Iran’s Cyber Tactics Expand Globally Amid Ongoing Conflict, Targeting Civilians with Sophisticated Attacks
Published on: 2026-03-29
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: There are a lot more attacks happening that arent being reported Irans cyber response creeps across the globe
1. BLUF (Bottom Line Up Front)
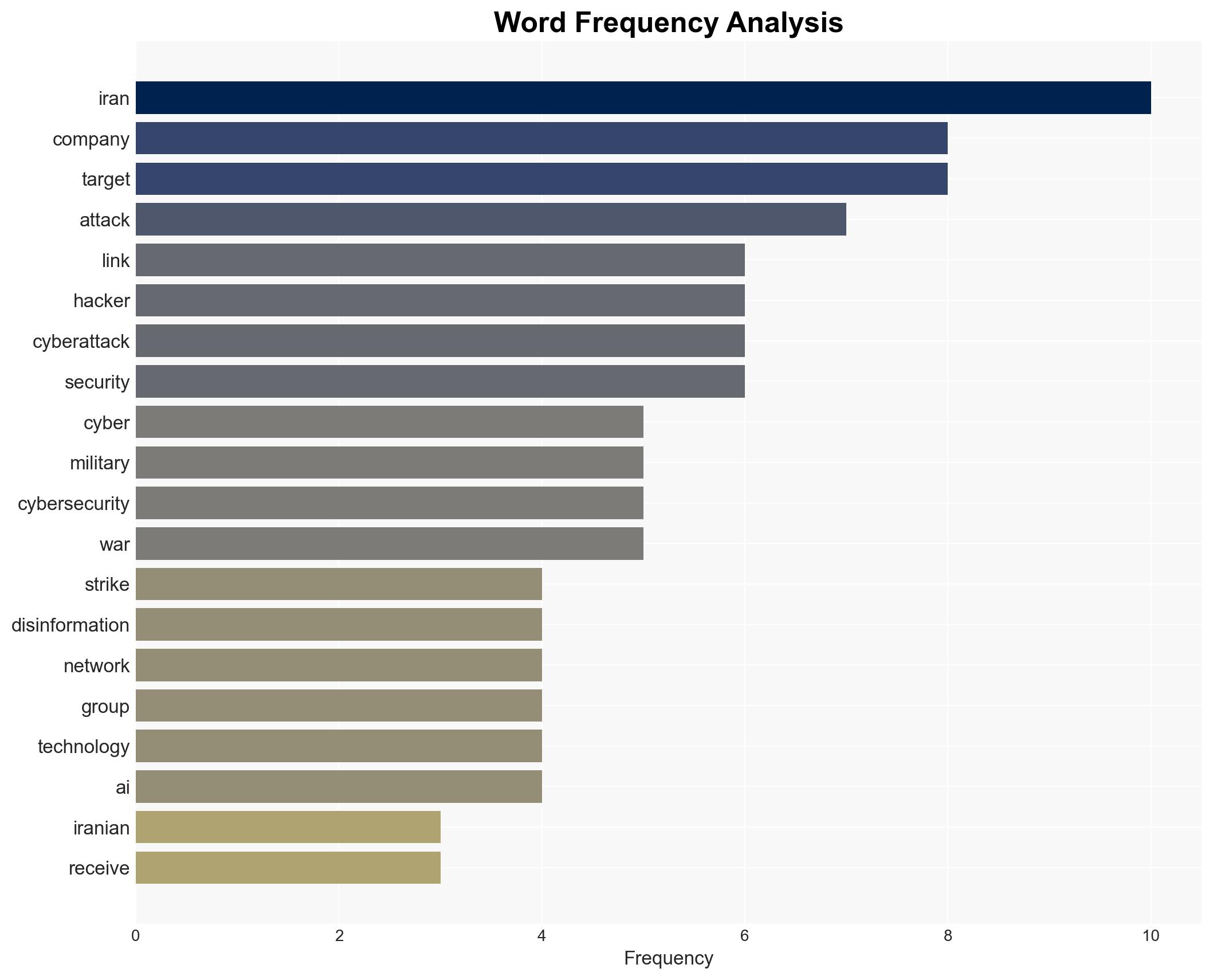
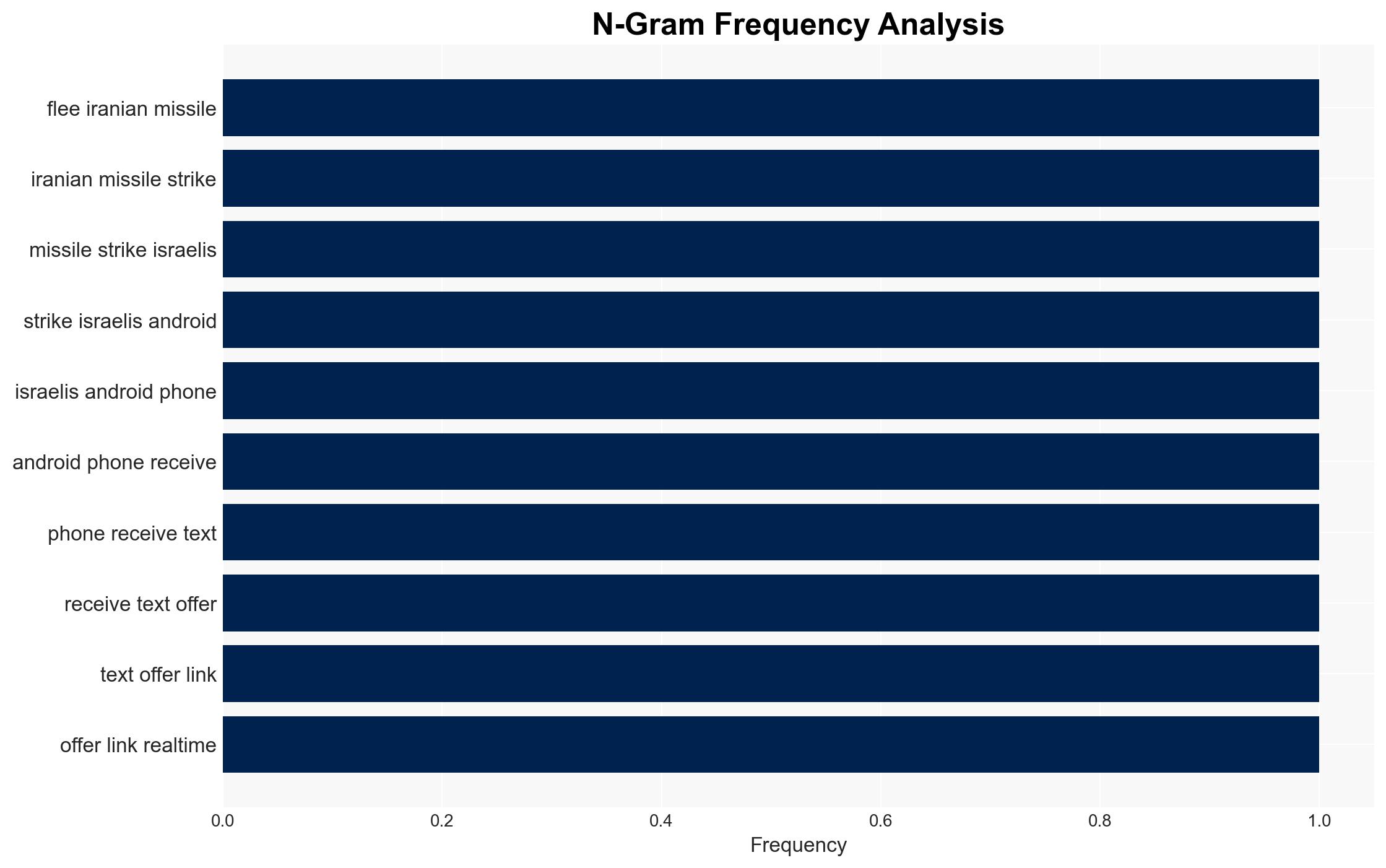
Iran’s cyber operations, characterized by sophisticated coordination and integration with physical attacks, are increasingly targeting U.S. and Israeli interests, as well as regional actors. These operations aim to exploit security vulnerabilities and create psychological impacts rather than cause direct physical damage. The most likely hypothesis is that Iran will continue to leverage cyber capabilities to offset military disadvantages. Overall confidence in this assessment is moderate due to the limited visibility into the full scope of cyber activities.
