Israeli Cyber Attack on Prayer App BadeSaba Distributes Anti-Regime Messages Amidst Conflict in Iran
Published on: 2026-03-02
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Popular prayer program becomes propaganda pusher after reported Israeli hack
1. BLUF (Bottom Line Up Front)
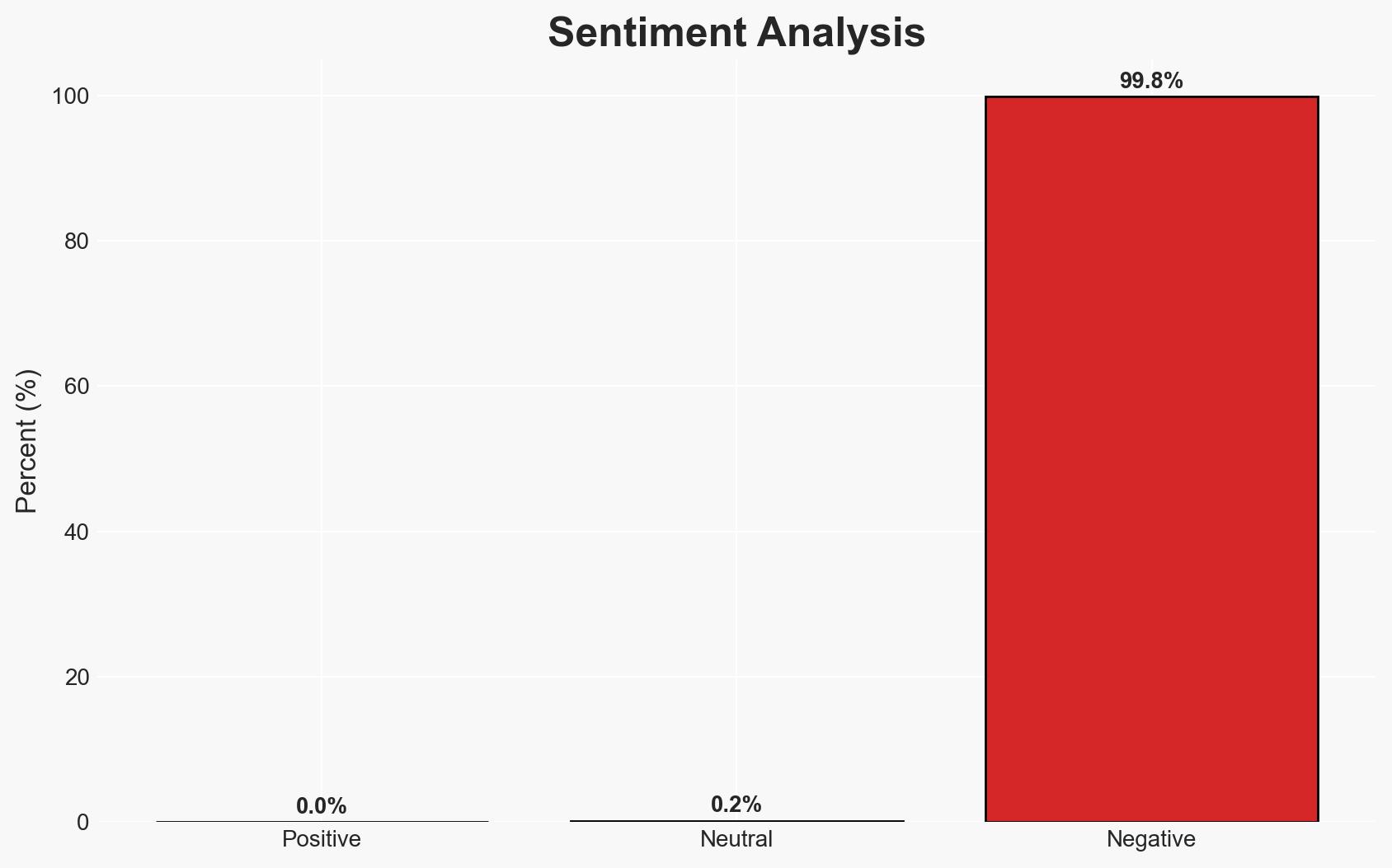
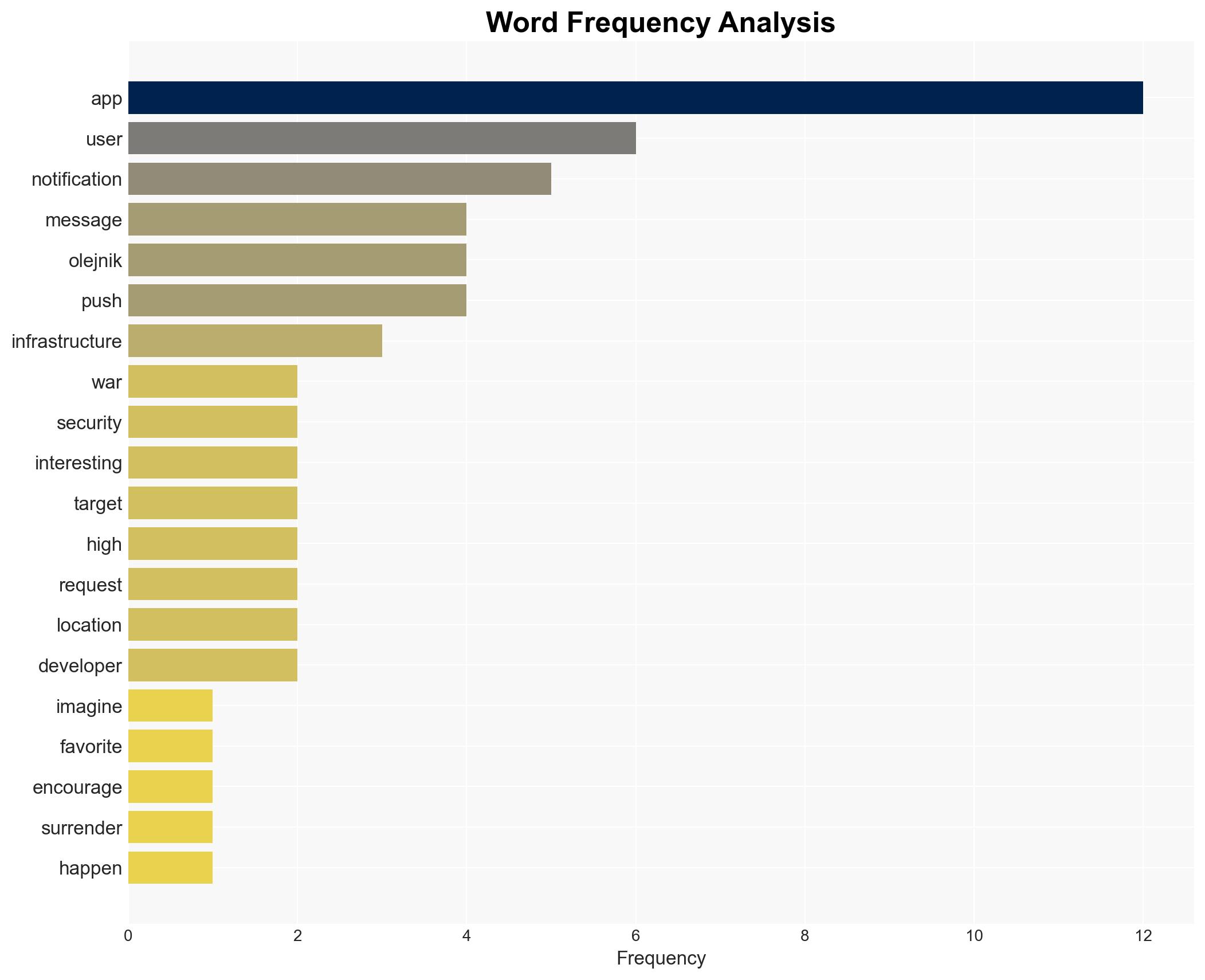
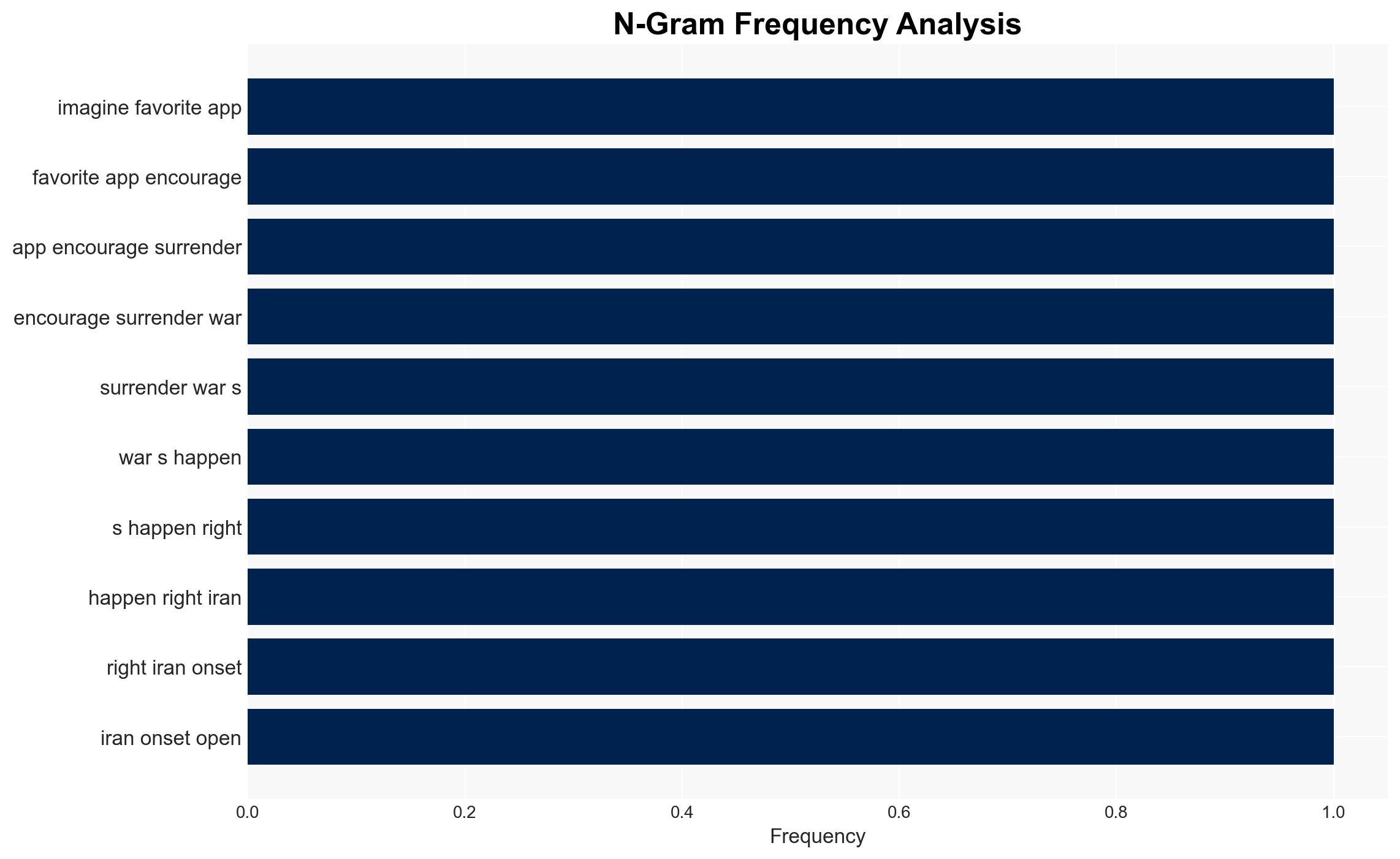
The BadeSaba app, reportedly hacked by Israeli operatives, is being used to disseminate propaganda aimed at Iranian military personnel. This incident highlights vulnerabilities in app notification systems, posing significant psychological and informational threats. The most likely hypothesis is that this is a strategic psychological operation by Israel, with moderate confidence due to limited direct evidence.
2. Competing Hypotheses
- Hypothesis A: The hack is a deliberate Israeli psychological operation targeting Iranian military morale. Supporting evidence includes the nature of the messages and the strategic targeting of a religious app with a pro-regime user base. However, uncertainties include lack of direct attribution and potential alternative actors.
