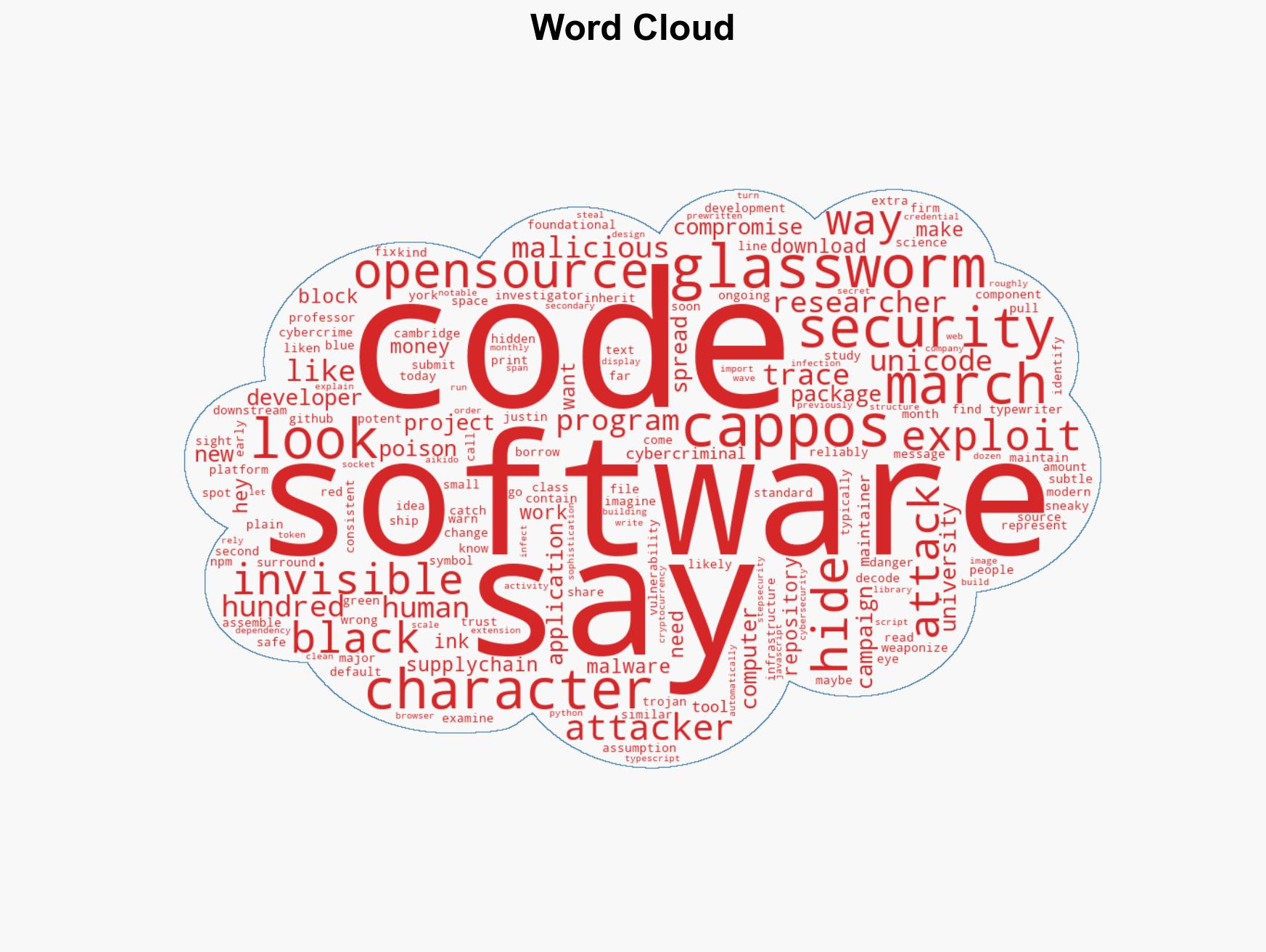
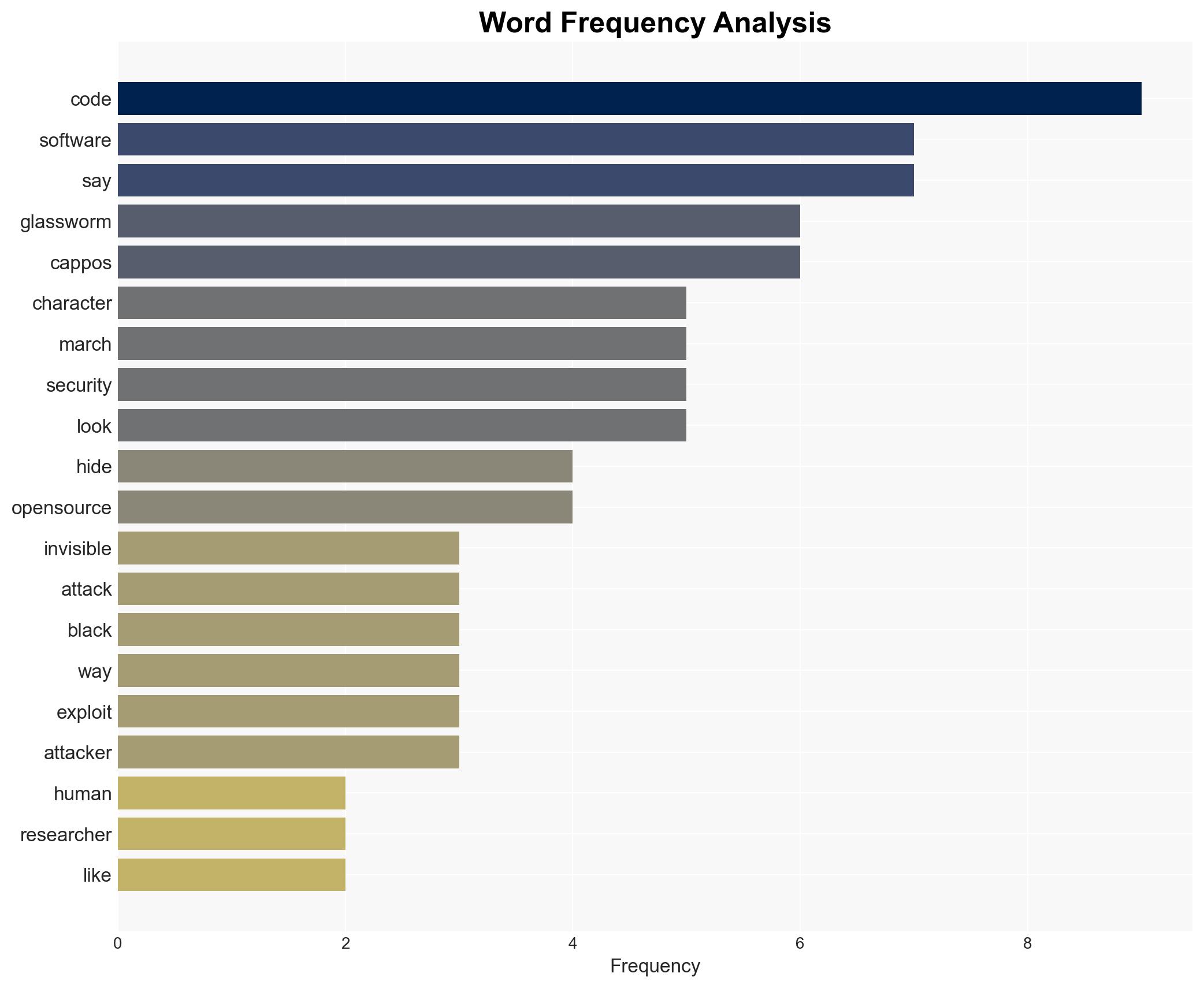
Invisible Unicode Characters Enable GlassWorm Malware to Compromise Open-Source Software Supply Chains
Published on: 2026-03-21
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: GlassWorm malware hides in invisible open-source code
1. BLUF (Bottom Line Up Front)
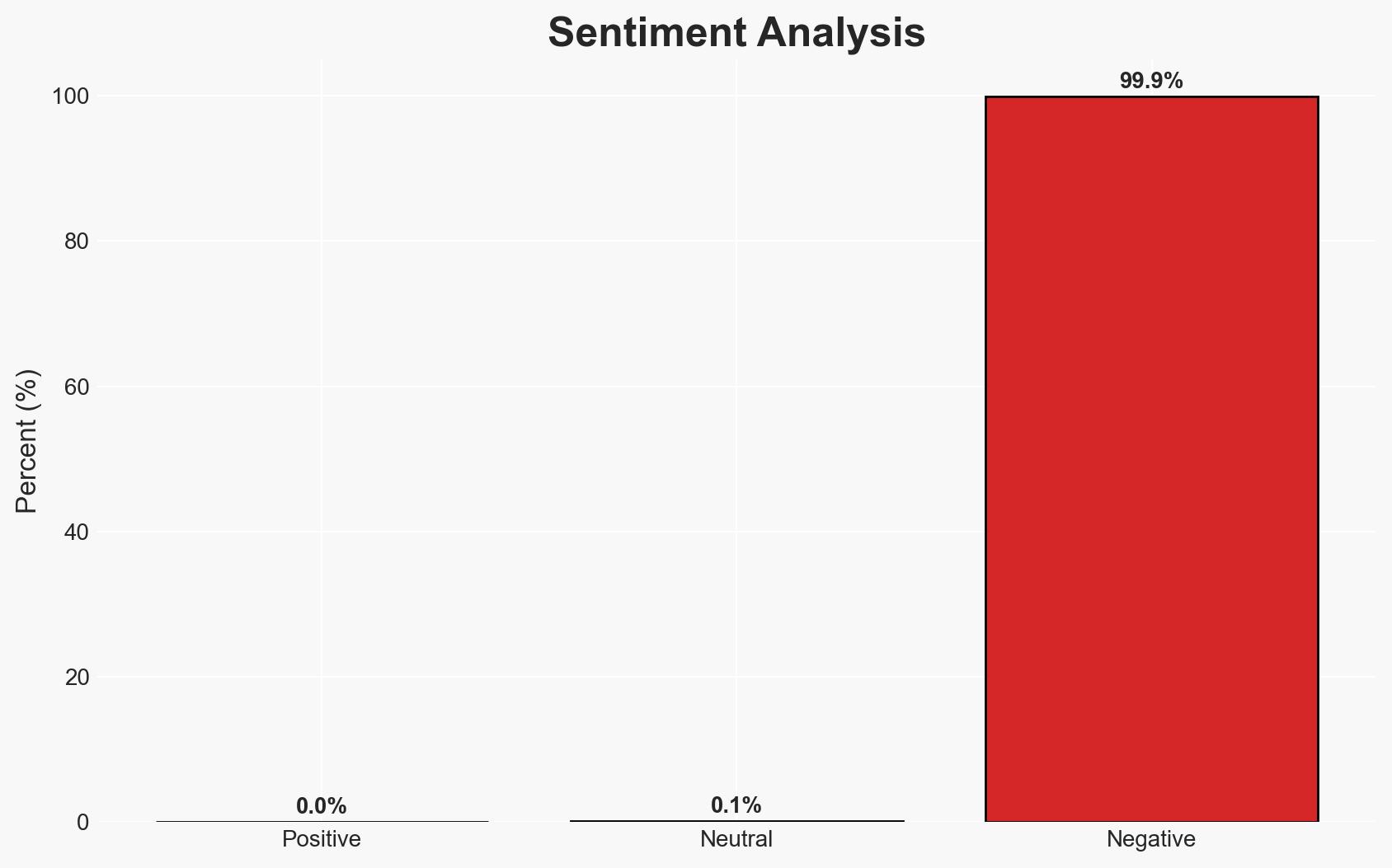
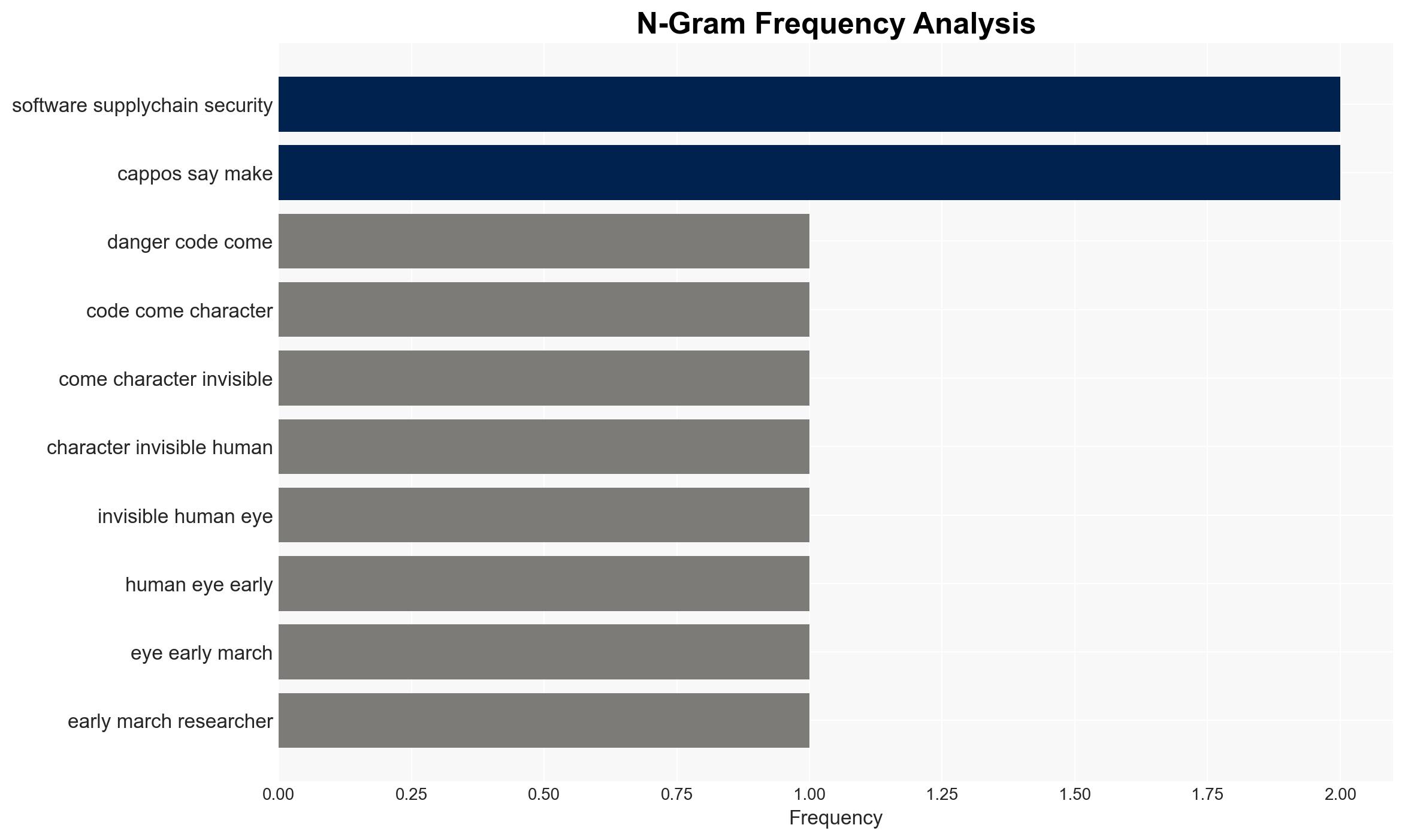
The GlassWorm malware campaign exploits invisible Unicode characters to compromise open-source software components, posing a significant threat to software supply chains. This campaign undermines foundational trust in open-source development and could have widespread implications across various sectors. Current analysis supports the hypothesis that this is a sophisticated cybercrime operation rather than state-sponsored activity. Overall confidence in this judgment is moderate.
2. Competing Hypotheses