2. Competing Hypotheses
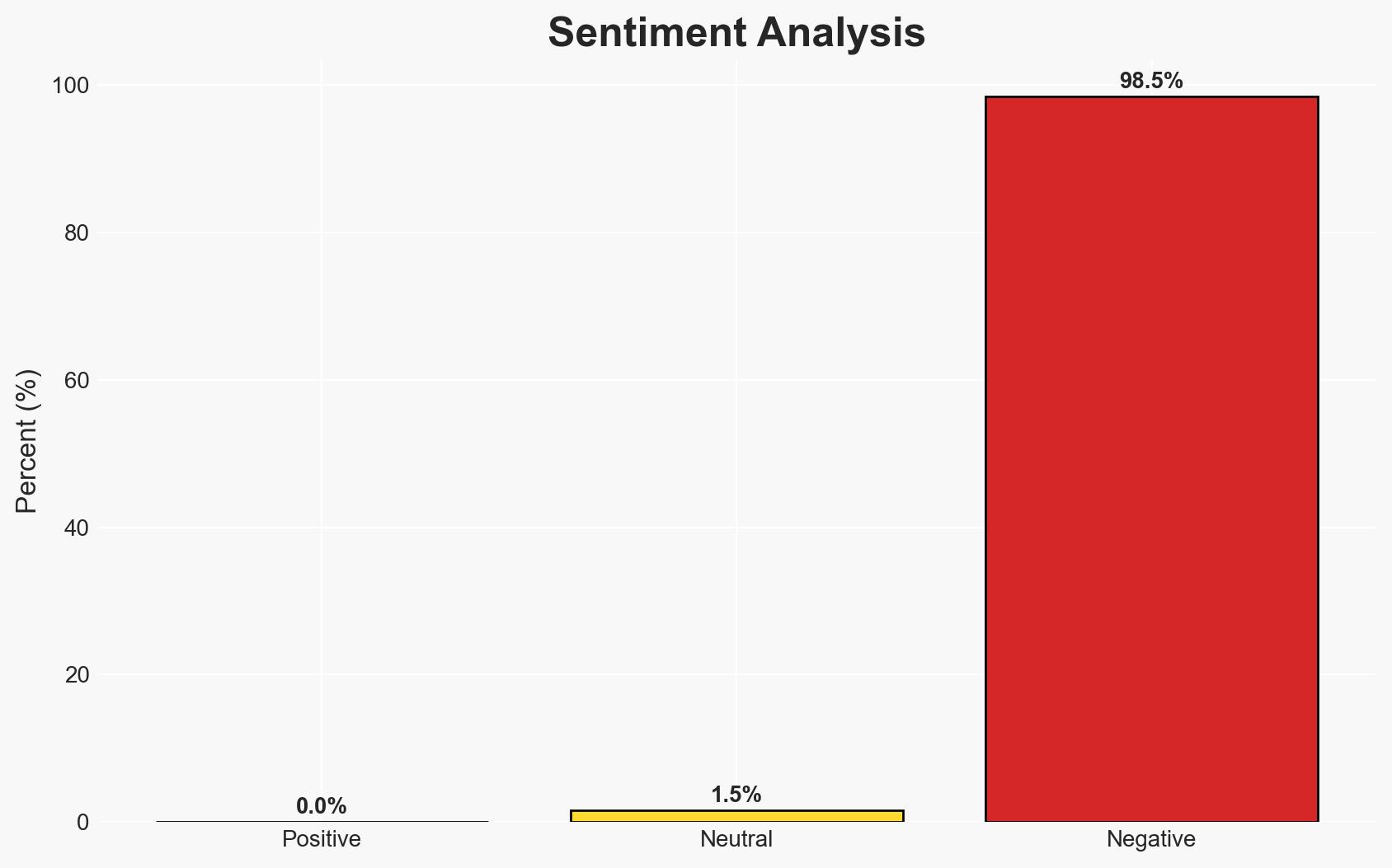
- Hypothesis A: Iran is using cyber operations primarily as a strategic tool to compensate for conventional military weaknesses. This is supported by the timing and coordination of cyber attacks with physical military actions and the focus on espionage and psychological impact rather than direct damage. Key uncertainties include the full extent of Iran’s cyber capabilities and the potential for escalation.
- Hypothesis B: Iran’s cyber activities are primarily aimed at boosting domestic and regional morale and undermining the confidence of adversaries, rather than achieving strategic military objectives. This is supported by the relatively minor damage caused by most attacks and the focus on high-profile but low-impact operations. Contradicting evidence includes the sophisticated nature of some attacks, suggesting strategic intent.
- Assessment: Hypothesis A is currently better supported due to the evidence of coordinated cyber-physical operations and the strategic benefits of cyber capabilities for Iran. Indicators that could shift this judgment include evidence of significant damage from cyber attacks or a shift in targeting patterns.
3. Key Assumptions and Red Flags
- Assumptions: Iran lacks the conventional military capability to challenge its adversaries directly; cyber operations are a cost-effective alternative; the primary goal is strategic advantage rather than immediate damage.
- Information Gaps: Detailed intelligence on the full scope of Iran’s cyber capabilities and the specific objectives of its cyber campaigns.
- Bias & Deception Risks: Potential overestimation of Iran’s cyber capabilities due to reliance on publicized attacks; possible deception in attributing attacks to Iran without definitive evidence.
4. Implications and Strategic Risks
The continuation of Iran’s cyber operations could lead to increased tensions and potential escalation in the region. These activities may also drive adversaries to enhance their cyber defenses and develop retaliatory capabilities.
- Political / Geopolitical: Potential for increased diplomatic tensions and retaliatory actions by affected states.
- Security / Counter-Terrorism: Heightened alertness and defensive postures among targeted nations, with possible impacts on military readiness.
- Cyber / Information Space: Increased investment in cybersecurity measures and potential for cyber arms race in the region.
