Iranian Cyber Attack Targets Kash Patel’s Email, Leaves FBI Systems Unbreached
Published on: 2026-03-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Iranian Hackers Breached Kash Patels Emailbut Not the FBIs
1. BLUF (Bottom Line Up Front)
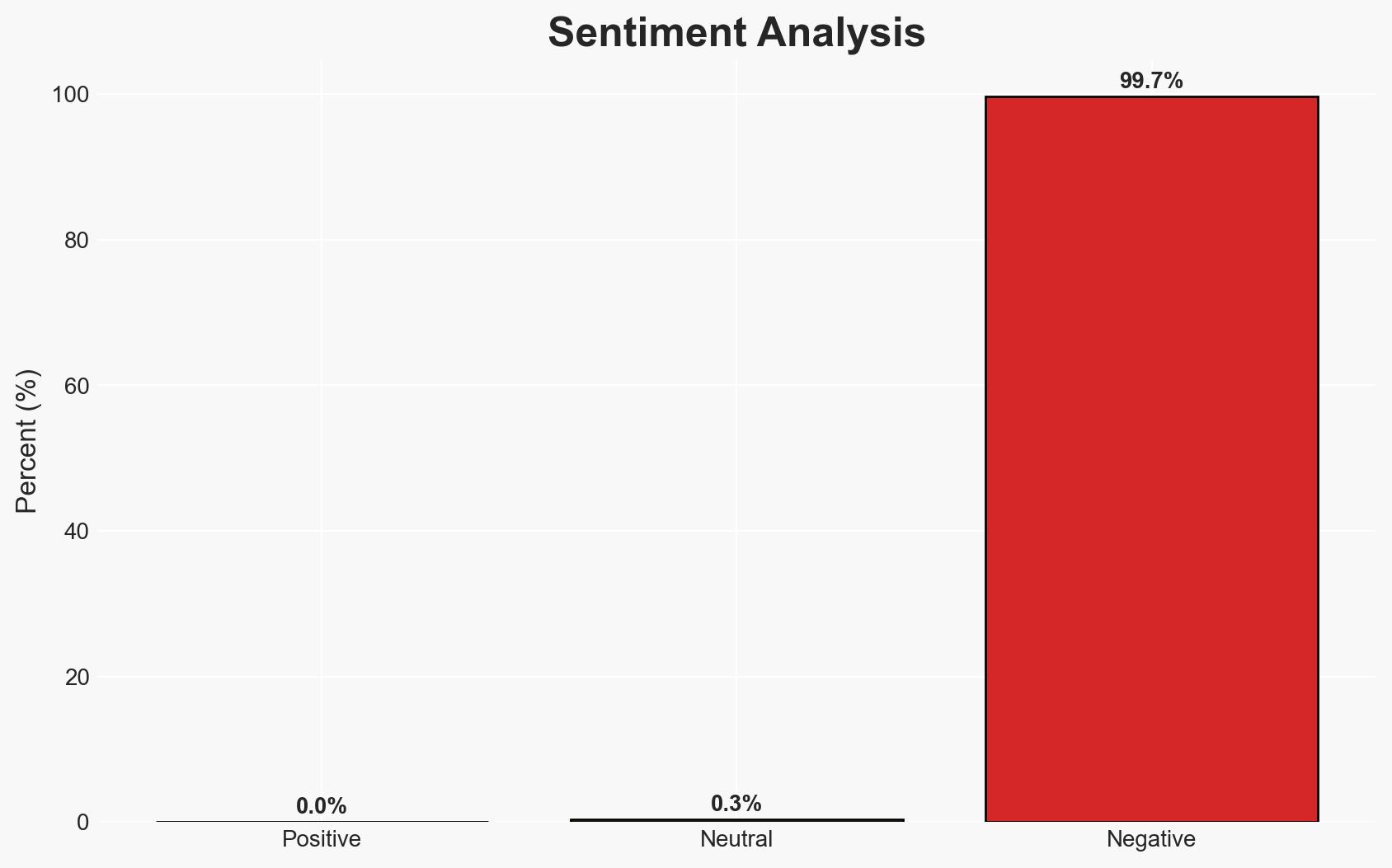
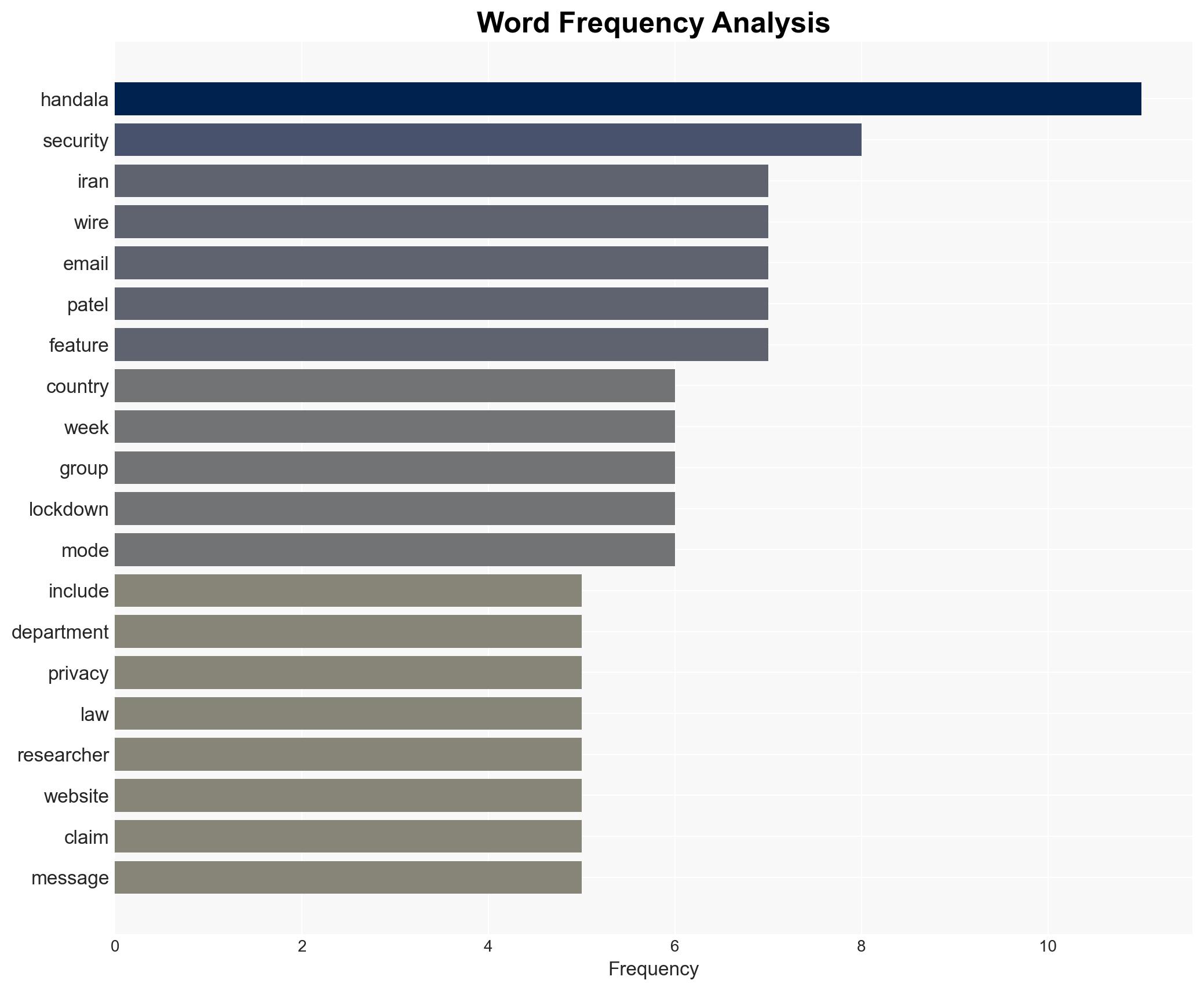
Iranian hackers, identified as the group Handala, have reportedly breached the email of Kash Patel but not the FBI’s. This incident highlights ongoing cyber threats amidst heightened tensions due to the US-Israel conflict with Iran. The primary hypothesis suggests a targeted cyber retaliation strategy by Iran. Overall confidence in this assessment is moderate due to limited specific details on the breach.
