Integrating AI with Cybersecurity: A Critical National Security Strategy for the Administration
Published on: 2026-03-03
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Why the convergence of AI and cybersecurity must be a top priority for the administration
1. BLUF (Bottom Line Up Front)
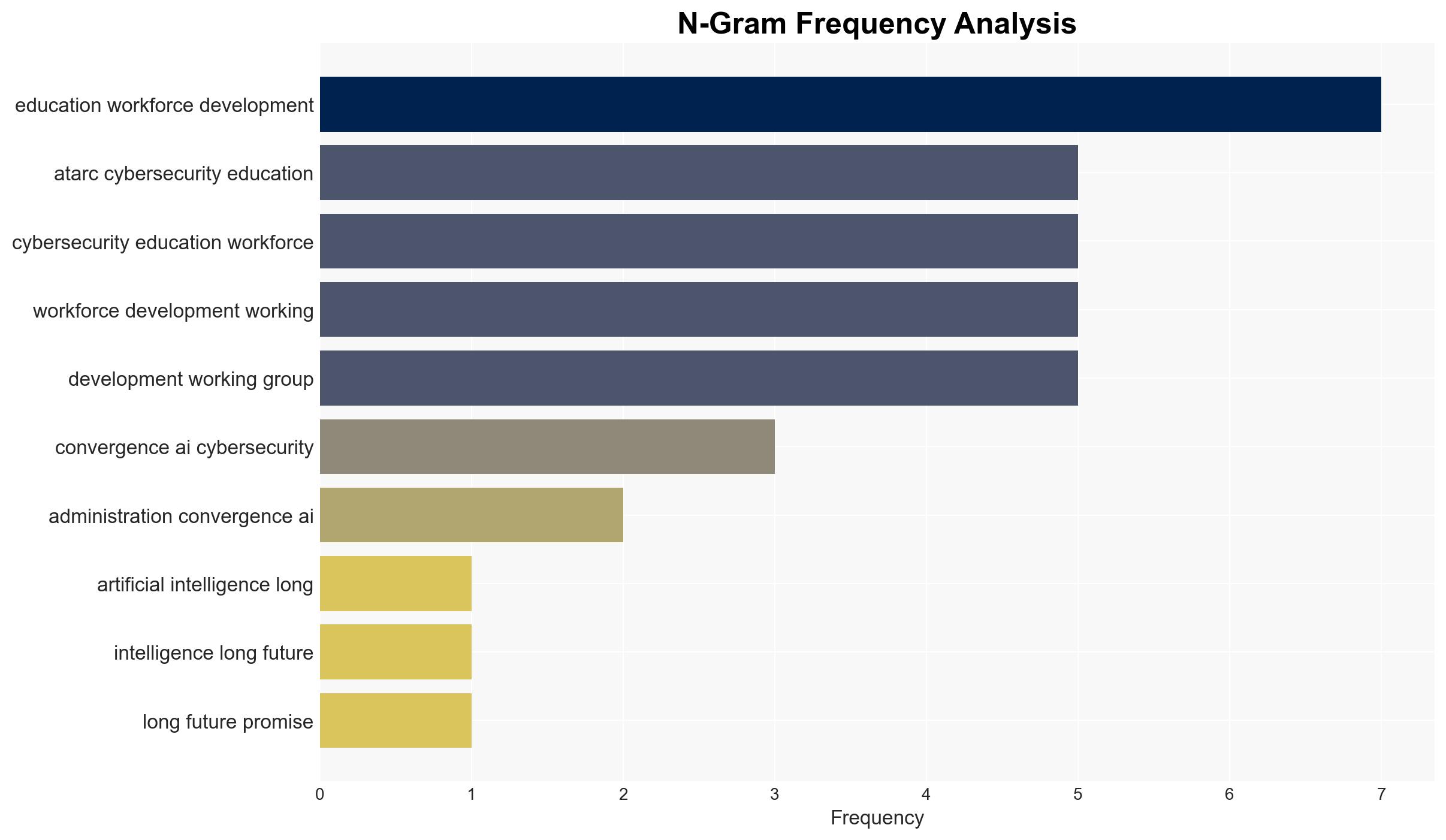
The convergence of AI and cybersecurity is a critical national security priority due to its dual role as both a tool and a threat. The federal government must address the workforce and governance challenges to modernize effectively. The most likely hypothesis is that AI will continue to reshape cybersecurity practices, necessitating immediate investment in skills development. Overall confidence in this judgment is moderate.
2. Competing Hypotheses
- Hypothesis A: AI integration into cybersecurity will enhance defense capabilities, allowing federal agencies to better detect and respond to threats. This is supported by the current reliance on AI for anomaly detection and predictive threat intelligence. However, uncertainties include the pace of AI adoption and the effectiveness of workforce training.
