Iranian Hackers Expand Cyber Operations Targeting U.S. and Allies Amid Ongoing Conflict
Published on: 2026-03-17
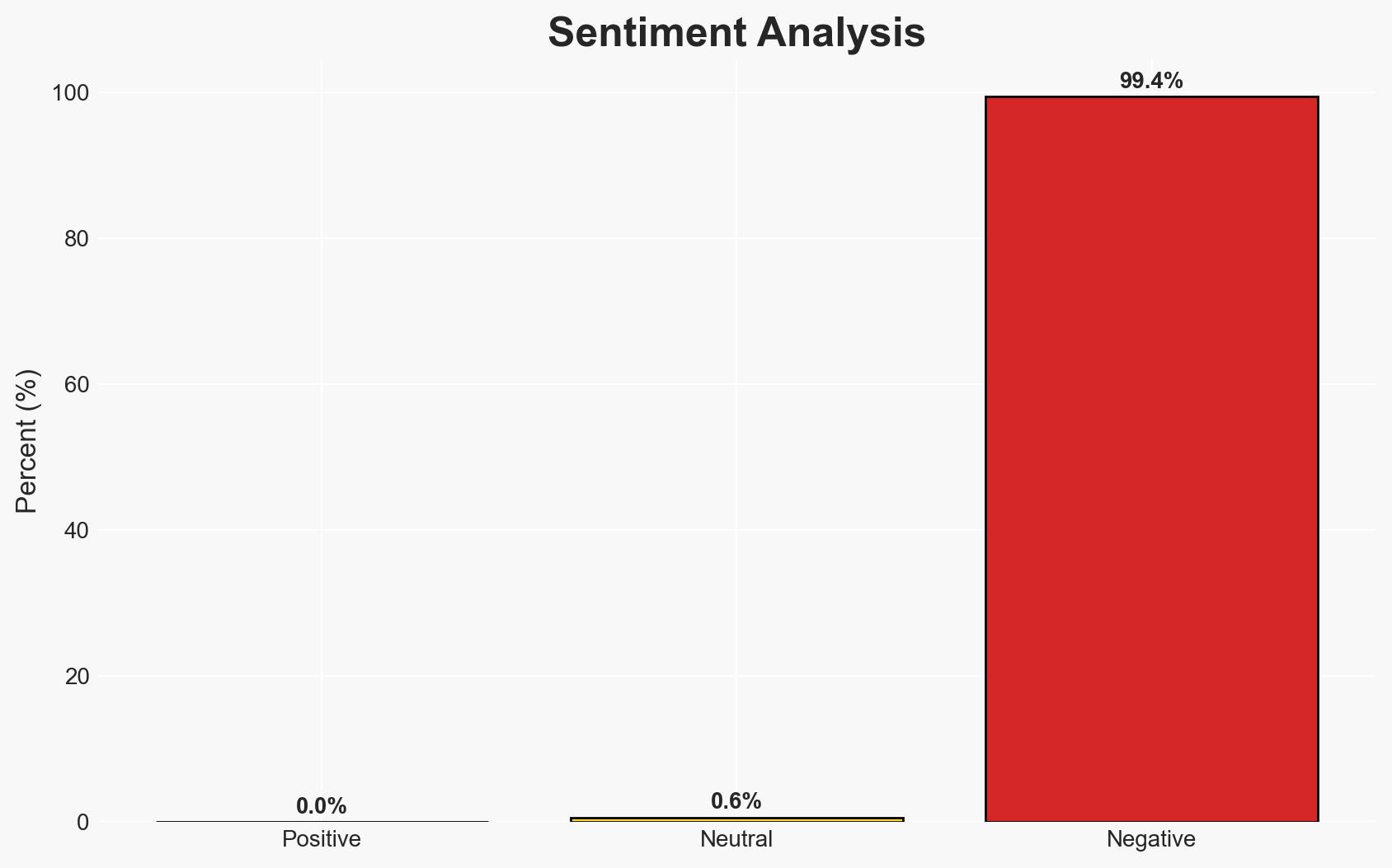
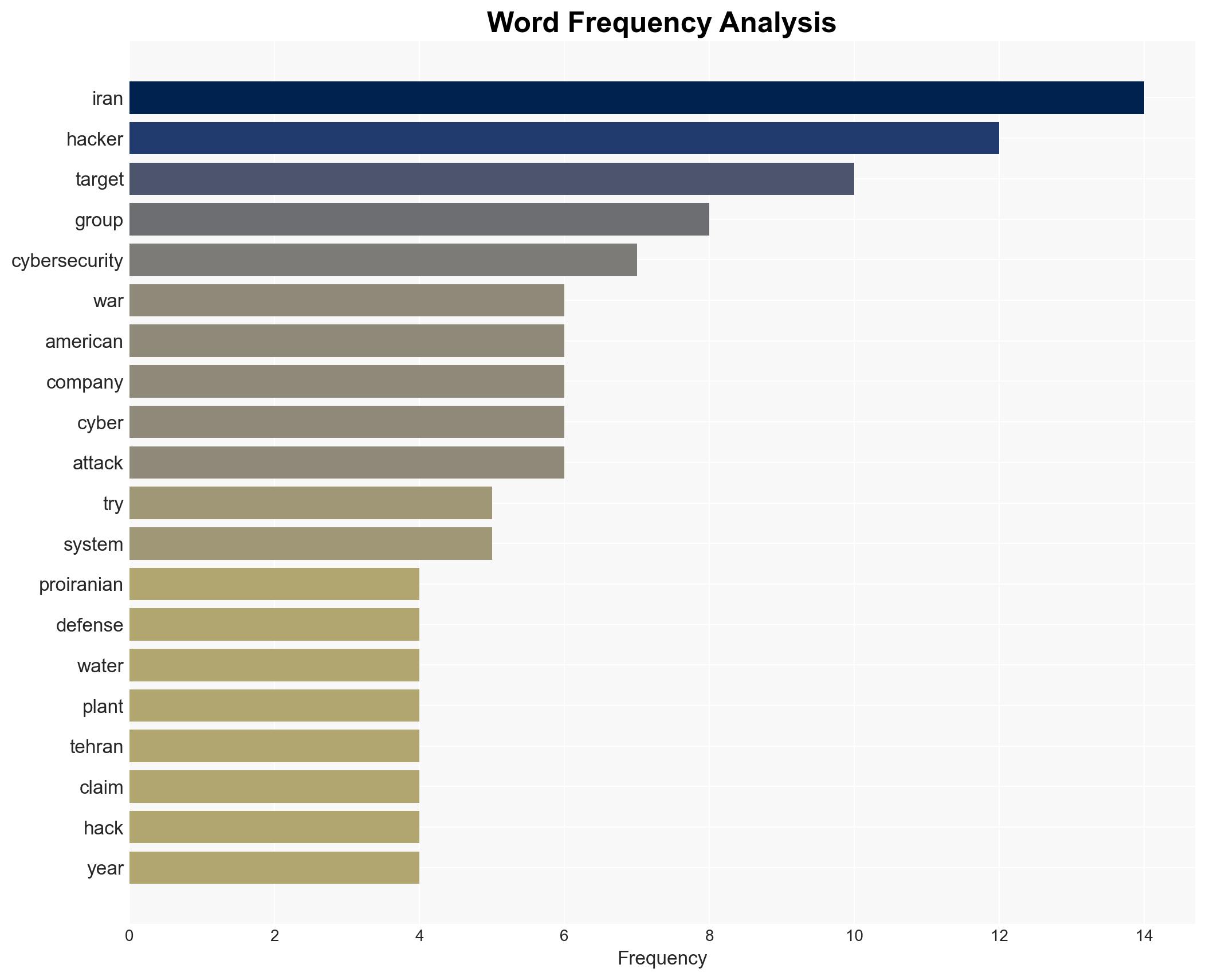
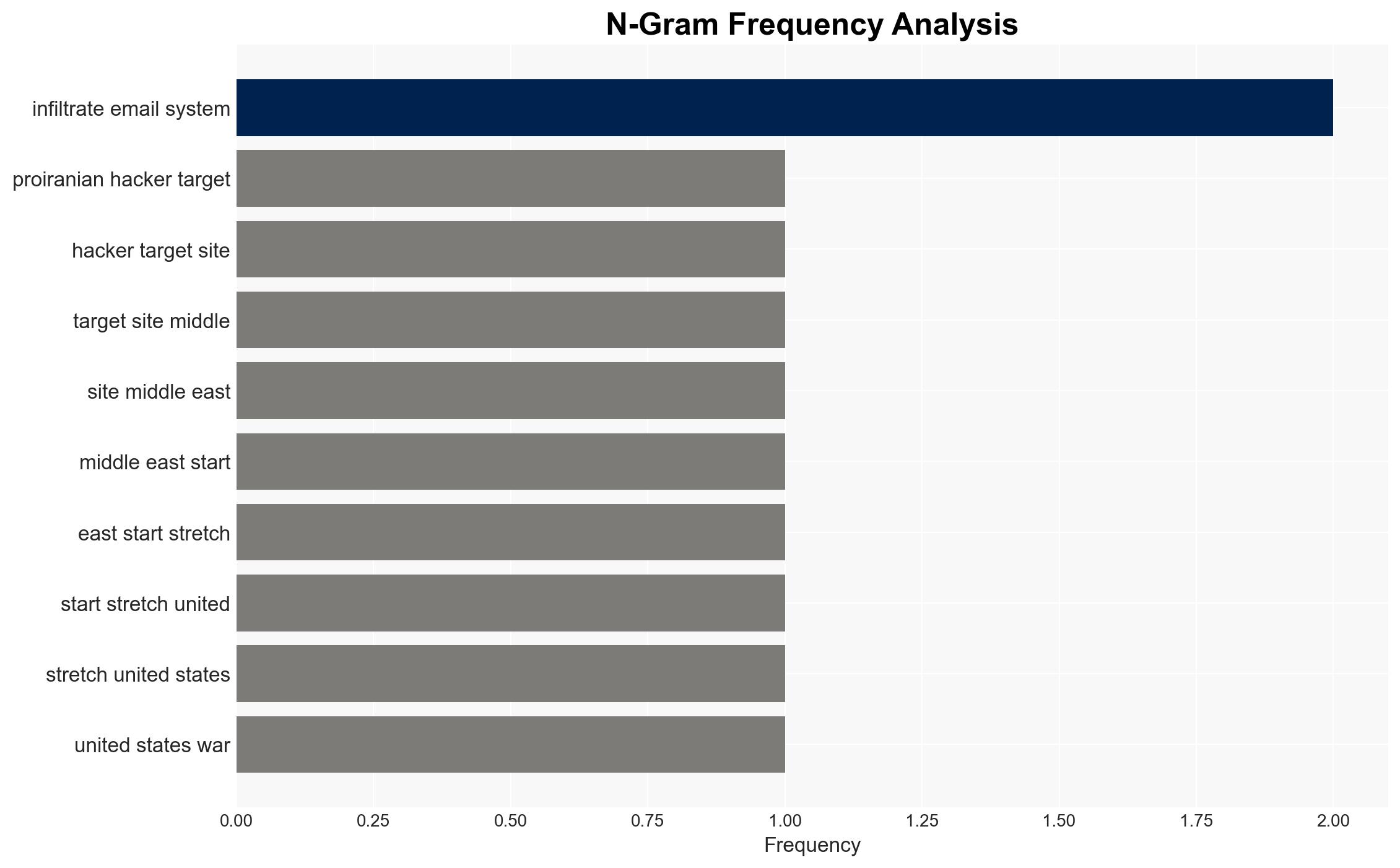
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Iran-Linked Hackers Take Aim at US Other Targets Raising Risk of Cyberattacks
1. BLUF (Bottom Line Up Front)
Pro-Iranian hackers are expanding their cyber operations from the Middle East to the United States, targeting critical infrastructure and defense-related entities. This escalation increases the risk of significant disruptions in sectors such as defense, energy, and healthcare. The most likely hypothesis is that these actions are part of a broader strategy to weaken U.S. capabilities and influence. Overall, this assessment is made with moderate confidence.
2. Competing Hypotheses
- Hypothesis A: The cyberattacks are a coordinated effort by Iran-linked groups to disrupt U.S. critical infrastructure as part of a strategic campaign to weaken American military and economic capabilities. Supporting