- Hypothesis A: GlassWorm is a cybercrime campaign aimed at financial gain by exploiting open-source software vulnerabilities. Supporting evidence includes the use of sophisticated techniques to hide malicious code and the targeting of widely-used developer platforms. However, there is uncertainty regarding the ultimate goals and potential state involvement.
- Hypothesis B: GlassWorm is a state-sponsored operation designed to disrupt or surveil critical infrastructure by compromising software supply chains. While the scale and sophistication could suggest state involvement, there is limited direct evidence linking the campaign to any specific nation-state actor.
- Assessment: Hypothesis A is currently better supported due to the lack of direct evidence of state sponsorship and the typical financial motivations associated with cybercrime. Indicators that could shift this judgment include attribution to a nation-state or evidence of targeting critical infrastructure.
3. Key Assumptions and Red Flags
- Assumptions: Open-source software is inherently vulnerable to such attacks; the campaign is primarily financially motivated; current detection capabilities are limited.
- Information Gaps: Specific attribution of the actors behind GlassWorm; detailed impact assessment on affected systems; potential connections to other known cyber campaigns.
- Bias & Deception Risks: Confirmation bias towards viewing all sophisticated cyber attacks as state-sponsored; potential misinformation from compromised sources.
4. Implications and Strategic Risks
The GlassWorm campaign could lead to increased scrutiny and regulation of open-source software, impacting development practices and trust. It may also prompt a reevaluation of software supply chain security measures.
- Political / Geopolitical: Potential for increased geopolitical tensions if state sponsorship is suspected or confirmed.
- Security / Counter-Terrorism: Heightened threat environment for software supply chains and potential for similar tactics to be used in future cyber-terrorism efforts.
- Cyber / Information Space: Increased focus on securing software dependencies and enhancing detection of hidden code manipulations.
- Economic / Social: Potential economic impact on companies reliant on open-source software and increased costs for implementing enhanced security measures.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of open-source repositories for similar attack patterns; increase collaboration with cybersecurity firms to identify and mitigate threats.
- Medium-Term Posture (1–12 months): Develop partnerships with open-source communities to improve code review processes; invest in advanced detection technologies for hidden code manipulations.
- Scenario Outlook:
- Best: Enhanced security measures prevent future attacks, restoring trust in open-source software.
- Worst: Continued exploitation leads to significant disruptions in critical systems.
- Most-Likely: Incremental improvements in detection and response reduce the impact of similar future campaigns.
6. Key Individuals and Entities
- Justin Cappos, Professor of Computer Science, New York University
- Cybersecurity companies: Aikido, StepSecurity, Socket
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, open-source software, malware, software supply chain, cybercrime, Unicode, software vulnerabilities
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us