Iranian Cyber Forces Mobilize for Intensified Digital Warfare Against Israel
Published on: 2026-03-31
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Its all hands on deck Irans hackers go to war
1. BLUF (Bottom Line Up Front)
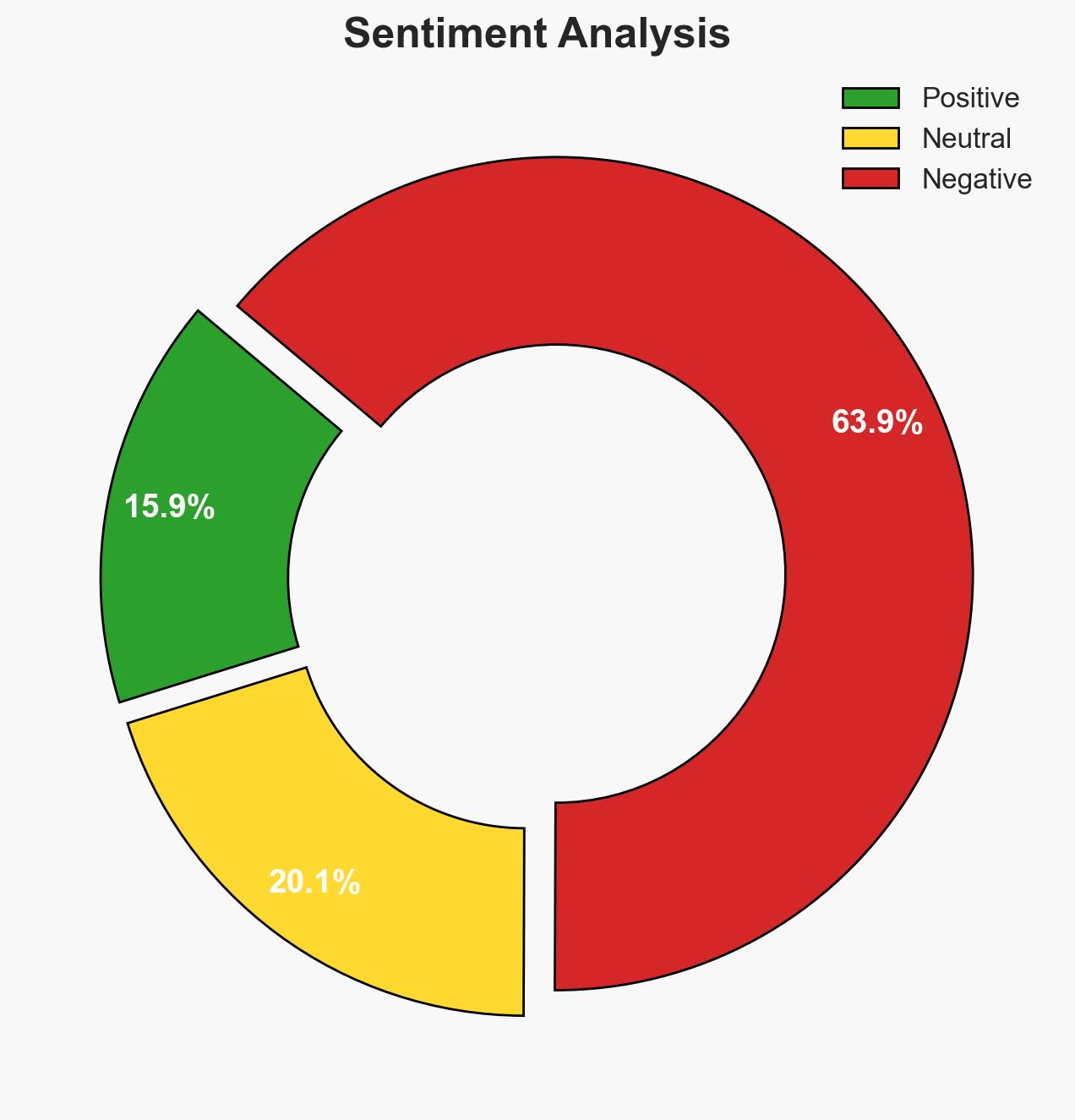
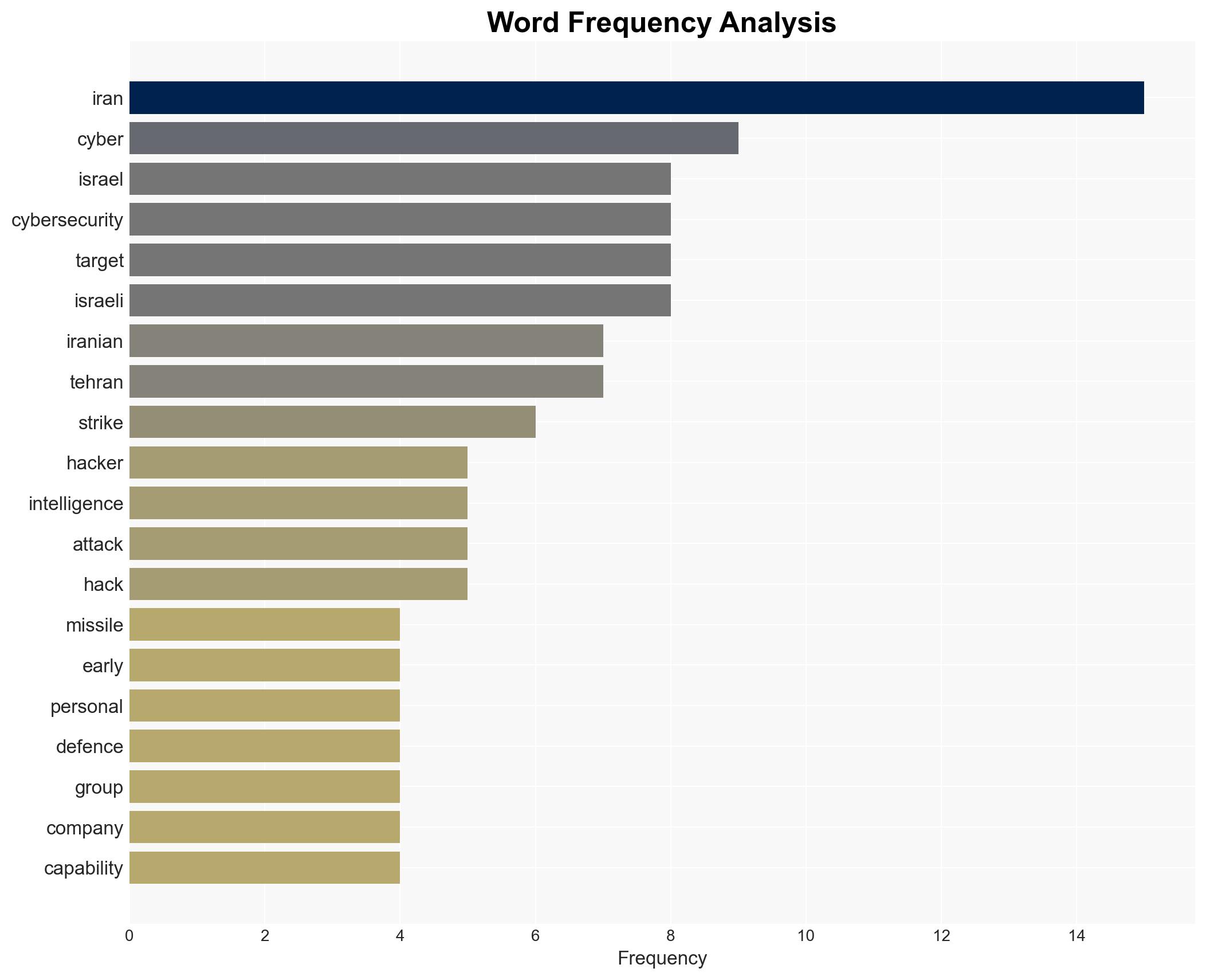
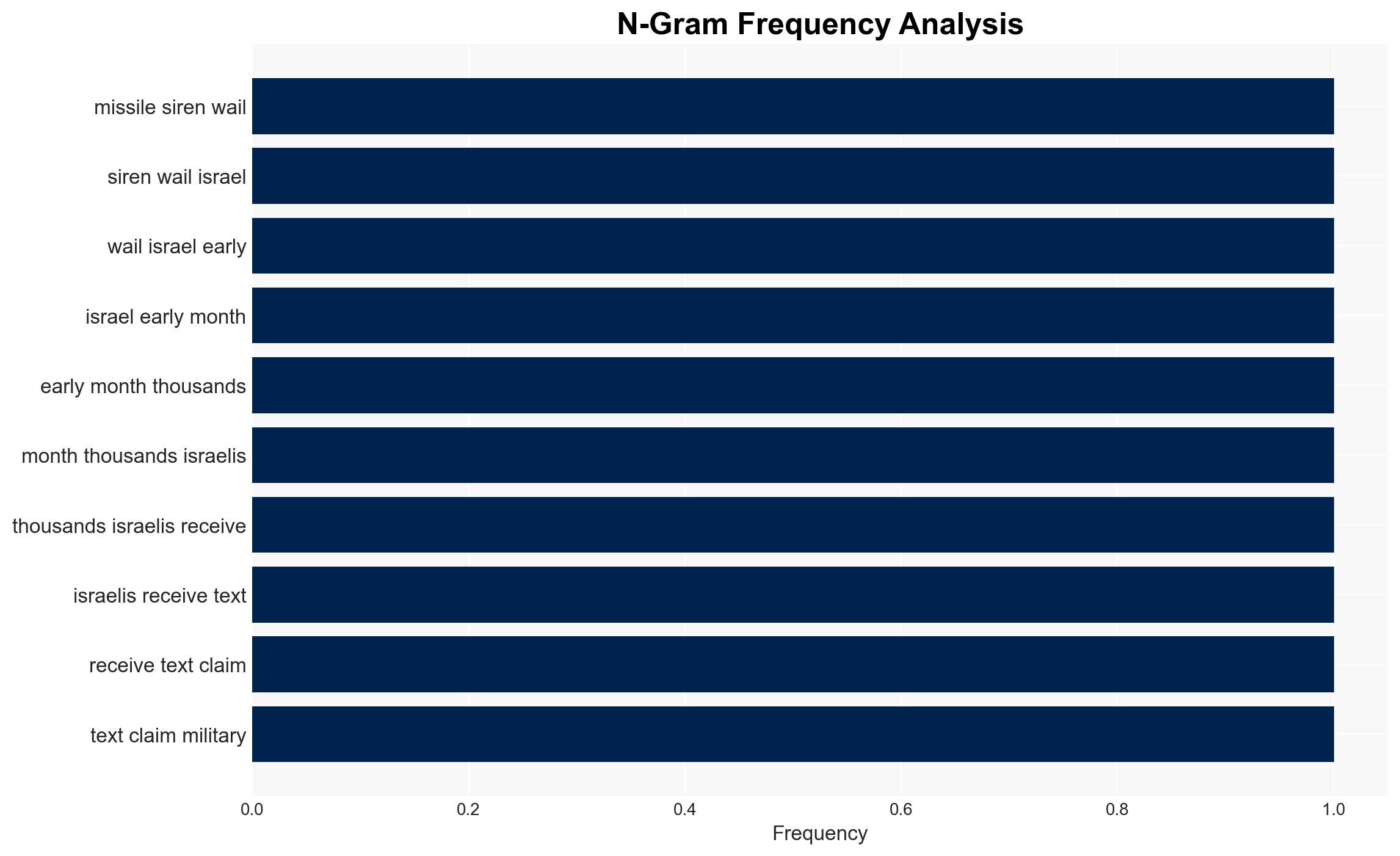
Iranian cyber operations are intensifying against Israel and the US, leveraging a multi-tiered approach involving state-run units, proxies, and hacktivists. These efforts aim to disrupt, gather intelligence, and influence public perception. The most likely hypothesis is that Iran seeks to destabilize its adversaries through cyber means, with moderate confidence in this assessment due to the complexity and opacity of cyber warfare.
2. Competing Hypotheses
- Hypothesis A: Iran is conducting a coordinated cyber campaign to destabilize Israel and the US, evidenced by recent cyber attacks and disinformation campaigns. However, the extent of state control over all actors involved remains uncertain.
