Hackers at DEF CON express frustration with government actions and commitment to critical infrastructure secu…
Published on: 2026-02-28
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Denizens of DEF CON are ‘fed up with government’
1. BLUF (Bottom Line Up Front)
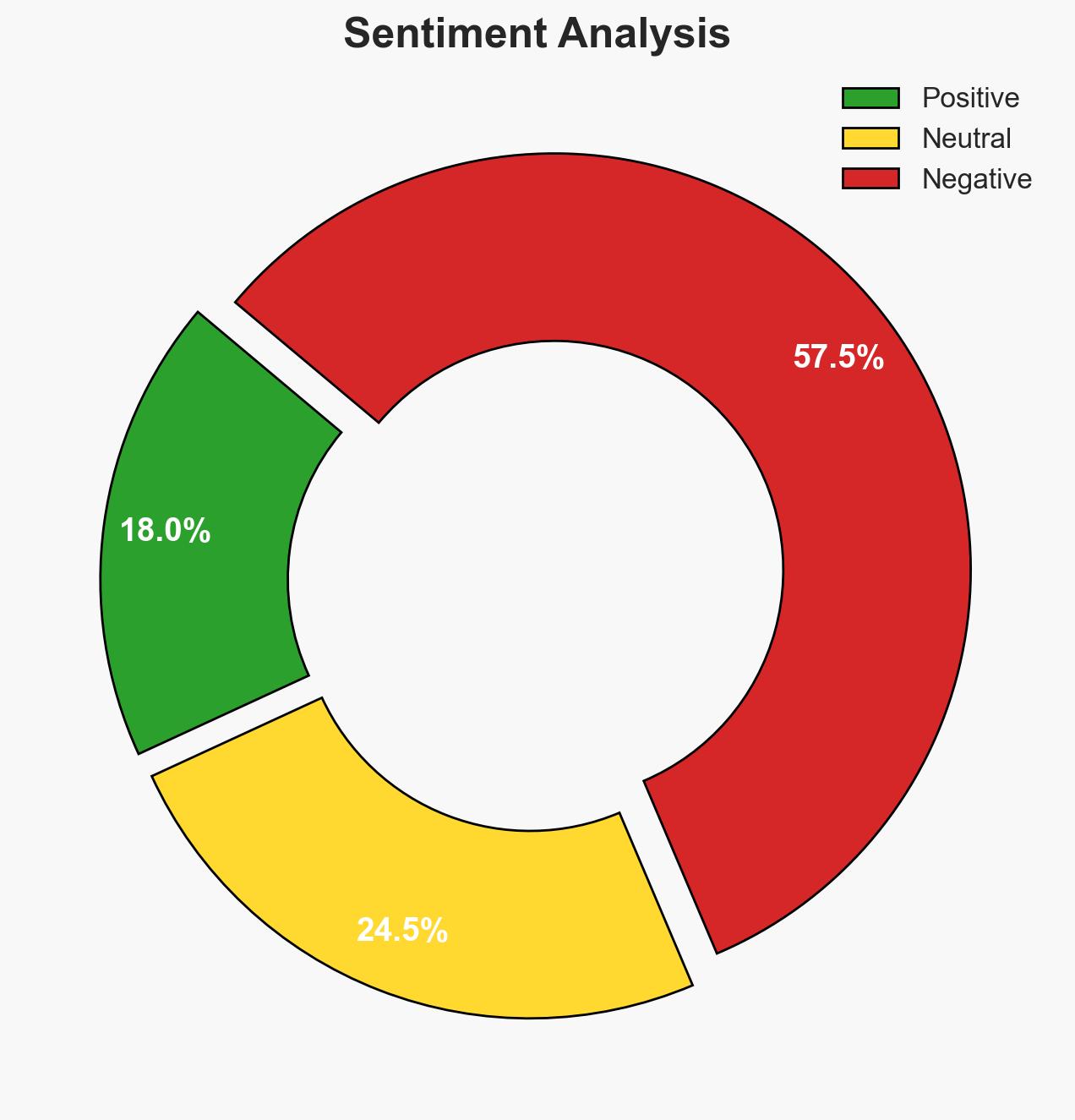
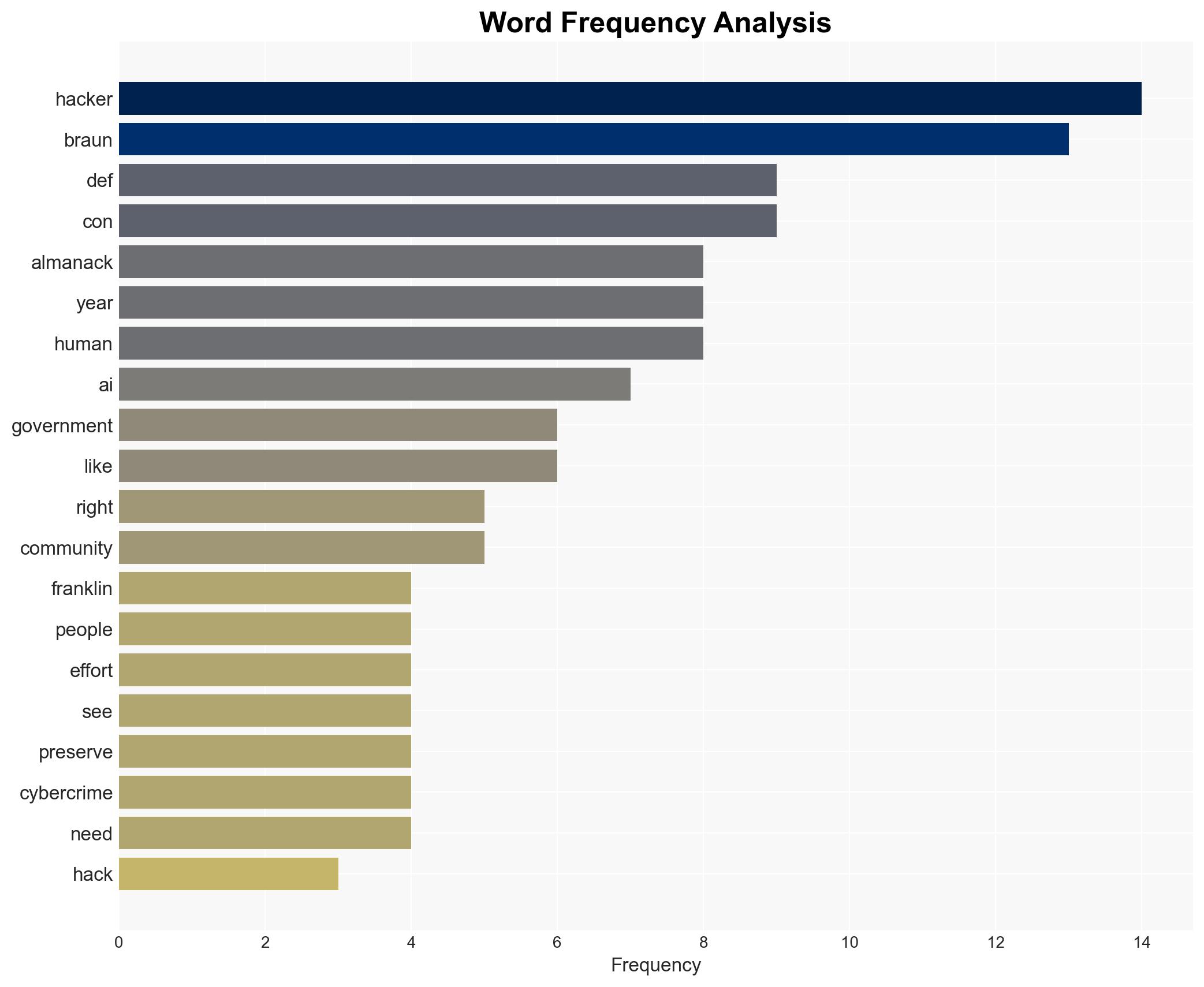
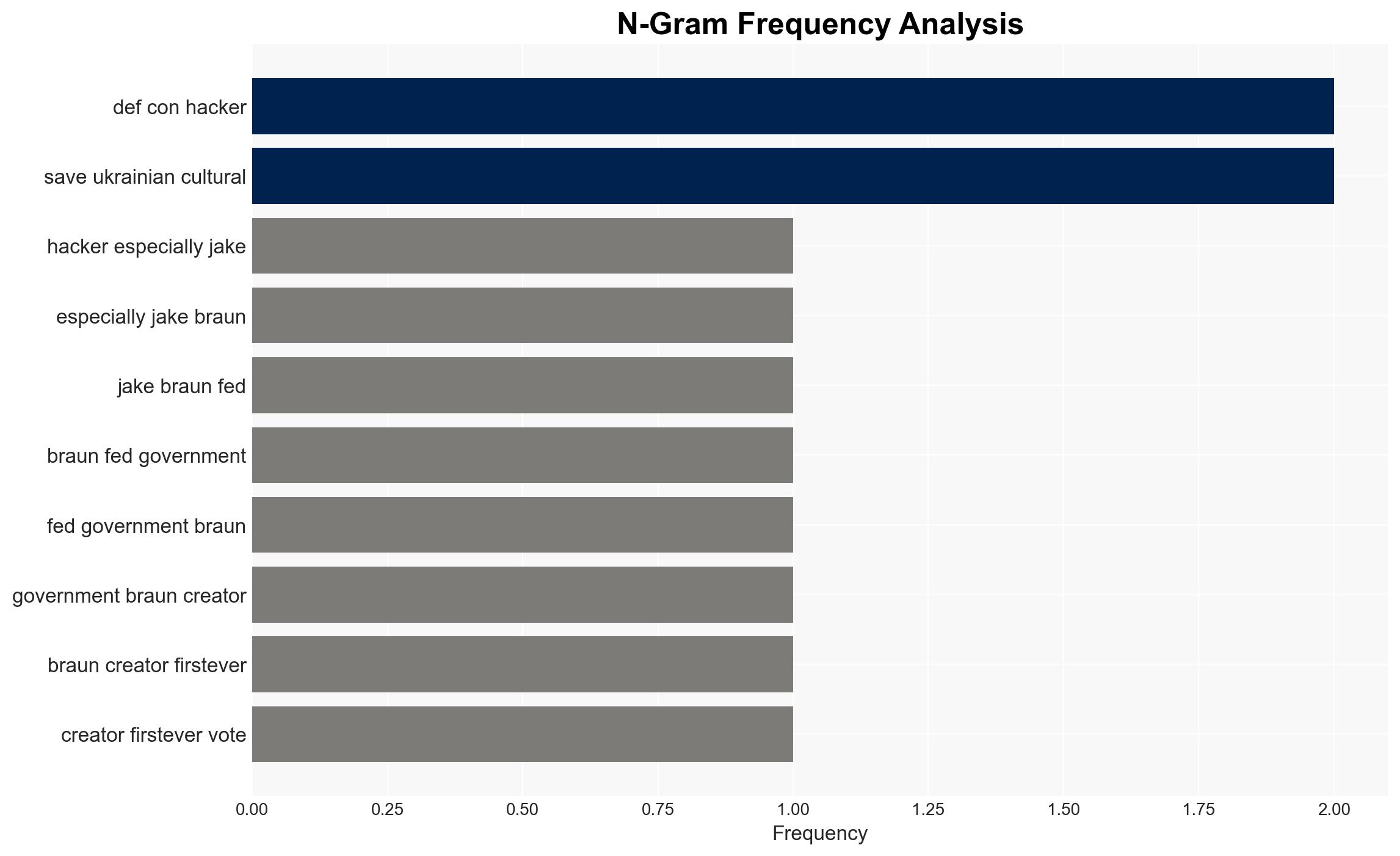
The DEF CON community, led by figures like Jake Braun, expresses significant dissatisfaction with governmental progress on cyber and societal issues, particularly cybercrime, AI, and authoritarianism. The community’s proactive measures, such as the Franklin project, aim to address these gaps independently. This assessment is made with moderate confidence due to the strong alignment of DEF CON activities with stated objectives, though broader governmental responses remain uncertain.
2. Competing Hypotheses
- Hypothesis A: The DEF CON community’s dissatisfaction stems from genuine concerns about governmental inaction on critical issues like cybercrime and AI. This is supported by the establishment of initiatives like the Franklin project and the Hacker’s Almanack. However, the extent of governmental inaction remains partially unverified.
