Iranian State-Backed Hackers Breach Critical U.S. Infrastructure Amid Rising Military Tensions
Published on: 2026-03-06
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
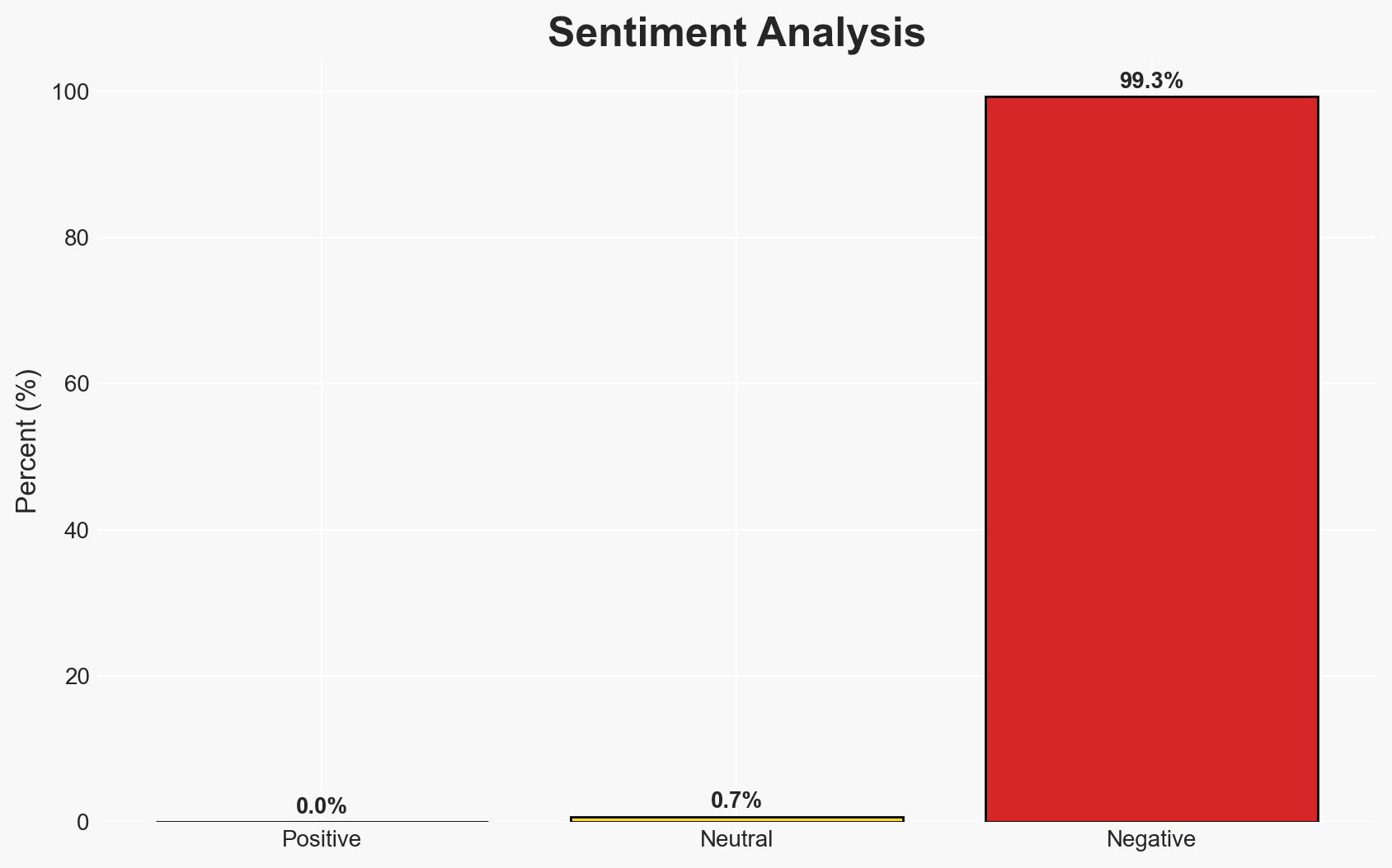
Intelligence Report: Iran-linked hackers plant secret backdoors in critical American infrastructure
1. BLUF (Bottom Line Up Front)
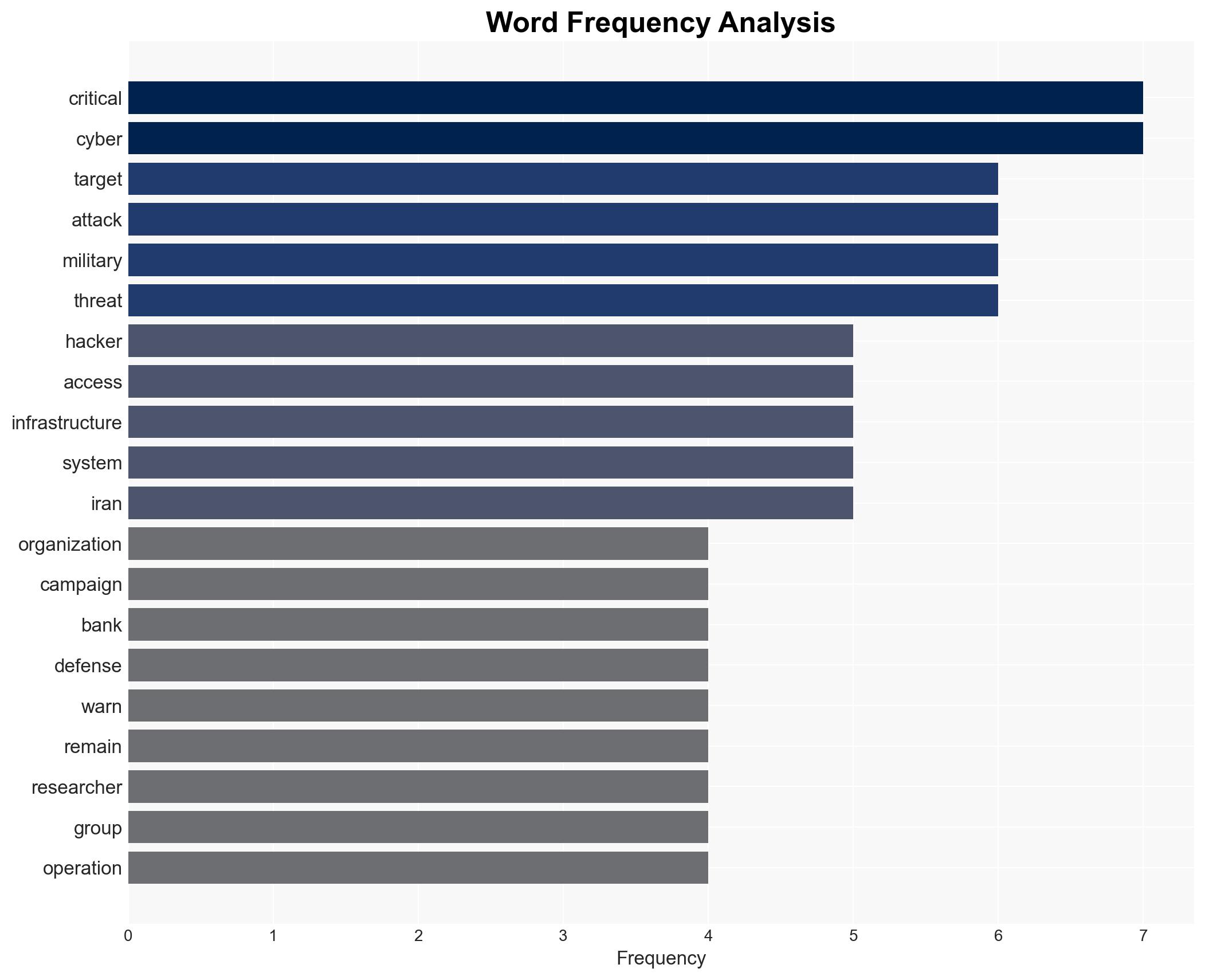
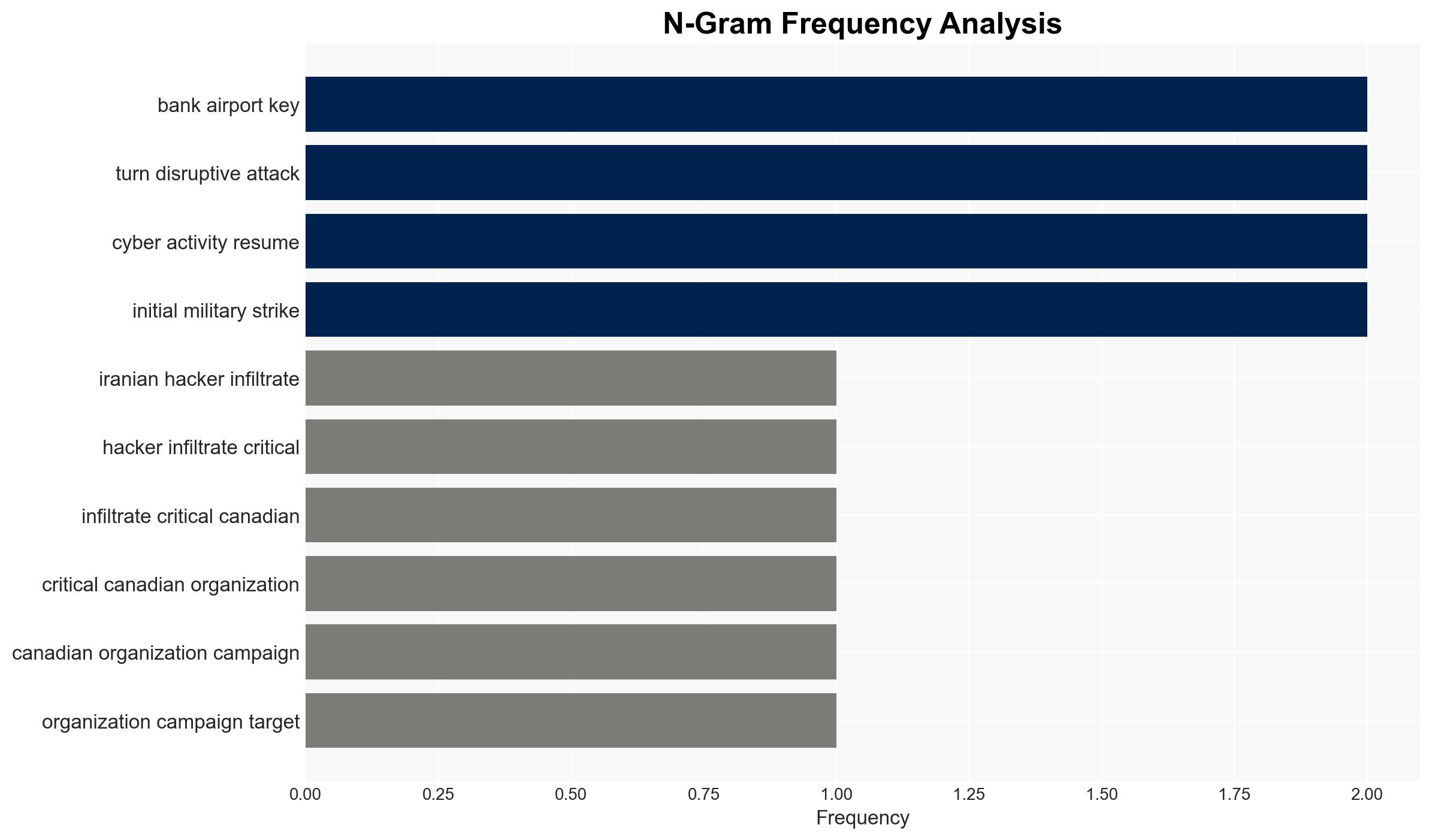
Iranian state-backed hackers have infiltrated critical U.S. and Canadian infrastructure, targeting sectors such as finance, transportation, and defense. This campaign, linked to increased military tensions, poses a significant risk of disruptive cyber attacks. The most likely hypothesis is that these actions are preparatory for potential future strikes. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The infiltration is primarily for cyber espionage purposes, aiming to gather intelligence and exert strategic pressure. Supporting evidence includes the use of backdoor malware for persistent access and the targeting of sensitive sectors. However, the lack of immediate disruptive attacks suggests espionage rather than direct sabotage.
