HellCat ransomware what you need to know – tripwire.com
Published on: 2025-04-03
Intelligence Report: HellCat ransomware what you need to know – tripwire.com
1. BLUF (Bottom Line Up Front)
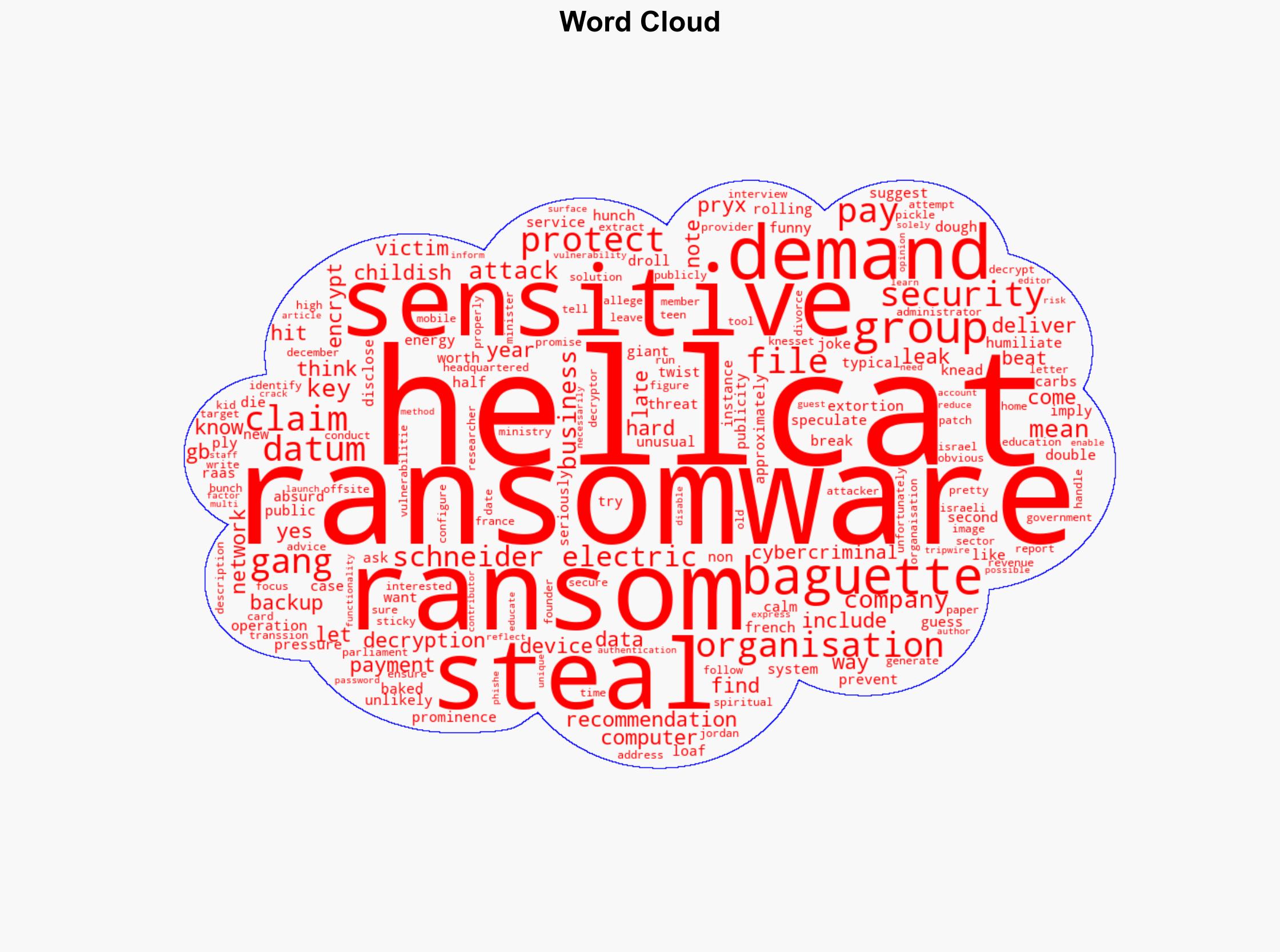
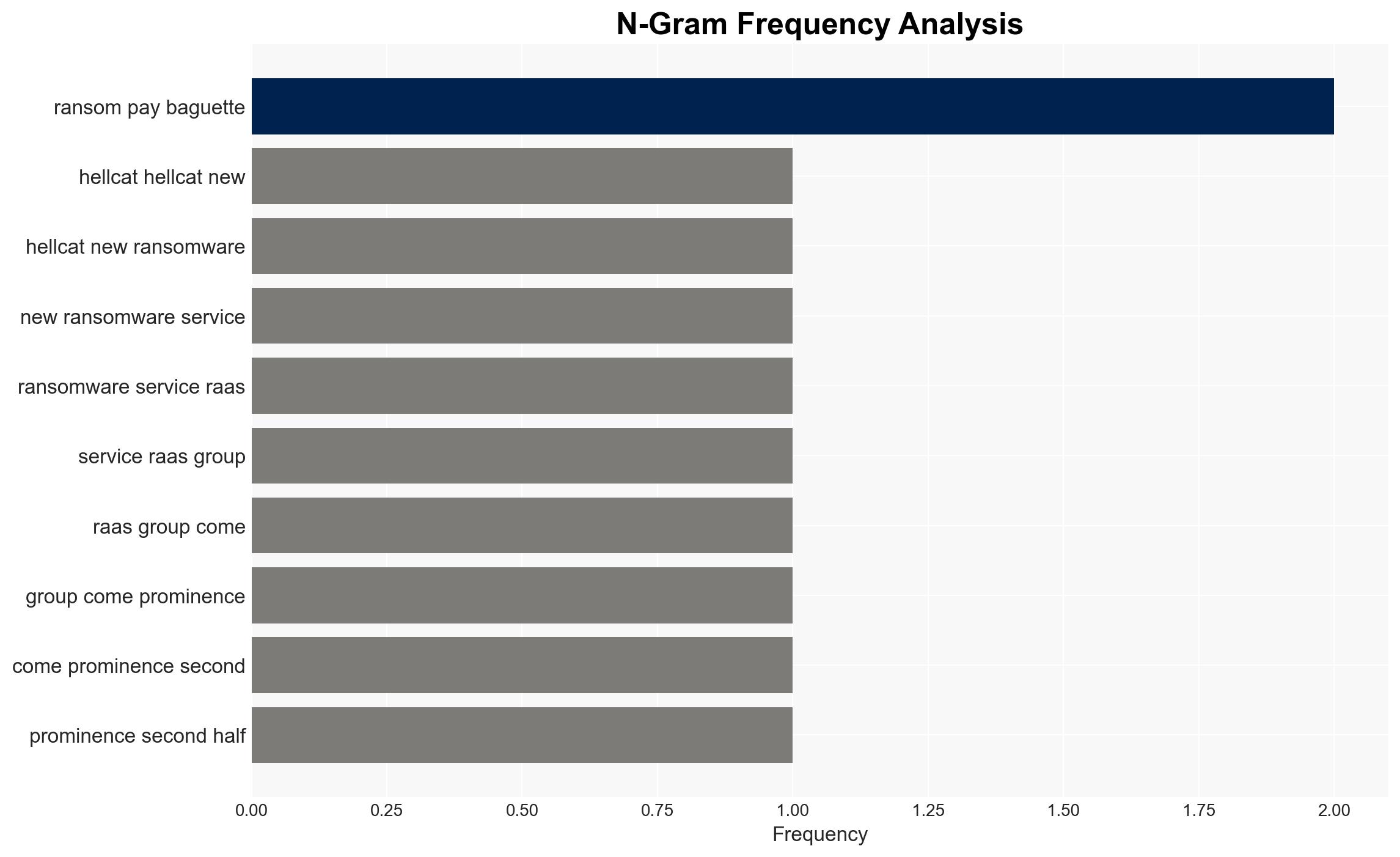
HellCat is a new ransomware-as-a-service (RaaS) group that has gained prominence in the latter half of the year. It employs a typical double extortion tactic, encrypting data and threatening to leak it unless a ransom is paid. Unusually, HellCat has demanded a ransom in the form of baguettes from Schneider Electric, suggesting a possible attempt at public humiliation or a publicity stunt. The group has targeted high-profile organizations, including the Israeli parliament and the Jordanian Ministry of Education. Immediate action is recommended to bolster cybersecurity defenses, as no public decryption tool is available for HellCat ransomware at this time.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
HellCat’s operations involve the theft of sensitive data and the encryption of computer systems. The group’s unusual ransom demands, such as requesting baguettes, may indicate a strategy to gain media attention or to mock their victims. Security researchers have identified key figures within HellCat, including an alleged founder known as Pryx, who is reportedly in their late teens. The group’s focus on high-revenue businesses and government sectors suggests a strategic targeting approach.
3. Implications and Strategic Risks
The activities of HellCat pose significant risks to national security and economic interests, particularly for organizations in critical infrastructure sectors. The group’s ability to steal and potentially leak sensitive data could lead to severe reputational damage and financial losses. The demand for non-monetary ransoms could set a precedent for future ransomware attacks, complicating negotiations and response strategies.
4. Recommendations and Outlook
Recommendations:
- Implement robust cybersecurity measures, including secure offsite backups and up-to-date security solutions.
- Ensure all network devices are configured correctly and protected with the latest security patches.
- Adopt strong, unique passwords and enable multi-factor authentication for sensitive accounts.
- Educate staff on the risks and methods of cybercriminal attacks, particularly phishing.
Outlook:
In the best-case scenario, increased awareness and improved cybersecurity measures will mitigate the impact of HellCat’s operations. In the worst-case scenario, the group could inspire similar tactics among other ransomware actors, leading to a rise in unconventional ransom demands. The most likely outcome is a continued focus on high-profile targets, with potential escalations in ransom demands and data theft.
5. Key Individuals and Entities
The report mentions significant individuals and organizations, including Schneider Electric, Pryx, and the Israeli parliament. These entities are central to the analysis of HellCat’s operations and strategic targeting.