Google warns that quantum computers could breach Bitcoin’s encryption by 2029, urging immediate defensive mea…
Published on: 2026-04-01
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
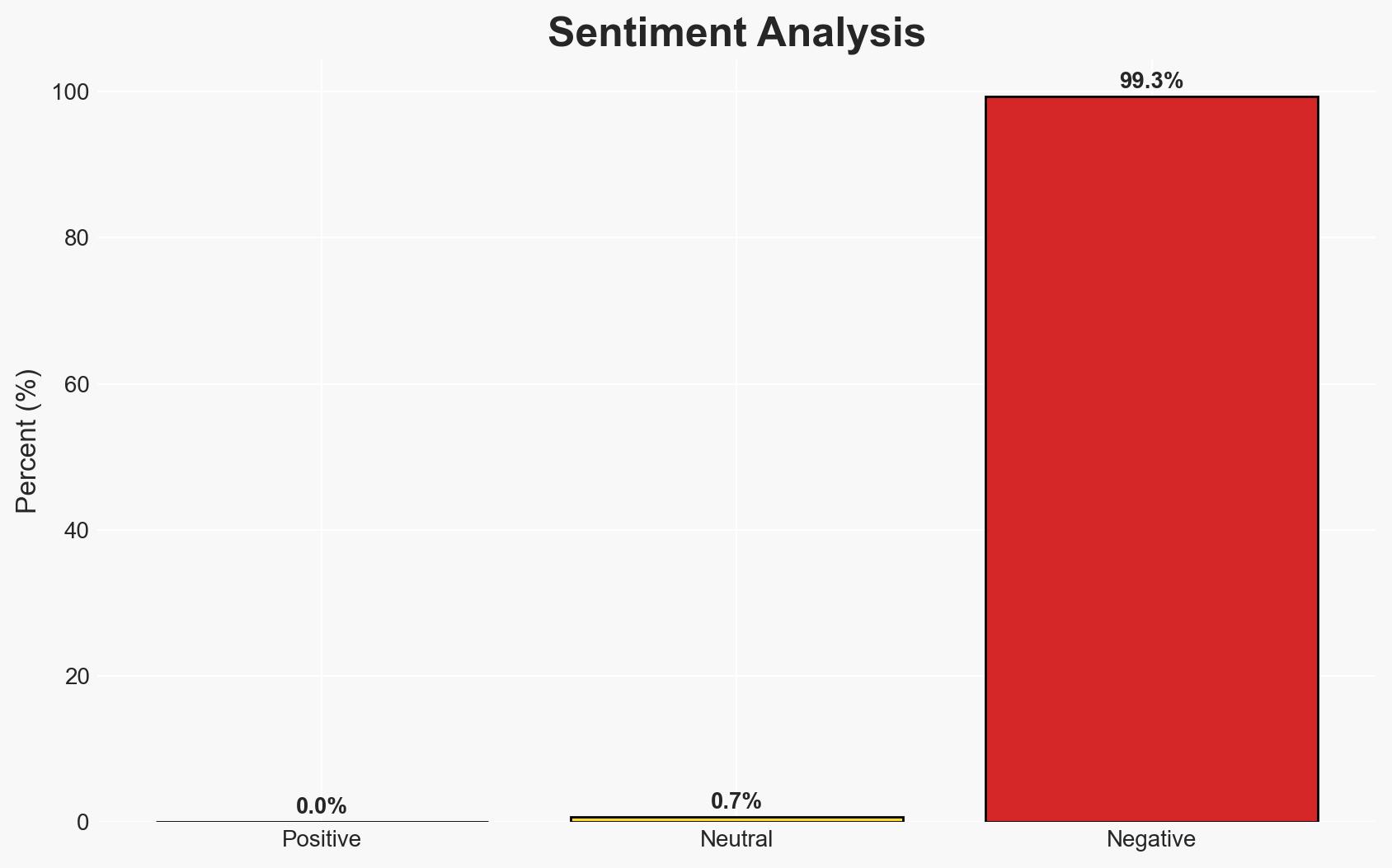
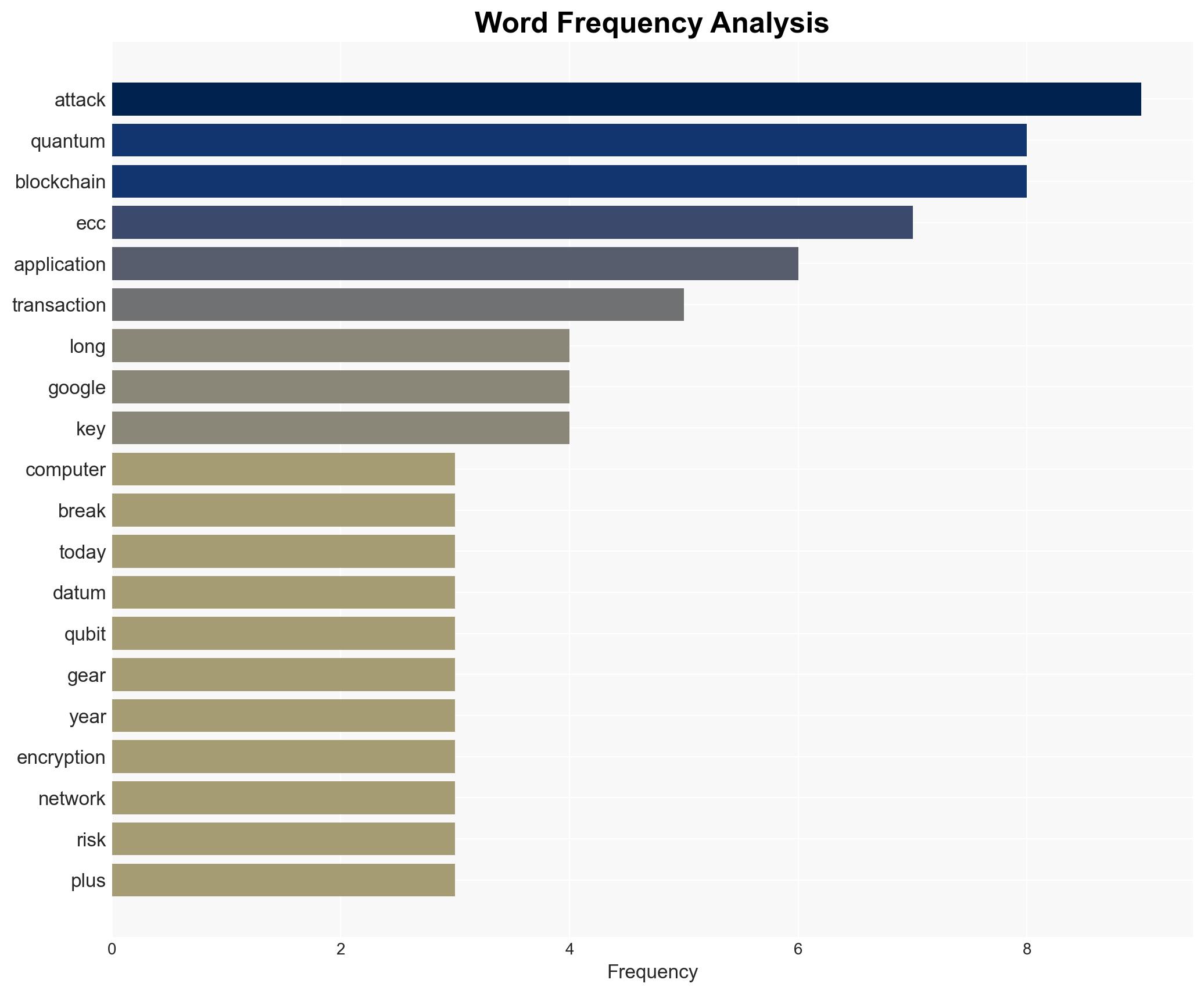
Intelligence Report: Google research suggests encryption technique used by Bitcoin will be cracked by quantum computers around 2029 search giant says quantum attacks need to be prepared for now
1. BLUF (Bottom Line Up Front)
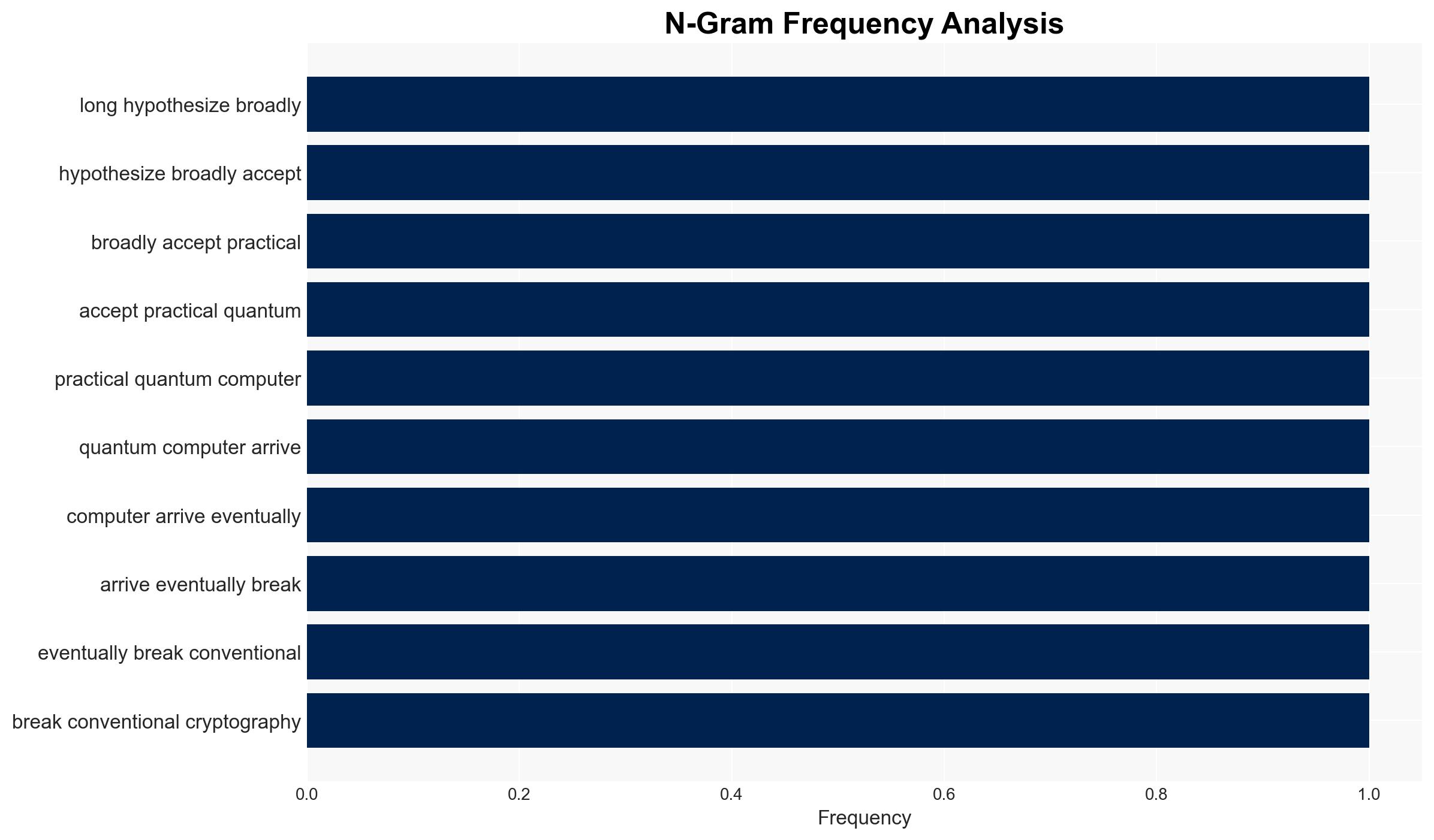
Google’s research indicates that quantum computers could break elliptic-curve cryptography (ECC) by 2029, posing a significant threat to blockchain and cryptocurrency security. The most likely hypothesis is that blockchain networks will face severe vulnerabilities unless they transition to post-quantum encryption. This assessment is made with moderate confidence, given the rapid advancements in quantum computing technology.
2. Competing Hypotheses
- Hypothesis A: Quantum computers will be capable of breaking ECC by 2029, necessitating an urgent transition to post-quantum encryption to protect blockchain infrastructures. Supporting evidence includes Google’s research