- Hypothesis B: AI will primarily benefit adversaries, leading to more sophisticated cyberattacks that outpace defensive measures. This is supported by AI’s potential to automate and enhance attack strategies. Contradicting evidence includes ongoing efforts to integrate AI into defense strategies.
- Assessment: Hypothesis A is currently better supported due to the proactive measures being taken to incorporate AI into cybersecurity frameworks. Key indicators that could shift this judgment include significant advancements in adversarial AI capabilities or failures in workforce development initiatives.
3. Key Assumptions and Red Flags
- Assumptions: AI technology will continue to evolve rapidly; federal agencies will prioritize AI-cybersecurity integration; workforce development programs will be effective.
- Information Gaps: Detailed data on the current state of AI integration in federal cybersecurity operations and the effectiveness of existing workforce training programs.
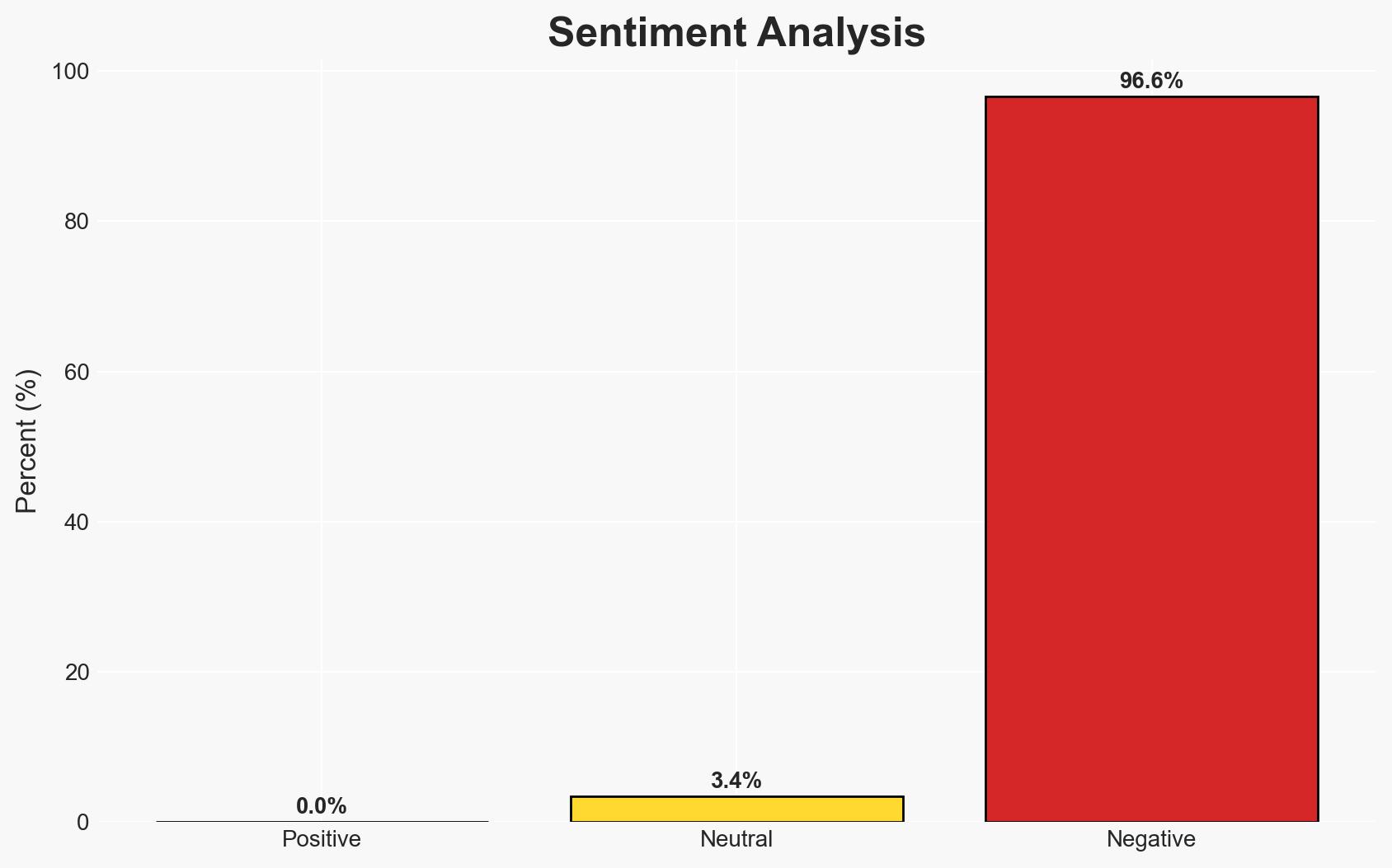
- Bias & Deception Risks: Potential bias in the evaluation of AI’s effectiveness due to vested interests in technology adoption; risk of adversarial misinformation campaigns exaggerating AI threats.