- Hypothesis B: The campaign is a preparatory phase for potential future disruptive cyber attacks, possibly in retaliation for military actions. This is supported by the timing of the cyber activity alongside military tensions and the strategic positioning within critical infrastructure networks.
- Assessment: Hypothesis B is currently better supported due to the strategic nature of the targets and the timing of the campaign. Indicators such as increased military tensions and the specific targeting of defense-related entities could shift this judgment if further evidence of espionage emerges.
3. Key Assumptions and Red Flags
- Assumptions: The Iranian state directly supports the hackers; the campaign’s timing is linked to geopolitical tensions; the backdoor malware is primarily for future disruptive capabilities.
- Information Gaps: Specific data exfiltrated by the hackers; the full extent of network infiltration; potential undiscovered malware variants.
- Bias & Deception Risks: Potential confirmation bias in linking cyber activity to geopolitical events; reliance on cybersecurity firm reports which may have commercial biases; possible Iranian deception to mask true intentions.
4. Implications and Strategic Risks
This development could lead to increased geopolitical tensions and potential retaliatory actions. The cyber threat landscape may evolve, affecting national security and economic stability.
- Political / Geopolitical: Escalation of tensions between Iran and Western nations, potentially leading to diplomatic or military responses.
- Security / Counter-Terrorism: Heightened threat environment requiring increased vigilance and defensive measures in critical infrastructure sectors.
- Cyber / Information Space: Potential for increased cyber warfare activities and information operations targeting public perception and morale.
- Economic / Social: Disruptions in critical sectors could lead to economic instability and public unrest, particularly if attacks affect essential services.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of critical infrastructure networks, conduct vulnerability assessments, and increase information sharing with allies.