and the exponential growth in quantum computing capabilities. Key uncertainties involve the pace of technological advancements and the readiness of blockchain networks to adapt.
- Hypothesis B: Quantum computers will not achieve the capability to break ECC by 2029, allowing more time for blockchain networks to transition. This hypothesis is less supported due to the current trajectory of quantum computing advancements and Google’s predictive analysis.
- Assessment: Hypothesis A is currently better supported due to Google’s research and the technological trends indicating rapid progress in quantum computing. Indicators that could shift this judgment include breakthroughs in quantum-resistant encryption or a slowdown in quantum computing advancements.
3. Key Assumptions and Red Flags
- Assumptions: Quantum computing technology will continue to advance at an exponential rate; blockchain networks will not universally adopt post-quantum encryption in the immediate term; current cryptographic methods will remain vulnerable to quantum attacks.
- Information Gaps: Specific timelines for the development of cryptographically relevant quantum computers; readiness and willingness of blockchain networks to transition to post-quantum encryption.
- Bias & Deception Risks: Potential overestimation of quantum computing capabilities by vested interests; reliance on a single source (Google) for predictive analysis could introduce bias.
4. Implications and Strategic Risks
The development of quantum computers capable of breaking ECC could lead to widespread disruption in blockchain and cryptocurrency sectors, with cascading effects across various domains.
- Political / Geopolitical: Potential for increased regulatory scrutiny and international cooperation on quantum encryption standards.
- Security / Counter-Terrorism: Heightened risk of cyber-attacks targeting blockchain networks, with implications for financial and identity security.
- Cyber / Information Space: Increased focus on developing and implementing post-quantum encryption standards to safeguard digital infrastructures.
- Economic / Social: Potential destabilization of cryptocurrency markets, affecting investor confidence and economic stability.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Initiate monitoring of quantum computing advancements and assess blockchain networks’ readiness for post-quantum encryption transition.
