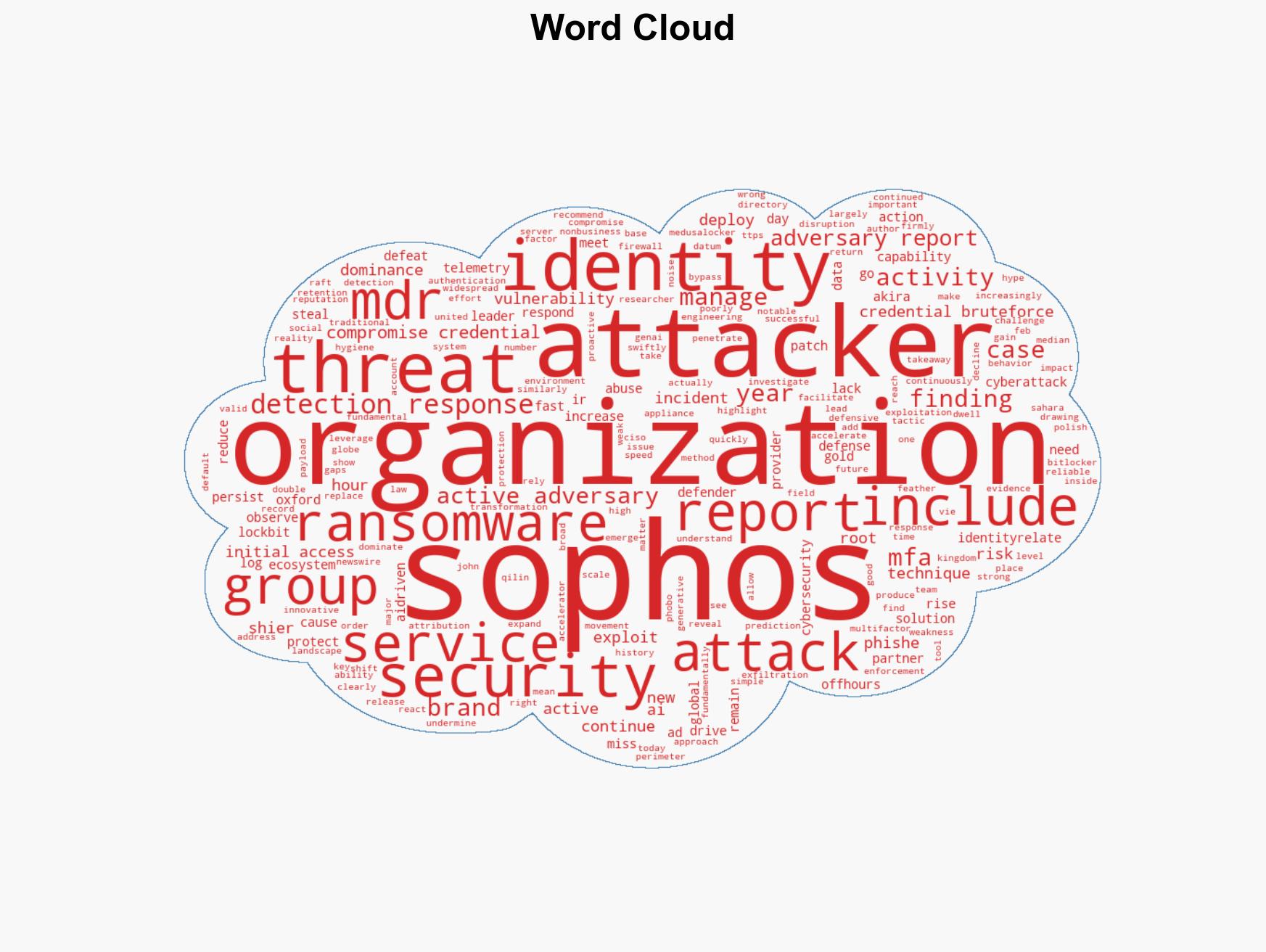
Identity-related attacks surge in 2026 as threat actors increasingly exploit compromised credentials
Published on: 2026-02-24
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
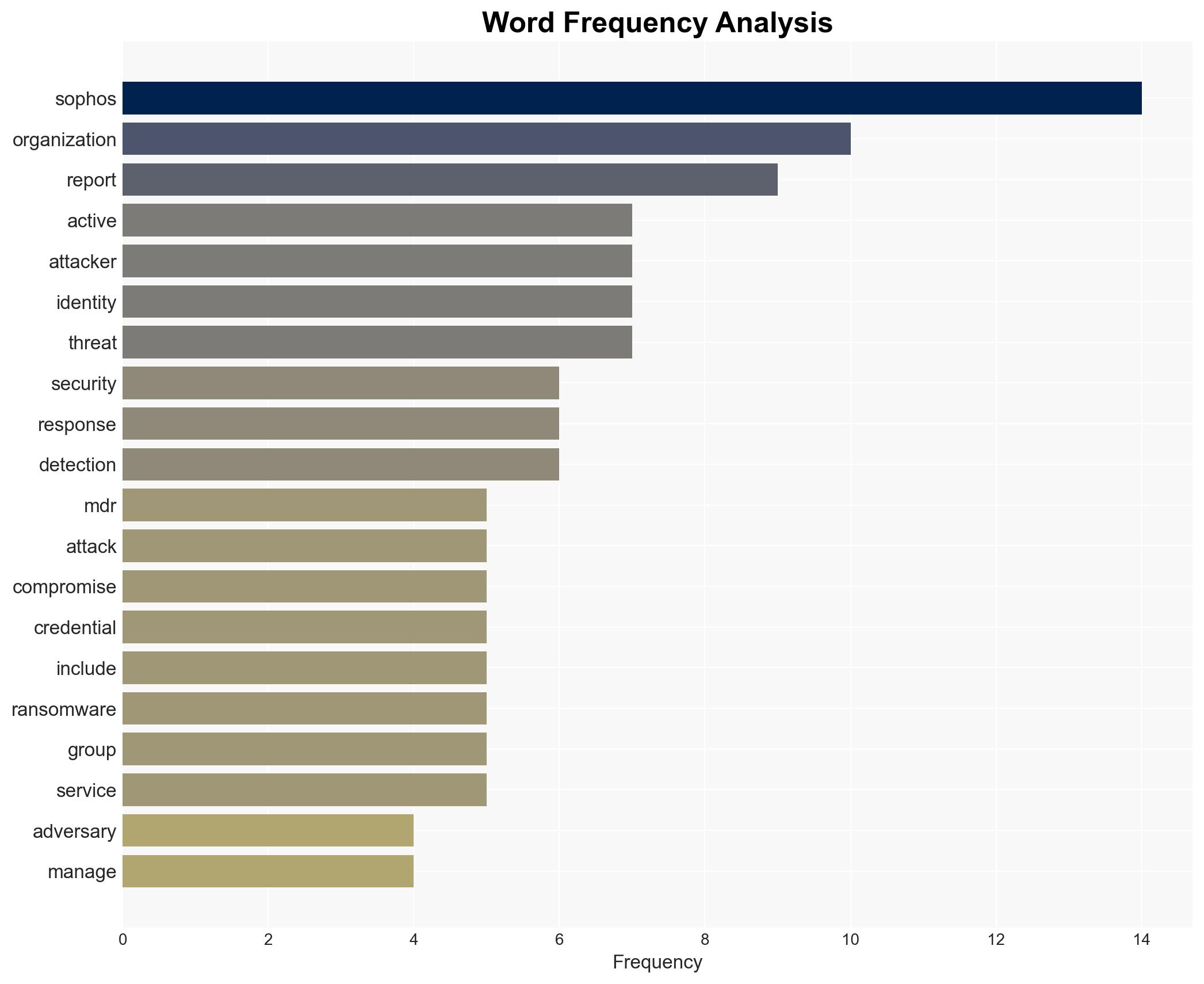
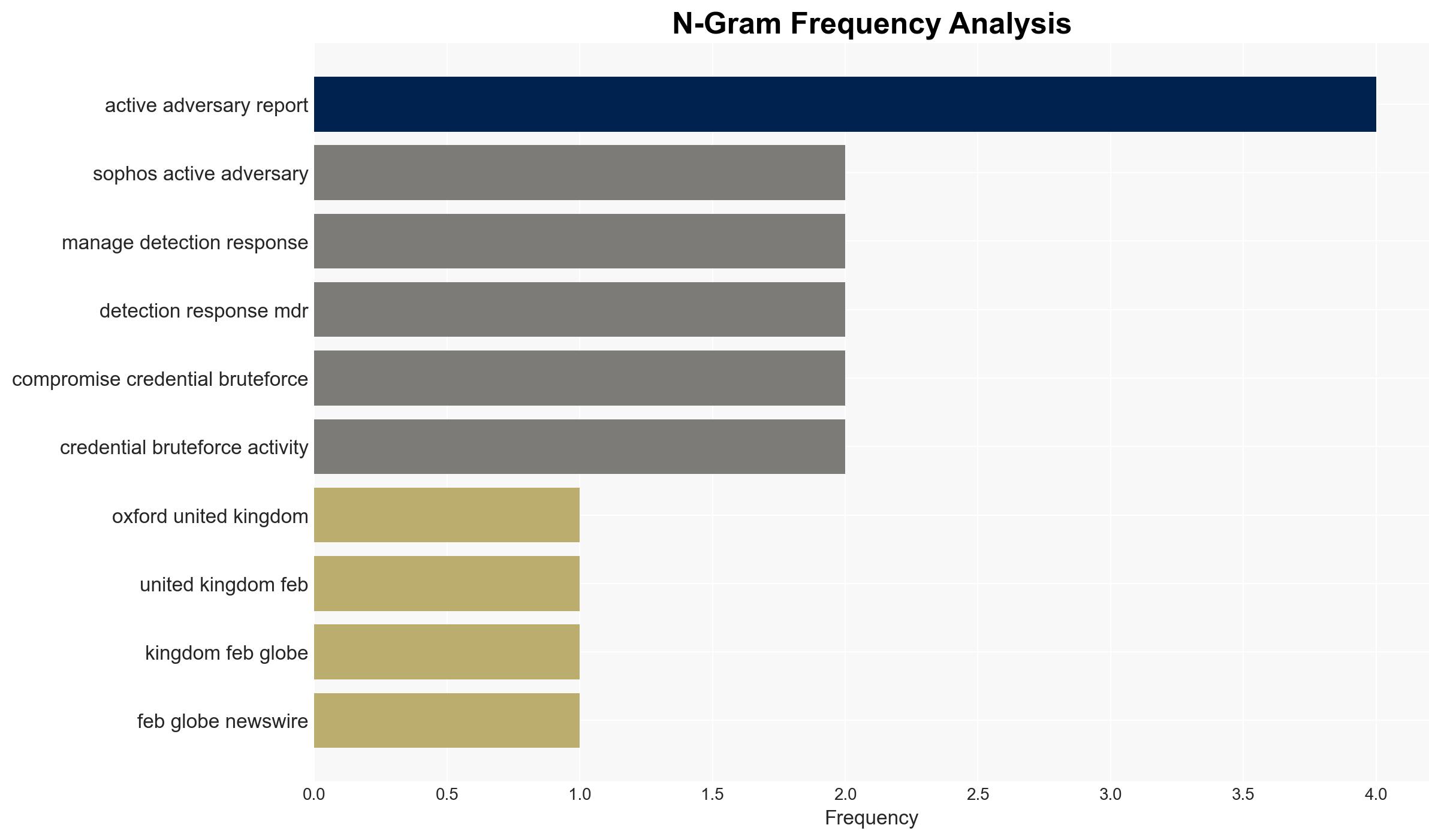
Intelligence Report: Sophos Active Adversary Report 2026 Identity attacks dominate as threat groups proliferate
1. BLUF (Bottom Line Up Front)
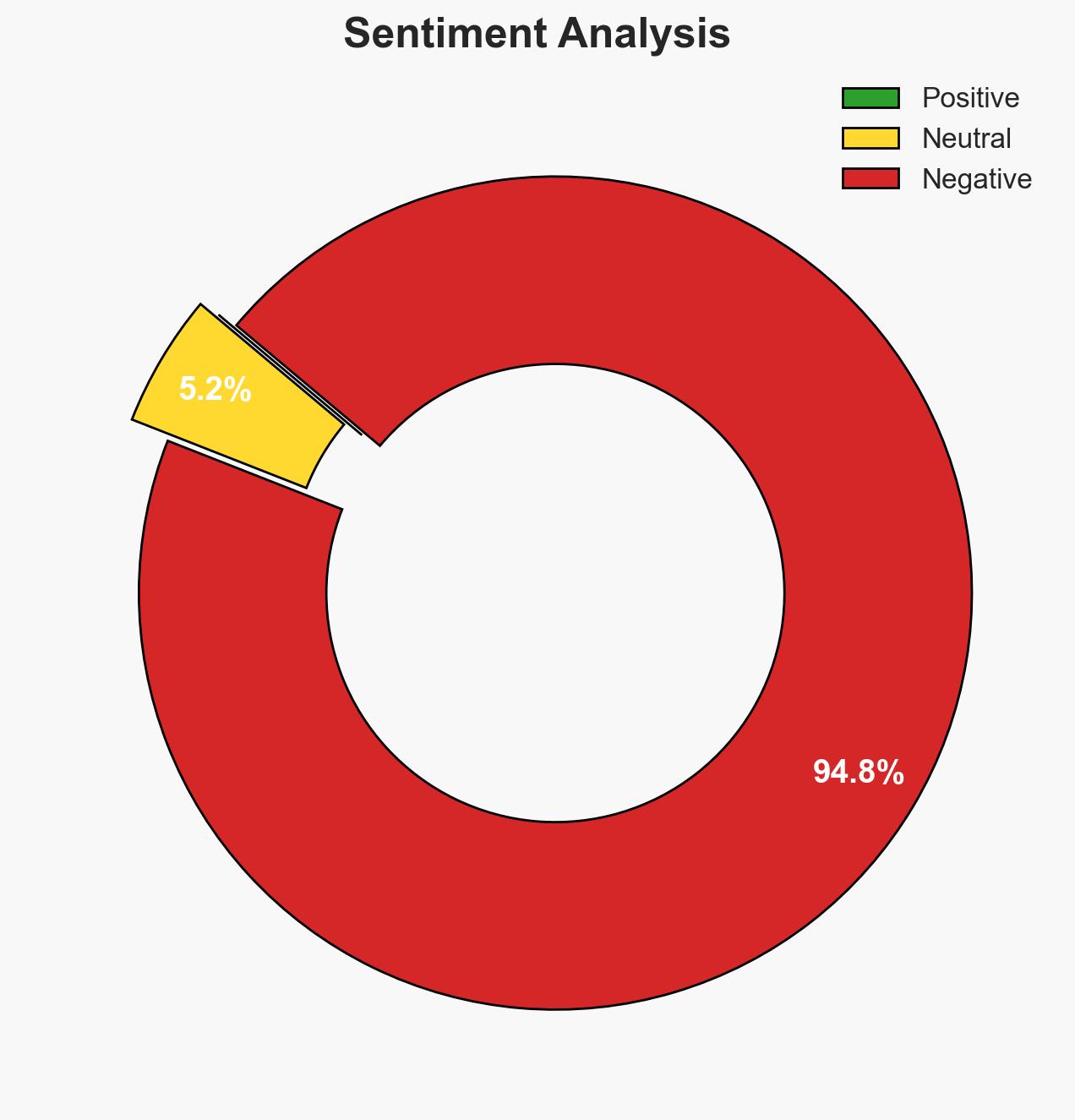
The 2026 Sophos Active Adversary Report indicates a significant shift towards identity-related cyberattacks, with 67% of incidents involving compromised credentials. This trend highlights vulnerabilities in identity security systems, exacerbated by the lack of multifactor authentication (MFA). The proliferation of threat groups further complicates the cyber threat landscape. Overall, there is moderate confidence in these findings due to the comprehensive data presented, though gaps in telemetry and potential biases in reporting are noted.
2. Competing Hypotheses