2. Competing Hypotheses
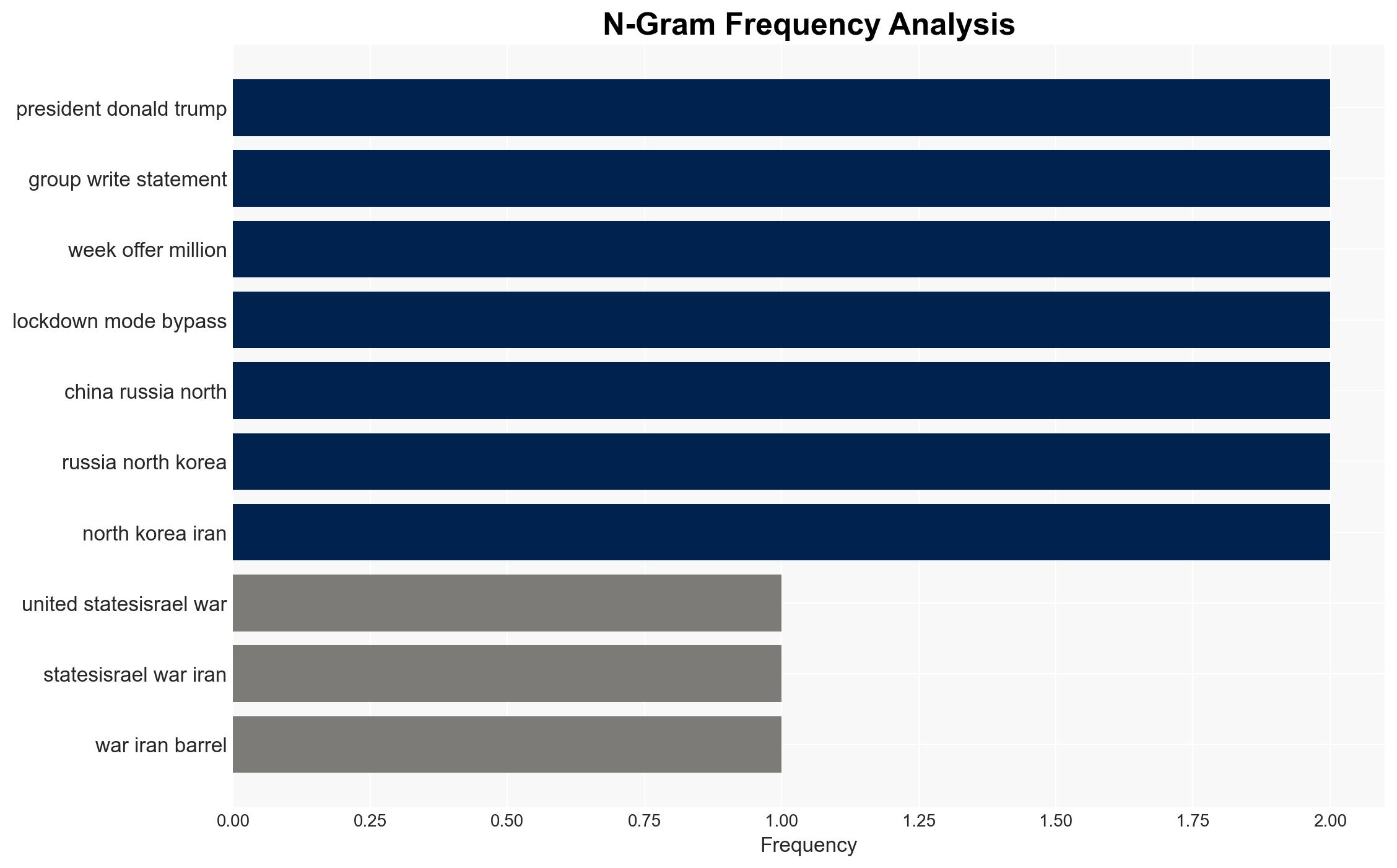
- Hypothesis A: The breach of Kash Patel’s email is part of a broader Iranian cyber retaliation campaign against US interests. Supporting evidence includes the timing of the breach amidst the US-Israel conflict with Iran. Key uncertainties include the specific objectives and scope of the campaign.
- Hypothesis B: The breach is an isolated incident, possibly conducted by independent actors using the conflict as a cover. Contradicting evidence is the lack of similar breaches reported against other high-profile targets. This hypothesis is less supported due to the known activities of the Handala group.
- Assessment: Hypothesis A is currently better supported due to the alignment of the breach with known Iranian cyber capabilities and historical patterns of retaliation. Indicators that could shift this judgment include evidence of coordination with other state or non-state actors.
3. Key Assumptions and Red Flags
- Assumptions: The Handala group operates with some level of state support or endorsement; Kash Patel was targeted due to his perceived influence or role; Iranian cyber capabilities are sufficiently advanced to breach high-profile targets.
- Information Gaps: Detailed technical analysis of the breach, confirmation of the data accessed, and the specific motivations behind targeting Kash Patel.
- Bias & Deception Risks: Potential overestimation of Iranian capabilities based on past incidents; reliance on open-source information that may be incomplete or skewed by media narratives.
4. Implications and Strategic Risks
This development could exacerbate existing tensions between the US and Iran, potentially leading to further cyber exchanges or escalations. The breach may also embolden other state or non-state actors to engage in similar activities.
- Political / Geopolitical: Increased diplomatic strain and potential for retaliatory measures by the US.
- Security / Counter-Terrorism: Heightened alert for cyber threats against US infrastructure and personnel.
- Cyber / Information Space: Potential for increased cyber espionage and misinformation campaigns targeting US interests.
- Economic / Social: Limited direct economic impact, but potential for increased public concern over cybersecurity and privacy.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of Iranian cyber activities, increase cybersecurity measures for high-profile targets, and engage in diplomatic channels to de-escalate tensions.