evidence includes the targeting of defense contractors and critical infrastructure, and historical patterns of Iranian cyber operations. Key uncertainties include the full extent of Iranian government involvement and the potential for other state actors to be involved.
- Hypothesis B: The attacks are primarily opportunistic actions by ideologically motivated hackers with limited direct coordination with the Iranian government. This is supported by the focus on data destruction over financial gain and the use of public forums to discuss plans. Contradicting evidence includes the strategic nature of the targets and the historical context of Iranian cyber operations.
- Assessment: Hypothesis A is currently better supported due to the strategic selection of targets and the alignment with Iran’s historical cyber activities. Indicators that could shift this judgment include evidence of direct state sponsorship or a significant increase in attack sophistication.
3. Key Assumptions and Red Flags
- Assumptions: Iran-linked hackers have the capability to conduct sophisticated cyber operations; the Iranian government supports or condones these activities; U.S. critical infrastructure remains vulnerable to cyberattacks.
- Information Gaps: The extent of Iranian government involvement; the full scope of the hackers’ capabilities; potential involvement of other state or non-state actors.
- Bias & Deception Risks: Potential source bias from cybersecurity firms; risk of attributing attacks to Iran without conclusive evidence; possibility of false flag operations by other actors.
4. Implications and Strategic Risks
This development could lead to increased geopolitical tensions and a heightened cyber threat environment, potentially prompting retaliatory measures by the U.S. and its allies.
- Political / Geopolitical: Potential escalation of U.S.-Iran tensions; increased pressure on U.S. allies in the Middle East.
- Security / Counter-Terrorism: Heightened threat to critical infrastructure and defense sectors; increased resource allocation to cyber defense.
- Cyber / Information Space: Potential for widespread disruption of critical services; increased cyber espionage activities.
