Hazeldenes poultry operations in Australia disrupted following significant cyberattack
Published on: 2026-02-25
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
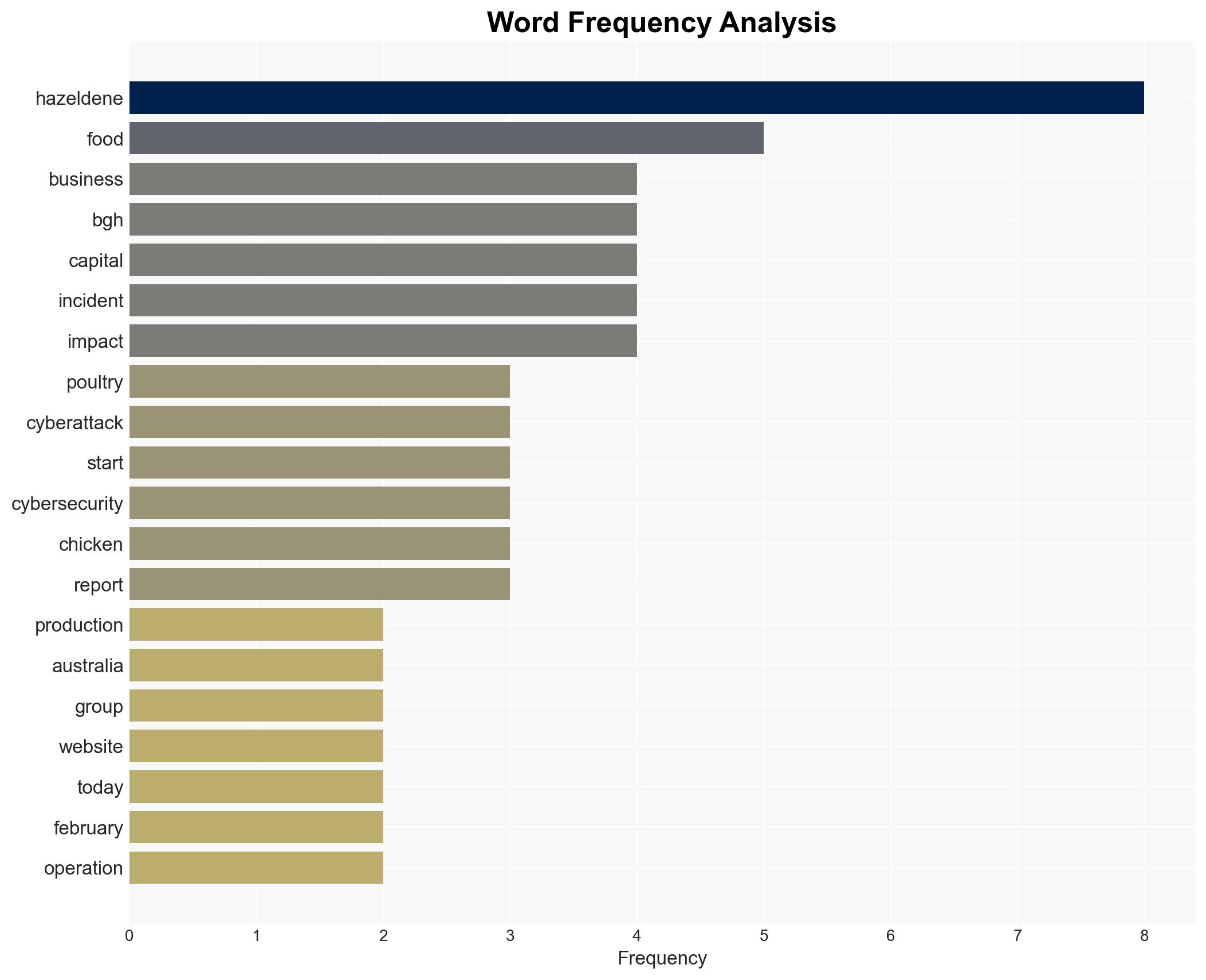
Intelligence Report: Australia chicken processor Hazeldenes hit by cyberattack
1. BLUF (Bottom Line Up Front)
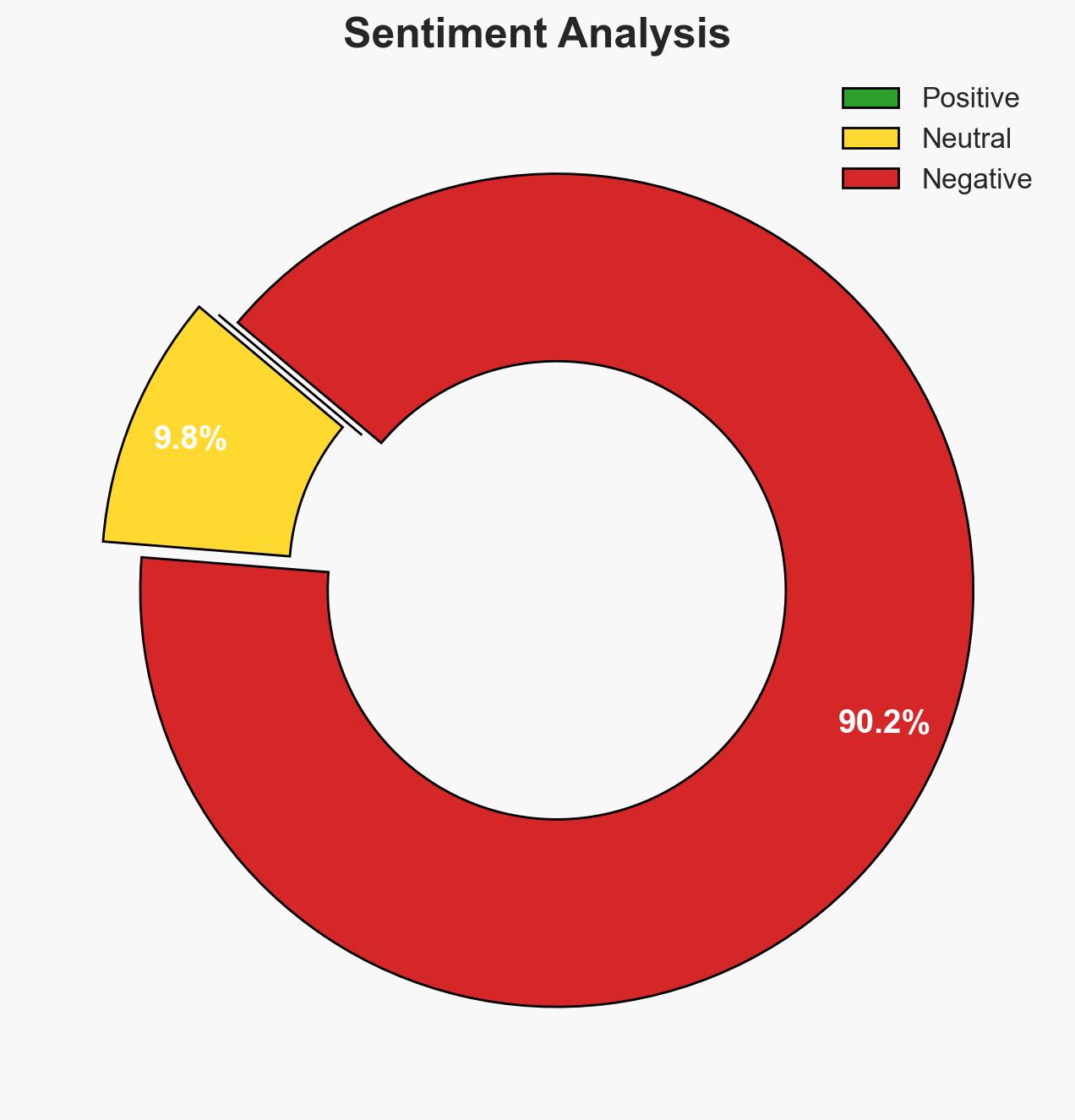
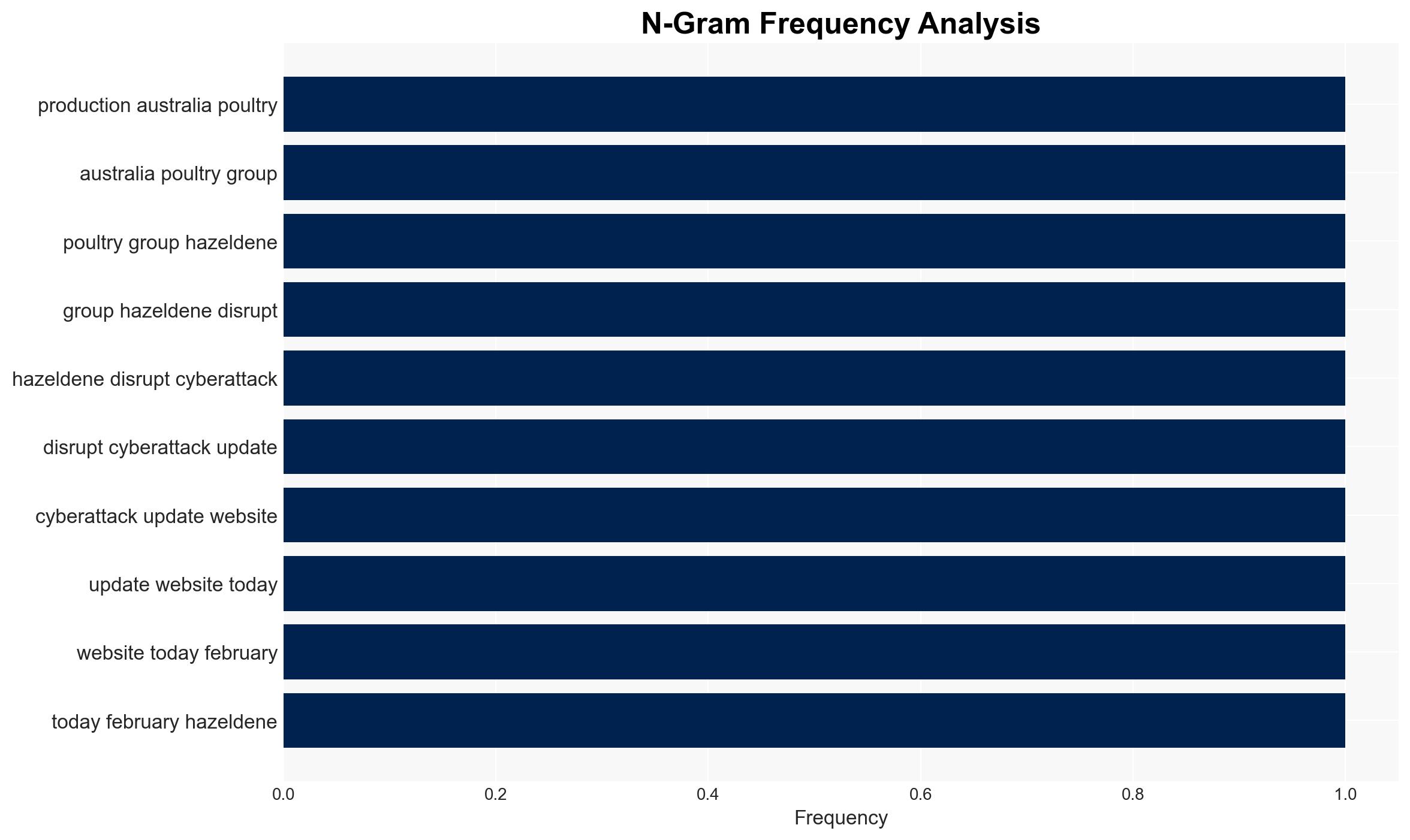
The cyberattack on Hazeldenes has disrupted poultry production, affecting supply chains in Victoria. The company is in the process of restoring operations. The most likely hypothesis is that this incident is part of a broader trend of cyberattacks targeting the food industry, with moderate confidence. This impacts local retailers and consumers due to potential shortages and economic implications.
2. Competing Hypotheses
- Hypothesis A: The cyberattack on Hazeldenes is an isolated incident aimed at disrupting its operations for financial gain. Supporting evidence includes the lack of immediate claims of responsibility and the company’s engagement with cybersecurity experts. Key uncertainties involve the attacker’s identity and motives.