- Hypothesis B: The DEF CON community’s actions are primarily driven by a desire to increase its influence and visibility within cybersecurity and policy circles, rather than solely by governmental failures. While the creation of high-profile projects supports this, the consistent focus on societal threats suggests a deeper motivation.
- Assessment: Hypothesis A is currently better supported, as the DEF CON community’s initiatives align closely with their stated concerns about societal threats. Indicators such as increased governmental engagement or policy shifts could alter this assessment.
3. Key Assumptions and Red Flags
- Assumptions: The DEF CON community’s motivations are primarily altruistic; government inaction is a significant driver of DEF CON’s initiatives; AI and cybercrime are perceived as escalating threats by the community.
- Information Gaps: Detailed governmental responses to DEF CON’s critiques; comprehensive data on the effectiveness of DEF CON’s initiatives in mitigating identified threats.
- Bias & Deception Risks: Potential bias from DEF CON community members who may exaggerate governmental failures to justify their initiatives; risk of underestimating governmental efforts due to limited open-source visibility.
4. Implications and Strategic Risks
The DEF CON community’s initiatives could catalyze broader societal engagement in cybersecurity, potentially influencing policy and operational practices. However, the lack of governmental collaboration could lead to fragmented efforts.
- Political / Geopolitical: Increased tension between cybersecurity communities and governments could arise, potentially impacting international cyber policy cooperation.
- Security / Counter-Terrorism: Enhanced focus on cybersecurity by independent groups may improve threat detection and mitigation, but could also lead to uncoordinated responses.
- Cyber / Information Space: The rise of AI in offensive cyber capabilities highlights the need for robust defenses and ethical guidelines.
