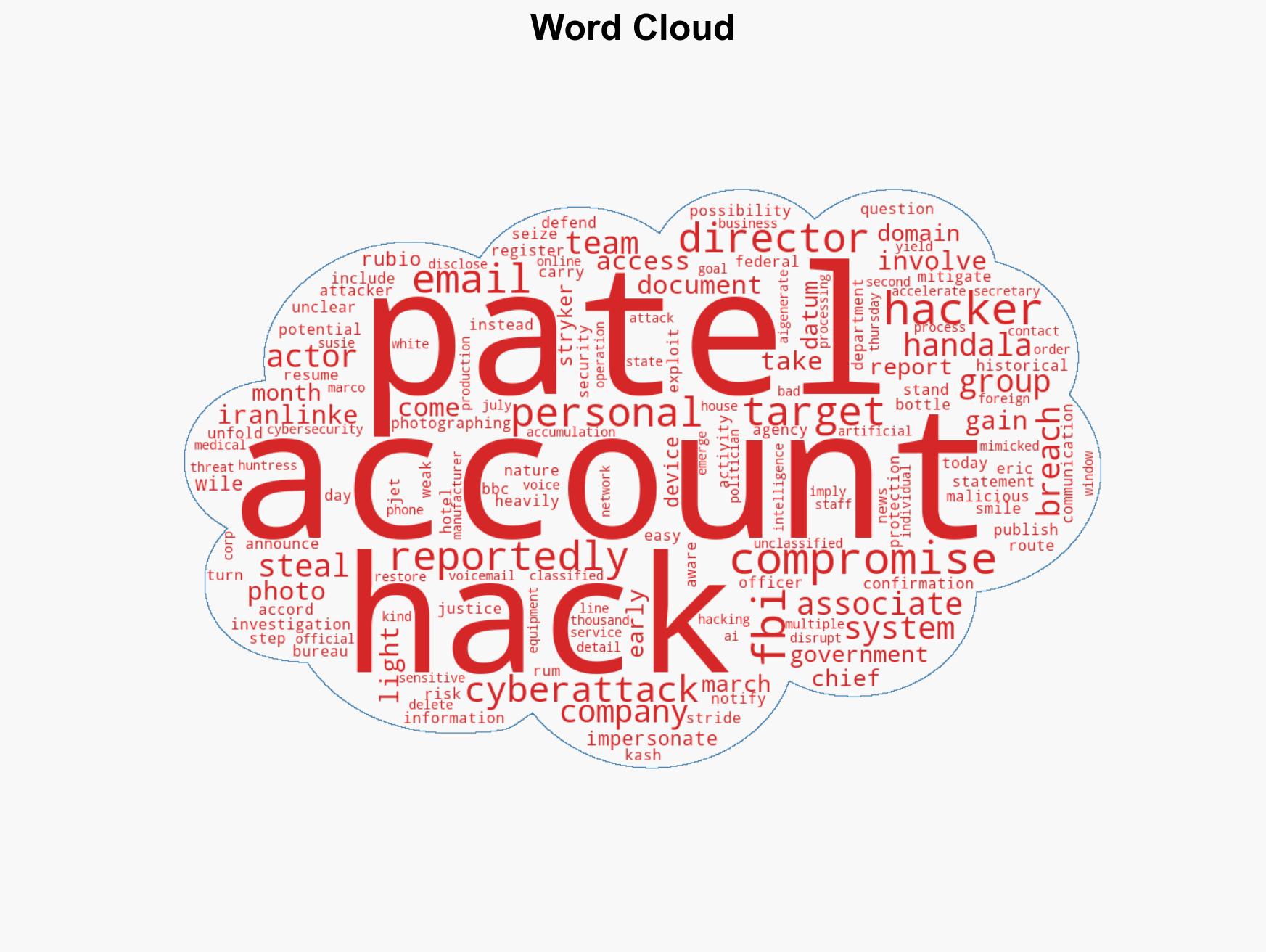
Iranian Hackers Compromise FBI Director Kash Patel’s Personal Email, Exposing Sensitive Information
Published on: 2026-03-28
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Iran-linked hackers breach personal email account of FBI director Kash Patel
1. BLUF (Bottom Line Up Front)
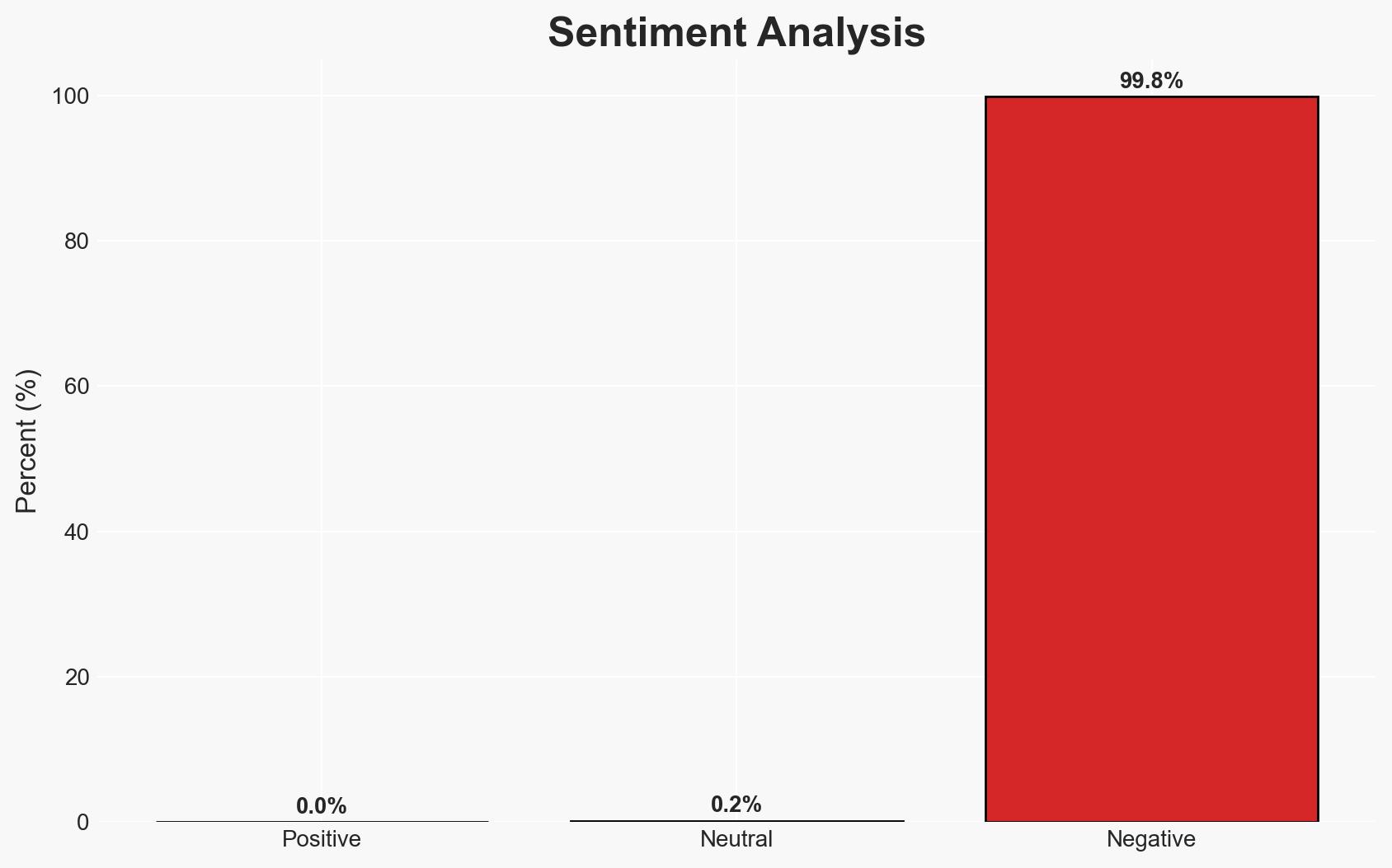
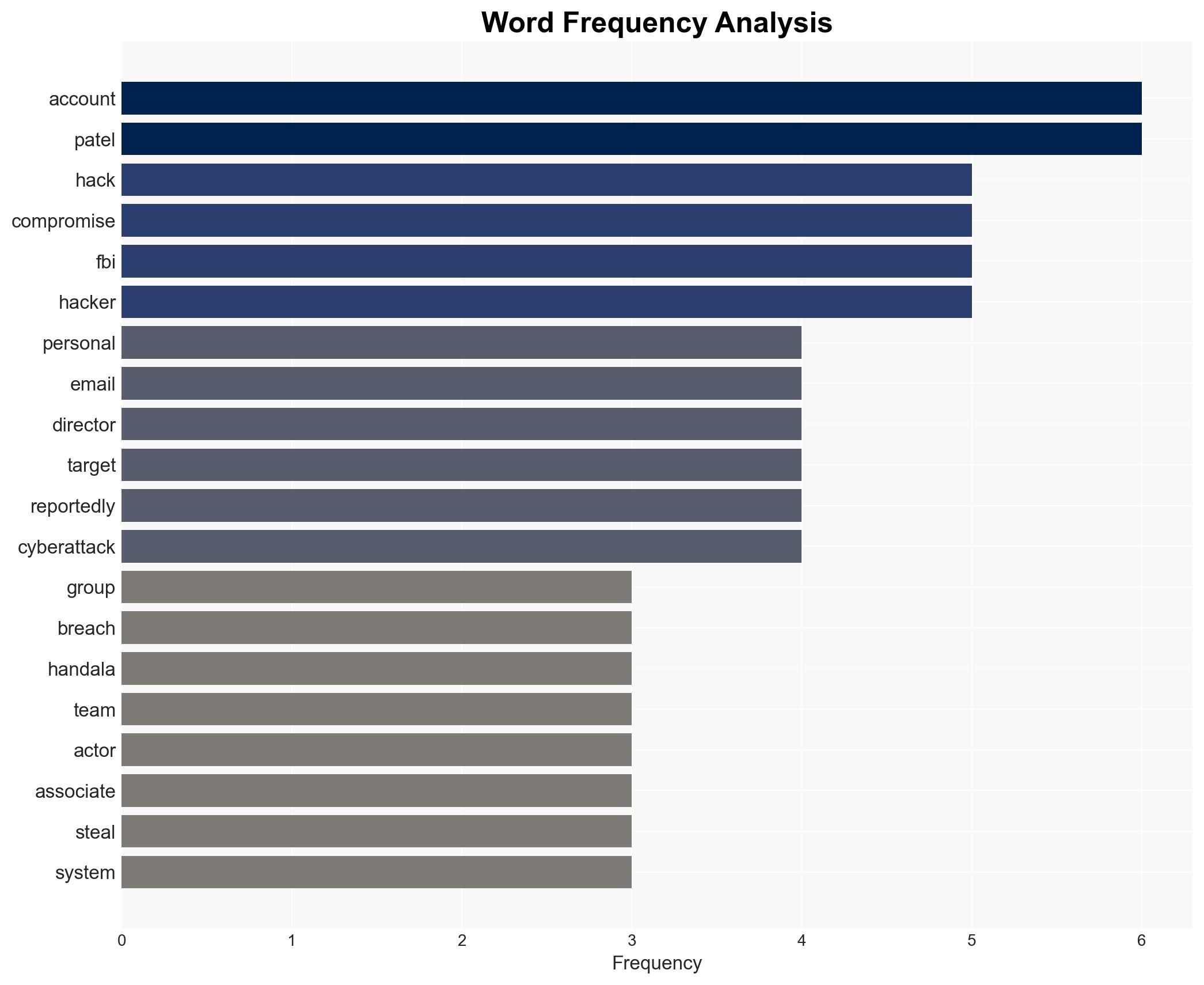
The personal email account of FBI Director Kash Patel was compromised by the Iran-linked Handala Hack Team, exposing non-governmental information. The breach highlights vulnerabilities in personal communication systems. The most likely hypothesis is that the attack leveraged previously stolen information. This incident underscores the need for enhanced security measures for personal accounts of high-profile individuals. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
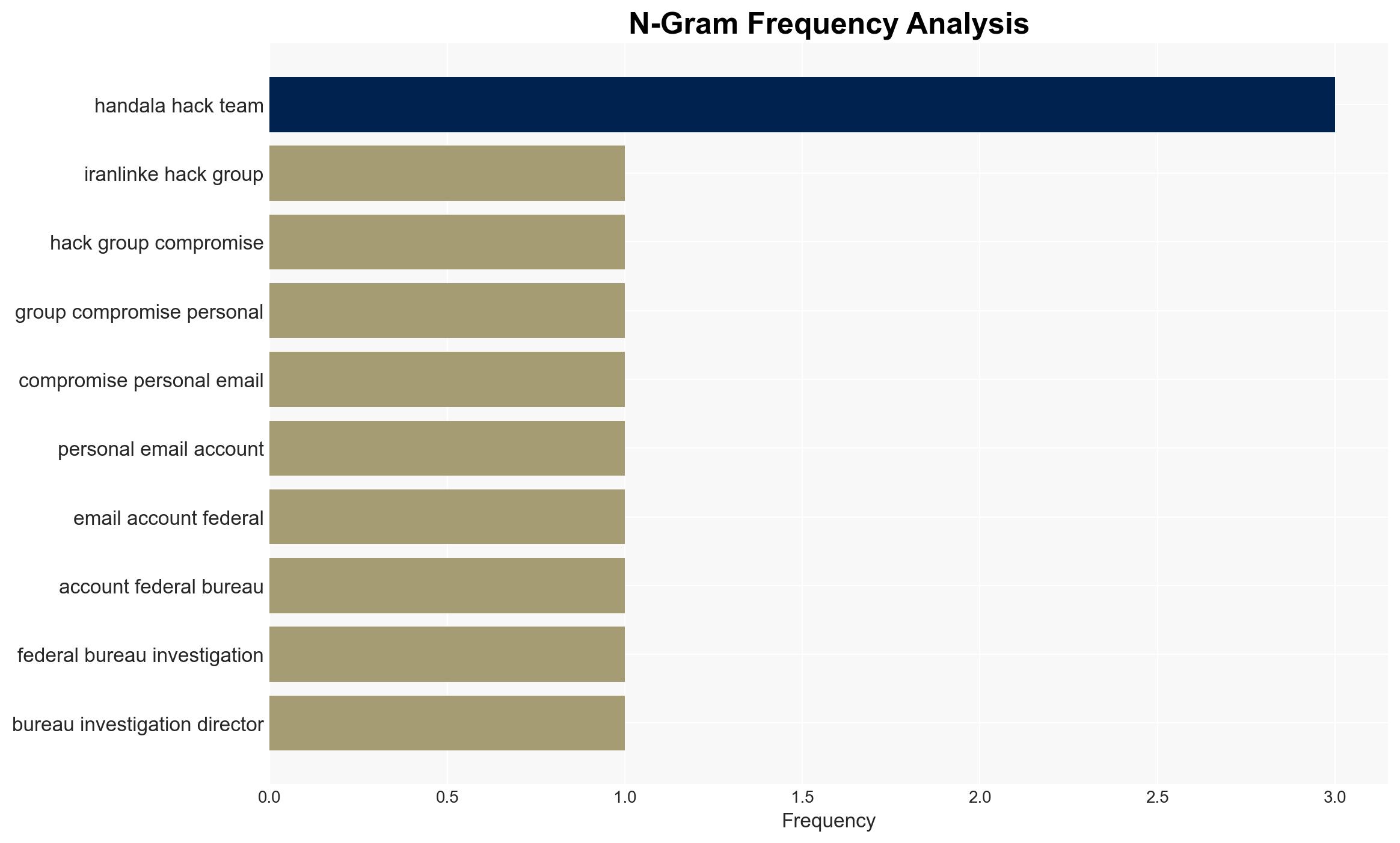
