Introducing Cisco Talos Incident Response: Your Crisis Management Experts in Cybersecurity Emergencies
Published on: 2026-03-20
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Meet Your Incident Responders
1. BLUF (Bottom Line Up Front)
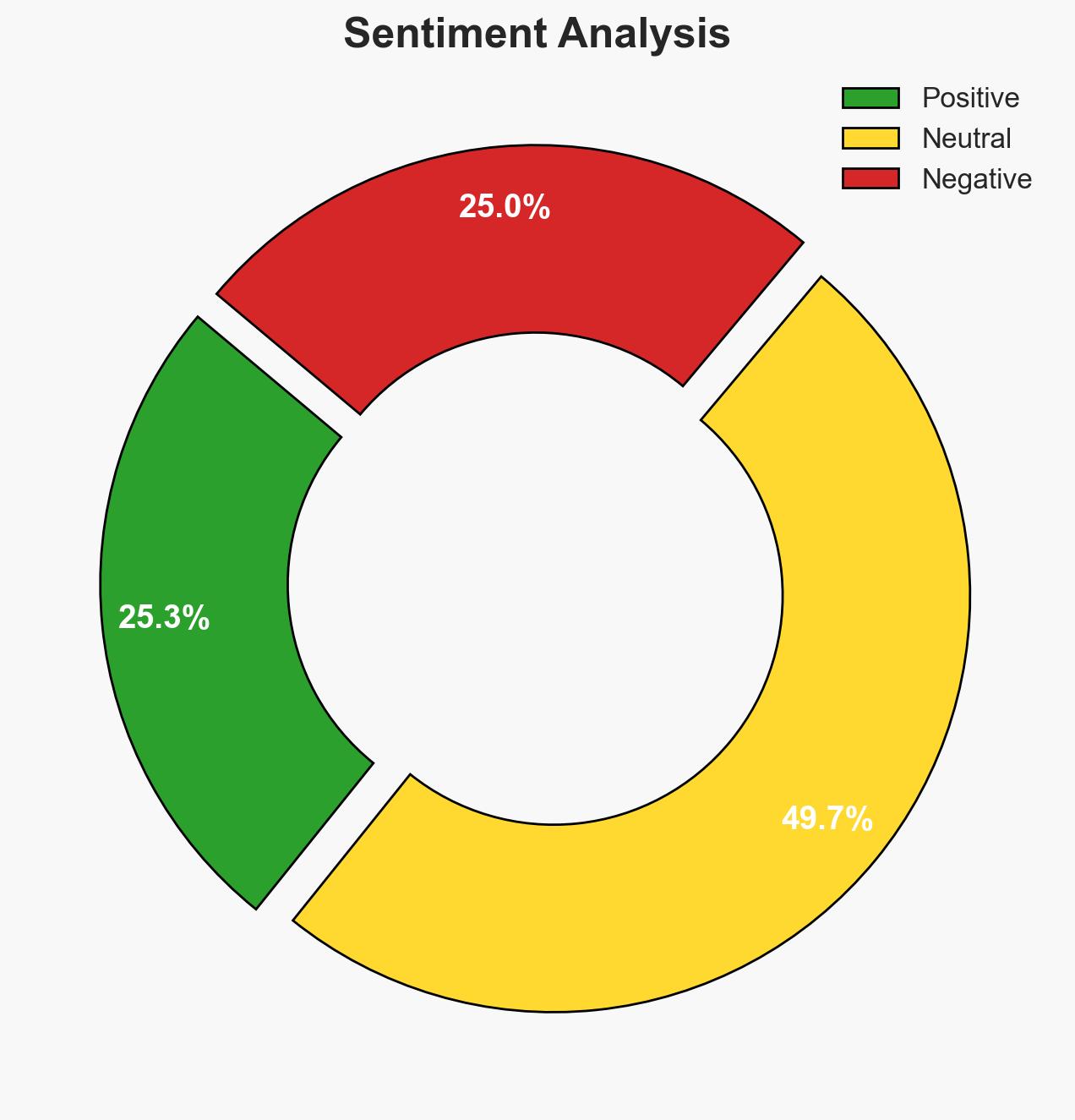
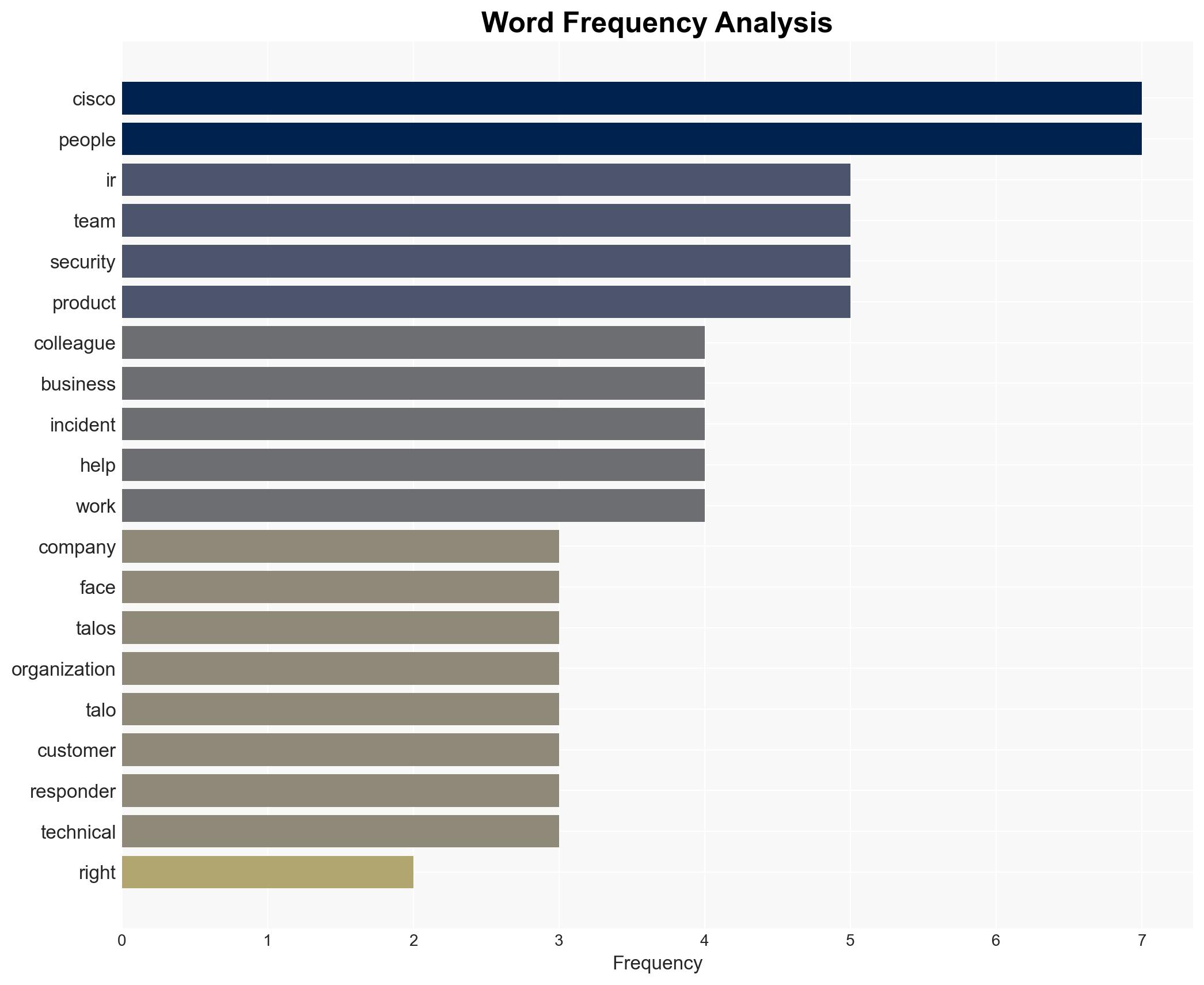
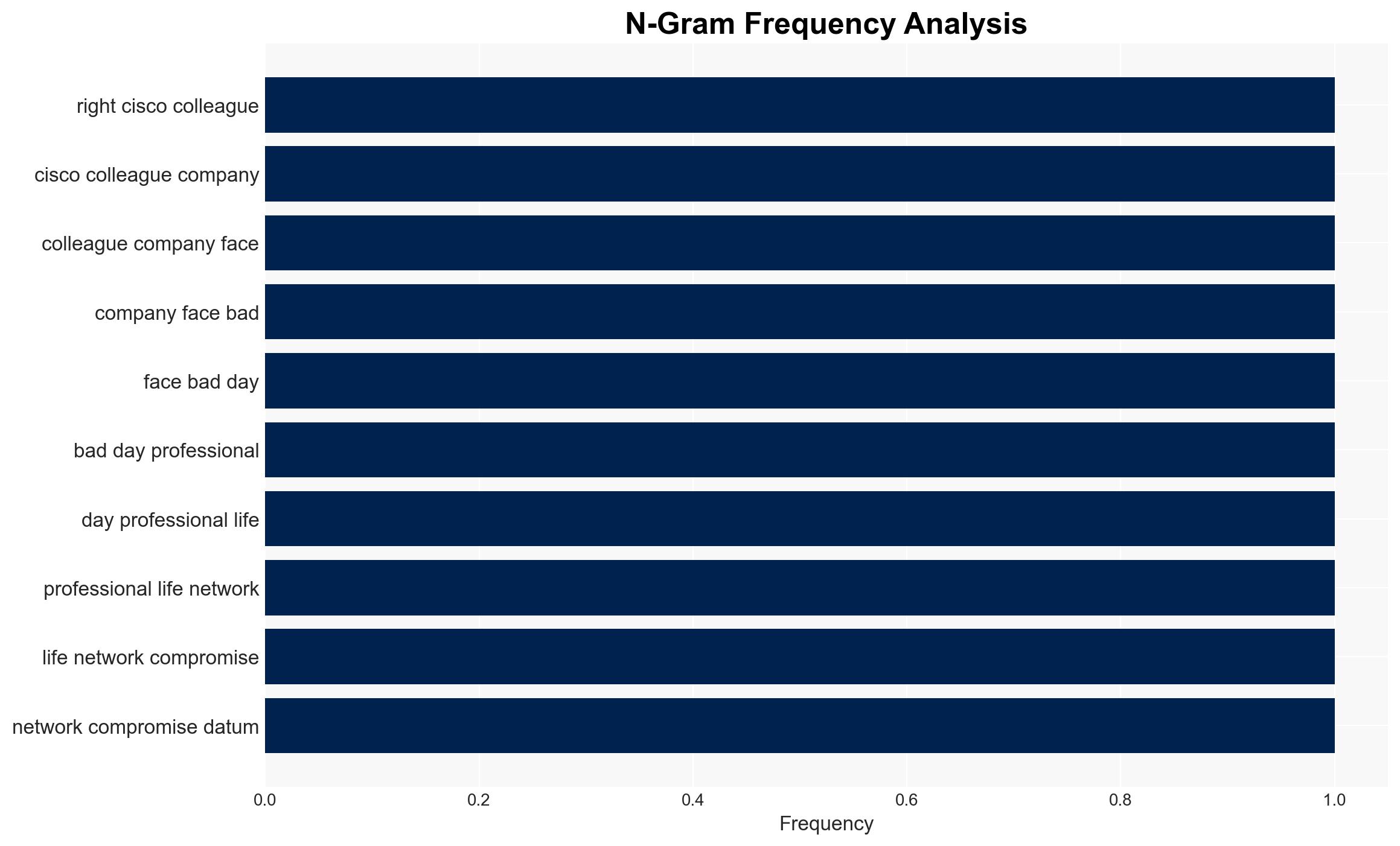
The Cisco Talos Incident Response (IR) team plays a critical role in mitigating cybersecurity incidents for organizations, providing both technical expertise and empathetic support. The most likely hypothesis is that Talos IR enhances Cisco’s product offerings by integrating field intelligence, thus strengthening customer trust and security posture. This affects organizations across various sectors facing cyber threats. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: Talos IR primarily enhances Cisco’s product efficacy by feeding real-time threat intelligence back into product development. Supporting evidence includes the integration of field intelligence into Cisco products. Key uncertainties involve the extent of this integration and its direct impact on product improvements.
