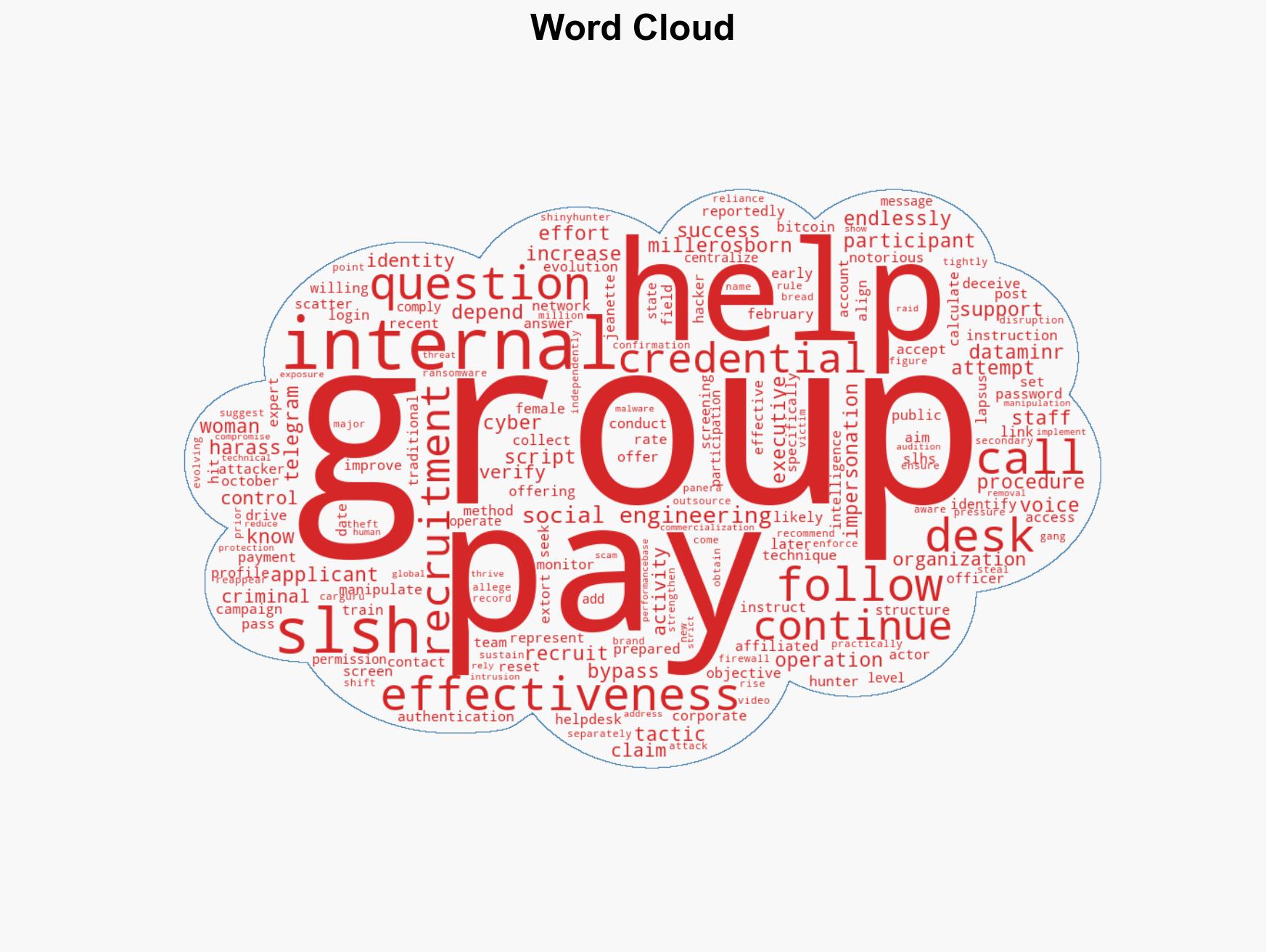
Hacker Group SLSH Recruits Women for Social Engineering Scams, Offering Up to $1,000 per Successful Call
Published on: 2026-03-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Cybercriminals are hiring women for more authentic social engineering scams and are promising up to 1000 per call
1. BLUF (Bottom Line Up Front)
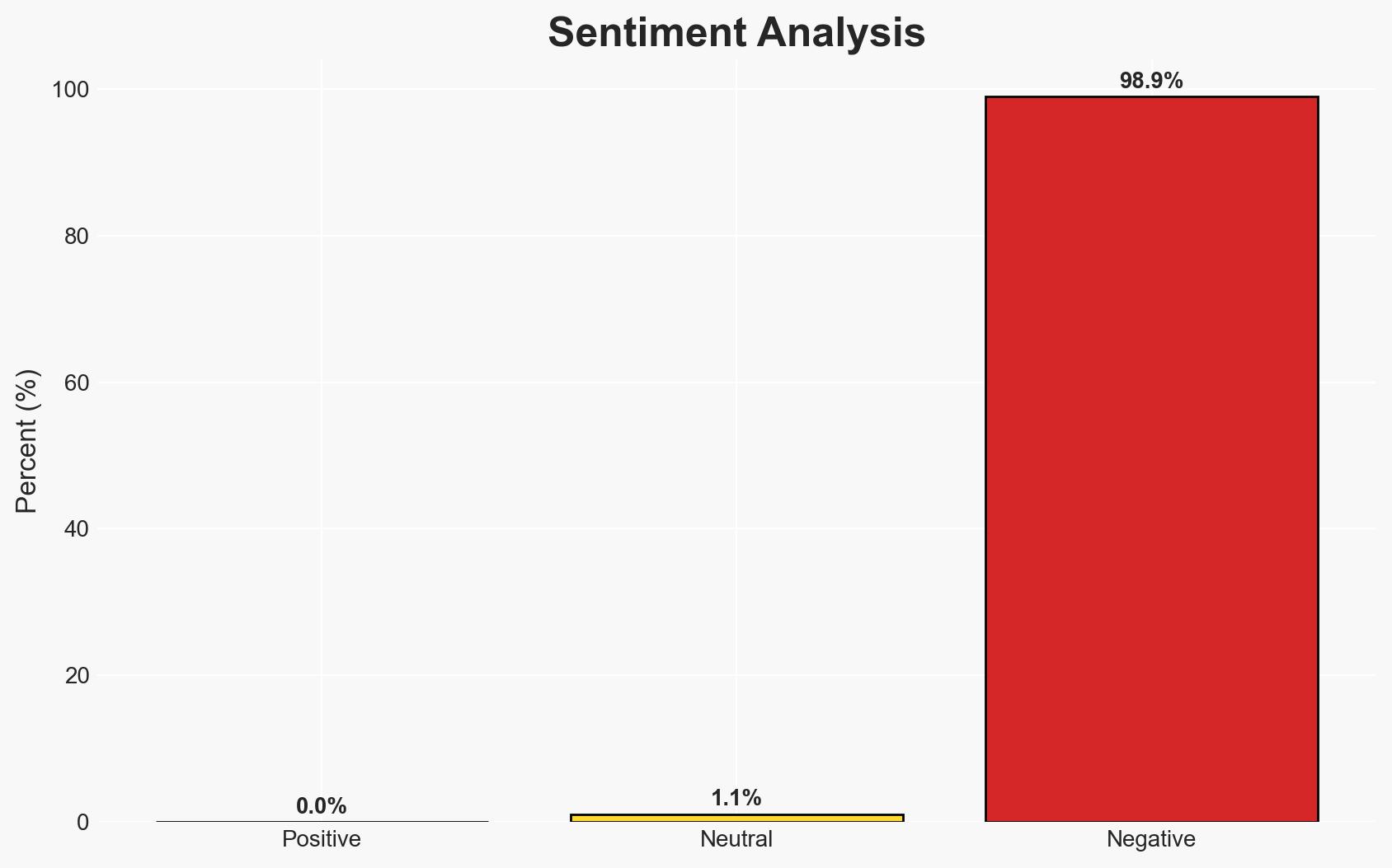
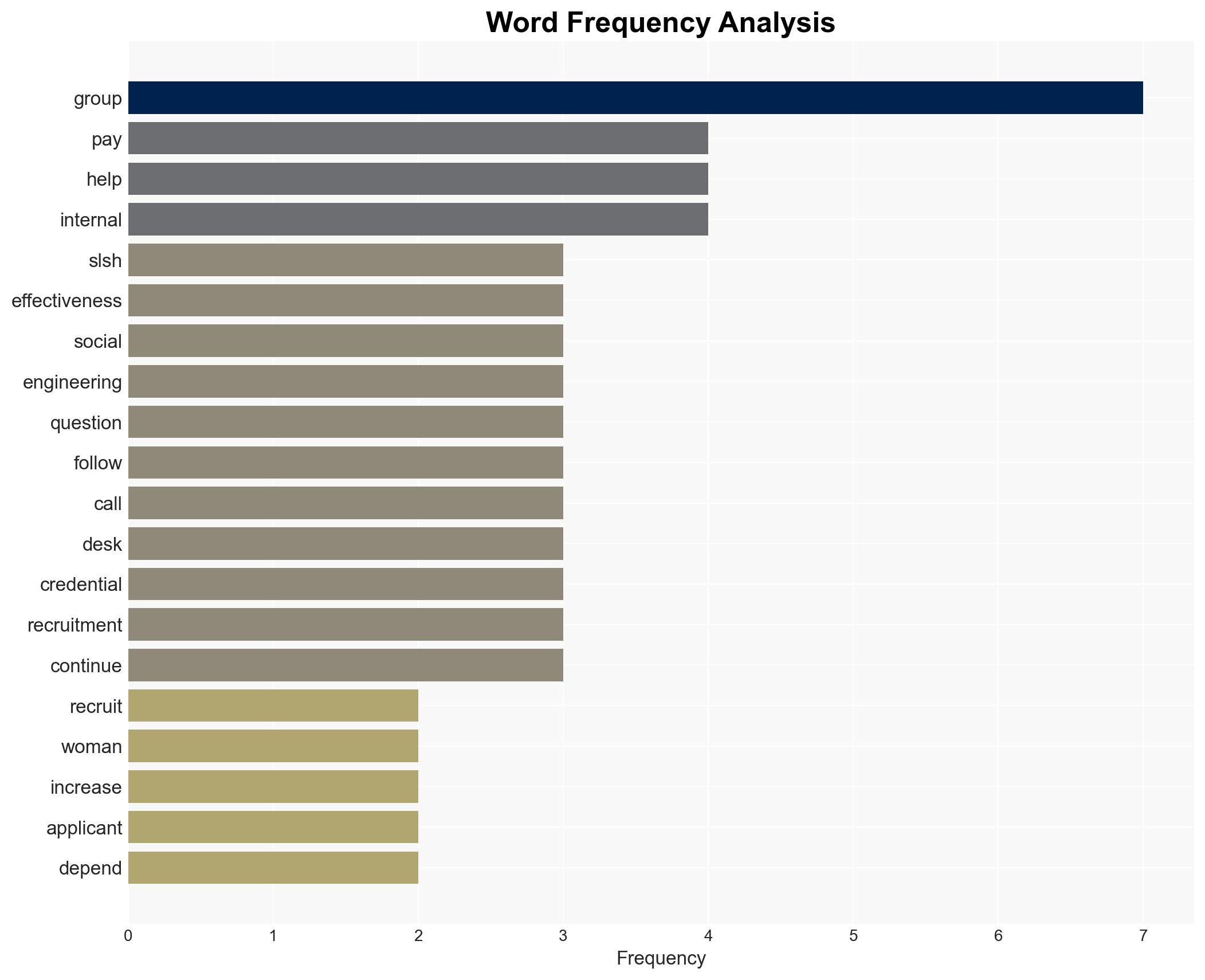
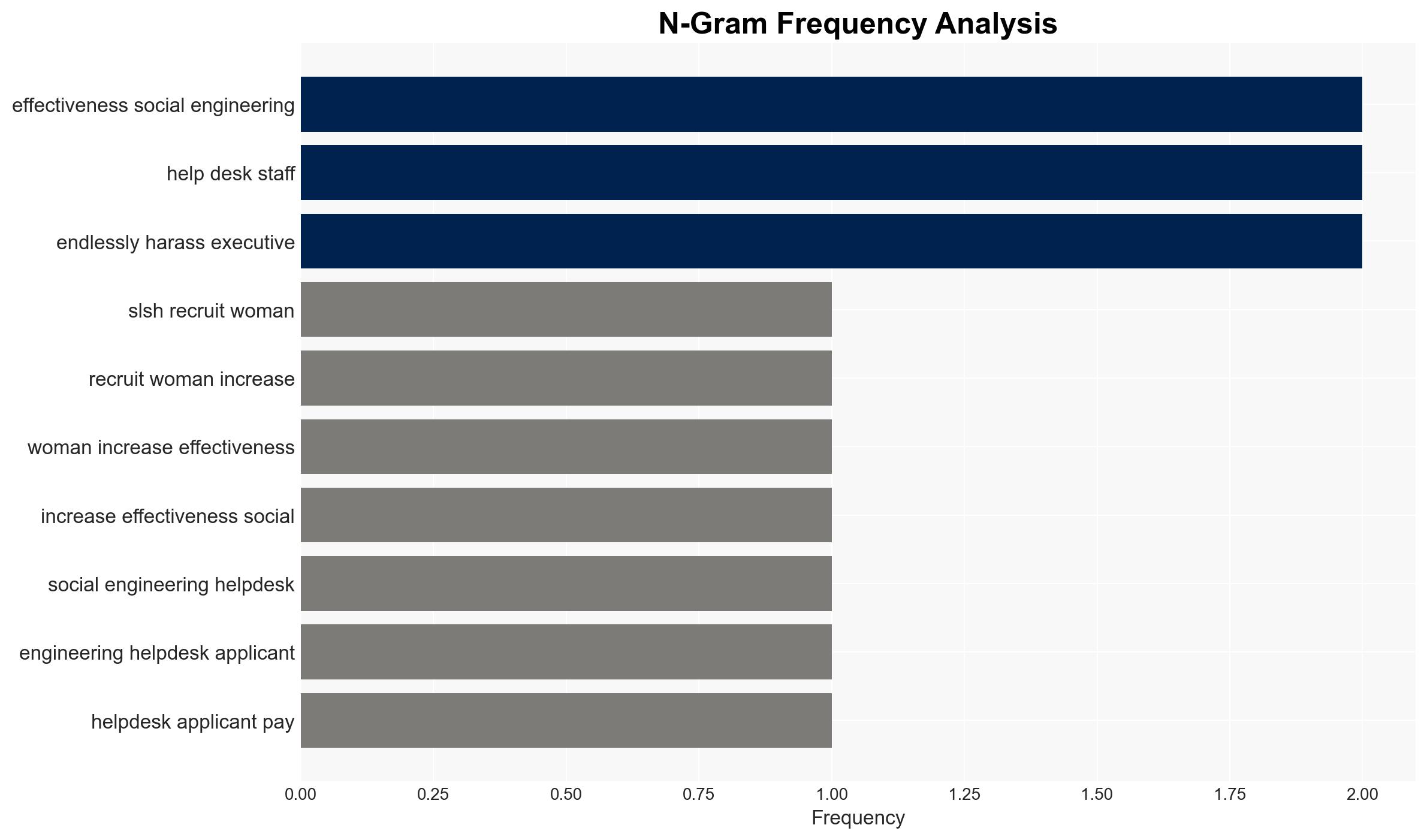
The hacker group Scattered Lapsus$ Hunters (SLSH) is recruiting women to enhance the effectiveness of their social engineering attacks on IT help desks, offering up to $1,000 per successful call. This tactic aims to exploit gender biases to bypass security measures. The primary threat is to corporate IT security, with moderate confidence in the assessment due to limited independent verification of recruitment success.
2. Competing Hypotheses
