Iran’s IRGC Plans Attacks on Major US Tech Firms in Retaliation for Ongoing Conflict, Starting April 1
Published on: 2026-03-31
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Iran Threatens to Start Attacking Major US Tech Firms on April 1
1. BLUF (Bottom Line Up Front)
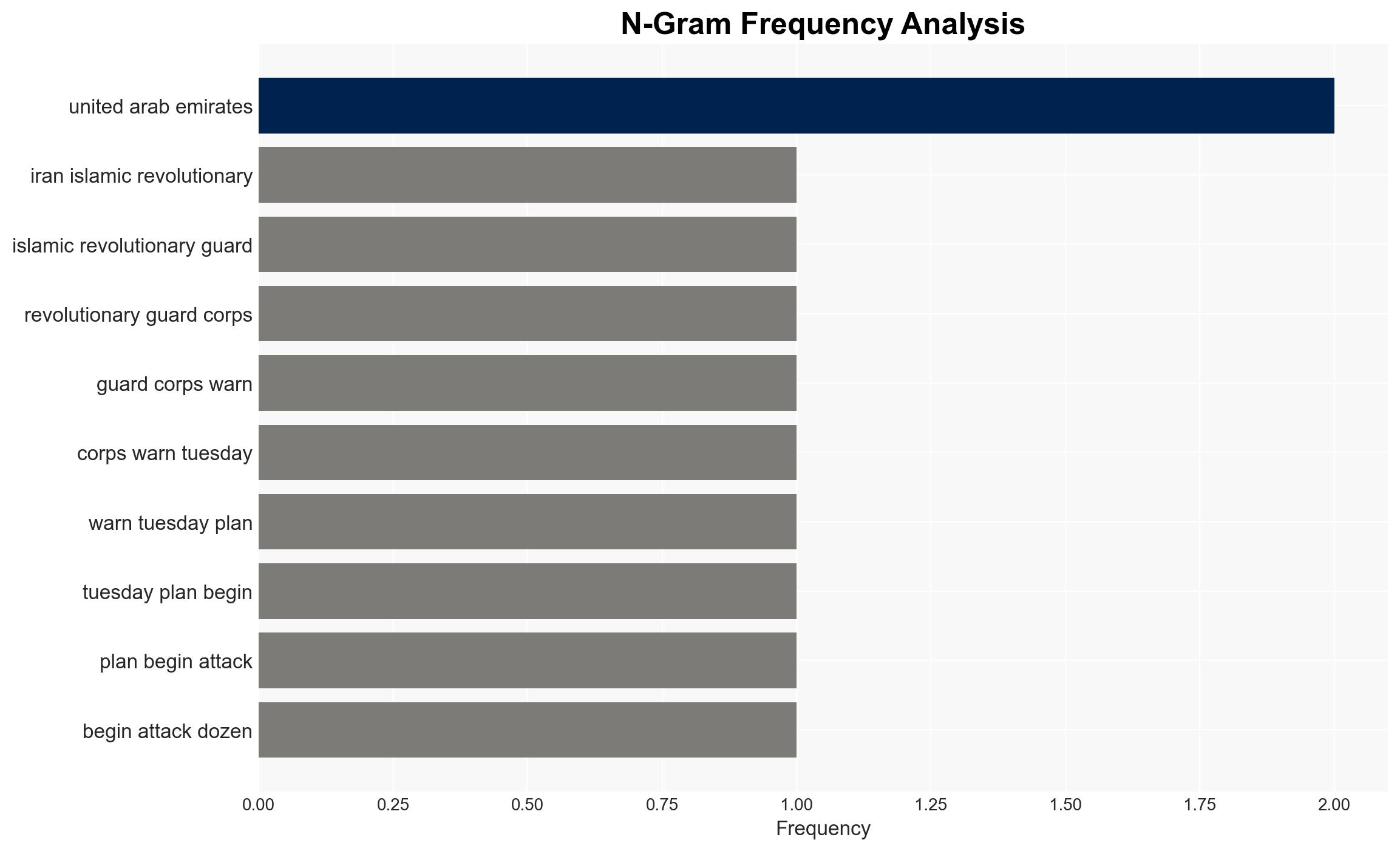
Iran’s Islamic Revolutionary Guard Corps (IRGC) has threatened to attack major US tech firms in the Middle East, potentially disrupting regional operations and escalating tensions. The most likely hypothesis is that these threats are intended to deter US and Israeli military actions by targeting commercial interests. This development affects US tech companies and regional stability, with a moderate confidence level in this assessment.
2. Competing Hypotheses
- Hypothesis A: The IRGC’s threats are a strategic move to deter further US-Israeli military actions by targeting commercial interests. This is supported by the IRGC’s history of using asymmetric tactics and the recent attacks on AWS data centers. Key uncertainties include the IRGC’s actual capability to execute such widespread attacks.
- Hypothesis B: The threats are primarily psychological operations aimed at creating fear and uncertainty among US companies and their regional partners, without a concrete plan for execution. This is supported by the lack of immediate response from targeted companies and the potential for exaggeration in the IRGC’s messaging.
