Iranian Hackers Target Stryker in Escalating Cyber Conflict Amid U.S.-Iran Tensions
Published on: 2026-03-13
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
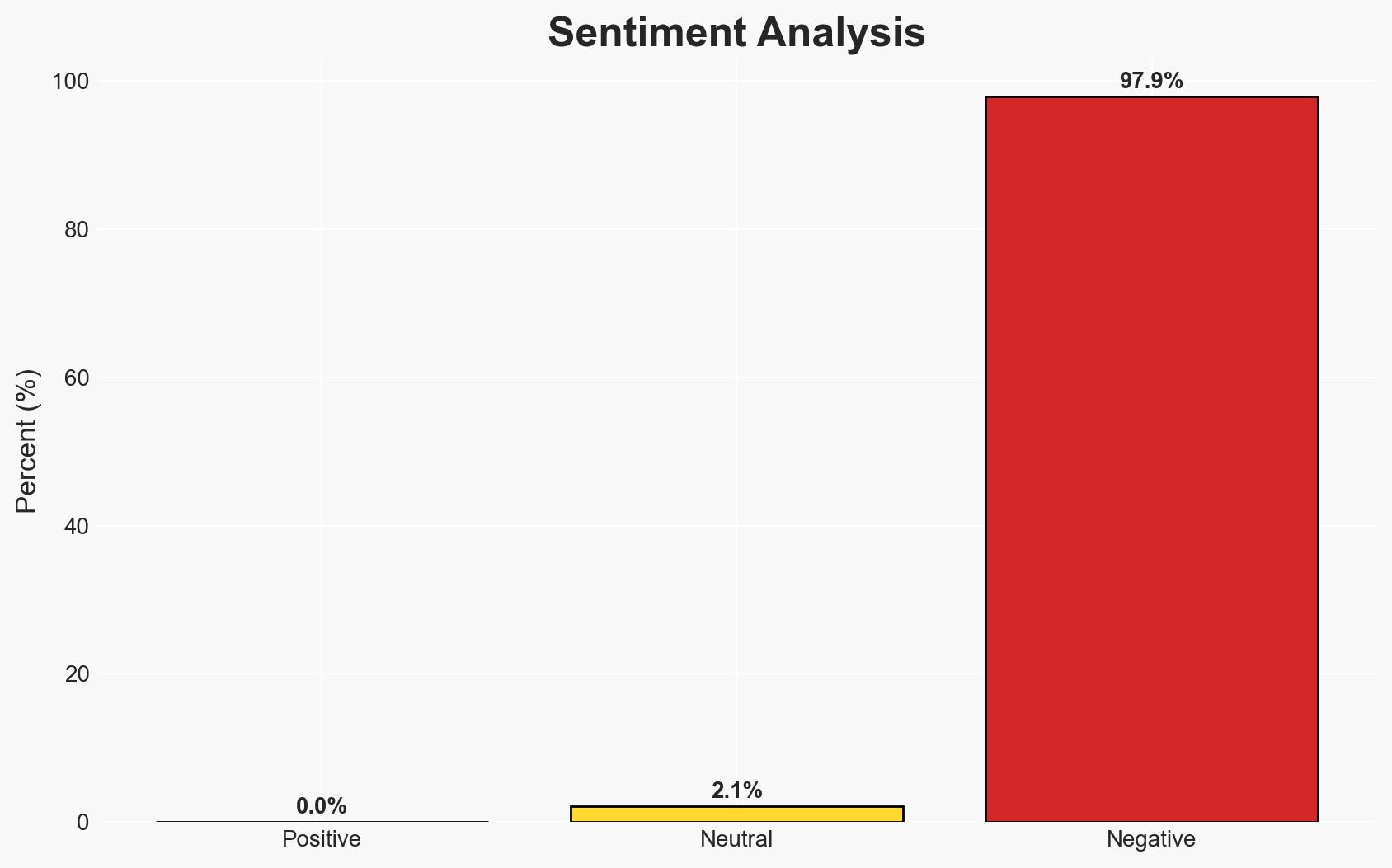
Intelligence Report: Cyber war escalates Iran-backed hackers target US medical-technology giant Stryker
1. BLUF (Bottom Line Up Front)
The cyberattack on Stryker by Iranian-aligned hackers represents a significant escalation in the ongoing cyber conflict between the U.S. and Iran. This incident underscores vulnerabilities in U.S. corporate digital infrastructure and highlights the potential for further retaliatory cyber operations. The most likely hypothesis is that this attack is a direct response to U.S. military actions against Iran. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
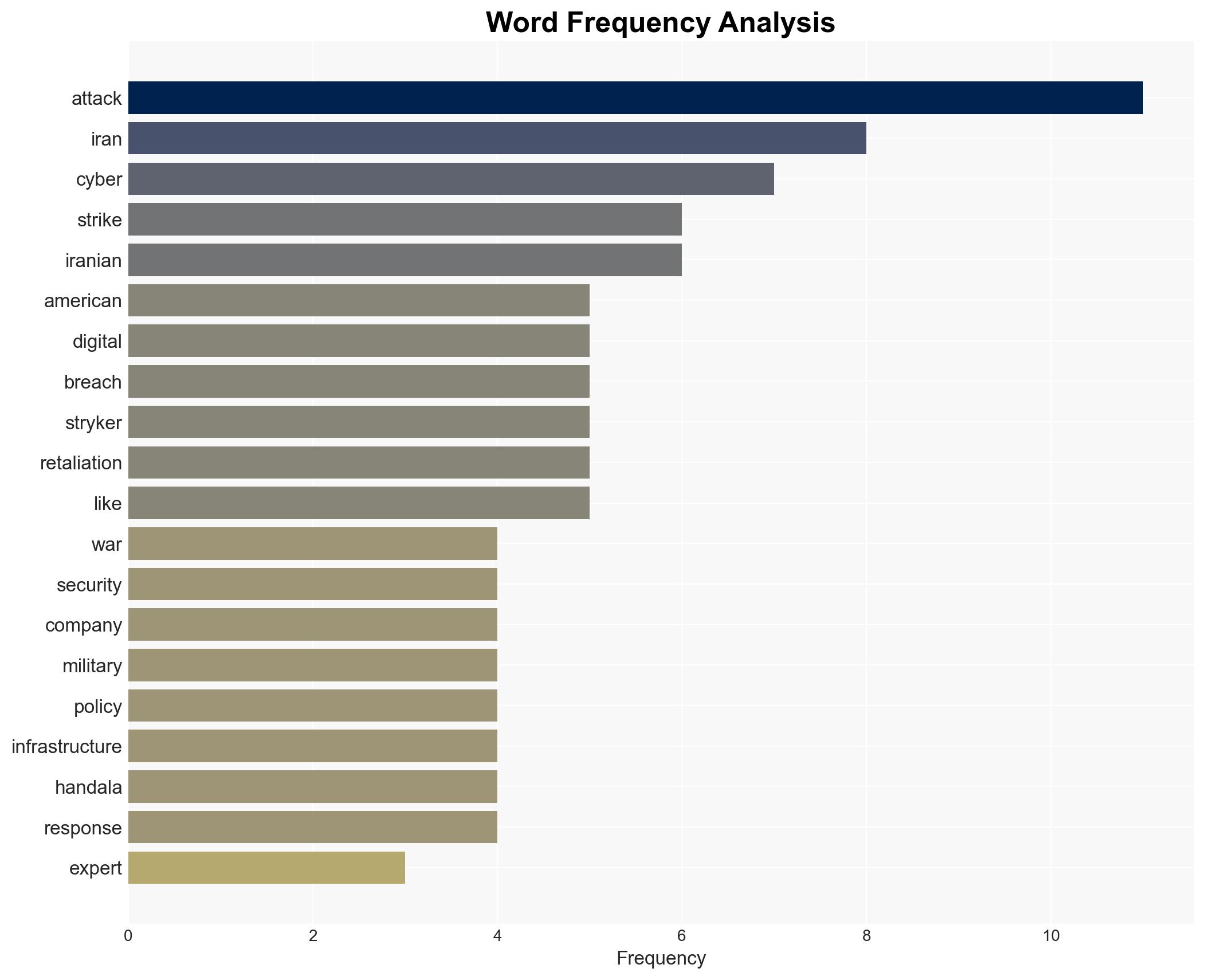
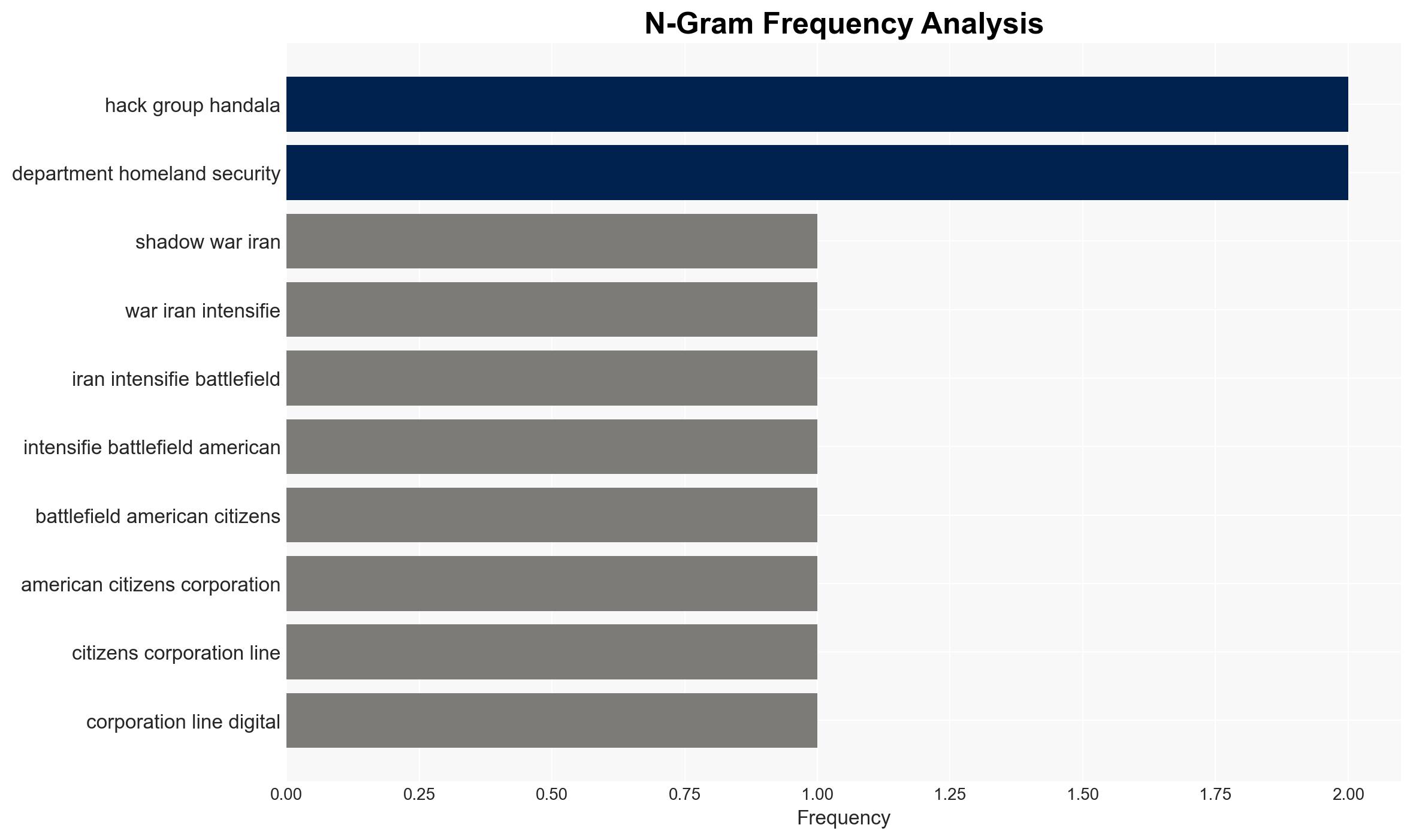
