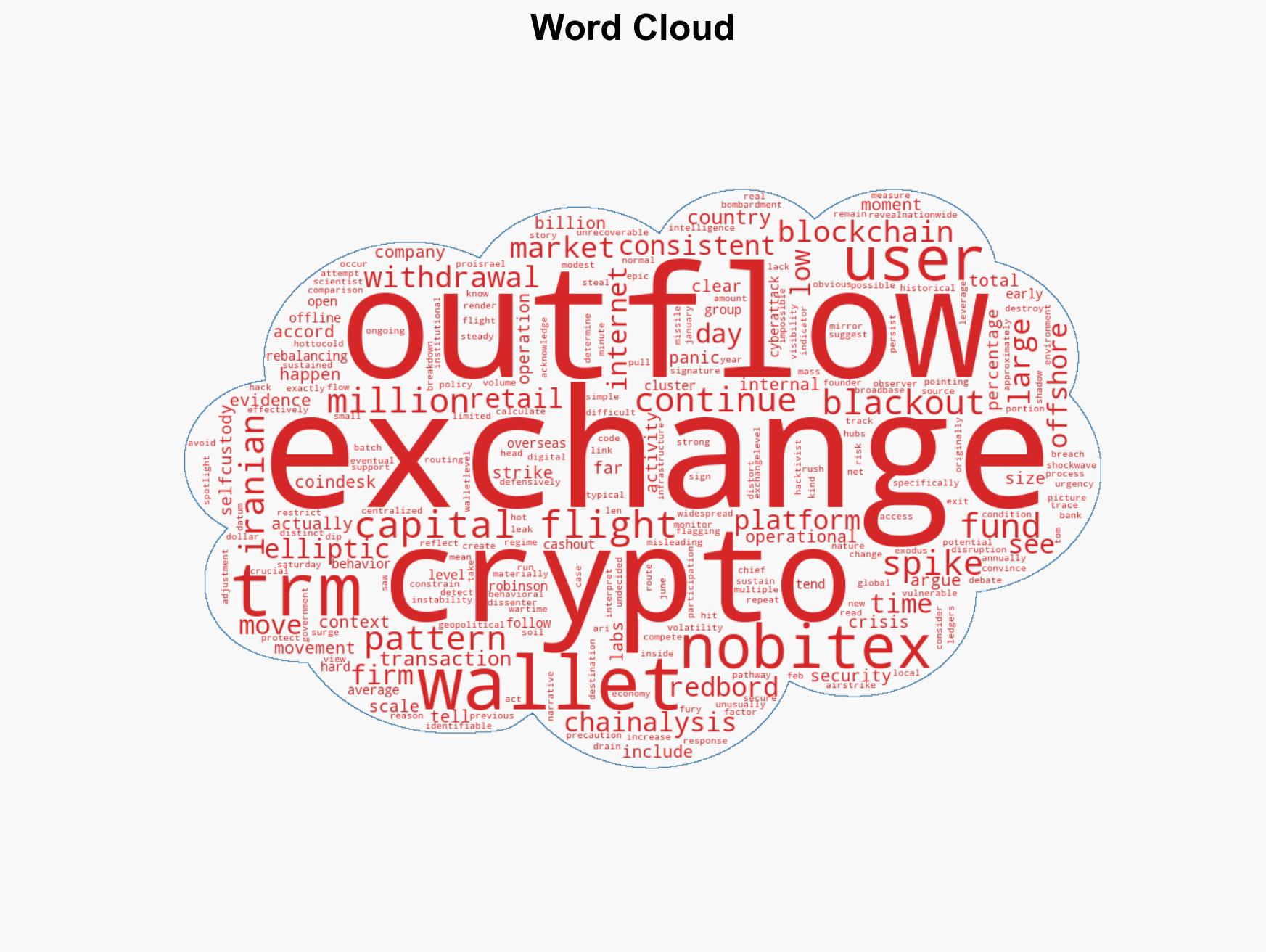
Iran’s Crypto Outflows Spark Debate: Panic or Strategic Security Measures?
