Iran Intensifies Cyber Operations Against US and Israel with Coordinated Multi-Layered Attacks
Published on: 2026-04-03
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Iran Expands Cyber Campaign Against US and Israel With Multi-Tiered Digital Attacks
1. BLUF (Bottom Line Up Front)
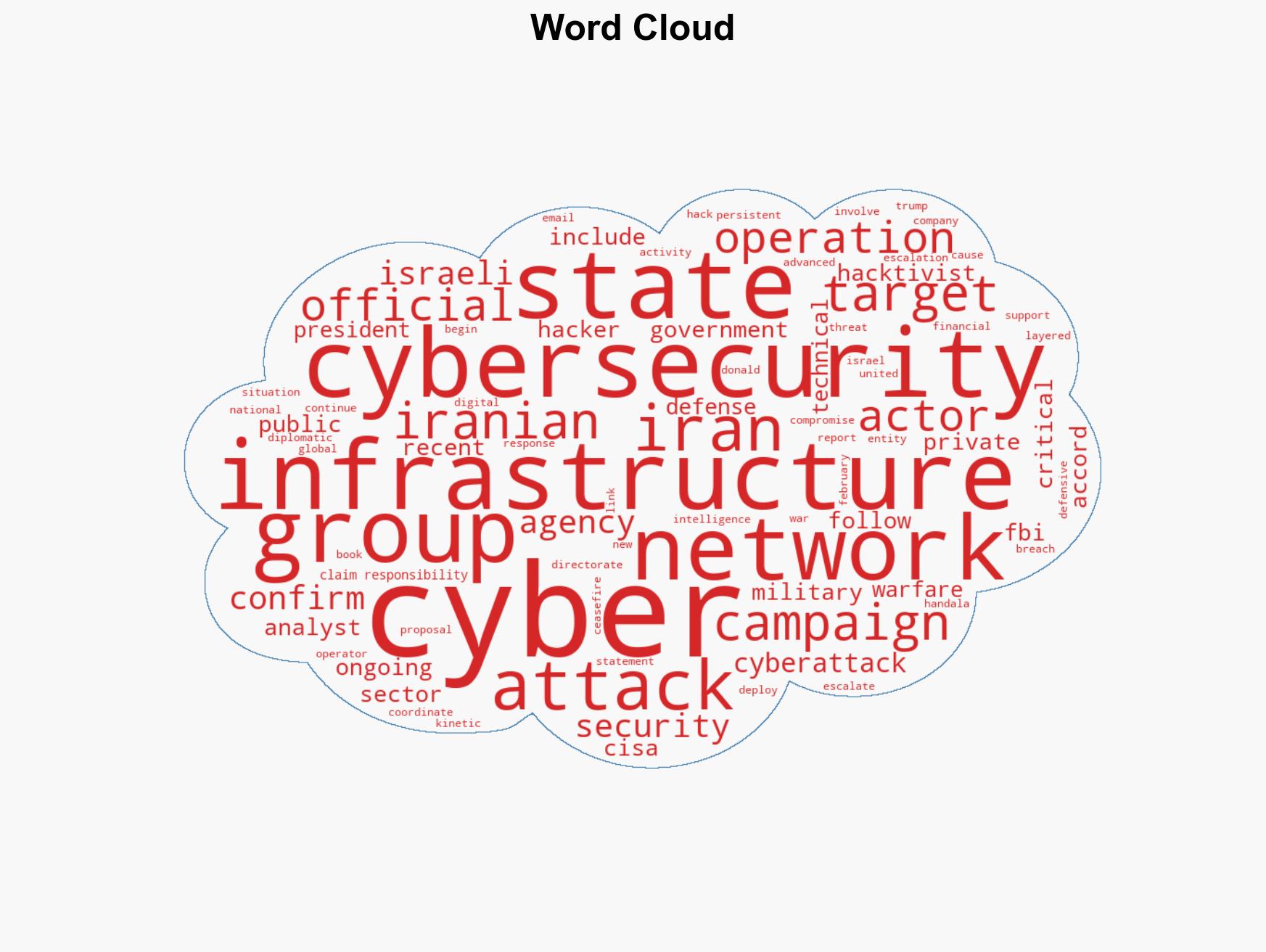
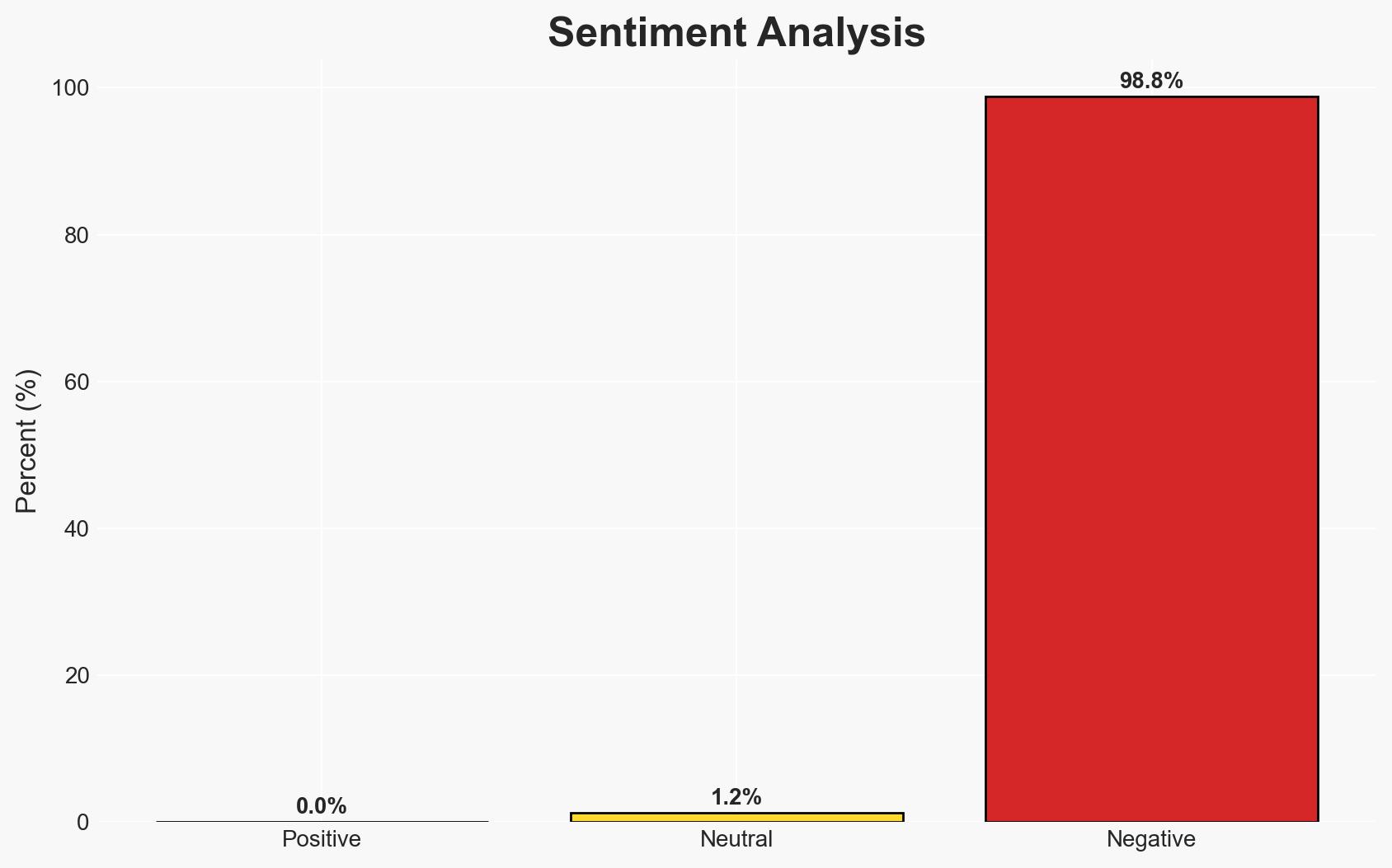
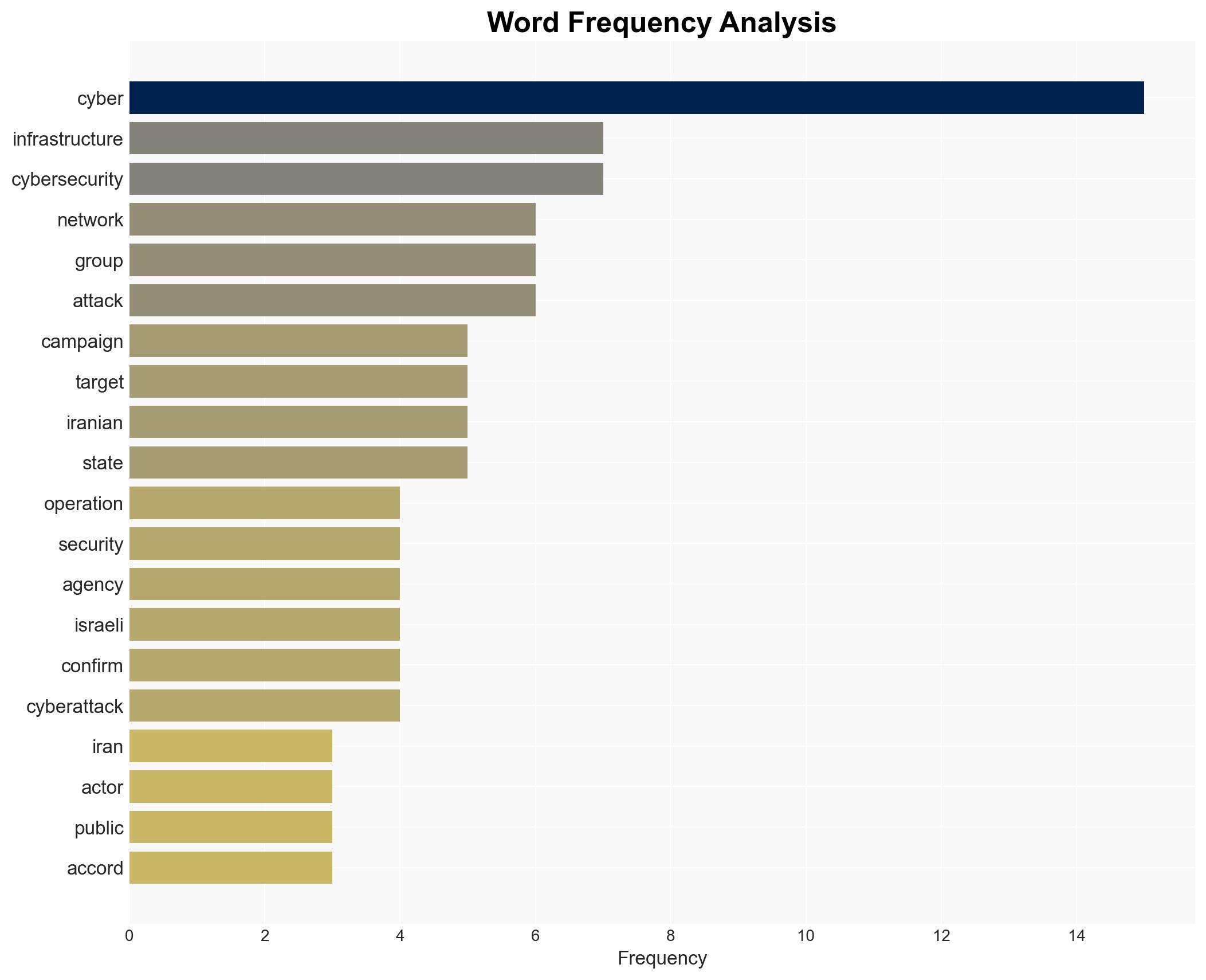
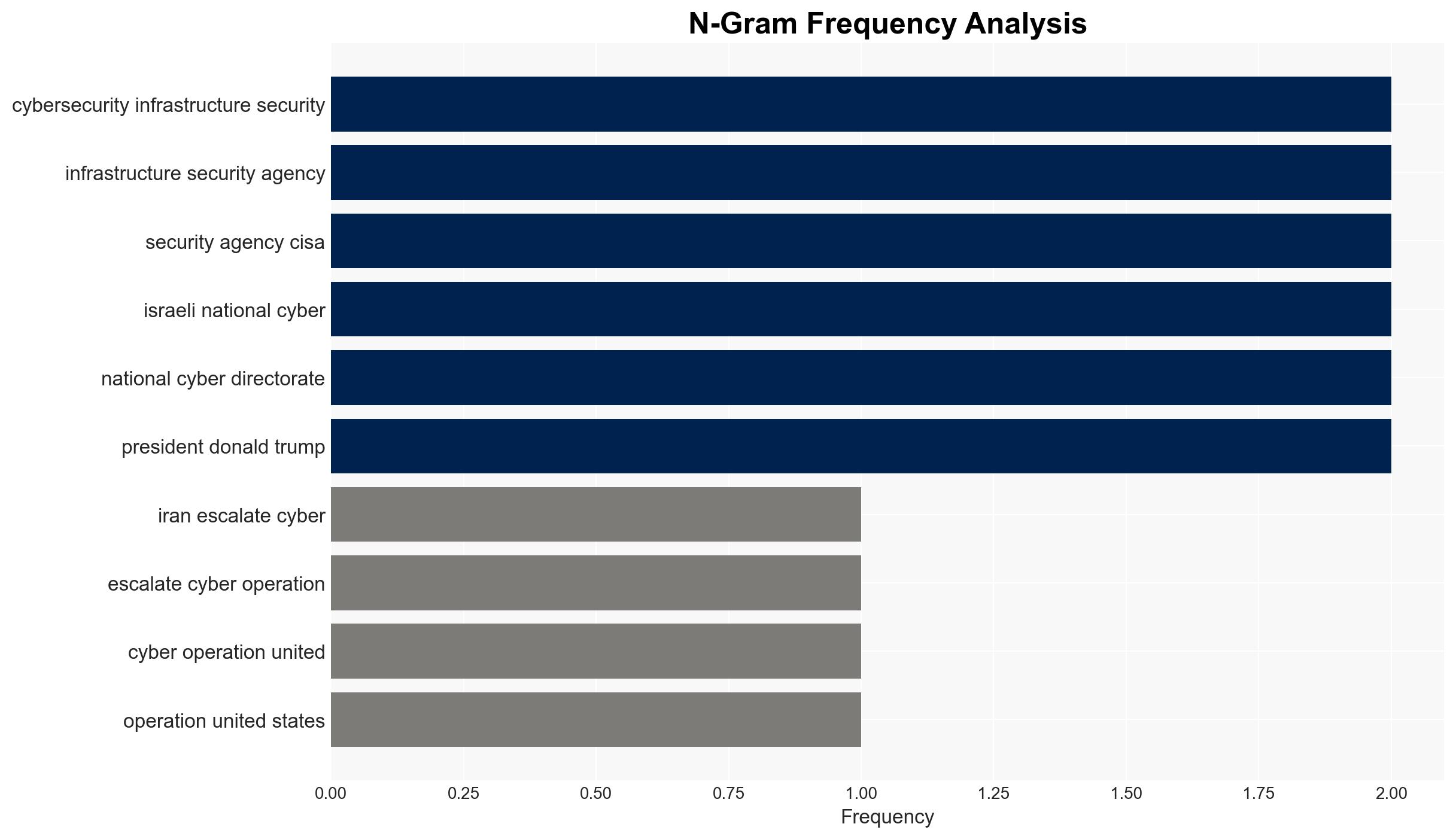
Iran is intensifying its cyber operations against the United States and Israel, employing a multi-tiered strategy involving elite military units, state-aligned proxies, and hacktivist groups. This campaign targets critical infrastructure and private sectors, signaling a convergence of cyber and kinetic operations amid heightened regional tensions. The most likely hypothesis is that Iran aims to leverage cyber capabilities to influence geopolitical dynamics and retaliate against perceived aggressions. Overall confidence in this assessment is moderate due to existing information gaps and potential bias in source reporting.