4. Implications and Strategic Risks
The convergence of AI and cybersecurity is likely to redefine digital conflict landscapes, impacting national security and economic stability. The evolution of this dynamic will depend on the balance between defensive and offensive AI capabilities.
- Political / Geopolitical: Increased pressure on international norms and agreements regarding AI and cybersecurity usage.
- Security / Counter-Terrorism: Enhanced capabilities for threat detection but also potential for more complex cyber threats.
- Cyber / Information Space: Potential for AI-driven misinformation and cyber-espionage campaigns.
- Economic / Social: Workforce displacement and retraining challenges; potential economic impacts from cyber disruptions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive assessment of current AI-cybersecurity capabilities and gaps; initiate targeted workforce training programs.
- Medium-Term Posture (1–12 months): Develop partnerships with private sector and academia for AI research and development; enhance inter-agency collaboration on AI-cybersecurity initiatives.
- Scenario Outlook:
- Best: Successful integration of AI enhances cybersecurity defenses, reducing threat impact.
- Worst: AI advancements primarily benefit adversaries, leading to increased cyber incidents.
- Most-Likely: Gradual improvement in AI-cybersecurity integration with ongoing challenges in workforce adaptation.
6. Key Individuals and Entities
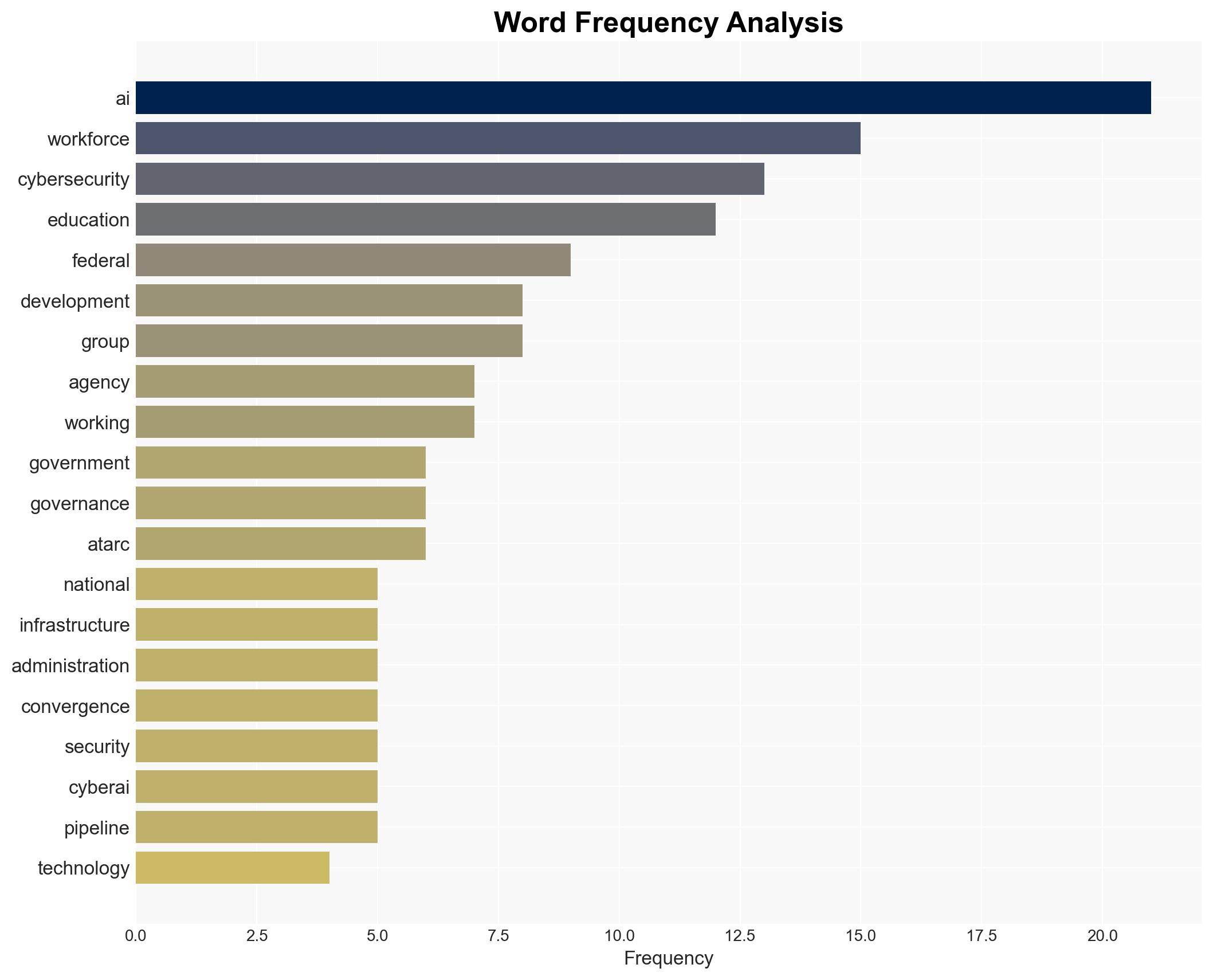
- ATARC Cybersecurity Education and Workforce Development Working Group
- Federal cybersecurity teams
- GovExec (owner of ATARC and Nextgov/FCW)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
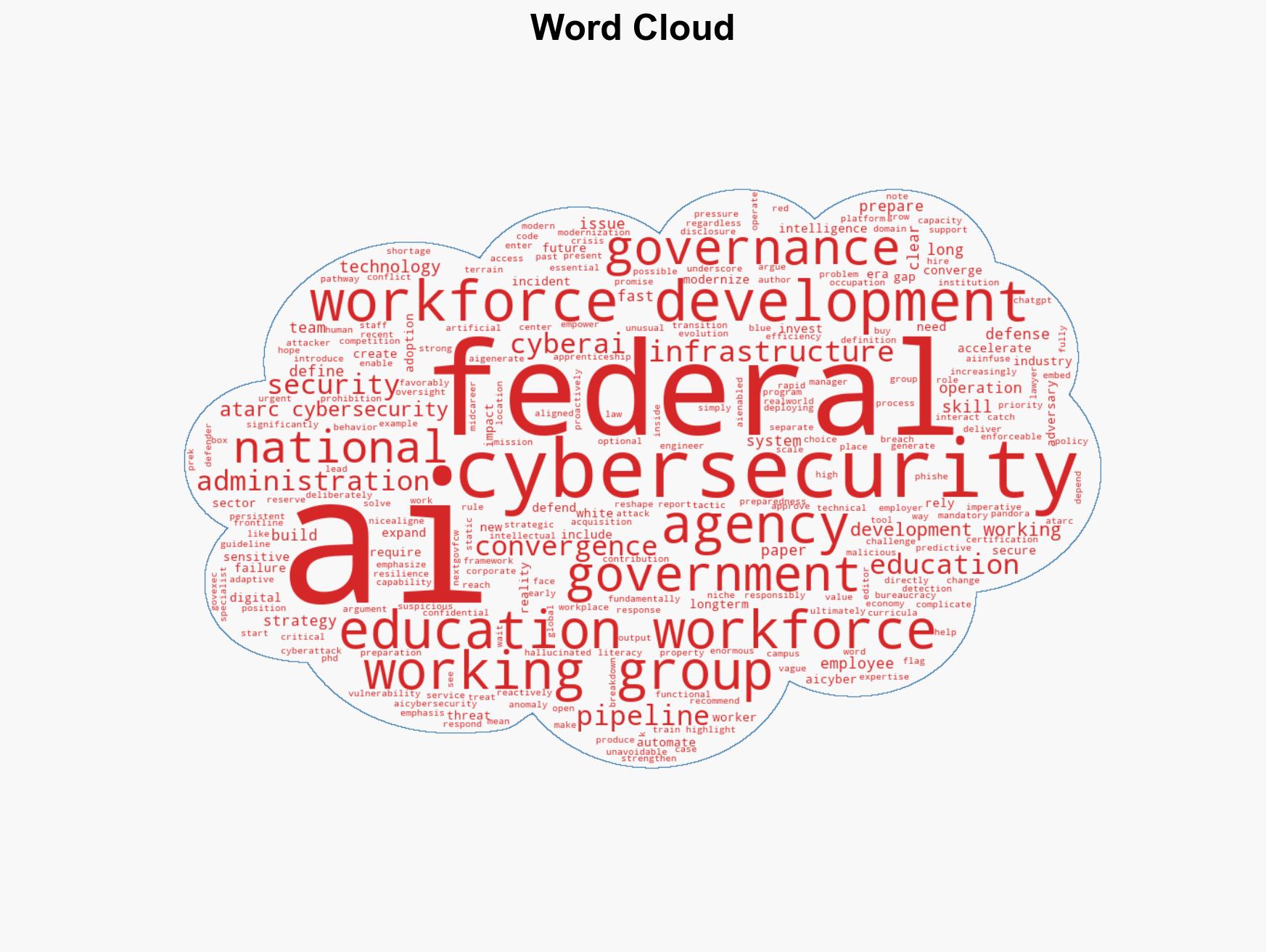
cybersecurity, AI integration, workforce development, national security, digital conflict, cyber defense, adversarial AI
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us