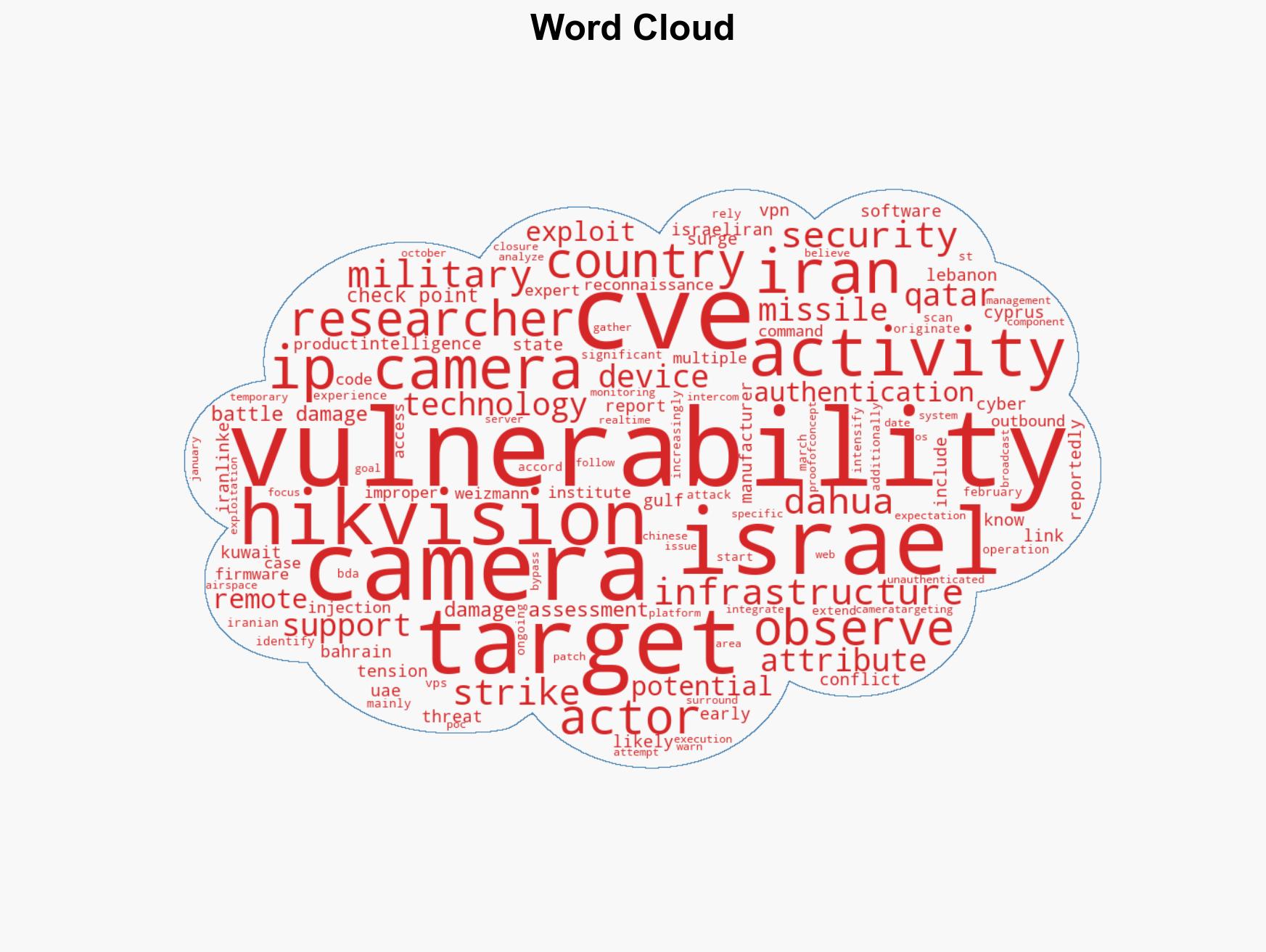
Iranian-affiliated hackers exploit IP camera vulnerabilities in Israel and Gulf nations for military intel pu…
Published on: 2026-03-07
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Iran-linked hackers target IP cameras across Israel and Gulf states for military intelligence
1. BLUF (Bottom Line Up Front)
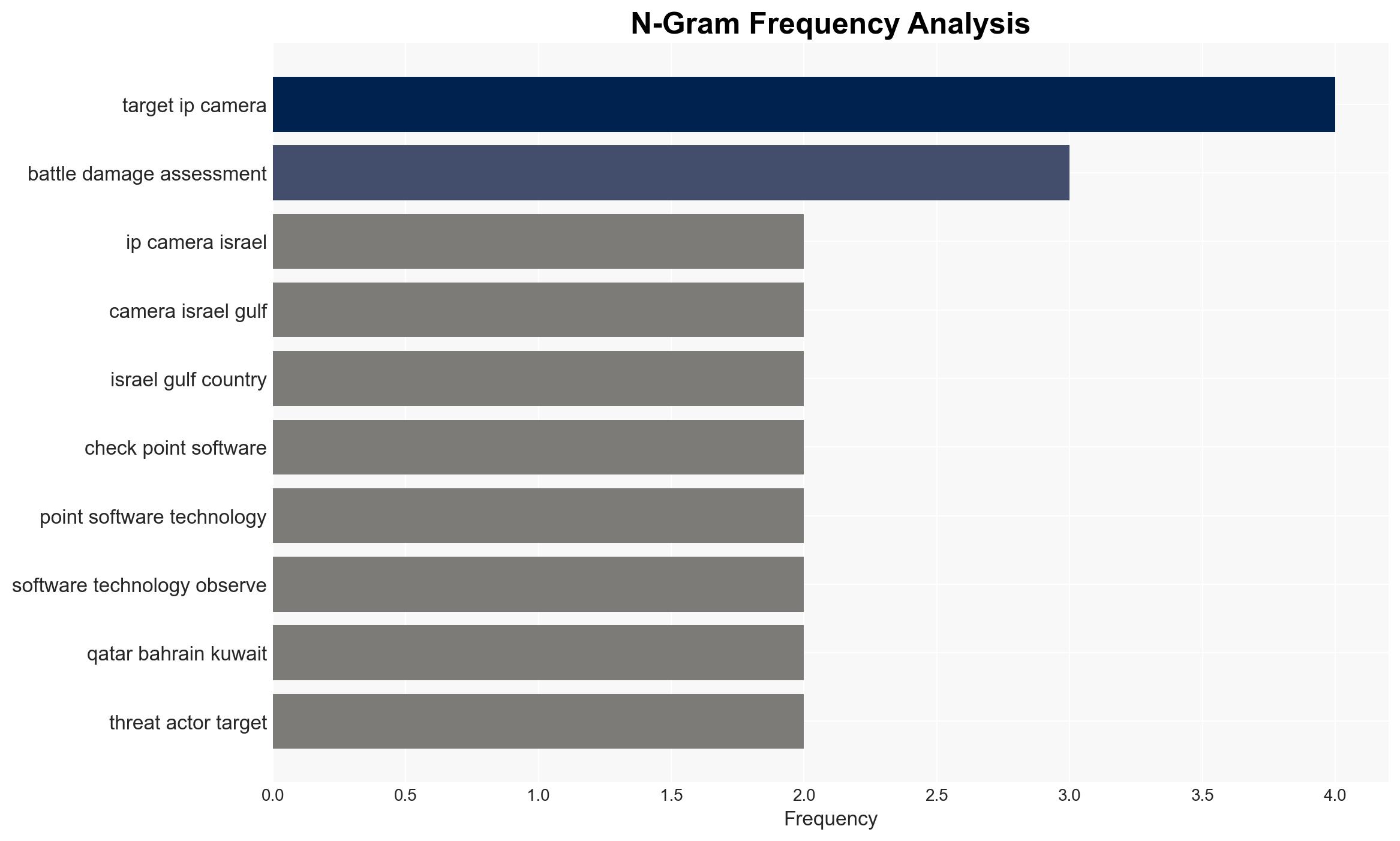
Iran-linked cyber actors are targeting IP cameras in Israel and Gulf states to support military intelligence and battle damage assessment, with moderate confidence. This activity is likely aimed at reconnaissance and real-time monitoring, affecting regional security dynamics and potentially escalating geopolitical tensions.
2. Competing Hypotheses
- Hypothesis A: Iran-linked hackers are conducting cyber operations to gather military intelligence and support battle damage assessment in anticipation of or response to military actions. This is supported by the targeting of IP cameras in strategic locations and the use of known vulnerabilities. Key uncertainties include the full extent of the operational objectives and the potential for misattribution.
- Hypothesis B: The cyber activities are part of a broader campaign of cyber espionage aimed at destabilizing regional adversaries and gathering intelligence for non-military purposes. This is supported by the pattern of targeting critical infrastructure and the timing of operations coinciding with geopolitical tensions. However, the focus on military-related targets suggests a more direct military intelligence objective.
- Assessment: Hypothesis A is currently better supported due to the specific targeting of IP cameras for battle damage assessment and military intelligence purposes. Indicators that could shift this judgment include evidence of broader espionage activities or changes in the geopolitical context that reduce military tensions.
3. Key Assumptions and Red Flags
- Assumptions: The cyber actors are state-sponsored or state-affiliated; the primary objective is military intelligence; the vulnerabilities exploited are not newly discovered but previously known.