- Hypothesis A: The attack on Stryker is a direct retaliation by Iranian-aligned hackers for recent U.S. military actions against Iran. This is supported by the timing of the attack and the claim of responsibility by the Handala group. However, the exact link between specific U.S. actions and this cyberattack remains uncertain.
- Hypothesis B: The attack could be part of a broader Iranian strategy to disrupt U.S. economic interests and test cyber defenses, irrespective of specific military actions. This hypothesis is less supported due to the explicit retaliatory claims made by the attackers.
- Assessment: Hypothesis A is currently better supported due to the direct claim of responsibility and the context of recent U.S.-Iran tensions. Indicators such as further cyberattacks following U.S. military actions could reinforce this judgment.
3. Key Assumptions and Red Flags
- Assumptions: The Iranian government has control over or influence on the Handala hacking group; U.S. military actions are perceived by Iran as requiring retaliation; Stryker was targeted due to its symbolic or strategic value.
- Information Gaps: Specific details of the cyberattack methodology and the full extent of the damage to Stryker’s operations; any direct communications between Iranian state actors and the Handala group.
- Bias & Deception Risks: Potential bias in attributing the attack solely to Iranian state interests without considering other actors; risk of deception in the Handala group’s public statements to mislead about their true motives or capabilities.
4. Implications and Strategic Risks
This development could lead to increased cyber hostilities between the U.S. and Iran, with potential spillover effects on other sectors and allies. The incident may prompt a reassessment of cyber defense strategies and international cyber norms.
- Political / Geopolitical: Potential escalation in U.S.-Iran tensions, influencing diplomatic and military engagements.
- Security / Counter-Terrorism: Increased vigilance required for potential retaliatory actions in other domains.
- Cyber / Information Space: Heightened risk of further cyberattacks on U.S. infrastructure, necessitating improved cybersecurity measures.
