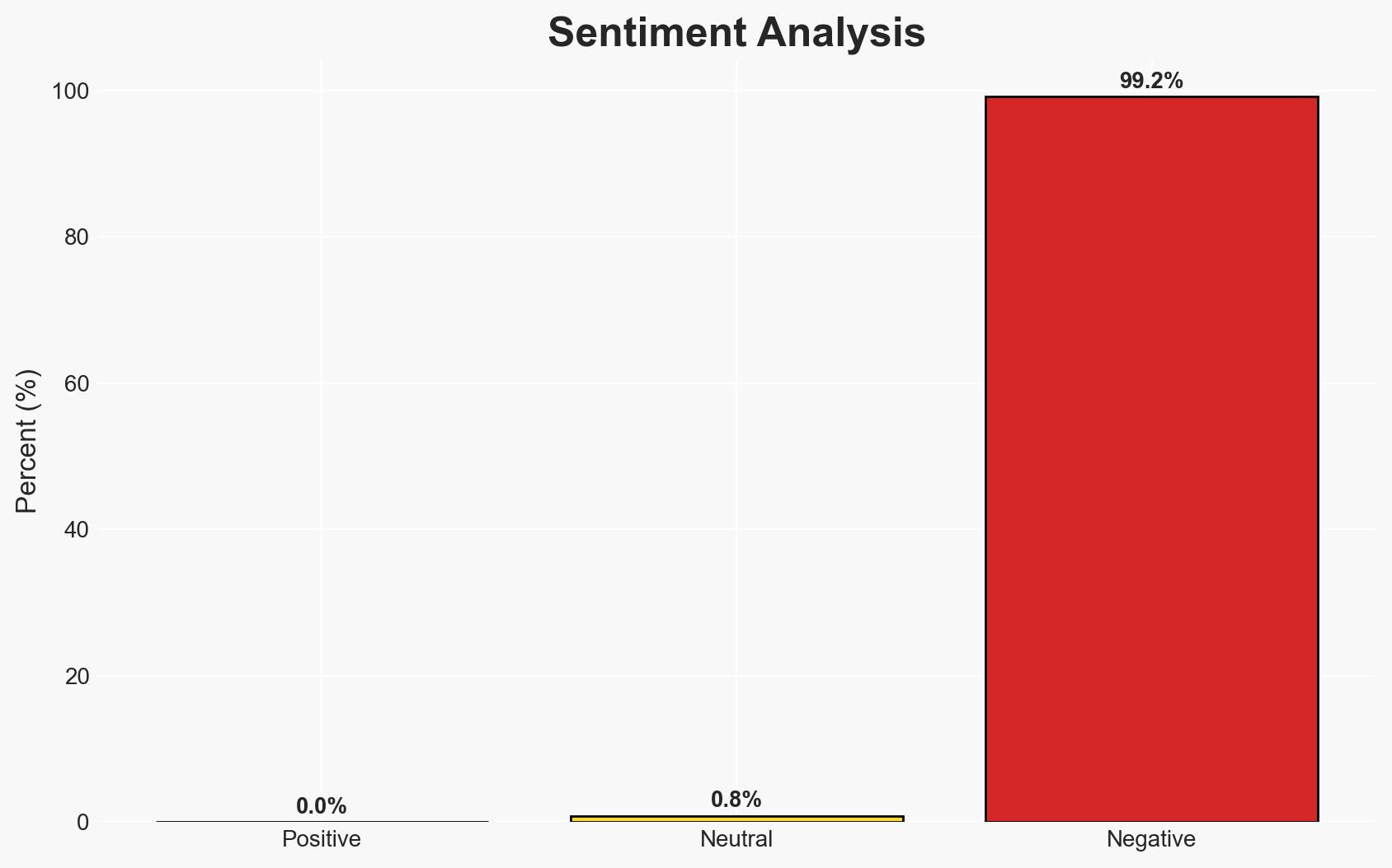
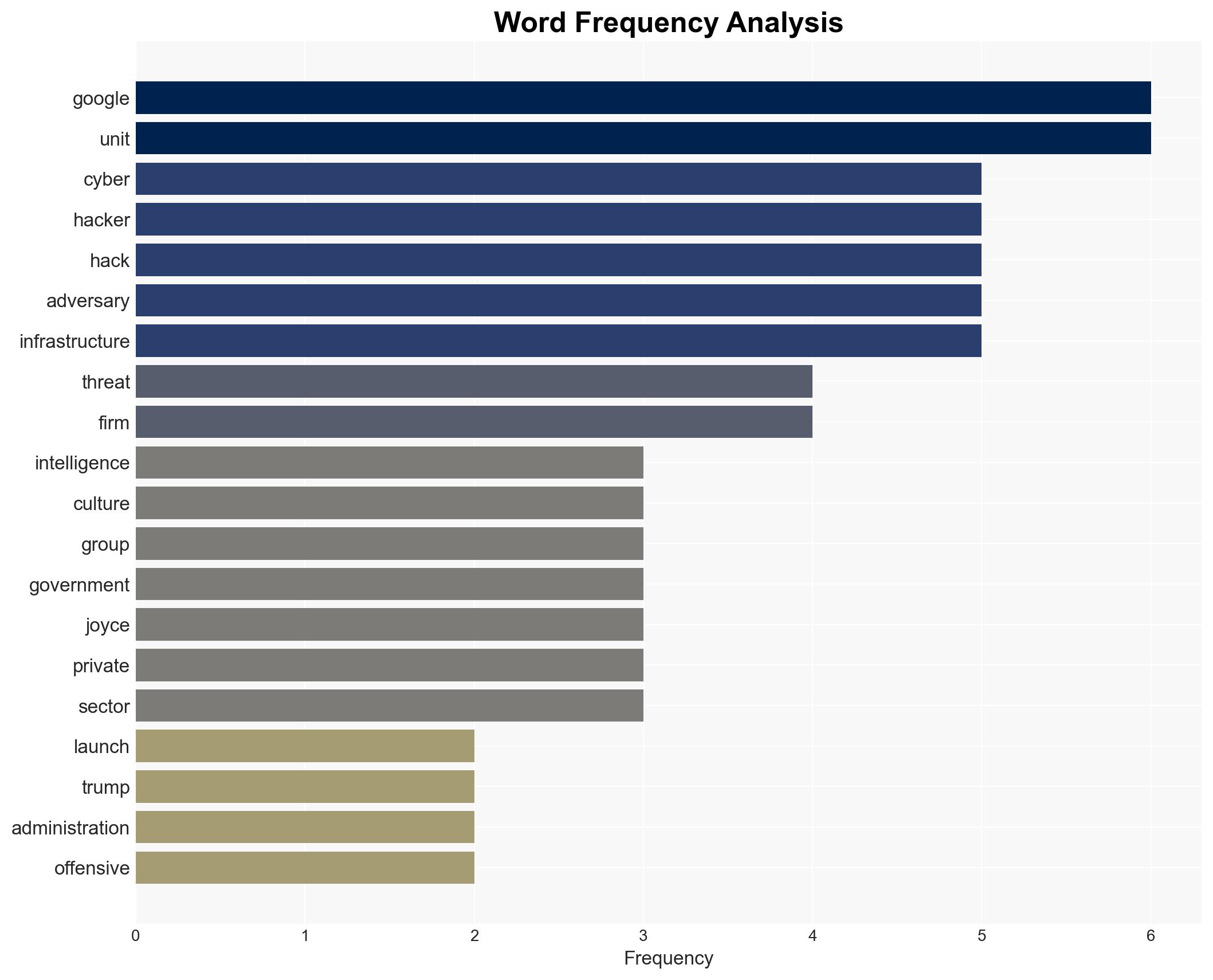
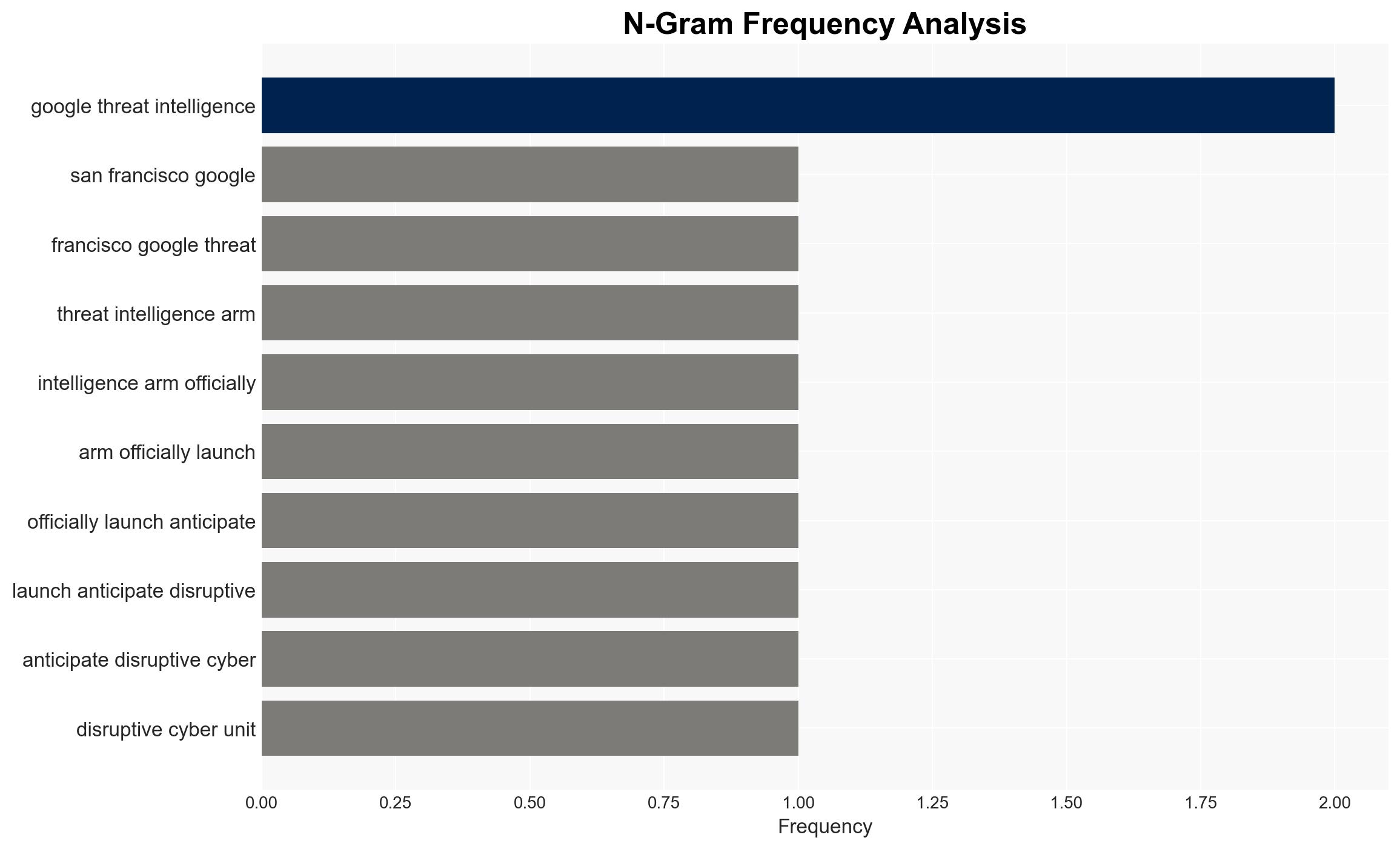
Google has launched a new threat disruption unit aimed at proactively impeding cyber adversaries by disrupting their infrastructure, aligning with a broader trend towards a proactive cyber defense posture. This initiative is framed as defensive, avoiding direct offensive actions, and is likely to influence both private and public sector cybersecurity strategies. Overall confidence in this assessment is moderate, given the limited details on operational specifics and potential impacts.
2. Competing Hypotheses
- Hypothesis A: Google’s unit is primarily a defensive measure aimed at protecting its own infrastructure and users, leveraging legal and ethical means to disrupt cyber threats. Supporting evidence includes statements from Google officials emphasizing defensive actions and legal compliance. Key uncertainties involve the extent of cooperation with government agencies and the actual scope of operations.
- Hypothesis B: The unit may serve as a precursor to more offensive cyber operations, potentially aligning with governmental strategies for a more aggressive cyber posture. This hypothesis is less supported due to explicit denials from Google and the White House against private sector offensive actions. However, the strategic timing and language used could suggest future shifts.