- Information Gaps: Detailed attribution of the cyber actors; specific military objectives or targets; the extent of data exfiltration or real-time monitoring capabilities achieved.
- Bias & Deception Risks: Potential confirmation bias in attributing activities to Iran; reliance on cybersecurity firm reports which may have commercial interests; possibility of false flag operations by other actors.
4. Implications and Strategic Risks
This development could exacerbate regional tensions and lead to increased cyber and military confrontations. The targeting of IP cameras suggests a focus on real-time intelligence, potentially escalating military readiness and response measures.
- Political / Geopolitical: Increased tensions between Iran and affected states, potential for diplomatic conflicts or sanctions.
- Security / Counter-Terrorism: Heightened alert levels and security measures in targeted countries, potential for retaliatory cyber or military actions.
- Cyber / Information Space: Increased cyber defense postures, potential for information warfare or disinformation campaigns.
- Economic / Social: Potential impacts on regional economic stability and public confidence in cybersecurity measures.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of IP camera networks, prioritize patching known vulnerabilities, and increase intelligence sharing among affected nations.
- Medium-Term Posture (1–12 months): Develop regional cyber defense collaborations, invest in cybersecurity infrastructure, and conduct joint military-cyber exercises.
- Scenario Outlook:
- Best: De-escalation of tensions through diplomatic channels, leading to reduced cyber activities.
- Worst: Escalation into open military conflict, with cyber operations supporting kinetic actions.
- Most-Likely: Continued cyber skirmishes and intelligence gathering, with periodic escalations tied to geopolitical events.
6. Key Individuals and Entities
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
cybersecurity, cyber-espionage, military intelligence, Iran, Middle East security, IP cameras, cybersecurity vulnerabilities, geopolitical tensions
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us