Iran Declares US Tech Firms in the Middle East as Potential Targets Amid Escalating Conflict
Published on: 2026-04-01
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Iran Threatens to Strike US Tech Companies in the Middle East
1. BLUF (Bottom Line Up Front)
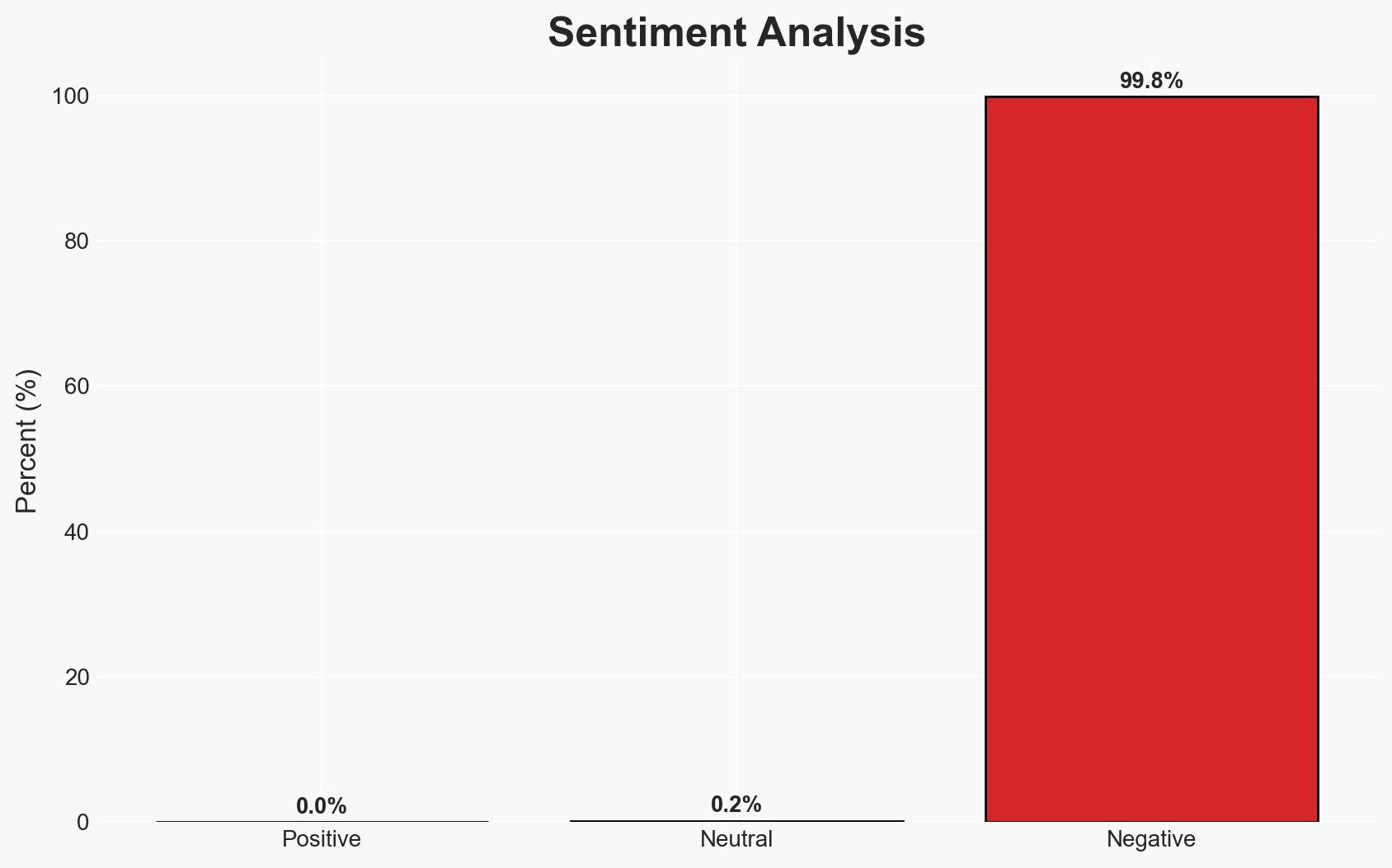
Iran’s Islamic Revolutionary Guards Corps (IRGC) has threatened to target US technology companies in the Middle East, potentially escalating regional tensions. The threat appears focused on disruption rather than physical harm, with implications for cybersecurity and economic stability. This assessment is made with moderate confidence, given the available evidence and current geopolitical context.