- Hypothesis B: The attack is part of a coordinated campaign targeting the food industry to cause broader supply chain disruptions. This is supported by similar incidents reported globally, such as those affecting Asahi and UNFI. Contradicting evidence includes the absence of direct links between these incidents.
- Assessment: Hypothesis B is currently better supported due to the pattern of similar attacks on the food industry, suggesting a possible trend. Indicators such as further attacks on similar entities could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The attack was financially motivated; Hazeldenes’ response will mitigate further disruptions; the incident is part of a broader trend.
- Information Gaps: Specific details about the attackers, their methods, and the extent of data compromise remain unknown.
- Bias & Deception Risks: Potential bias in reporting due to reliance on company statements; risk of underestimating the attack’s sophistication or broader implications.
4. Implications and Strategic Risks
This cyberattack could lead to increased scrutiny of cybersecurity practices in the food industry and highlight vulnerabilities in supply chains. Over time, it may prompt regulatory changes or increased investment in cybersecurity.
- Political / Geopolitical: Potential for increased government intervention in cybersecurity standards for critical industries.
- Security / Counter-Terrorism: Heightened awareness of cyber threats to food security, but no direct counter-terrorism implications identified.
- Cyber / Information Space: Increased focus on protecting digital infrastructure in the food sector; potential for information warfare if attackers leverage data breaches.
- Economic / Social: Short-term economic impact due to supply chain disruptions; potential for consumer price increases and decreased trust in food supply reliability.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of Hazeldenes’ recovery process; engage with cybersecurity experts to assess vulnerabilities; communicate transparently with stakeholders.