- Hypothesis B: The observed cyber activities are primarily conducted by independent groups with limited direct coordination by the Iranian state, using the geopolitical tension as an opportunity to act. This is less supported due to the sophisticated nature of the attacks and historical patterns of state involvement.
- Assessment: Hypothesis A is currently better supported due to the complexity and scale of the operations, which suggest state-level coordination. Indicators such as increased sophistication or direct attribution could further solidify this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Iran has the capability and intent to conduct sophisticated cyber operations; Iranian cyber activities are state-sanctioned; geopolitical tensions are a driving factor for increased cyber activity.
- Information Gaps: Specific attribution of attacks to Iranian state actors versus proxies; the full extent of data compromised in recent attacks; internal Iranian strategic objectives.
- Bias & Deception Risks: Potential for confirmation bias in attributing attacks to Iran; reliance on potentially biased sources; possibility of false flag operations by other actors.
4. Implications and Strategic Risks
The escalation of Iranian cyber activities could lead to heightened geopolitical tensions and potential retaliatory actions. The cyber domain’s opacity complicates response strategies and attribution, increasing the risk of miscalculation.
- Political / Geopolitical: Potential for increased diplomatic strain between Iran, Israel, and the US, with possible international condemnation or sanctions.
- Security / Counter-Terrorism: Elevated threat levels for critical infrastructure and defense sectors in targeted nations.
- Cyber / Information Space: Increased cyber defense posturing and potential for escalated cyber conflict; heightened misinformation campaigns.
- Economic / Social: Disruption to businesses and public services, leading to economic losses and public unrest in affected regions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of cyber threats, increase information sharing among allies, and conduct public awareness campaigns to mitigate misinformation.