- Hypothesis B: Talos IR’s primary function is to serve as a marketing tool to differentiate Cisco from competitors by showcasing their commitment to customer support. This is supported by the emphasis on Talos IR’s unique role and commitment. Contradicting evidence includes the technical focus and intelligence integration mentioned.
- Assessment: Hypothesis A is currently better supported due to explicit mentions of intelligence feedback into product development. Indicators that could shift this judgment include evidence of Talos IR being primarily used in marketing strategies without significant product impact.
3. Key Assumptions and Red Flags
- Assumptions: Talos IR effectively integrates field intelligence into product development; Talos IR’s presence significantly mitigates cybersecurity incidents; Cisco’s commitment to customer support is genuine and not primarily marketing-driven.
- Information Gaps: Specific metrics on how Talos IR’s intelligence integration improves product security; detailed case studies of Talos IR’s impact on incident resolution.
- Bias & Deception Risks: Potential bias in source material emphasizing positive aspects of Talos IR; lack of external validation of Talos IR’s effectiveness could indicate a marketing bias.
4. Implications and Strategic Risks
The development of Talos IR could lead to enhanced cybersecurity resilience for organizations and increased market competitiveness for Cisco. However, reliance on Talos IR without broader security measures could pose risks.
- Political / Geopolitical: Increased cybersecurity resilience could reduce vulnerability to state-sponsored cyber attacks.
- Security / Counter-Terrorism: Enhanced incident response capabilities may deter cyber-terrorism efforts targeting critical infrastructure.
- Cyber / Information Space: Talos IR’s intelligence integration could set industry standards for incident response and product development.