- Economic / Social: Potential economic impact from disrupted services; increased public concern over cybersecurity.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of critical infrastructure networks; increase information sharing with allies; conduct vulnerability assessments.
- Medium-Term Posture (1–12 months): Strengthen cyber resilience measures; develop partnerships with private sector cybersecurity firms; invest in cyber defense capabilities.
- Scenario Outlook:
- Best: Successful deterrence and mitigation of cyber threats with minimal disruption.
- Worst: Major cyberattack causing significant disruption to critical infrastructure.
- Most-Likely: Continued cyber skirmishes with periodic disruptions and increased defensive measures.
6. Key Individuals and Entities
- Kevin Mandia, founder of Mandiant and Armadin
- Ismael Valenzuela, Vice President of Threat Intelligence at Arctic Wolf
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
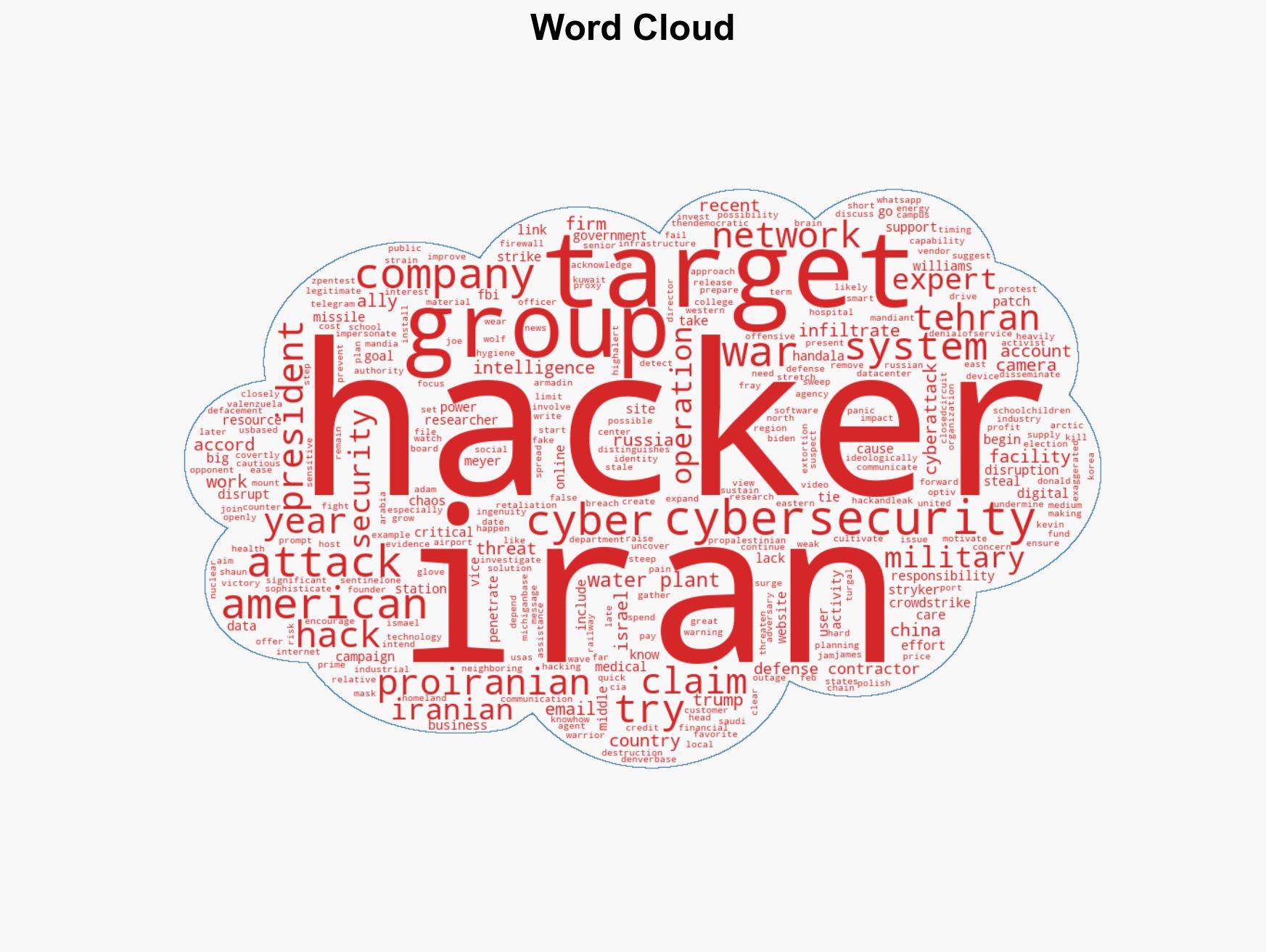
cybersecurity, Iran, critical infrastructure, cyber-espionage, geopolitical tensions, defense industry, cyber defense
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us