2. Competing Hypotheses
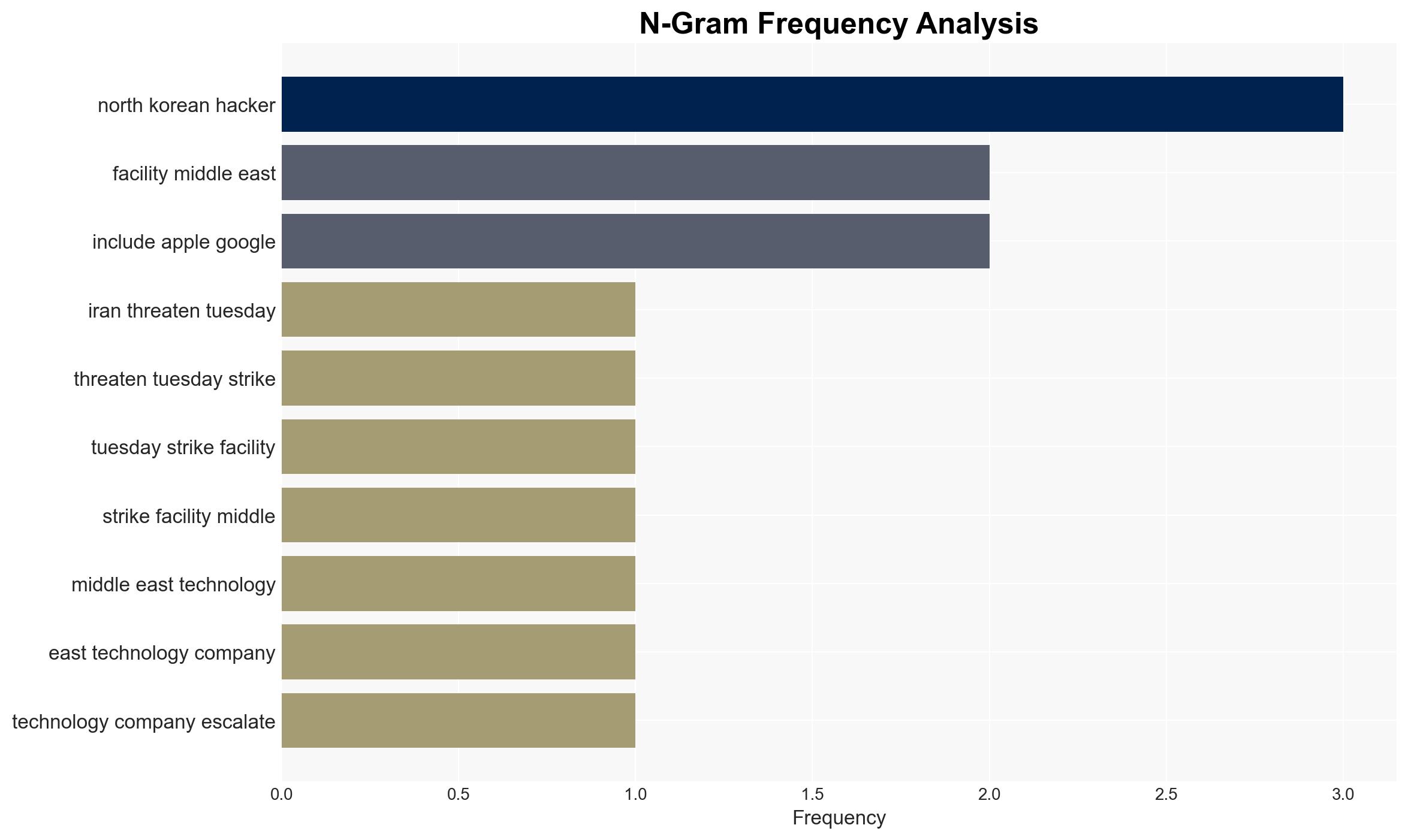
- Hypothesis A: The IRGC’s threats are primarily aimed at cyber disruption and data exposure, intending to damage reputations and operations of US tech companies without causing physical harm. This is supported by the language of the IRGC’s statement and past patterns of Iranian cyber operations.
- Hypothesis B: The threats are a precursor to more severe physical attacks on facilities, aiming to directly harm US interests and personnel in the region. This is less supported due to the lack of direct evidence indicating preparations for physical attacks.
- Assessment: Hypothesis A is currently better supported, given the IRGC’s historical preference for cyber operations and the specific language used in their threats. Indicators such as increased cyber activity or changes in military posture could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The IRGC has the capability to execute significant cyber operations; US tech companies are primary targets due to their symbolic and economic value; Iran seeks to avoid direct military confrontation with the US.
- Information Gaps: Specific details on the IRGC’s operational plans and capabilities; the extent of coordination with other state or non-state actors.
- Bias & Deception Risks: Potential over-reliance on open-source reporting; possibility of Iranian misinformation to exaggerate capabilities or intentions.