- Economic / Social: Improved cybersecurity could foster economic stability by protecting businesses from financial losses due to cyber incidents.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor Talos IR’s integration with product development; assess customer feedback on incident response effectiveness.
- Medium-Term Posture (1–12 months): Develop partnerships with other cybersecurity entities to enhance intelligence sharing; invest in training and capacity building for Talos IR.
- Scenario Outlook:
- Best: Talos IR significantly enhances Cisco’s market position and cybersecurity resilience.
- Worst: Talos IR fails to integrate effectively, leading to customer dissatisfaction and increased vulnerability.
- Most-Likely: Talos IR continues to provide valuable intelligence, moderately enhancing product security and customer trust.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
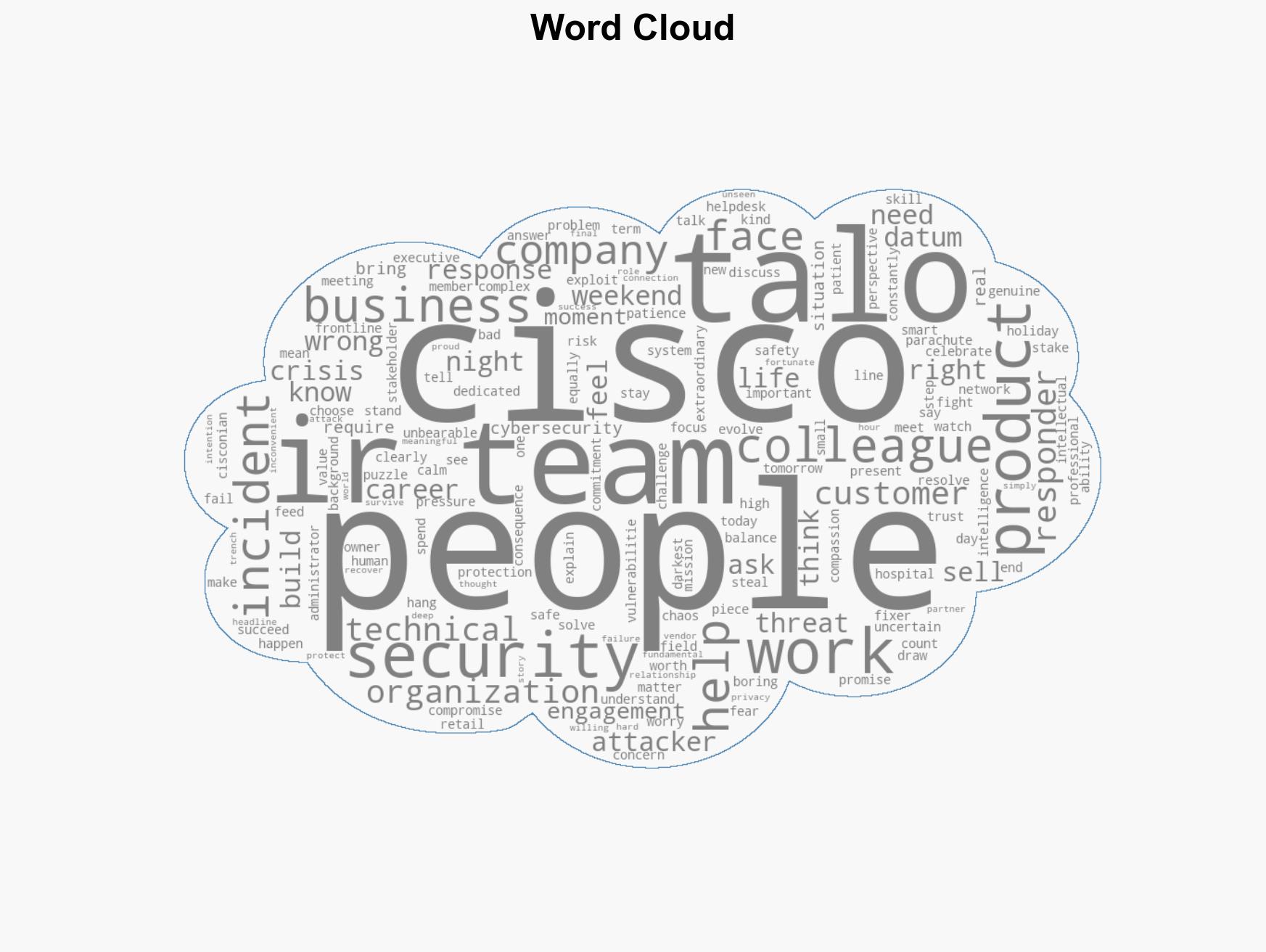
cybersecurity, incident response, threat intelligence, Cisco, product development, customer support, market differentiation
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us