- Economic / Social: Public awareness and engagement in cybersecurity could increase, potentially leading to greater societal resilience but also to public distrust in governmental capabilities.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor DEF CON community activities and publications for emerging trends; engage with key figures to understand their perspectives and potential collaboration opportunities.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity communities to enhance information sharing; invest in AI research to understand its implications for cybersecurity.
- Scenario Outlook:
- Best: Government and DEF CON collaborate, leading to improved cybersecurity policies and practices.
- Worst: Escalating tensions result in fragmented cybersecurity efforts and increased vulnerability.
- Most-Likely: DEF CON continues its independent initiatives, with gradual governmental engagement.
6. Key Individuals and Entities
- Jake Braun – DEF CON organizer and Franklin project co-founder
- Franklin project – Initiative to secure critical infrastructure
- Anthropic – Company involved in AI research
- Keane Lucas – Anthropic researcher
7. Thematic Tags
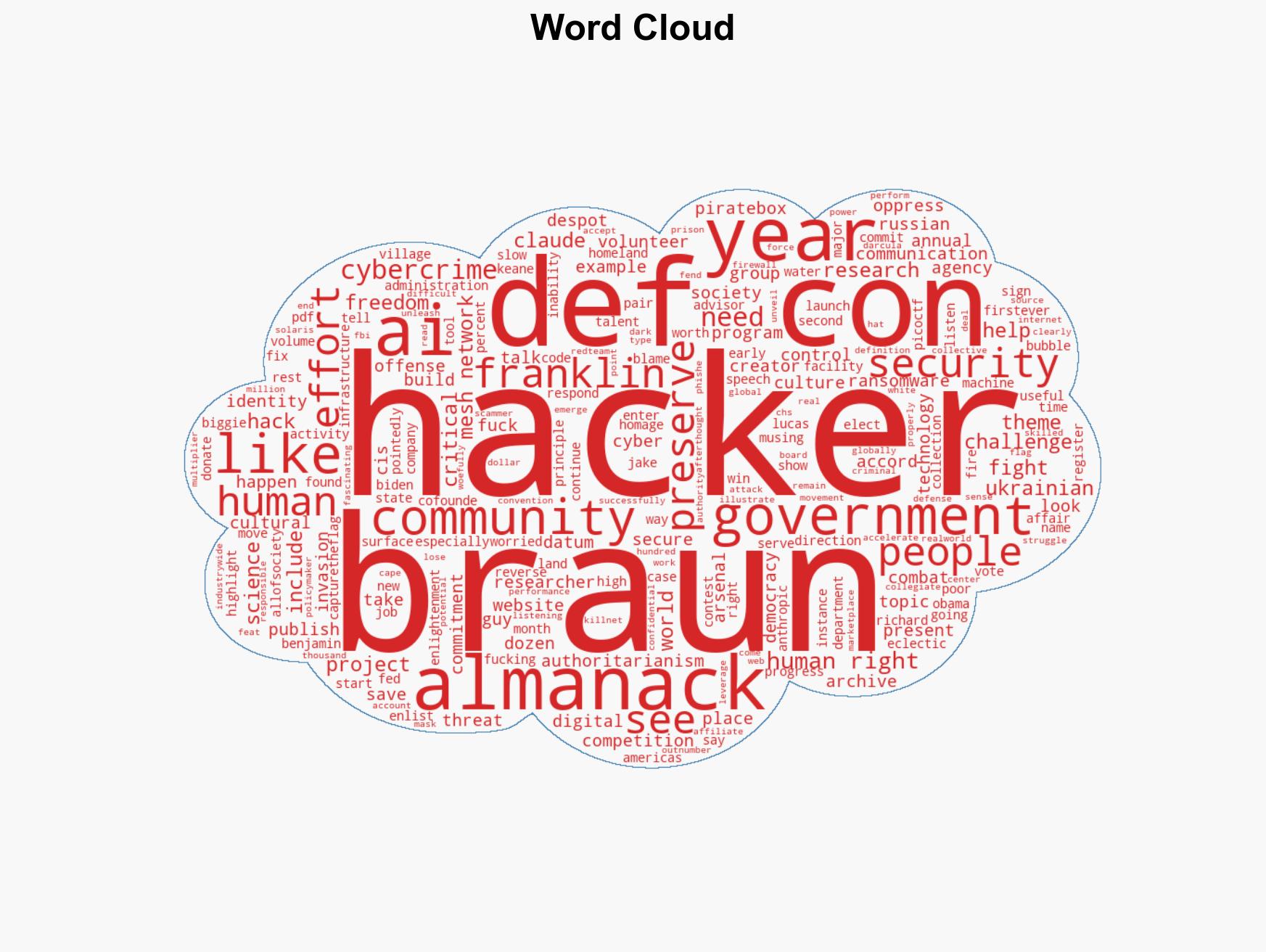
cybersecurity, government criticism, AI in cyber operations, DEF CON, critical infrastructure protection, hacker community, societal threats
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us