- Economic / Social: Potential disruptions to businesses and critical infrastructure, leading to economic costs and social unrest.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of cyber activities linked to Iran, strengthen cybersecurity protocols, and engage in diplomatic efforts to de-escalate tensions.
- Medium-Term Posture (1–12 months): Develop resilience measures, foster international cybersecurity partnerships, and invest in cyber capability development.
- Scenario Outlook:
- Best: De-escalation through diplomatic channels, leading to reduced cyber activity.
- Worst: Significant cyber attack causing major disruption or damage, prompting military retaliation.
- Most-Likely: Continued low-level cyber operations with periodic escalations, maintaining pressure on adversaries.
6. Key Individuals and Entities
- Gil Messing, Chief of Staff at Check Point Research
- Michael Smith, Field Chief Technology Officer at DigiCert
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
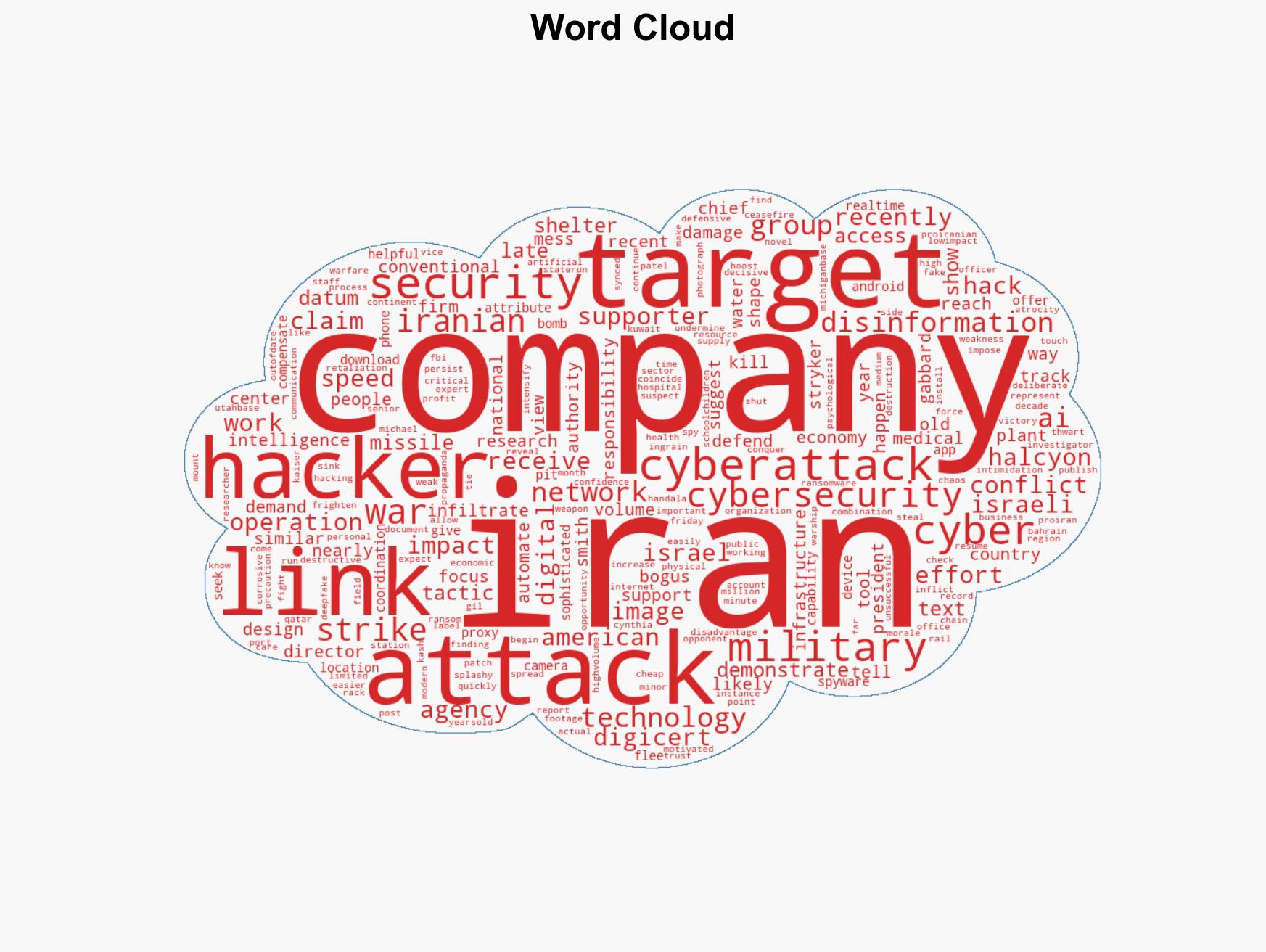
cybersecurity, cyber-espionage, Iran, cyber warfare, geopolitical tensions, digital conflict, intelligence analysis
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us