Published on: 2026-03-04
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Exodus or firewall Blockchain analysts clash over Irans crypto outflows
1. BLUF (Bottom Line Up Front)
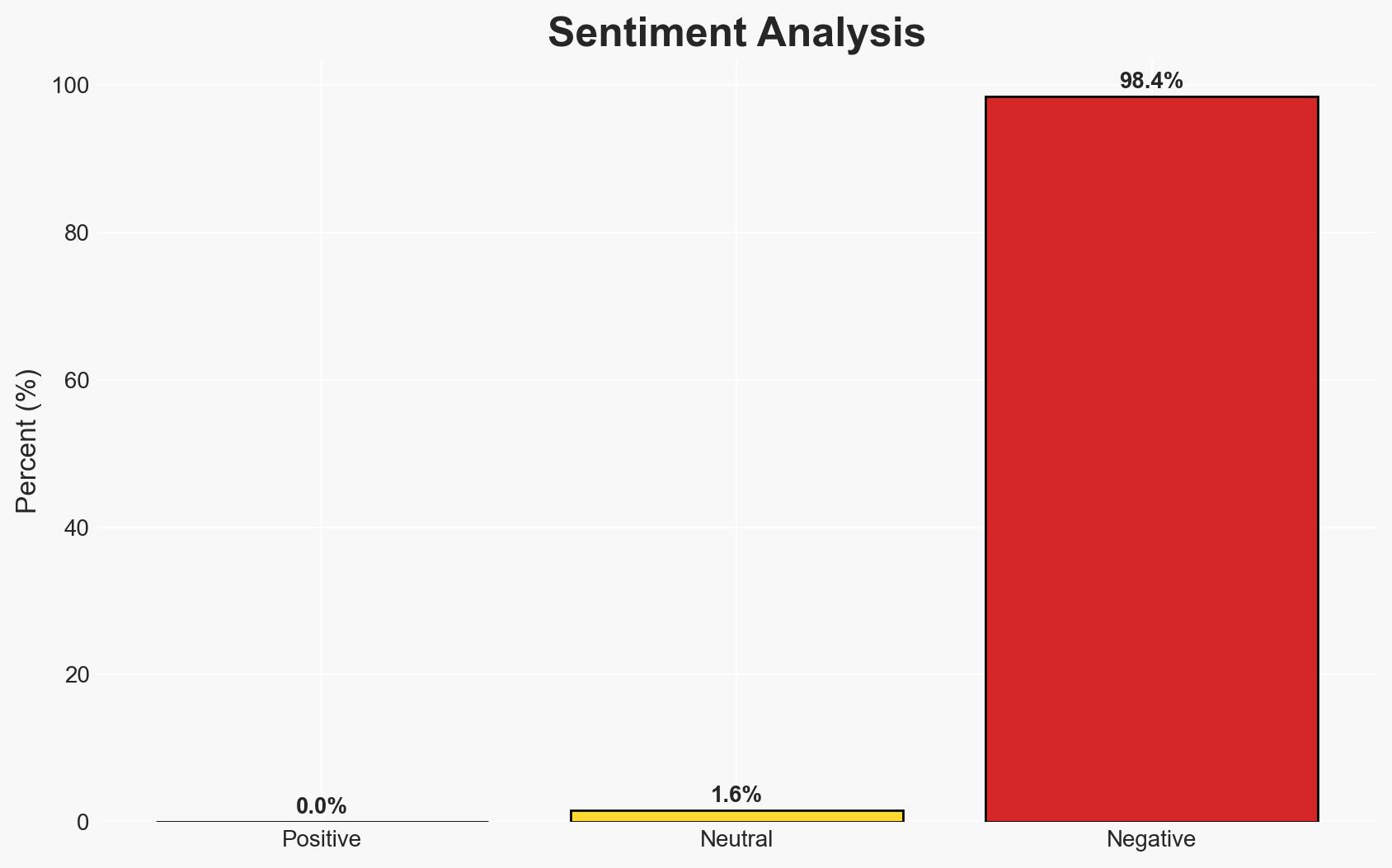
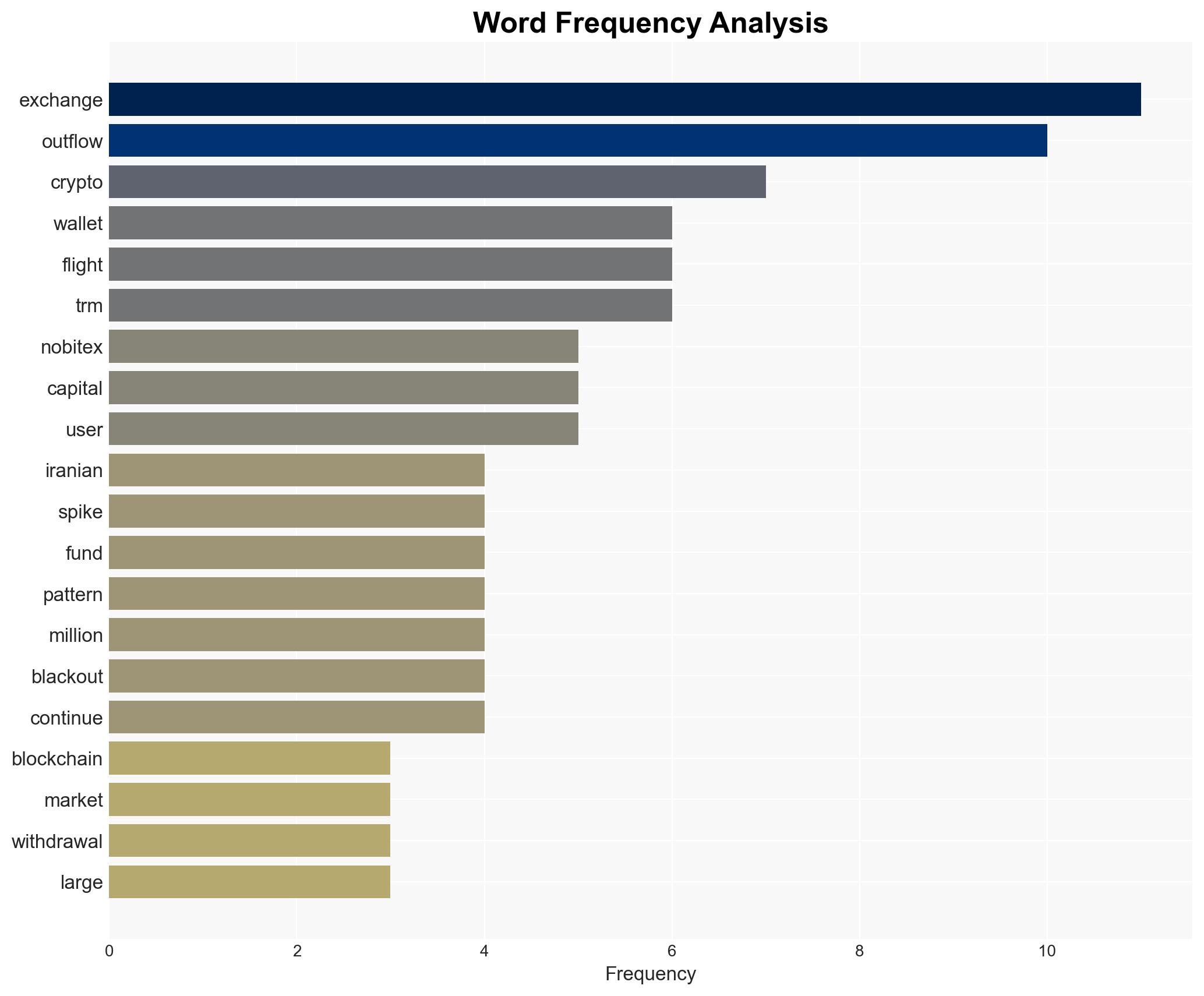
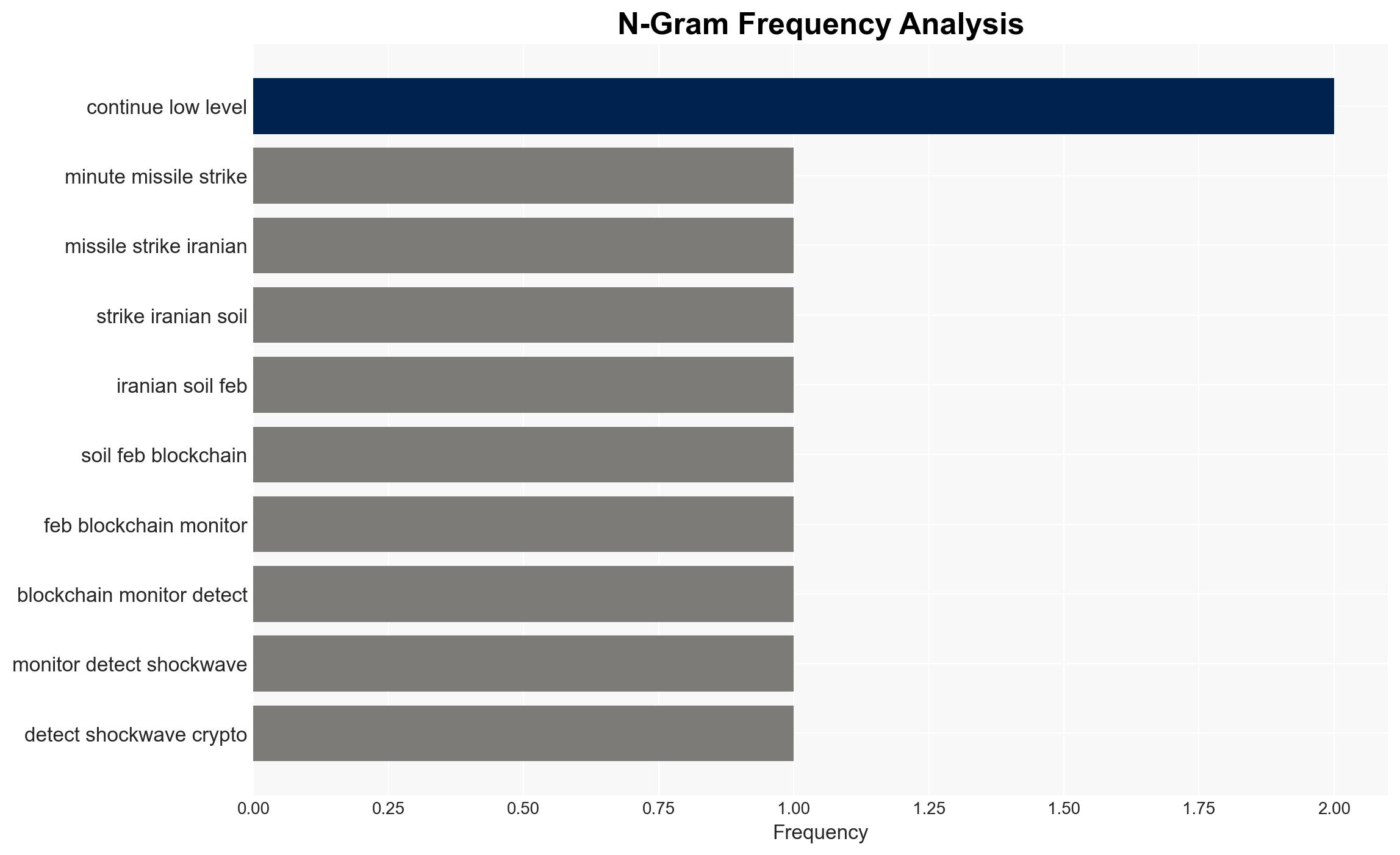
The recent spike in cryptocurrency outflows from Iranian exchanges, particularly Nobitex, following missile strikes on Iranian soil is more likely a defensive measure against potential cyber threats rather than a panic-driven capital flight. This assessment is based on the context of past cyberattacks and operational security measures. Overall, the confidence level in this judgment is moderate.
2. Competing Hypotheses
- Hypothesis A: The outflows represent a panic-driven capital flight by Iranian users in response to geopolitical instability. Supporting evidence includes the significant percentage increase in withdrawals. However, this is contradicted by the relatively small absolute value of the outflows and the context of internet disruptions.
- Hypothesis B: The outflows are part of a strategic operational security measure by Nobitex to protect against cyberattacks, particularly in light of past breaches. Supporting evidence includes the pattern of hot-to-cold wallet rebalancing and historical precedence of cyber threats.
