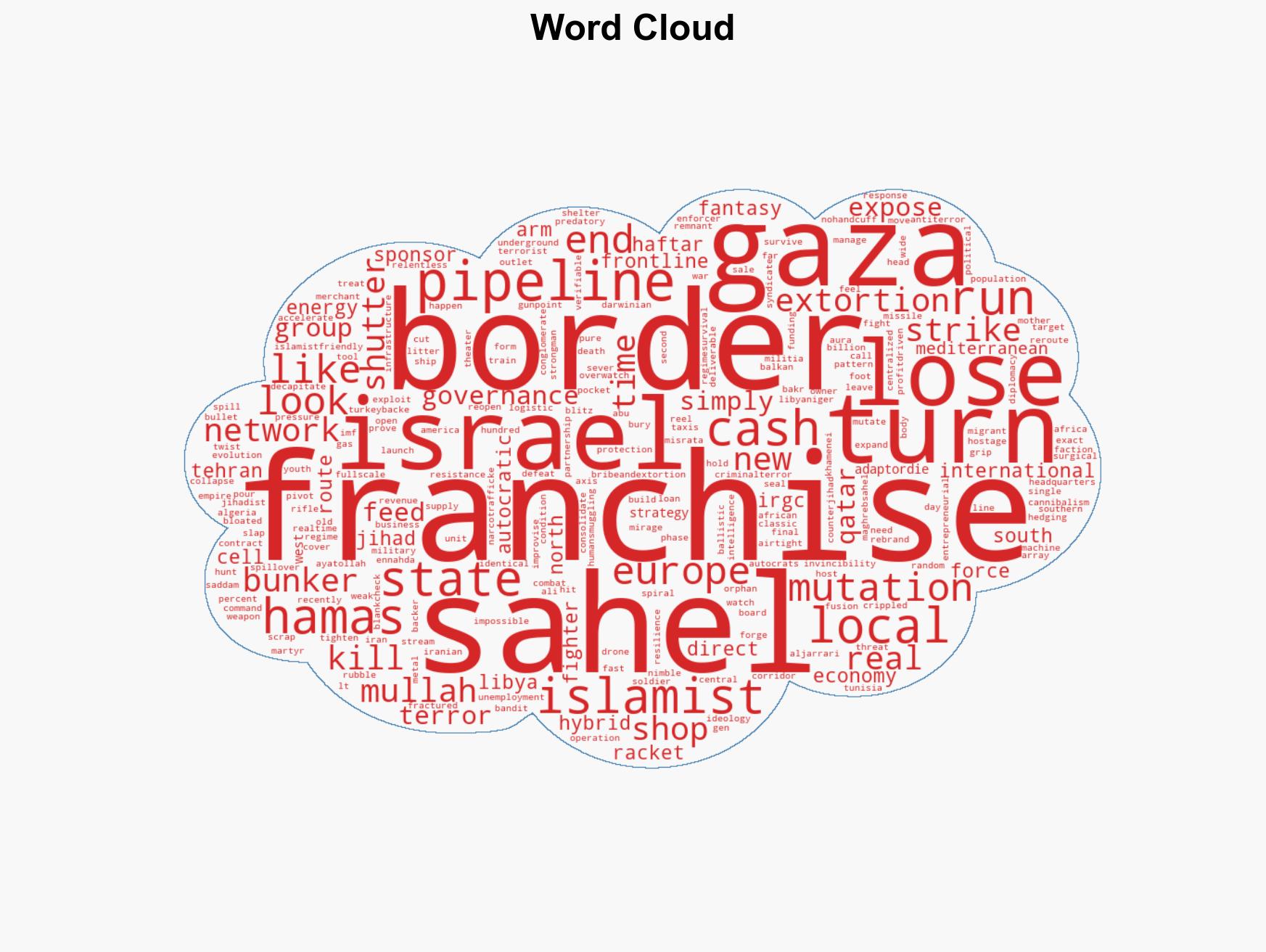
Islamist Networks Evolve Amidst Iran’s Collapse, Resorting to Predatory Tactics for Survival
Published on: 2026-03-08
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: The Islamist adapt-or-die strategy after Irans defeat
1. BLUF (Bottom Line Up Front)
The fragmentation of Iran’s influence has led to a rapid evolution of Islamist networks into decentralized, entrepreneurial entities. These groups are adapting by exploiting local vulnerabilities and engaging in criminal activities. This shift poses a significant threat to regional stability and European security, with moderate confidence in the assessment. Affected parties include North African states, European nations, and regional security forces.
2. Competing Hypotheses
- Hypothesis A: Islamist networks are primarily adapting to the loss of Iranian support by decentralizing and engaging in criminal activities to sustain operations. This is supported by evidence of extortion in Gaza and smuggling in the Sahel. However, there is uncertainty about the extent of coordination among these groups.
- Hypothesis B: The adaptation of Islamist networks is a temporary response, and they will eventually collapse without centralized support. This is contradicted by their demonstrated ability to exploit local opportunities and maintain operations independently.
- Assessment: Hypothesis A is currently better supported due to the observed adaptability and resilience of these networks. Indicators such as increased criminal activities and local partnerships could further support this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Islamist networks require external funding to sustain operations; local governments are unable or unwilling to effectively counter these groups; the loss of Iranian support is permanent.
- Information Gaps: Detailed intelligence on the internal dynamics and leadership structures of these decentralized networks; the extent of external support from other state or non-state actors.
- Bias & Deception Risks: Potential overestimation of the networks’ capabilities due to reliance on fragmented open-source reporting; possible deception by local actors exaggerating threats for external support.
4. Implications and Strategic Risks
The evolution of Islamist networks into decentralized entities could lead to increased regional instability and pose new security challenges for Europe. These developments may interact with broader geopolitical tensions and economic vulnerabilities.