2. Competing Hypotheses
- Hypothesis A: Iran’s cyber campaign is primarily a strategic response to military hostilities and diplomatic tensions with the US and Israel, aiming to disrupt and deter adversaries. Evidence includes the timing of escalated cyber activities with military events and statements from Iranian-linked groups. However, uncertainties remain regarding the full extent of state control over hacktivist actions.
- Hypothesis B: The cyber operations are opportunistic actions by semi-autonomous groups seeking to exploit regional instability for political or ideological gains, with limited direct coordination by Iranian state actors. This is supported by the diverse nature of the groups involved. Contradicting evidence includes the sophisticated nature of some attacks, which suggests state-level resources and planning.
- Assessment: Hypothesis A is currently better supported due to the coordinated nature of the attacks and the involvement of elite units linked to Iran’s military. Key indicators that could shift this judgment include evidence of independent operations by hacktivist groups or a lack of strategic alignment with Iran’s broader geopolitical objectives.
3. Key Assumptions and Red Flags
- Assumptions: Iran maintains centralized control over its cyber operations; regional tensions will persist, driving continued cyber activities; hacktivist groups have some level of state support or alignment.
- Information Gaps: Detailed attribution of specific cyber incidents to Iranian state actors; insights into internal decision-making processes within Iran’s cyber apparatus.
- Bias & Deception Risks: Potential bias in reporting from sources with vested interests; possibility of Iranian deception operations to mislead attribution or intentions.
4. Implications and Strategic Risks
This development could lead to increased cyber conflict, impacting regional stability and international relations. The convergence of cyber and kinetic operations may set a precedent for future conflicts.
- Political / Geopolitical: Escalation of tensions between Iran and Western allies; potential for diplomatic fallout or retaliatory measures.
- Security / Counter-Terrorism: Heightened threat environment for critical infrastructure in targeted countries; increased demand for cybersecurity measures.
- Cyber / Information Space: Potential for widespread misinformation campaigns and increased cyber espionage activities.
- Economic / Social: Disruptions to key sectors such as energy and finance, leading to economic instability and public unrest.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of critical infrastructure networks; increase information sharing among allied cybersecurity agencies; issue public advisories on potential cyber threats.
- Medium-Term Posture (1–12 months): Strengthen international partnerships for cyber defense; invest in resilience measures for critical sectors; develop capabilities to attribute and counter state-sponsored cyber threats.
- Scenario Outlook:
- Best Case: Diplomatic resolutions reduce cyber hostilities; cyber operations de-escalate.
- Worst Case: Cyber operations escalate into broader conflict; significant infrastructure disruptions occur.
- Most-Likely: Continued cyber operations with periodic escalations; ongoing geopolitical tensions.
6. Key Individuals and Entities
- Iran’s Islamic Revolutionary Guard Corps (IRGC)
- U.S. Cybersecurity and Infrastructure Security Agency (CISA)
- Israeli National Cyber Directorate
- Handala hacker group
- Five Eyes intelligence alliance
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, cyber-espionage, critical infrastructure, geopolitical tensions, state-sponsored attacks, hacktivism, regional security, cyber defense
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us