- Medium-Term Posture (1–12 months): Develop resilience measures, strengthen public-private partnerships, and invest in cybersecurity capabilities and training.
- Scenario Outlook:
- Best: De-escalation of military tensions reduces cyber threat levels.
- Worst: Coordinated cyber attacks cause significant disruptions in critical infrastructure.
- Most-Likely: Continued cyber espionage with sporadic disruptive activities, contingent on geopolitical developments.
6. Key Individuals and Entities
- Seedworm (Iran-linked hacker group)
- Symantec (cybersecurity firm)
- Carbon Black (cybersecurity firm)
- John Hultquist (Chief Analyst, Google’s Threat Intelligence Group)
- Not clearly identifiable from open sources in this snippet for specific Iranian state actors.
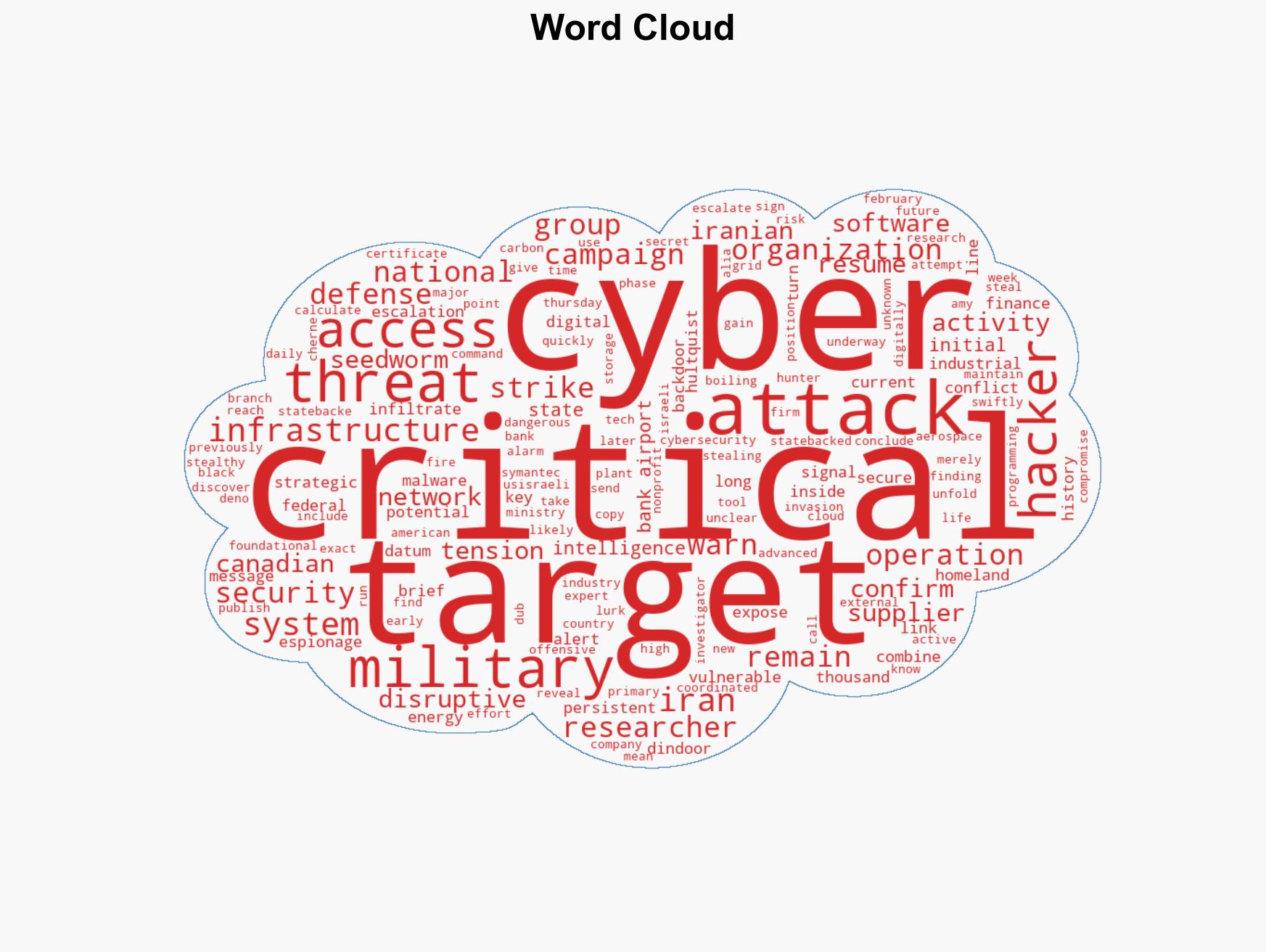
7. Thematic Tags
cybersecurity, cyber-espionage, critical infrastructure, Iran, cyber warfare, national security, geopolitical tensions
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us