Hacked Prayer App Distributes Surrender Alerts to Iranians During Israeli-US Military Strikes
Published on: 2026-02-28
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Hacked Prayer App Sends Surrender Messages to Iranians Amid Israeli Strikes
1. BLUF (Bottom Line Up Front)
The hacking of the BadeSaba Calendar app to send surrender messages to Iranian military personnel coincided with Israeli and US preemptive strikes on Iran. This suggests a coordinated psychological operation potentially involving state actors. The most likely hypothesis is that this was a nation-state cyber operation aimed at destabilizing Iranian military cohesion. The overall confidence level in this assessment is moderate due to attribution challenges.
2. Competing Hypotheses
- Hypothesis A: The hack was conducted by Israeli or US cyber units as part of a coordinated military and psychological operation. This is supported by the timing of the messages with the strikes and the strategic nature of the operation. However, there is no direct evidence linking these states to the hack, creating uncertainty.
- Hypothesis B: The hack was carried out by anti-government Iranian groups seeking to exploit the situation to weaken the regime. This is plausible given the content of the messages, but lacks evidence of such groups having the capability to execute a sophisticated cyber operation.
- Assessment: Hypothesis A is currently better supported due to the complexity and timing of the operation, which aligns with nation-state capabilities. Indicators that could shift this judgment include credible claims of responsibility or technical evidence of the hack’s origin.
3. Key Assumptions and Red Flags
- Assumptions: The hack was premeditated and strategically timed; the BadeSaba app was compromised well before the attack; the messages were intended to destabilize Iranian military morale.
- Information Gaps: The identity of the hackers; technical details of the app compromise; the full scope of the operation’s impact on Iranian military cohesion.
- Bias & Deception Risks: Attribution bias towards state actors; potential manipulation of public perception by involved parties; the possibility of false-flag operations.
4. Implications and Strategic Risks
This development could exacerbate regional tensions and lead to further military escalation. It also highlights vulnerabilities in digital infrastructure that could be exploited in future conflicts.
- Political / Geopolitical: Potential for increased hostilities between Iran and Israel/US; possible involvement of regional allies in retaliatory measures.
- Security / Counter-Terrorism: Heightened threat environment in the Middle East; potential for retaliatory cyber or kinetic attacks by Iran.
- Cyber / Information Space: Increased focus on cyber warfare capabilities; potential for further psychological operations targeting military personnel.
- Economic / Social: Potential destabilization of Iranian society; economic impacts from military escalation and sanctions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of cyber threats; engage in diplomatic efforts to de-escalate tensions; provide cybersecurity support to regional allies.
- Medium-Term Posture (1–12 months): Develop resilience measures for critical infrastructure; strengthen partnerships with regional cyber defense entities; invest in psychological operations countermeasures.
- Scenario Outlook:
- Best Case: De-escalation through diplomatic channels, with increased cybersecurity cooperation.
- Worst Case: Escalation to broader regional conflict involving multiple state actors.
- Most Likely: Continued low-level cyber and kinetic skirmishes with periodic escalations.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
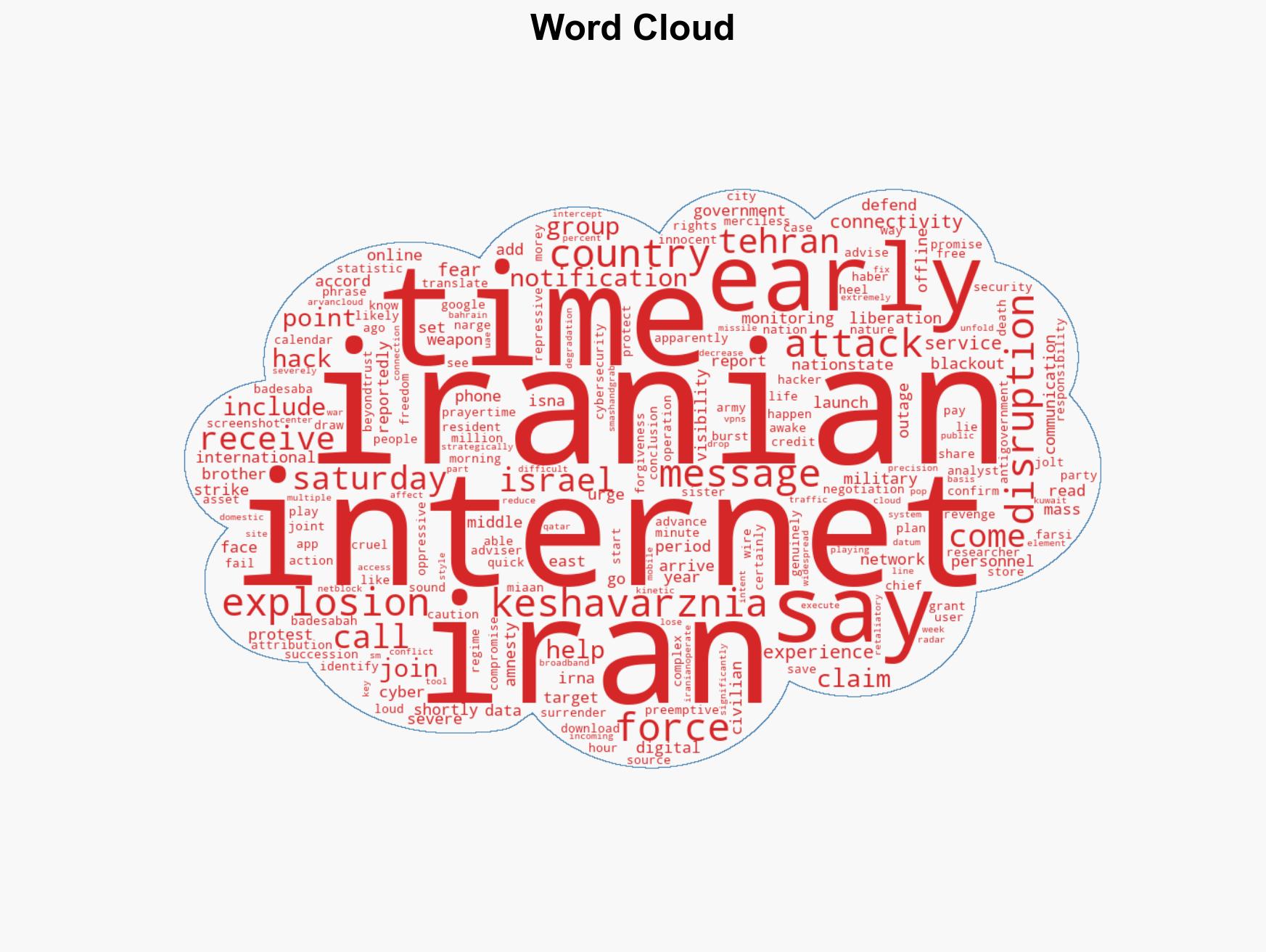
cybersecurity, cyber warfare, psychological operations, Middle East conflict, nation-state cyber operations, military strategy, regional security, digital infrastructure vulnerabilities
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us