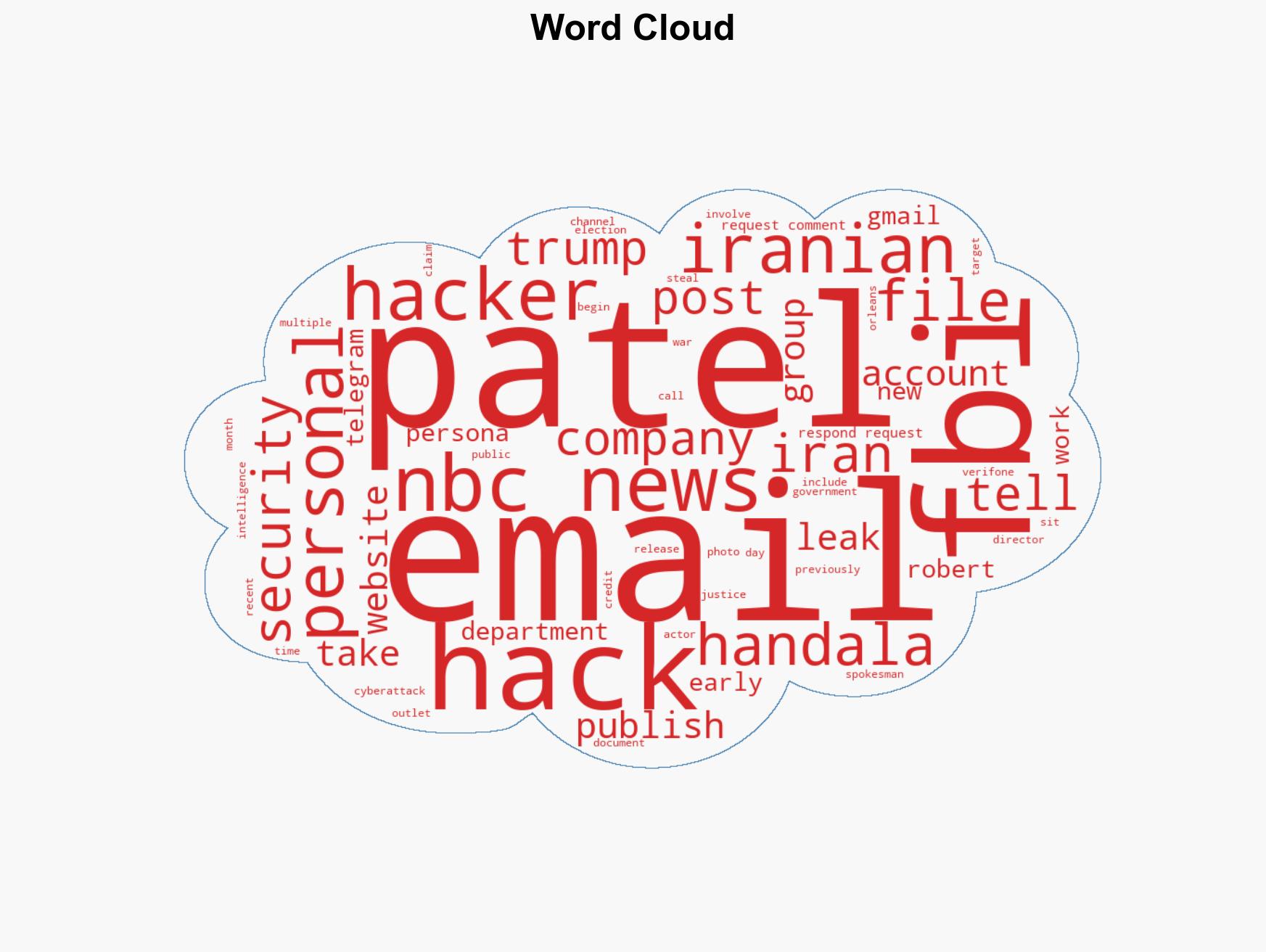
Iranian hacking group releases over 300 emails from FBI Director Kash Patel amid ongoing cyber tensions
Published on: 2026-03-27
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Iranian hackers publish emails allegedly stolen from Kash Patel
1. BLUF (Bottom Line Up Front)
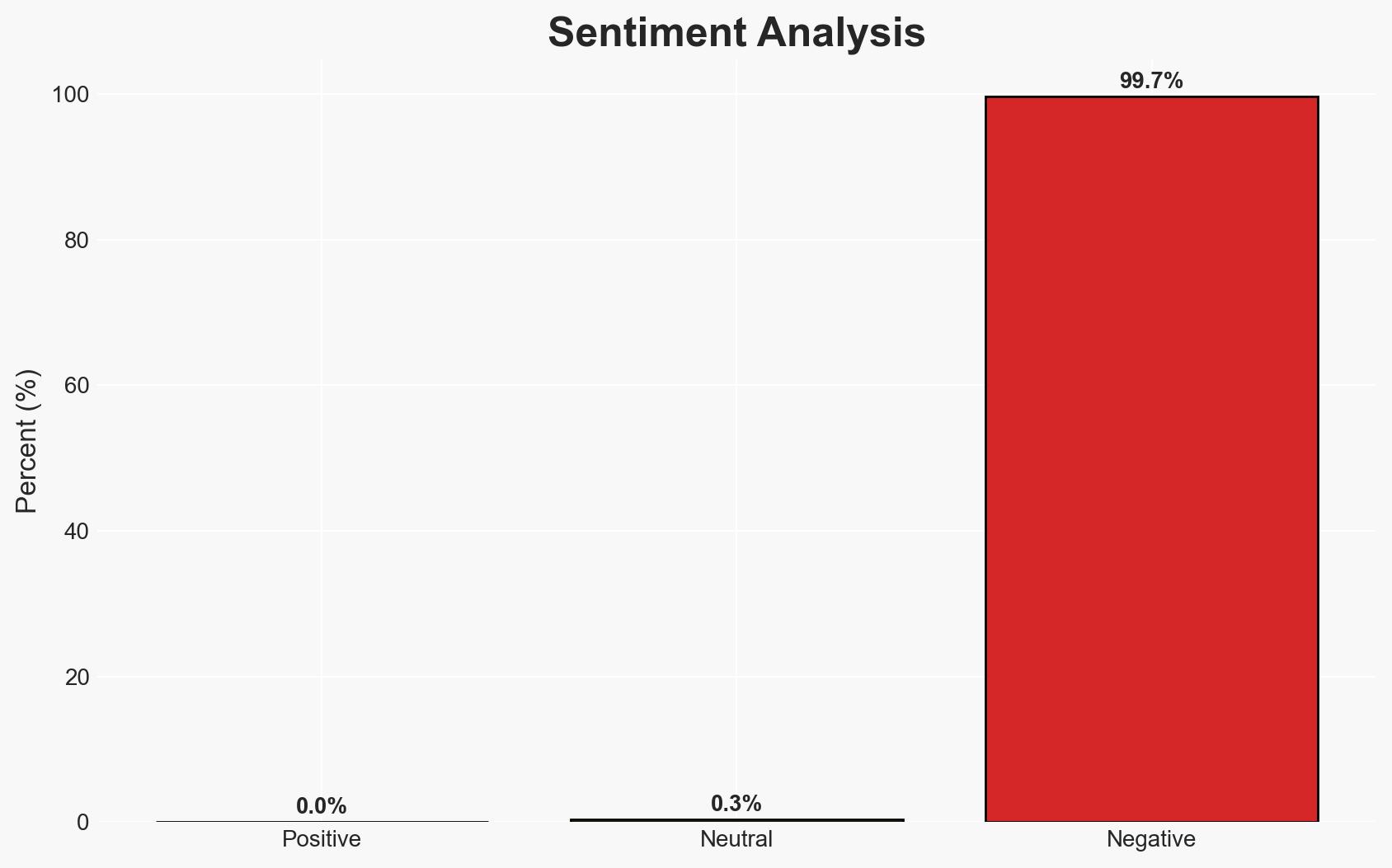
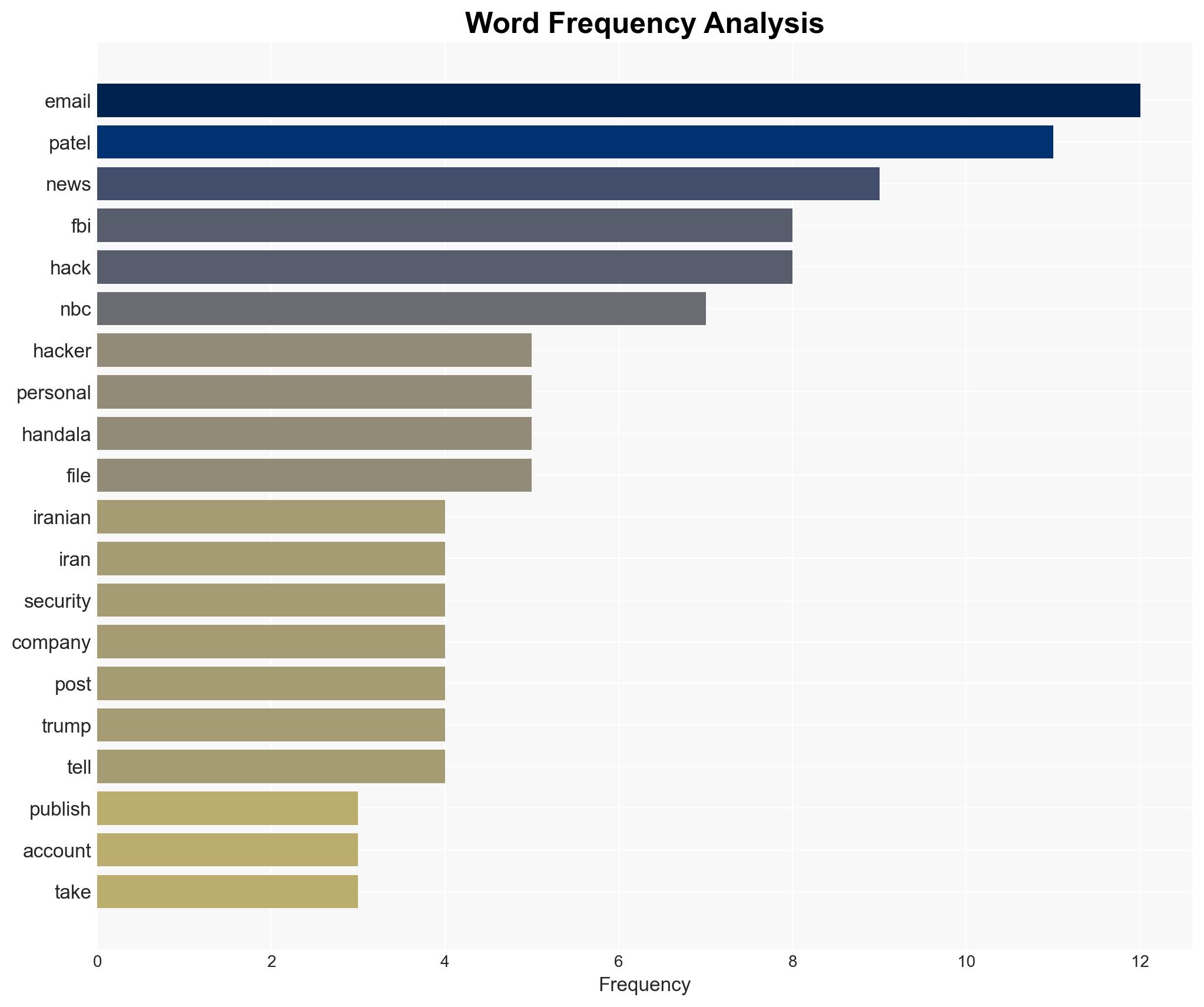
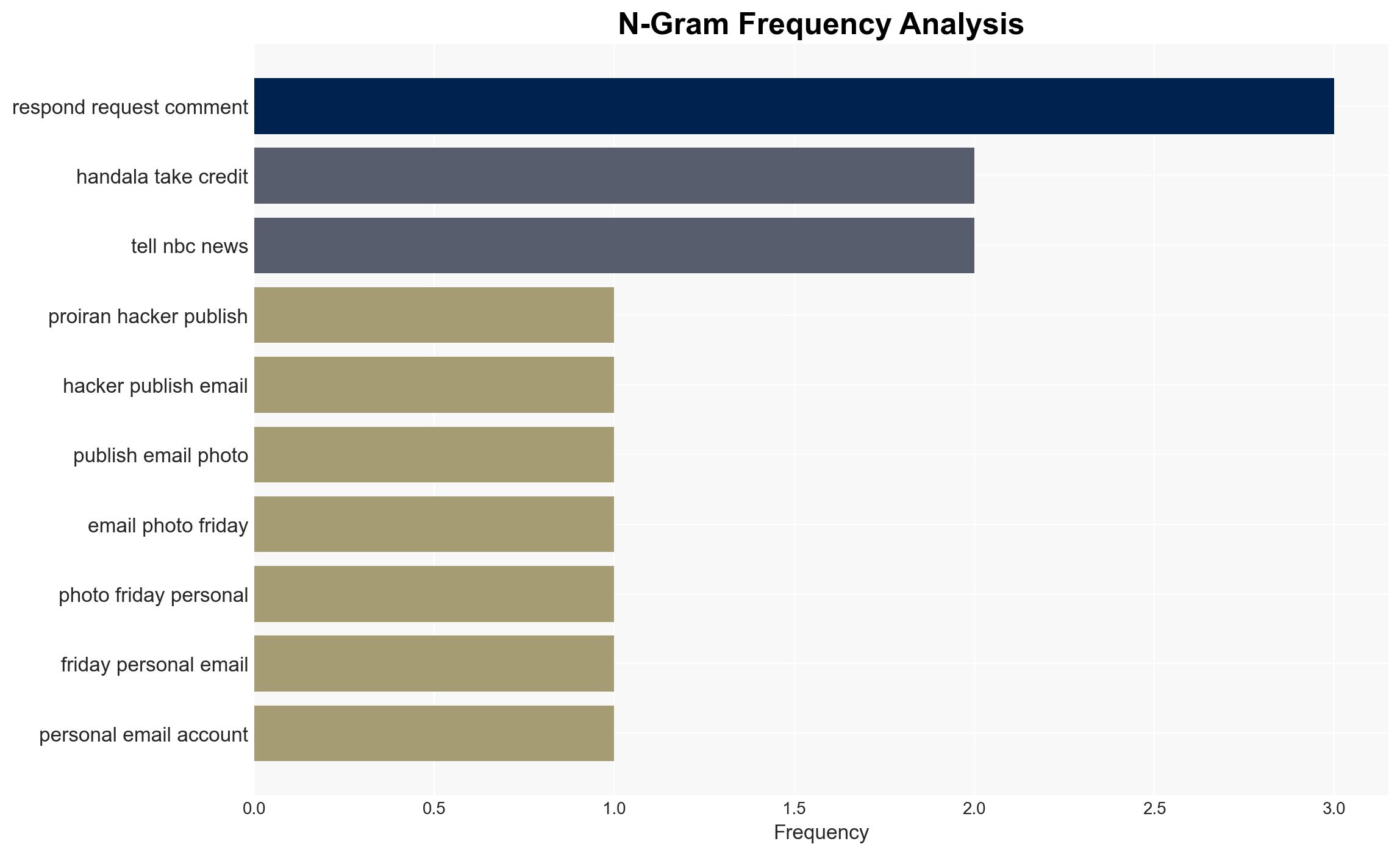
Pro-Iranian hackers, identified as Handala, have published emails allegedly stolen from Kash Patel’s personal account. This incident appears to be a retaliatory act following U.S. actions against the group’s online presence. The breach, while significant, involves historical personal data with no direct government information. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The hack is a direct retaliation by Handala against U.S. actions, specifically the seizure of their websites. This is supported by the group’s statements and timing of the leak. However, the authenticity of the emails remains partially unverified, creating uncertainty.