- Hypothesis A: SLSH is genuinely recruiting women to exploit gender biases in IT help desk interactions, increasing the success rate of their social engineering attacks. This is supported by the structured recruitment process and payment offers, but lacks independent verification of effectiveness.
- Hypothesis B: The recruitment drive is a deception tactic to create confusion and fear among corporate IT departments, with no real intent to employ women or pay the stated amounts. This is contradicted by the structured approach and past behavior of SLSH, but the lack of verifiable outcomes supports this hypothesis.
- Assessment: Hypothesis A is currently better supported due to the detailed recruitment process and alignment with known SLSH tactics. Indicators such as verified reports of successful breaches using female impersonators could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: SLSH has the capability to pay the promised amounts; IT help desks are susceptible to gender-based social engineering; the recruitment drive is genuine.
- Information Gaps: Verification of recruitment success and actual breaches; the scale of recruitment and number of participants; effectiveness of female impersonators in bypassing security.
- Bias & Deception Risks: Potential for cognitive bias in assuming gender-based tactics are more effective; source bias from SLSH’s own claims; possible deception in overstating recruitment success.
4. Implications and Strategic Risks
This development could lead to increased sophistication in social engineering attacks, potentially prompting changes in corporate security protocols and training. The evolution of these tactics may influence broader cyber threat landscapes.
- Political / Geopolitical: Minimal direct impact, but could increase pressure on international cooperation in cybercrime prevention.
- Security / Counter-Terrorism: Enhanced threat to corporate IT security, necessitating improved defensive measures.
- Cyber / Information Space: Potential for increased frequency and success of social engineering attacks, requiring adaptive cybersecurity strategies.
- Economic / Social: Potential financial losses for targeted companies and increased demand for cybersecurity services.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Increase awareness among IT help desks about gender-based social engineering tactics; implement multi-factor authentication and verification processes.
- Medium-Term Posture (1–12 months): Develop training programs to counteract evolving social engineering tactics; strengthen partnerships with cybersecurity firms for intelligence sharing.
- Scenario Outlook:
- Best: Enhanced security measures effectively mitigate the threat, reducing successful breaches.
- Worst: SLSH’s tactics lead to widespread breaches, causing significant economic damage.
- Most-Likely: Incremental improvements in security reduce but do not eliminate the threat, requiring ongoing vigilance.
6. Key Individuals and Entities
- Scattered Lapsus$ Hunters (SLSH)
- Jeanette Miller-Osborn, field cyber intelligence officer at Dataminr
- ShinyHunters
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, social engineering, cybercrime, IT security, gender tactics, corporate espionage, hacker groups
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us