- Political / Geopolitical: Increased pressure on European borders and energy supplies; potential for regional alliances to shift as states respond to new threats.
- Security / Counter-Terrorism: Enhanced threat environment with more unpredictable and localized terrorist activities; challenges in intelligence gathering and counter-terrorism operations.
- Cyber / Information Space: Potential for increased cyber operations targeting European infrastructure and information campaigns to exploit regional instability.
- Economic / Social: Strain on local economies due to criminal activities; potential for increased migration pressures on Europe.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance intelligence sharing among regional and European partners; increase monitoring of smuggling routes and financial flows.
- Medium-Term Posture (1–12 months): Develop resilience measures for critical infrastructure; strengthen partnerships with North African states to address root causes of instability.
- Scenario Outlook:
- Best: Effective regional cooperation leads to containment of threats, with improved stability.
- Worst: Escalation of criminal-terror activities destabilizes multiple regions, impacting European security.
- Most-Likely: Continued adaptation by Islamist networks, with localized threats persisting and requiring ongoing management.
6. Key Individuals and Entities
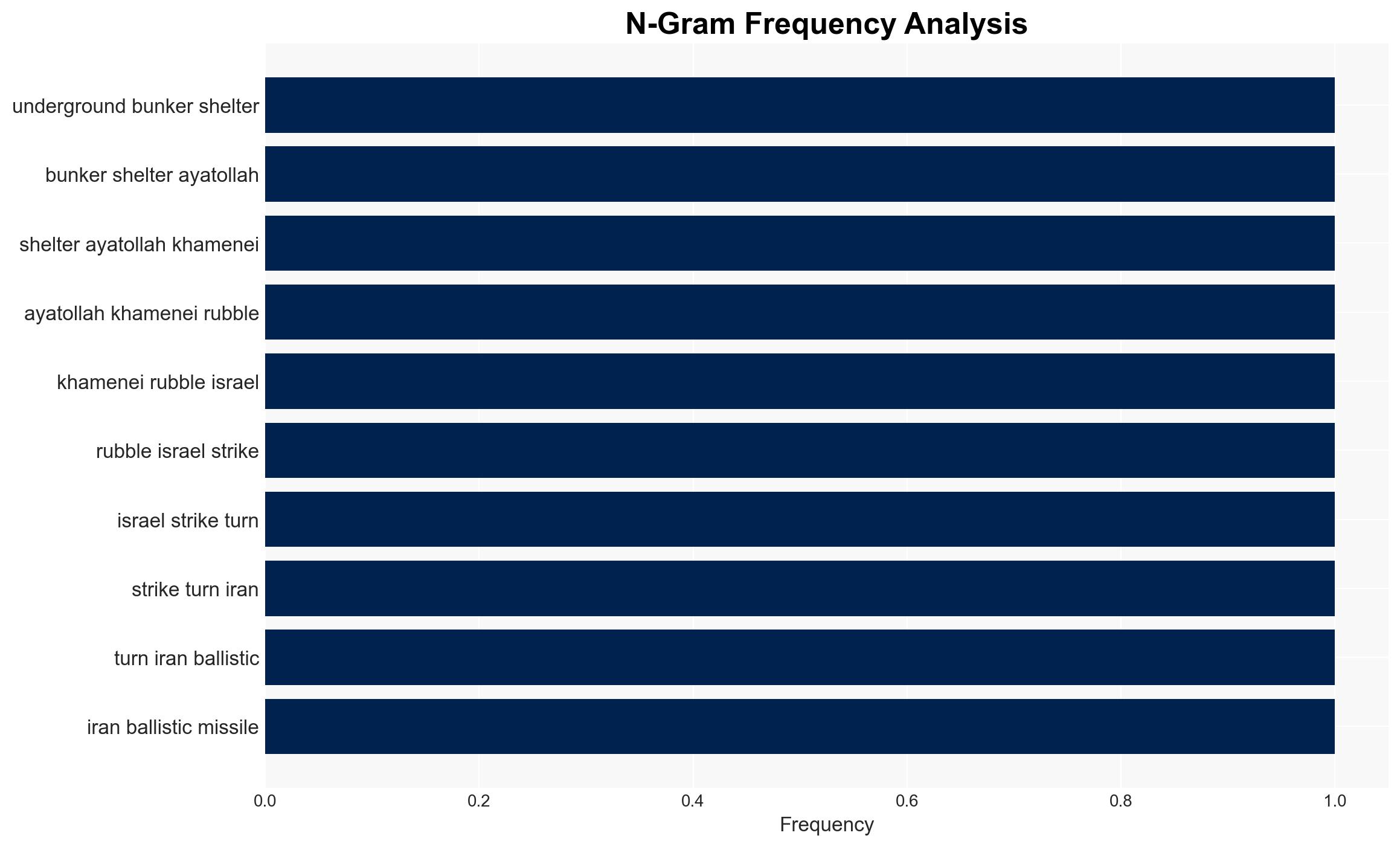
- Ayatollah Khamenei
- Lt. Gen. Saddam Haftar
- Abu Bakr Ali Al-Jarrari
- Not clearly identifiable from open sources in this snippet.
7. Thematic Tags
regional conflicts, counter-terrorism, regional stability, Islamist networks, criminal activities, European security, geopolitical dynamics, intelligence sharing
Structured Analytic Techniques Applied
- Causal Layered Analysis (CLA): Analyze events across surface happenings, systems, worldviews, and myths.
- Cross-Impact Simulation: Model ripple effects across neighboring states, conflicts, or economic dependencies.
- Scenario Generation: Explore divergent futures under varying assumptions to identify plausible paths.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Regional Conflicts Briefs ·
Daily Summary ·
Support us