Identifying Gaps in Multi-Factor Authentication for Windows Environments and Credential Exploitation Risks
Published on: 2026-03-05
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Where Multi-Factor Authentication Stops and Credential Abuse Starts
1. BLUF (Bottom Line Up Front)
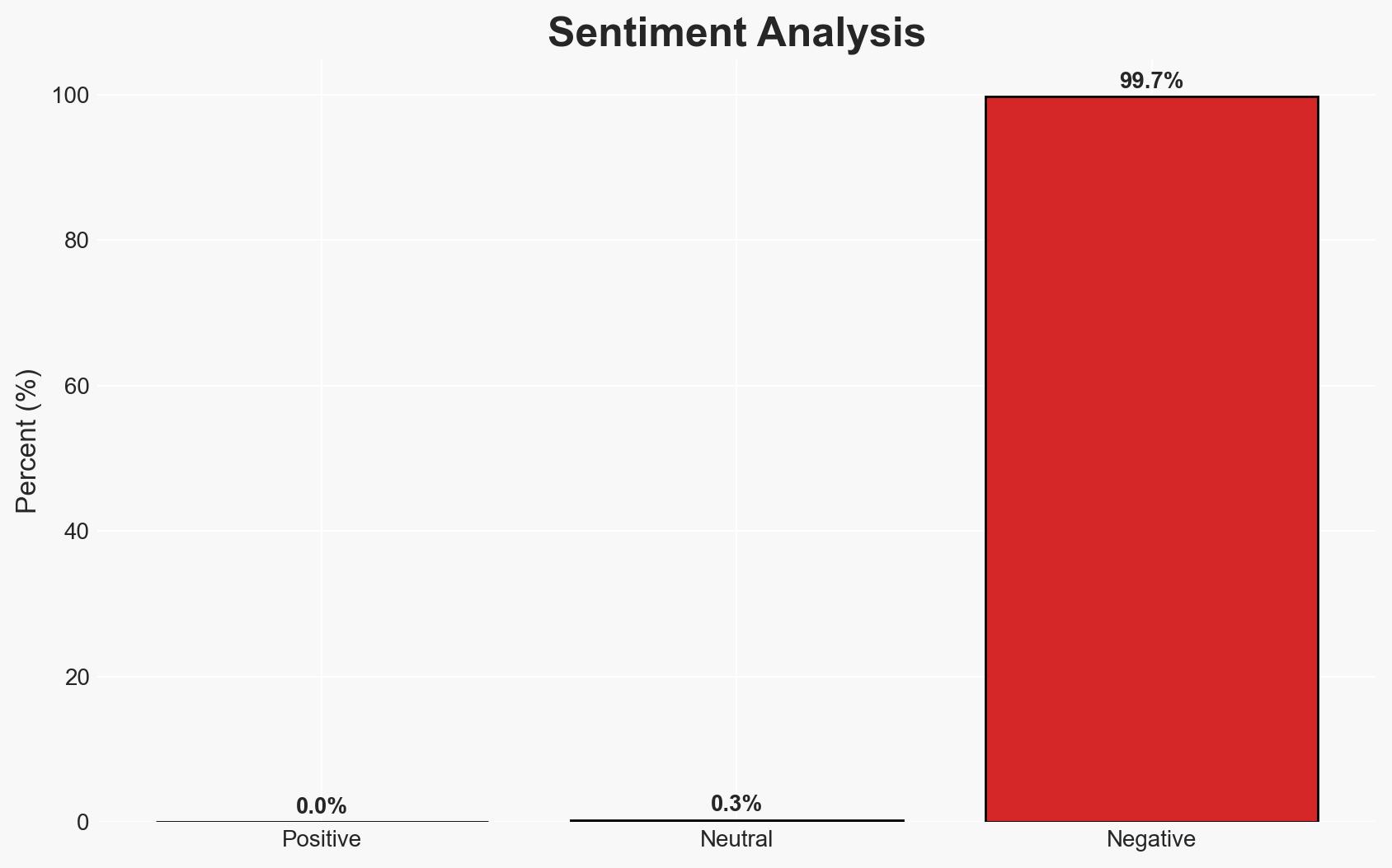
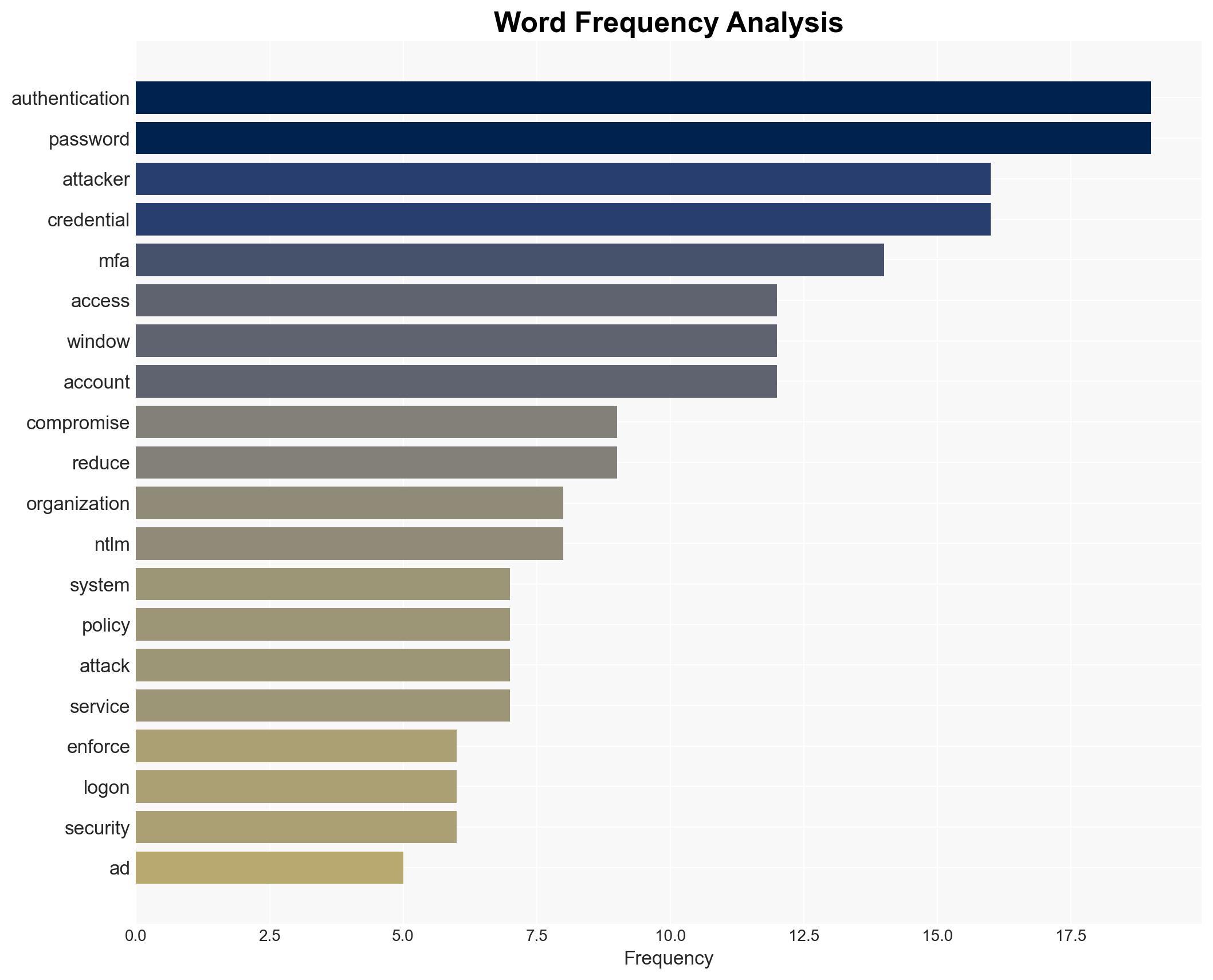
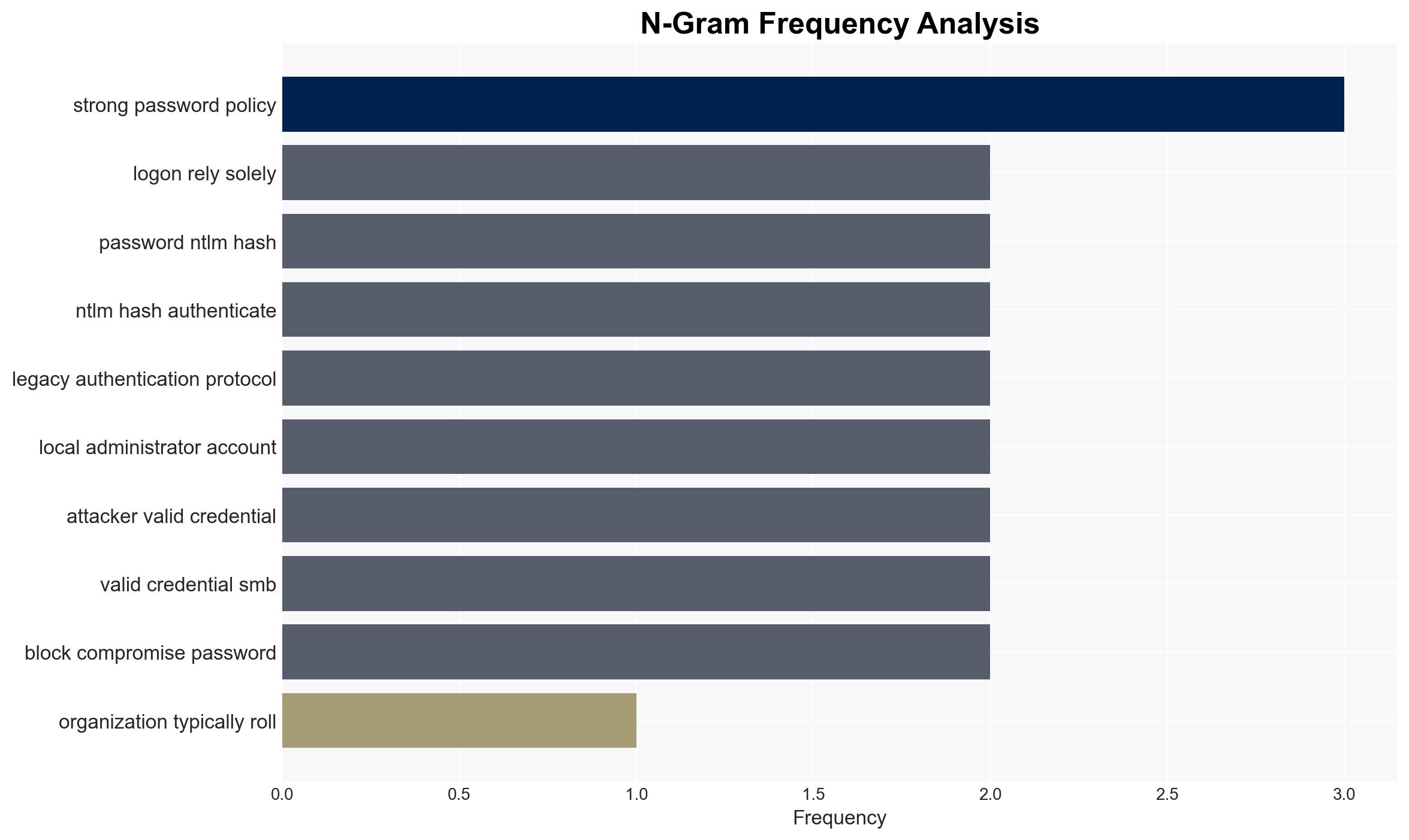
Credential abuse in Windows environments persists despite the implementation of Multi-Factor Authentication (MFA) due to incomplete coverage, particularly in Active Directory (AD) authentication paths. The most likely hypothesis is that attackers exploit these gaps to compromise networks using valid credentials. This affects organizations relying on Windows systems, with moderate confidence in this assessment.
2. Competing Hypotheses