- Assessment: Hypothesis B is currently better supported due to the contextual understanding of past cyber threats and the operational patterns observed. Key indicators that could shift this judgment include sustained net outflows over multiple days or evidence of user-driven cashouts.
3. Key Assumptions and Red Flags
- Assumptions: The assumption that Nobitex’s actions are primarily driven by cybersecurity concerns; the assumption that internet disruptions limited user access to exchanges; the assumption that the percentage increase in outflows does not equate to significant capital flight.
- Information Gaps: Lack of detailed data on user behavior during the outflow period; absence of comprehensive transaction tracing to determine final destinations of funds.
- Bias & Deception Risks: Potential bias from blockchain analysis firms with differing interpretations; risk of misinterpretation due to lack of context in percentage-based data.
4. Implications and Strategic Risks
The development could influence future operational security measures by exchanges in volatile regions and affect user trust in centralized platforms.
- Political / Geopolitical: Increased geopolitical tensions may lead to further scrutiny of financial flows and sanctions compliance.
- Security / Counter-Terrorism: Heightened risk of cyberattacks on financial infrastructure during geopolitical crises.
- Cyber / Information Space: Potential for increased cyber defense measures and information operations targeting financial systems.
- Economic / Social: Potential destabilization of local financial markets if perceived as capital flight; impact on public confidence in financial systems.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of cryptocurrency transactions for unusual patterns; engage with exchanges to understand security measures in place.
- Medium-Term Posture (1–12 months): Develop partnerships with blockchain intelligence firms for improved data sharing; invest in cybersecurity capabilities for financial institutions.
- Scenario Outlook:
- Best: Improved cybersecurity measures prevent future breaches, stabilizing market confidence.
- Worst: Continued geopolitical instability leads to sustained capital flight and market destabilization.
- Most-Likely: Exchanges implement robust security protocols, mitigating immediate risks but maintaining cautious user behavior.
6. Key Individuals and Entities
- Nobitex (Iran’s largest crypto exchange)
- Chainalysis (Blockchain analysis firm)
- TRM Labs (Blockchain intelligence company)
- Ari Redbord (Global head of policy at TRM Labs)
7. Thematic Tags
cybersecurity, cryptocurrency, cyber-security, geopolitical instability, capital flight, blockchain analysis, financial systems, operational security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us