- Medium-Term Posture (1–12 months): Develop partnerships with tech companies and research institutions to accelerate post-quantum encryption adoption; enhance regulatory frameworks to support secure blockchain operations.
- Scenario Outlook: Best: Rapid adoption of post-quantum encryption mitigates risks. Worst: Quantum breakthroughs outpace encryption adoption, leading to widespread security breaches. Most-Likely: Gradual transition to post-quantum encryption with intermittent vulnerabilities.
6. Key Individuals and Entities
- Google (research entity)
- Blockchain networks (affected entities)
- Cryptocurrency developers and stakeholders
- Quantum computing research institutions
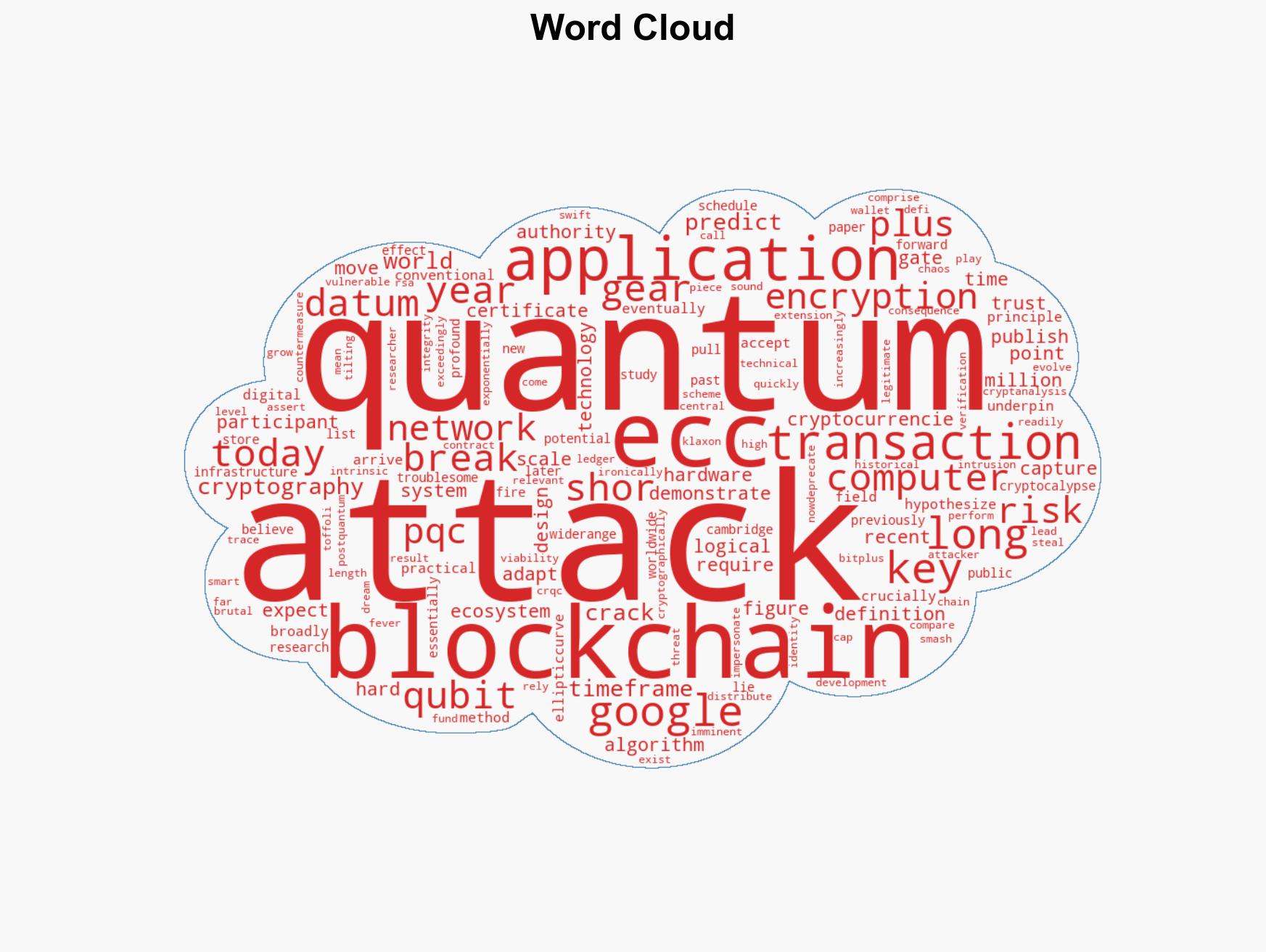
7. Thematic Tags
cybersecurity, quantum computing, blockchain security, cryptography, financial technology, encryption standards, digital infrastructure
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us