4. Implications and Strategic Risks
This development could lead to increased cyber incidents targeting US interests, potentially straining diplomatic relations and impacting regional stability.
- Political / Geopolitical: Escalation could lead to increased tensions between the US and Iran, affecting diplomatic negotiations and regional alliances.
- Security / Counter-Terrorism: Heightened threat environment for US assets in the Middle East, necessitating increased security measures.
- Cyber / Information Space: Potential for significant cyber disruptions affecting operations and data integrity of targeted companies.
- Economic / Social: Disruption of tech operations could impact regional economies and lead to broader economic instability.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance cybersecurity measures for US tech companies; increase intelligence monitoring of IRGC activities; engage in diplomatic efforts to de-escalate tensions.
- Medium-Term Posture (1–12 months): Develop resilience strategies for critical infrastructure; strengthen partnerships with regional allies; invest in cyber defense capabilities.
- Scenario Outlook:
- Best: De-escalation through diplomatic channels, leading to reduced threats.
- Worst: Escalation to physical attacks, causing significant damage and loss of life.
- Most-Likely: Continued cyber threats with sporadic disruptions, maintaining high tension but avoiding direct conflict.
6. Key Individuals and Entities
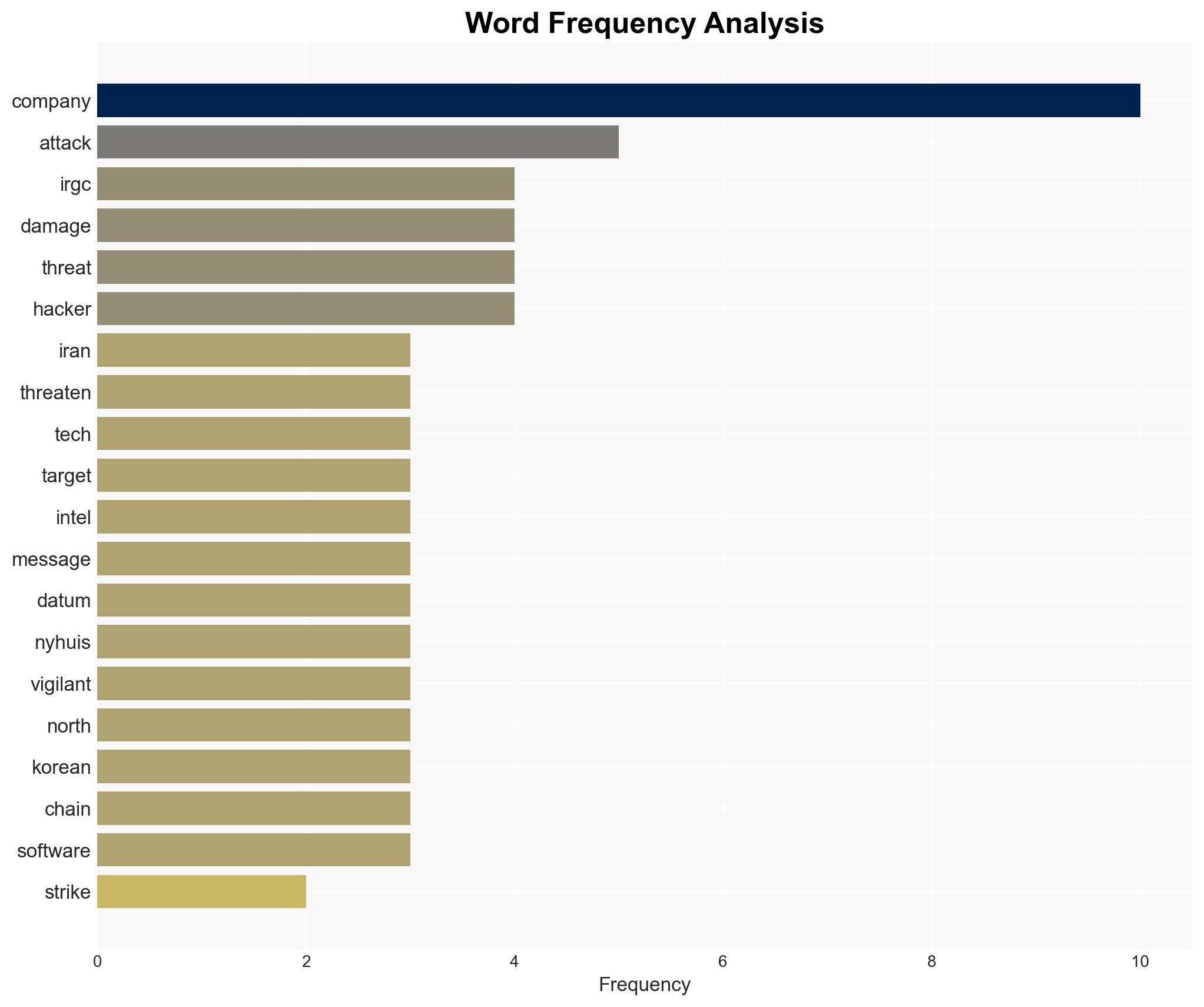
- Islamic Revolutionary Guards Corps (IRGC)
- US Technology Companies (Apple, Google, Intel, Tesla, etc.)