- Economic / Social: Disruption to Stryker’s operations could impact the medical technology sector and broader economic confidence.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance cybersecurity monitoring and defenses for critical infrastructure; engage in diplomatic channels to de-escalate tensions.
- Medium-Term Posture (1–12 months): Develop resilience measures and public-private partnerships to bolster cybersecurity capabilities; consider strategic cyber deterrence policies.
- Scenario Outlook: Best: De-escalation through diplomatic engagement; Worst: Escalation to broader cyber conflict; Most-Likely: Continued low-level cyber skirmishes with periodic escalations.
6. Key Individuals and Entities
- Handala hacking group
- Stryker Corporation
- Department of Homeland Security
- Not clearly identifiable from open sources in this snippet.
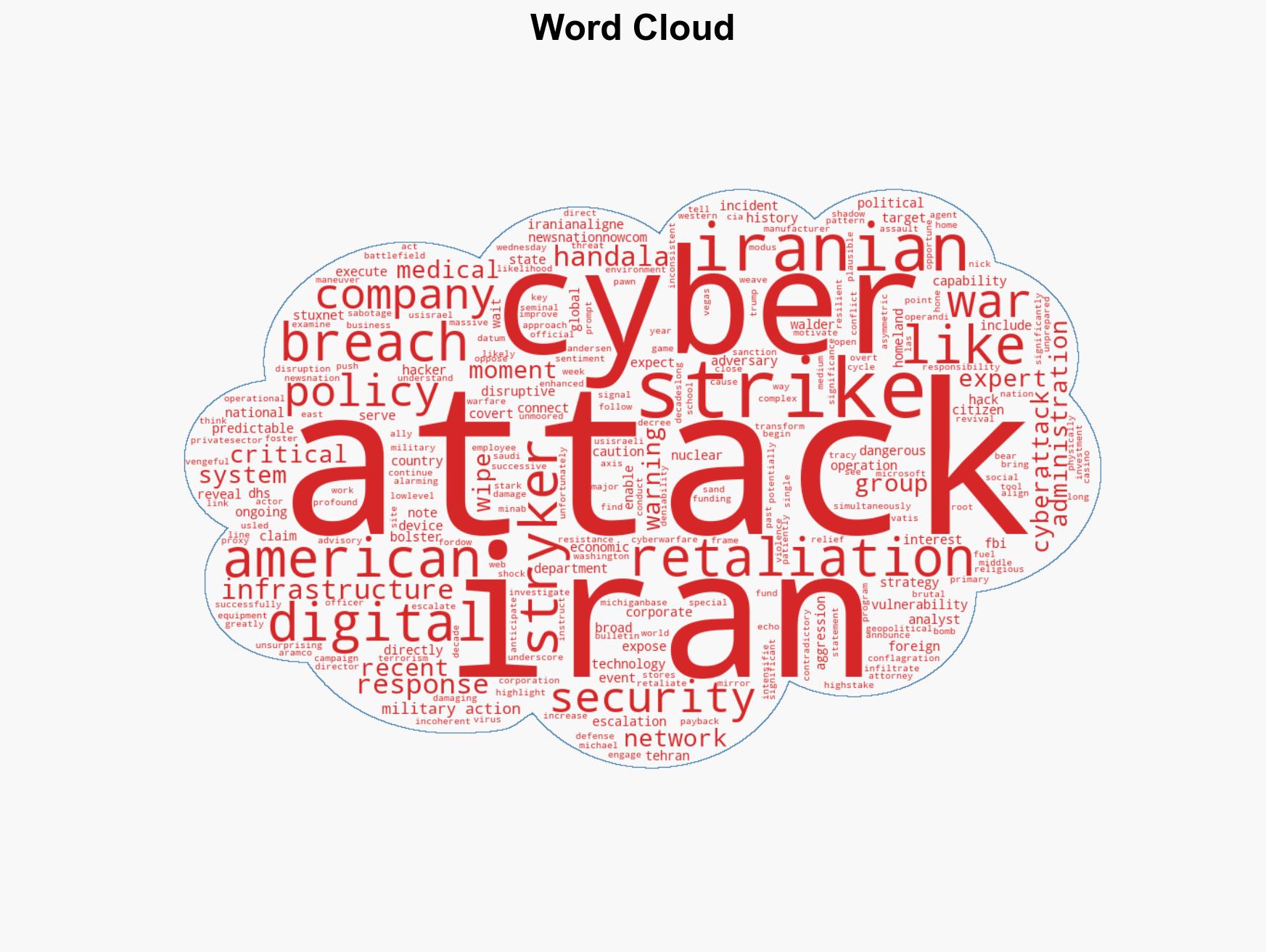
7. Thematic Tags
cybersecurity, cyber-warfare, U.S.-Iran relations, retaliation, geopolitical tensions, digital infrastructure, economic impact
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us