Inside The Bybit Hacking Incident Lessons From The Breach – Forbes
Published on: 2025-04-01
Intelligence Report: Inside The Bybit Hacking Incident Lessons From The Breach – Forbes
1. BLUF (Bottom Line Up Front)
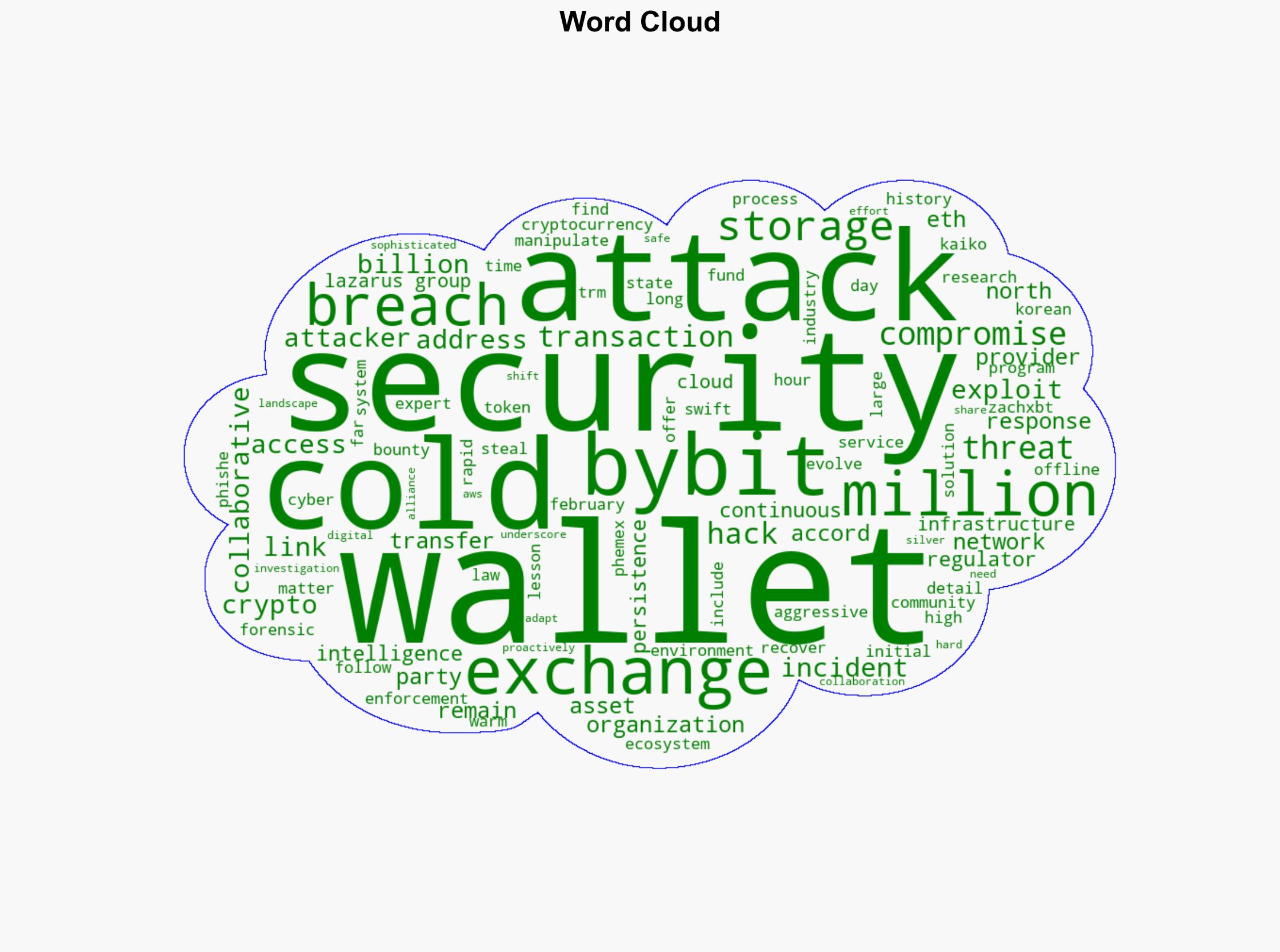
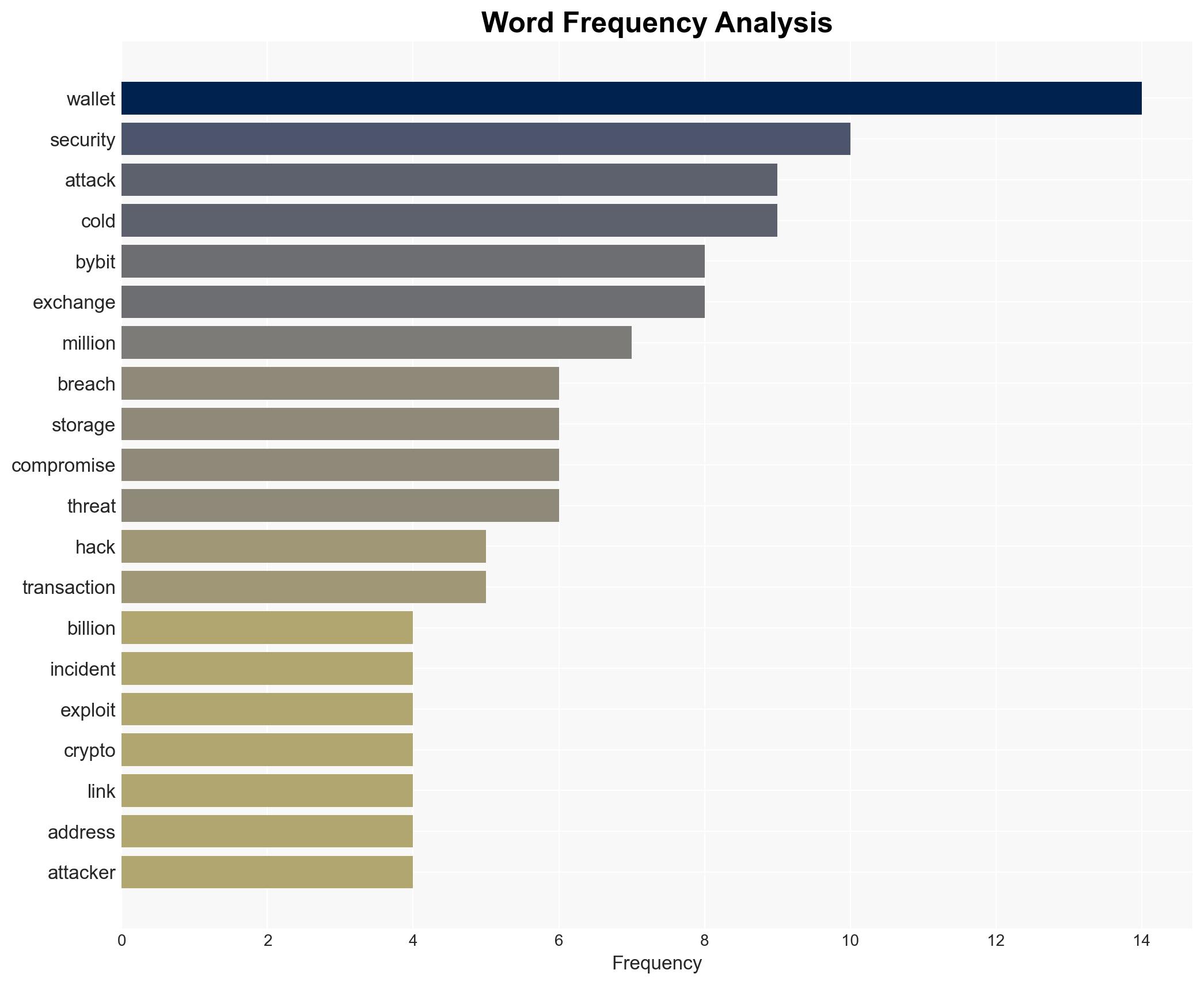
The Bybit hacking incident represents one of the largest cryptocurrency heists in history, with approximately $1 billion in Ethereum tokens stolen. The attack, attributed to the North Korean cybercriminal organization known as the Lazarus Group, highlights significant vulnerabilities in cryptocurrency exchange security protocols. The incident underscores the need for enhanced security measures and collaborative defense strategies within the cryptocurrency ecosystem.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
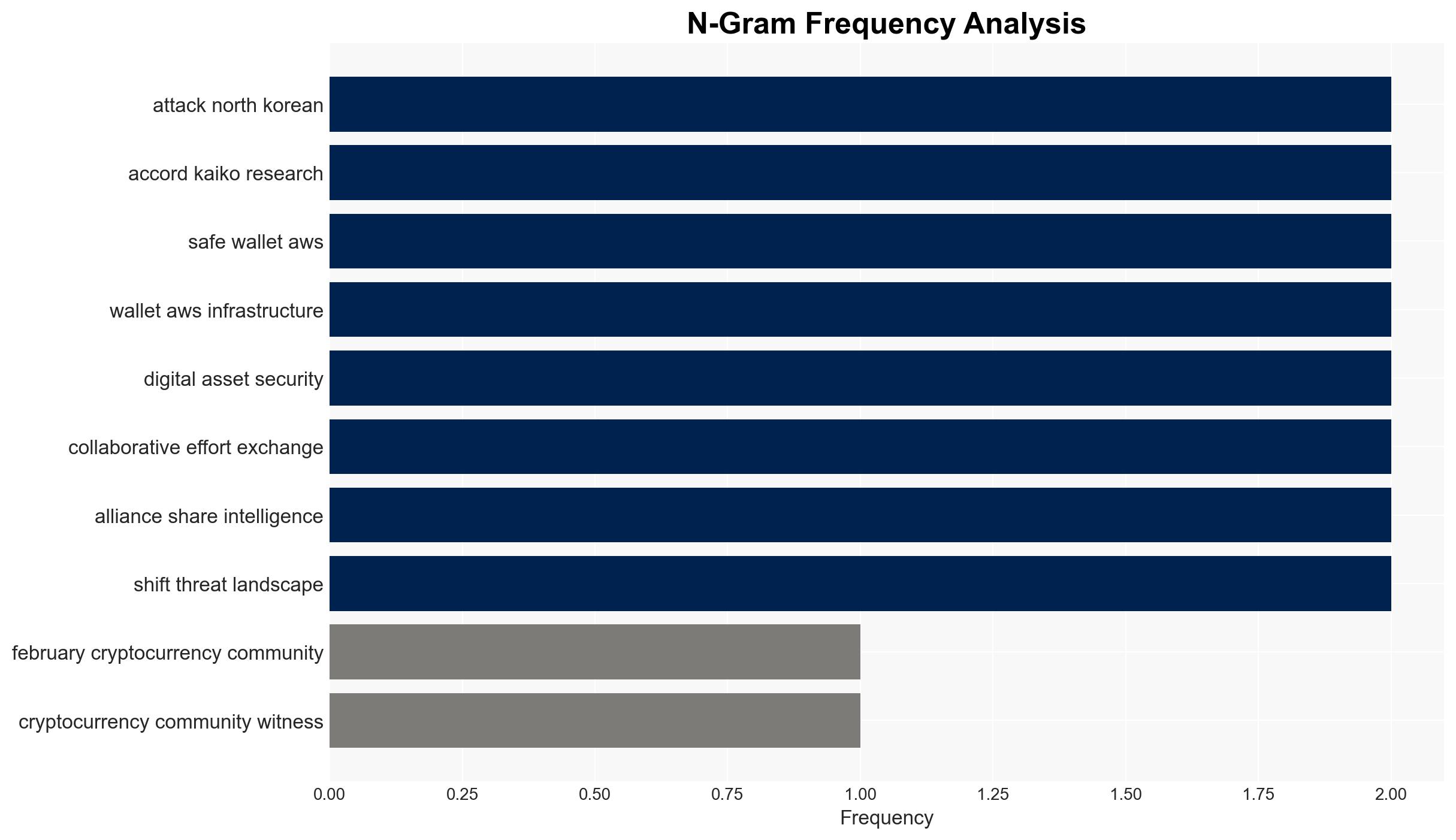
The Bybit hack involved sophisticated cyber warfare tactics, including exploiting faulty code and using advanced phishing and social engineering techniques. Attackers compromised a