- Hypothesis A: The increase in identity-related attacks is primarily due to the exploitation of weak or absent MFA and compromised credentials. This is supported by the report’s findings of 59% of cases lacking MFA and the rapid exploitation of Active Directory. However, uncertainties remain regarding the full extent of these vulnerabilities across different sectors.
- Hypothesis B: The rise in identity-related attacks is driven by an increase in the number and sophistication of threat groups, rather than solely by technical vulnerabilities. This is supported by the report’s observation of the highest number of active threat groups. Contradictory evidence includes the consistent focus on identity vulnerabilities as a root cause.
- Assessment: Hypothesis A is currently better supported due to the direct link between identity vulnerabilities and attack success rates. Indicators that could shift this judgment include new data on threat group tactics or changes in MFA adoption rates.
3. Key Assumptions and Red Flags
- Assumptions: Organizations will continue to underutilize MFA; threat groups will maintain current levels of activity; identity systems will remain primary targets.
- Information Gaps: Detailed sector-specific data on MFA adoption and identity system vulnerabilities; comprehensive attribution data for threat groups.
- Bias & Deception Risks: Potential bias in data collection favoring incidents with identity-related issues; possible underreporting of successful MFA implementations.
4. Implications and Strategic Risks
The persistence of identity-related attacks could lead to increased regulatory scrutiny and demand for enhanced cybersecurity measures. This development may also influence threat group strategies and operational focus.
- Political / Geopolitical: Potential for increased international cooperation on cybersecurity standards and practices.
- Security / Counter-Terrorism: Heightened risk of cyber incidents impacting critical infrastructure and national security.
- Cyber / Information Space: Continued evolution of attack techniques targeting identity systems; potential for increased cyber espionage activities.
- Economic / Social: Possible economic impacts from increased cybersecurity spending and potential disruptions from successful cyberattacks.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of identity systems; prioritize MFA implementation; increase awareness of identity-related threats among stakeholders.
- Medium-Term Posture (1–12 months): Develop partnerships for threat intelligence sharing; invest in advanced identity protection technologies; conduct regular security audits.
- Scenario Outlook: Best: Widespread adoption of MFA reduces identity-related attacks. Worst: Increased sophistication of threat groups overwhelms current defenses. Most-Likely: Gradual improvement in identity security with continued threat group activity.
6. Key Individuals and Entities
- John Shier, Field CISO and lead author of the report
- Akira (GOLD SAHARA), ransomware group
- Qilin (GOLD FEATHER), ransomware group
- Not clearly identifiable from open sources in this snippet for other entities.
7. Thematic Tags
cybersecurity, identity security, cyber threats, ransomware, multifactor authentication, threat groups, cybersecurity strategy, data protection
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us