- Hypothesis A: Credential abuse in Windows environments is primarily due to incomplete MFA coverage, particularly in AD authentication paths. Evidence includes the reliance on AD for Windows logons and the lack of MFA prompts in these scenarios. Uncertainties include the extent of MFA implementation across different organizations.
- Hypothesis B: Credential abuse is primarily due to sophisticated attacker techniques that bypass MFA, regardless of coverage. This is supported by the use of techniques like pass-the-hash with NTLM. However, this does not fully explain the persistence of credential abuse where MFA could be applied.
- Assessment: Hypothesis A is currently better supported due to the clear evidence of incomplete MFA coverage in Windows environments. Indicators that could shift this judgment include new data on the prevalence of sophisticated bypass techniques.
3. Key Assumptions and Red Flags
- Assumptions: MFA is correctly implemented where possible; attackers have access to valid credentials; organizations use AD for Windows logons.
- Information Gaps: Detailed statistics on MFA implementation across different sectors; data on the frequency of credential abuse incidents.
- Bias & Deception Risks: Potential bias in reporting MFA effectiveness; lack of comprehensive data on attacker techniques may skew analysis.
4. Implications and Strategic Risks
This development could lead to increased security vulnerabilities in organizations relying heavily on Windows systems without comprehensive MFA coverage. Over time, this may necessitate shifts in cybersecurity strategies and policies.
- Political / Geopolitical: Potential for increased international collaboration on cybersecurity standards.
- Security / Counter-Terrorism: Heightened risk of network compromises could impact national security operations.