- Hypothesis B: The hack is part of a broader Iranian intelligence operation targeting U.S. officials, with the leak serving as a psychological operation. This is supported by the group’s alleged ties to Iran’s Ministry of Intelligence and Security, but lacks direct evidence linking the operation to broader strategic goals.
- Assessment: Hypothesis A is currently better supported due to the explicit retaliatory statements by Handala and the context of recent U.S. actions against them. Indicators that could shift this judgment include verification of the emails’ authenticity and further evidence of strategic intent beyond retaliation.
3. Key Assumptions and Red Flags
- Assumptions: The emails are assumed to be authentic unless proven otherwise; Handala’s claims are taken at face value; the group’s ties to Iranian intelligence are presumed based on U.S. accusations.
- Information Gaps: Lack of forensic verification of the emails; unclear extent of Handala’s operational capabilities and strategic objectives.
- Bias & Deception Risks: Potential bias in U.S. statements regarding Handala’s ties to Iranian intelligence; possible deception by Handala in exaggerating the impact of the breach.
4. Implications and Strategic Risks
This development could escalate tensions between the U.S. and Iran, particularly in the cyber domain, and may influence future U.S. cyber defense strategies.
- Political / Geopolitical: Potential for increased diplomatic friction and retaliatory measures between the U.S. and Iran.
- Security / Counter-Terrorism: Heightened threat environment for U.S. officials and potential for further cyberattacks targeting critical infrastructure.
- Cyber / Information Space: Increased focus on cyber defense and intelligence operations; potential for misinformation campaigns leveraging leaked data.
- Economic / Social: Limited immediate economic impact, but potential for long-term effects on public trust in digital security.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of Iranian cyber activities; verify the authenticity of leaked emails; engage in diplomatic channels to de-escalate tensions.
- Medium-Term Posture (1–12 months): Strengthen cyber resilience measures; develop partnerships with allies for intelligence sharing; invest in public awareness campaigns on digital security.
- Scenario Outlook:
- Best Case: Diplomatic resolution reduces cyber tensions; no further significant breaches occur.
- Worst Case: Escalation leads to widespread cyberattacks on U.S. infrastructure.
- Most Likely: Continued low-level cyber skirmishes with occasional data leaks.
6. Key Individuals and Entities
- Kash Patel – Alleged victim of the email hack.
- Handala – Pro-Iranian hacking group responsible for the breach.
- FBI – U.S. federal agency involved in the response to the breach.
- Iran’s Ministry of Intelligence and Security – Alleged sponsor of Handala.
7. Thematic Tags
cybersecurity, cyber-espionage, Iran-U.S. relations, intelligence operations, cyber-security, information warfare, diplomatic tensions
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us