third-party service provider to inject malicious JavaScript into the transaction signing workflow, allowing unauthorized access to internal credentials. The speed and complexity of the operation, including laundering funds through decentralized exchanges and cross-chain bridges, demonstrate a high level of operational efficiency.
3. Implications and Strategic Risks
The attack poses significant risks to national security and economic interests, given the involvement of state-sponsored actors. The persistence and stealth of the Lazarus Group highlight the potential for future attacks on cryptocurrency exchanges and related financial systems. The incident also raises concerns about the adequacy of current regulatory frameworks and the need for improved international cooperation in combating cybercrime.
4. Recommendations and Outlook
Recommendations:
- Enhance security protocols for cryptocurrency exchanges, including multi-signature approval processes and offline storage solutions.
- Strengthen collaboration between cryptocurrency companies, law enforcement, and national security organizations to improve threat intelligence sharing and response coordination.
- Implement regulatory changes to address vulnerabilities in third-party service providers and improve oversight of cryptocurrency transactions.
Outlook:
In the best-case scenario, increased collaboration and improved security measures will mitigate the risk of future attacks. In the worst-case scenario, continued vulnerabilities could lead to further high-profile breaches, undermining trust in the cryptocurrency ecosystem. The most likely outcome is a gradual improvement in security protocols and regulatory frameworks, driven by ongoing collaboration and technological advancements.
5. Key Individuals and Entities
The report mentions significant individuals and organizations, including ZachXBT, Nick Carlsen, and the Lazarus Group. These entities play critical roles in the analysis and attribution of the attack, as well as in the broader context of cybersecurity and cryptocurrency security.