- Assessment: Hypothesis A is currently better supported due to the IRGC’s previous actions and the specificity of the threats. Indicators that could shift this judgment include evidence of increased cyber capabilities or a lack of follow-through on the threats.
3. Key Assumptions and Red Flags
- Assumptions: The IRGC has the capability to carry out cyber and physical attacks on US tech firms; US tech firms are integral to US military operations; the IRGC’s threats are credible and not merely propaganda.
- Information Gaps: Detailed intelligence on the IRGC’s cyber capabilities and specific attack plans; the response plans of the targeted companies.
- Bias & Deception Risks: Potential overestimation of IRGC capabilities due to source bias; possible IRGC deception to mislead US and allied responses.
4. Implications and Strategic Risks
This development could lead to increased regional instability and impact US tech operations in the Middle East. The situation may evolve into broader geopolitical tensions if not managed carefully.
- Political / Geopolitical: Potential for escalation between Iran and the US/Israel, affecting diplomatic relations and regional alliances.
- Security / Counter-Terrorism: Heightened threat environment for US assets in the region, requiring increased security measures.
- Cyber / Information Space: Increased risk of cyber-attacks on US tech infrastructure, potentially disrupting services and data integrity.
- Economic / Social: Potential economic disruptions in the Gulf region, affecting investment and development in the tech sector.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of IRGC communications and cyber activities; coordinate with regional allies to secure tech infrastructure; issue advisories to US firms operating in the region.
- Medium-Term Posture (1–12 months): Develop resilience measures for tech infrastructure; strengthen partnerships with regional governments; invest in cyber defense capabilities.
- Scenario Outlook: Best: De-escalation through diplomatic engagement. Worst: Successful IRGC attacks causing significant disruption. Most-Likely: Continued threats with limited successful attacks, leading to increased security measures.
6. Key Individuals and Entities
- Islamic Revolutionary Guard Corps (IRGC)
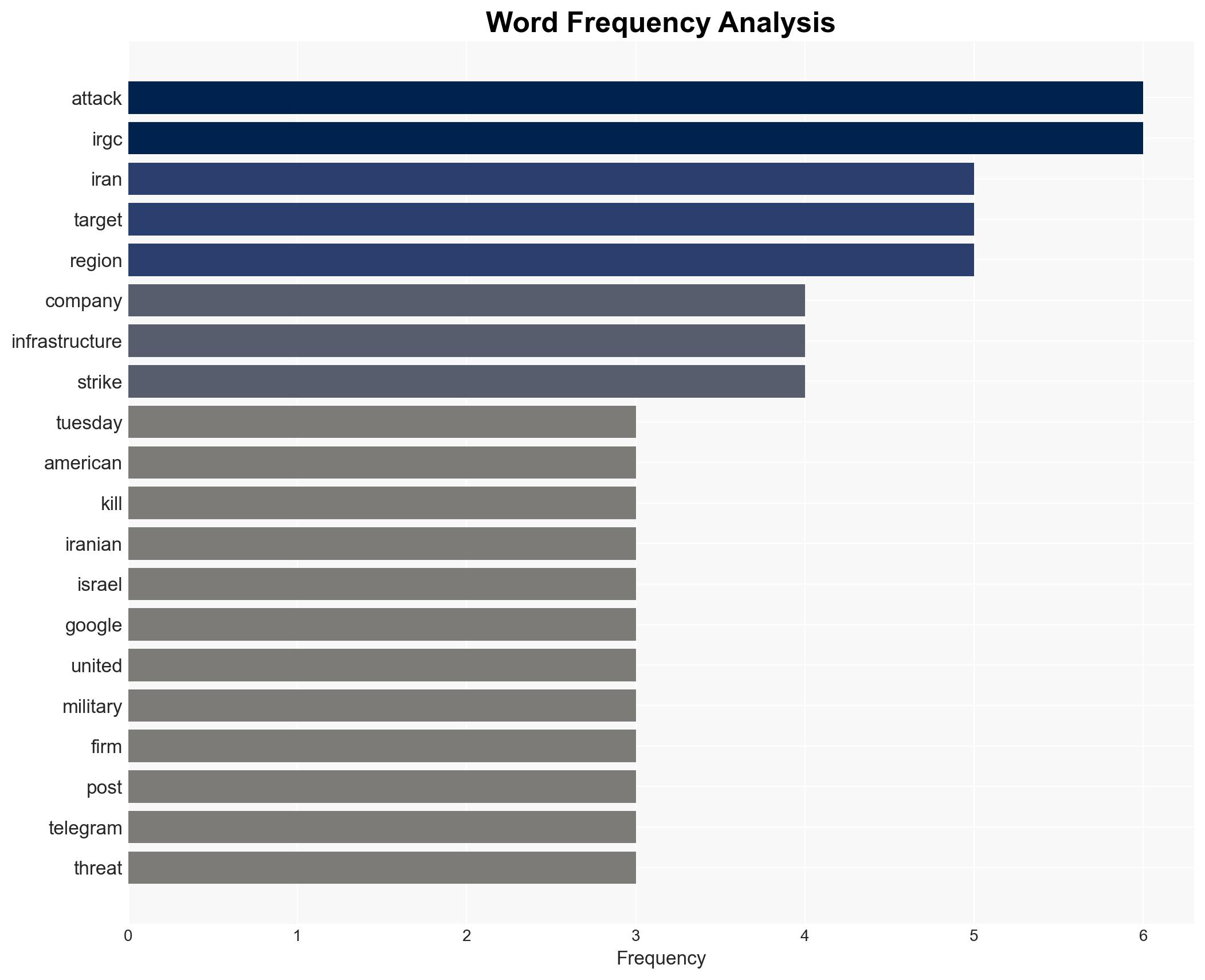
- US Tech Firms: Apple, Google, IBM, Intel, Microsoft, Tesla, Boeing
- Amazon Web Services
- Palantir
- US Central Command
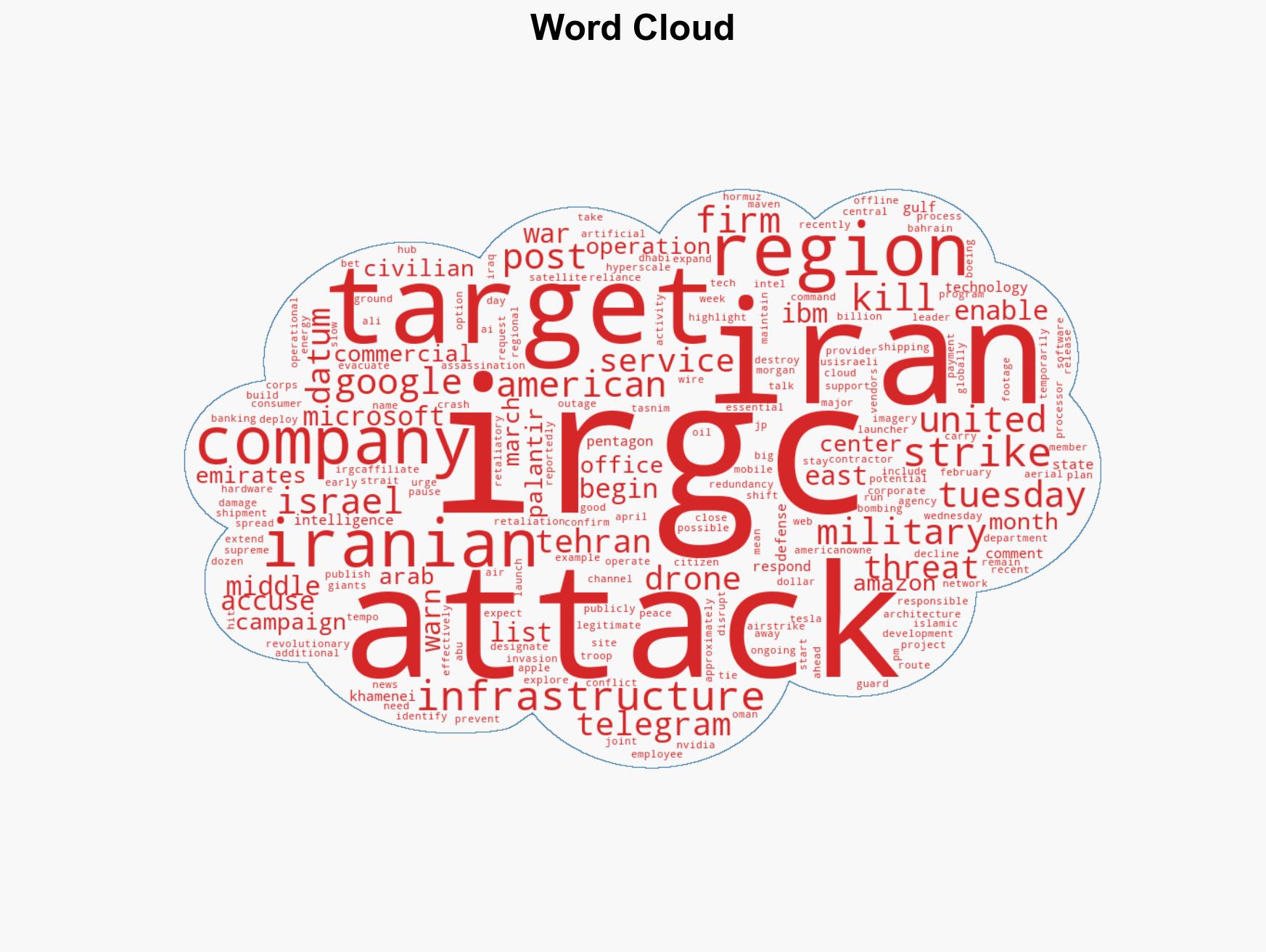
7. Thematic Tags
cybersecurity, cyber-security, Middle East, US-Iran relations, tech industry, geopolitical tensions, asymmetric warfare, regional stability
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us