- Medium-Term Posture (1–12 months): Develop resilience strategies, strengthen international cyber cooperation, and invest in advanced threat detection technologies.
- Scenario Outlook:
- Best Case: De-escalation of cyber activities through diplomatic engagement; minimal further breaches.
- Worst Case: Escalation into broader cyber conflict affecting critical infrastructure.
- Most Likely: Continued sporadic cyber incidents with limited direct impact but ongoing strategic tension.
6. Key Individuals and Entities
- Kash Patel
- Handala (Iranian hacker group)
- Not clearly identifiable from open sources in this snippet for others involved.
7. Thematic Tags
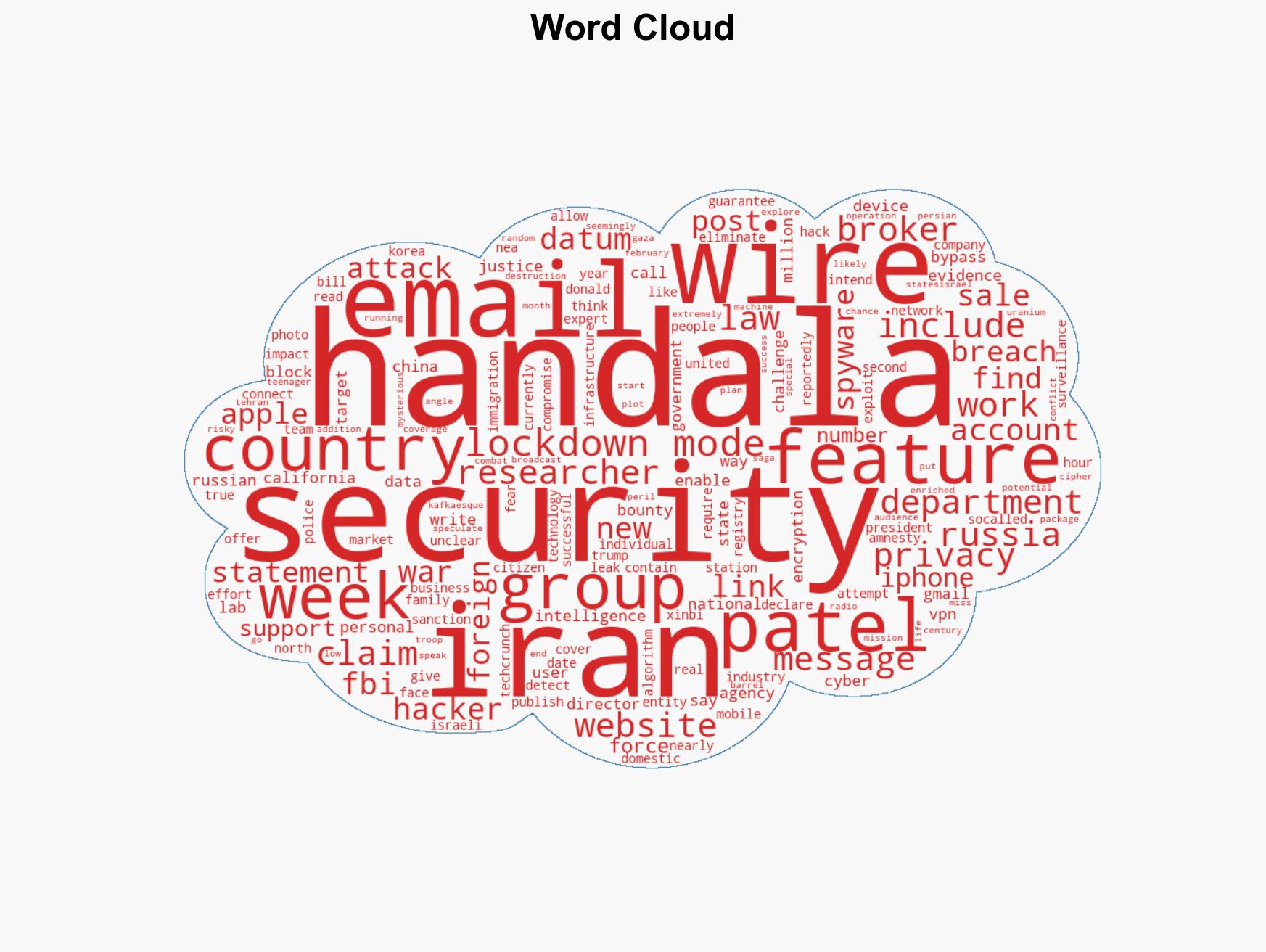
cybersecurity, cyber-espionage, Iran-US relations, cyber warfare, national security, information security, geopolitical tensions
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us