- Cyber / Information Space: Increased focus on securing authentication processes and updating legacy systems.
- Economic / Social: Potential economic impact from data breaches and increased cybersecurity spending.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct audits to identify MFA coverage gaps; implement MFA for all possible authentication paths.
- Medium-Term Posture (1–12 months): Develop partnerships for sharing threat intelligence; invest in training for cybersecurity personnel.
- Scenario Outlook: Best: Full MFA implementation reduces credential abuse; Worst: Continued gaps lead to significant breaches; Most-Likely: Gradual improvement in MFA coverage with ongoing challenges.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
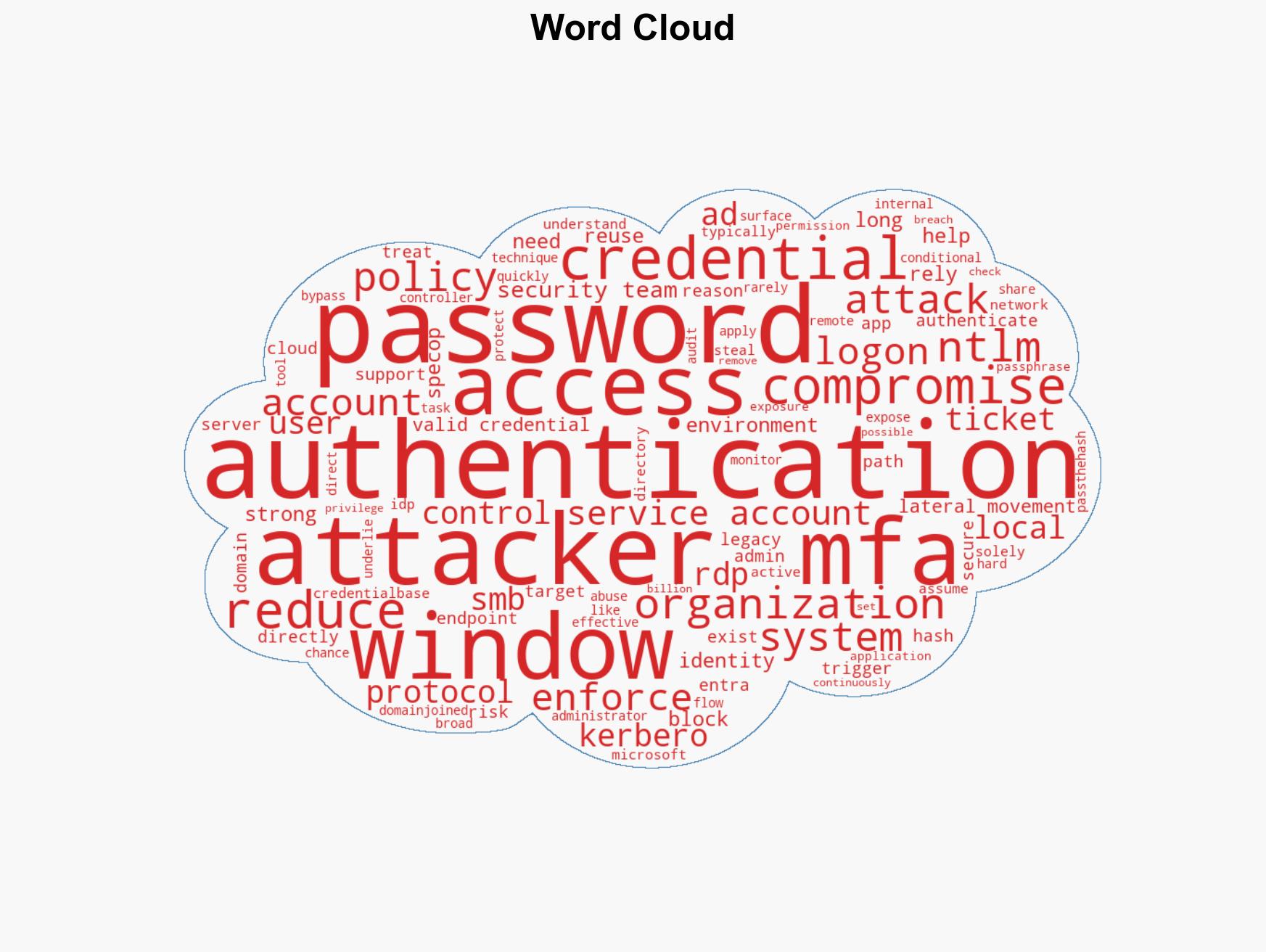
cybersecurity, multi-factor authentication, credential abuse, Windows environments, Active Directory, network security, identity management
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us