Imperva Protects Against Apache Tomcat Deserialization Vulnerability – Imperva.com
Published on: 2025-03-20
Intelligence Report: Imperva Protects Against Apache Tomcat Deserialization Vulnerability – Imperva.com
1. BLUF (Bottom Line Up Front)
A newly disclosed vulnerability, identified as CVE, affects Apache Tomcat, posing a high-risk threat due to a path equivalence flaw. This vulnerability allows unauthorized file access and potential remote code execution (RCE). Organizations using vulnerable Apache Tomcat versions should prioritize patching and implementing security measures. Imperva provides protection against this vulnerability, emphasizing the importance of proactive defense strategies.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
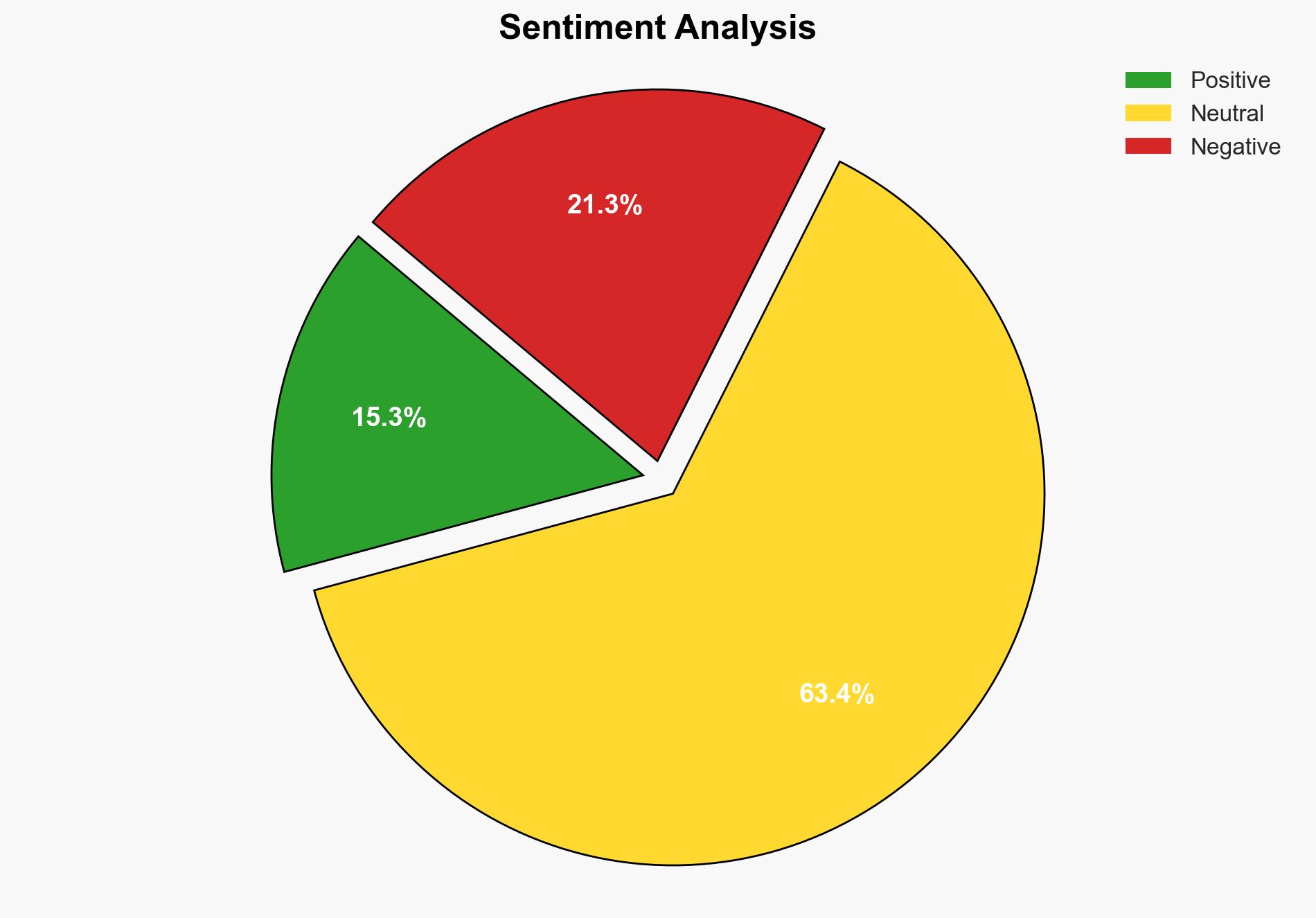
The CVE vulnerability arises from improper handling of path equivalence in Apache Tomcat, specifically when filenames contain internal dots. This flaw, combined with certain conditions such as default servlet write permissions, can lead to unauthorized file modifications and RCE. The vulnerability is particularly dangerous in environments where partial requests are supported. Imperva’s data indicates that attackers primarily target financial and business sites, exploiting the vulnerability for data theft and fraud.
3. Implications and Strategic Risks
The CVE vulnerability poses significant risks across multiple sectors, particularly for organizations relying on Apache Tomcat in enterprise applications, cloud environments, and SaaS platforms. The potential for unauthorized file access and RCE threatens national security, regional stability, and economic interests. The United States is the most frequently targeted country, with attackers focusing on industries handling sensitive data and financial transactions.
4. Recommendations and Outlook
Recommendations:
- Organizations should immediately apply patches released by Apache to address the vulnerability.
- Implement robust security configurations and utilize web application firewalls (WAF) like Imperva to mitigate risks.
- Conduct regular security audits and vulnerability assessments to identify and address potential threats.
Outlook:
In a best-case scenario, organizations promptly apply patches and enhance security measures, significantly reducing the risk of exploitation. In a worst-case scenario, failure to address the vulnerability could lead to widespread data breaches and financial losses. The most likely outcome involves a gradual reduction in successful attacks as awareness and mitigation efforts increase.
5. Key Individuals and Entities
The report references Imperva as a key entity providing protection against the CVE vulnerability. No specific individuals are mentioned in the context of this report.