- Medium-Term Posture (1–12 months): Strengthen cyber defense capabilities, develop international partnerships for cyber resilience, and invest in counter-disinformation strategies.
- Scenario Outlook:
- Best: De-escalation through diplomatic engagement and improved cyber defenses.
- Worst: Escalation to kinetic conflict due to cyber misattribution or severe infrastructure disruption.
- Most-Likely: Continued cyber skirmishes with periodic escalations, driven by geopolitical developments.
6. Key Individuals and Entities
- Islamic Revolutionary Guard Corps
- Iran’s Ministry of Intelligence
- Chris Krebs (former director of CISA)
- Handala (hacking front)
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
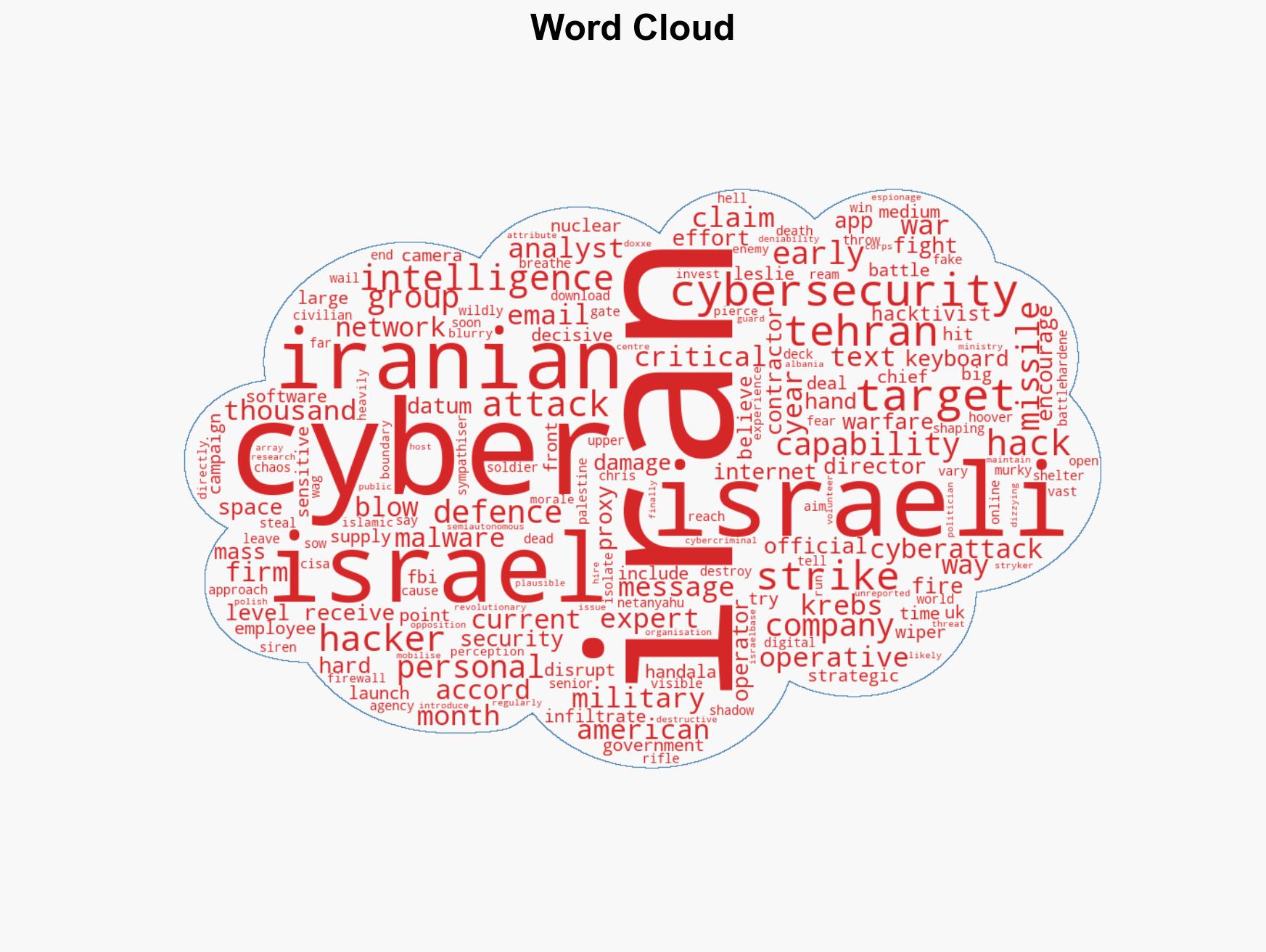
cybersecurity, cyber warfare, Iran, Israel, US, disinformation, state-sponsored hacking, geopolitical tensions
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us