- Assessment: Hypothesis A is currently better supported due to clear public statements from Google and alignment with legal frameworks. Indicators that could shift this judgment include any future changes in policy statements or operational actions suggesting offensive capabilities.
3. Key Assumptions and Red Flags
- Assumptions: Google will maintain a defensive posture; the unit will operate within legal frameworks; the private sector will not engage in offensive cyber operations.
- Information Gaps: Specific operational details of the unit; the extent of collaboration with government agencies; metrics for success and impact.
- Bias & Deception Risks: Potential bias in public statements to align with legal and ethical norms; risk of underestimating the unit’s capabilities or intentions.
4. Implications and Strategic Risks
This development could lead to increased collaboration between private and public sectors in cybersecurity, potentially setting new industry standards for proactive defense. The initiative may also influence global cyber norms and practices.
- Political / Geopolitical: Could escalate tensions with state actors who perceive these actions as aggressive, potentially leading to diplomatic friction.
- Security / Counter-Terrorism: May improve overall cybersecurity resilience, reducing the operational space for cybercriminals and hostile state actors.
- Cyber / Information Space: Could lead to enhanced threat intelligence sharing and improved cyber defenses across sectors.
- Economic / Social: Potentially increases trust in digital platforms, but may also raise concerns about privacy and surveillance.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor public statements and policy changes from Google and government agencies; assess initial impacts on cyber threat activity.
- Medium-Term Posture (1–12 months): Develop partnerships for intelligence sharing; enhance legal frameworks to support proactive cyber defense measures.
- Scenario Outlook:
- Best: Improved global cybersecurity posture with minimal geopolitical tensions.
- Worst: Escalation of cyber conflicts and increased international tensions.
- Most-Likely: Gradual improvement in cybersecurity standards and practices, with ongoing debates over privacy and legal boundaries.
6. Key Individuals and Entities
- Sandra Joyce, Vice President of Google’s Threat Intelligence Group
- Sean Cairncross, White House Cyber Czar
- John Hultquist, Chief Threat Analyst at Google
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, proactive defense, private sector, cyber strategy, threat intelligence, legal compliance, cyber infrastructure
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us