- Hypothesis A: The Handala Hack Team used previously stolen information to breach Patel’s email. Supporting evidence includes prior warnings of targeting and the use of a domain registered on the day of a related DOJ announcement. Uncertainties include the exact method of attack.
- Hypothesis B: The breach was a result of a new, undisclosed vulnerability in Patel’s personal email security. This is less supported due to the lack of evidence indicating a novel exploit.
- Assessment: Hypothesis A is currently better supported due to the timing of the domain registration and prior targeting warnings. Indicators such as new attack vectors or vulnerabilities could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The breach did not involve classified information; the hackers’ primary motivation was intelligence gathering; personal email systems are less secure than official ones.
- Information Gaps: Specific technical details of the breach method; full extent of the data accessed; potential connections to other cyber incidents.
- Bias & Deception Risks: Potential bias in attributing the attack solely to Handala Hack Team without considering other actors; risk of deception in hackers’ public claims.
4. Implications and Strategic Risks
This breach could lead to increased scrutiny of personal communication security for government officials and may embolden similar cyber operations by state-linked groups.
- Political / Geopolitical: Potential for increased tensions between the U.S. and Iran, especially if further links to state actors are established.
- Security / Counter-Terrorism: Heightened awareness and potential policy shifts regarding personal cybersecurity for officials.
- Cyber / Information Space: Increased focus on securing personal accounts and potential rise in AI-driven cyberattacks.
- Economic / Social: Limited immediate economic impact, but potential for increased cybersecurity spending and public concern over digital privacy.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance security protocols for personal accounts of high-profile individuals; conduct a thorough forensic analysis of the breach.
- Medium-Term Posture (1–12 months): Develop partnerships with cybersecurity firms to improve threat detection; implement regular security training for government officials.
- Scenario Outlook: Best: Strengthened cybersecurity measures prevent future breaches. Worst: Escalation of cyber operations leads to broader geopolitical tensions. Most-Likely: Incremental improvements in personal cybersecurity with ongoing low-level cyber threats.
6. Key Individuals and Entities
- Kash Patel – FBI Director
- Handala Hack Team – Iran-linked hacking group
- Eric Stride – Chief Security Officer, Huntress Inc.
- U.S. Justice Department
- Stryker Corp. – U.S. medical equipment manufacturer
7. Thematic Tags
cybersecurity, Iran, cyber-espionage, personal security, information warfare, geopolitical tensions, AI-driven attacks
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us