- Medium-Term Posture (1–12 months): Develop industry-wide cybersecurity standards; foster public-private partnerships to enhance resilience; conduct regular security audits.
- Scenario Outlook:
- Best: Rapid recovery with minimal long-term impact; increased cybersecurity measures prevent future incidents.
- Worst: Prolonged disruptions lead to significant economic losses and regulatory backlash.
- Most-Likely: Gradual recovery with moderate economic impact; increased focus on cybersecurity in the industry.
6. Key Individuals and Entities
- Hazeldenes
- BGH Capital
- Australian Cyber Security Centre (potentially involved in response)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
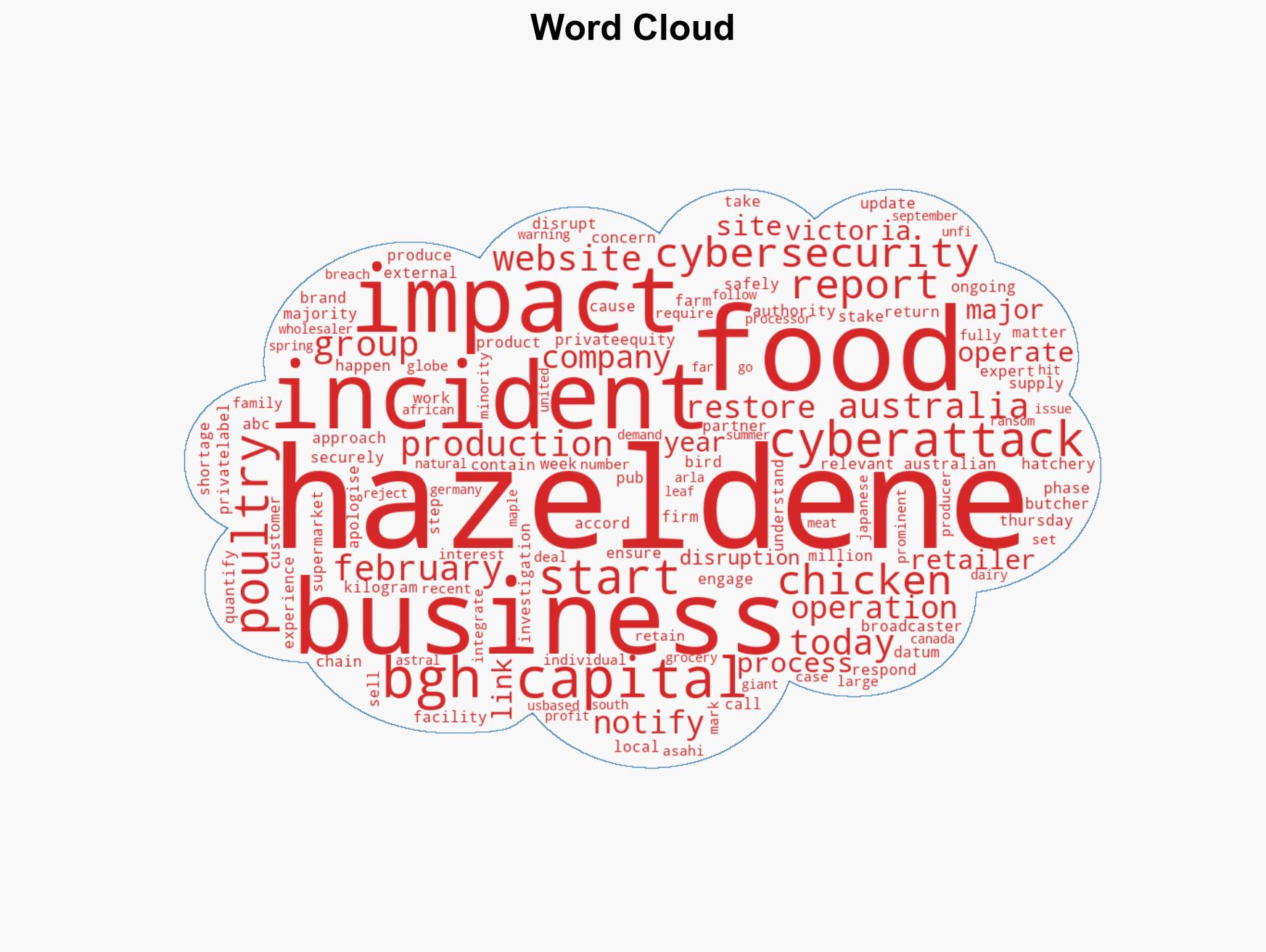
cybersecurity, food industry, supply chain disruption, economic impact, cyberattack trends, Australia, critical infrastructure
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us