- Chris Nyhuis, CEO of Vigilant
- Unnamed White House Official
7. Thematic Tags
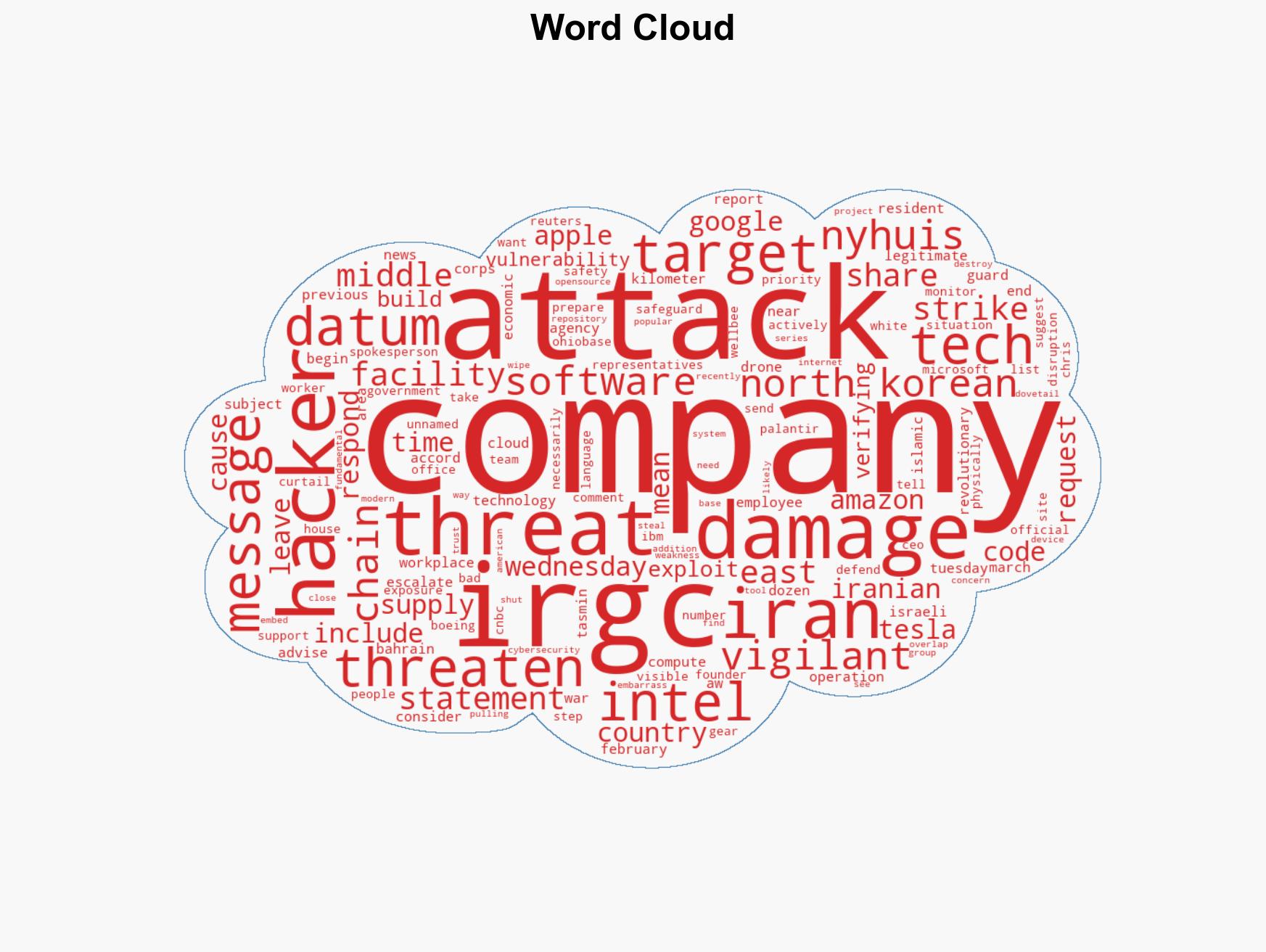
cybersecurity, US-Iran relations, regional stability, cyber threats, economic impact, geopolitical tensions, information warfare
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us