- Hypothesis B: The hack is a false flag operation by a third party aiming to escalate tensions between Iran and Israel. This is supported by the potential for misattribution and the complex geopolitical landscape. Contradicting evidence includes the specific targeting of an app with a likely pro-regime user base, which aligns with Israeli interests.
- Assessment: Hypothesis A is currently better supported due to the alignment of the operation with known Israeli strategic interests and the specific targeting of a religiously inclined user base. Indicators that could shift this judgment include credible claims of responsibility from other actors or technical evidence of a different origin.
3. Key Assumptions and Red Flags
- Assumptions: The app’s user base is predominantly pro-regime; Israel has the capability and intent to conduct such operations; the messages were indeed sent via the app’s infrastructure.
- Information Gaps: Technical forensic evidence linking the hack to Israeli actors; confirmation of the app’s user demographics and their response to the messages.
- Bias & Deception Risks: Potential for confirmation bias in attributing the hack to Israel; risk of manipulated evidence or false claims by involved parties.
4. Implications and Strategic Risks
This development could exacerbate tensions between Iran and Israel, potentially leading to retaliatory actions. It underscores the vulnerability of digital platforms in psychological operations.
- Political / Geopolitical: Increased hostility between Iran and Israel, potential for diplomatic fallout or military escalation.
- Security / Counter-Terrorism: Heightened alertness in Iranian military and security circles, potential for internal dissent.
- Cyber / Information Space: Demonstrates the strategic use of app infrastructure in psychological operations, highlighting a need for improved cybersecurity measures.
- Economic / Social: Potential for increased social unrest in Iran if the operation succeeds in sowing dissent within the military.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Monitor app infrastructure for further breaches, engage in diplomatic channels to de-escalate tensions, and issue public advisories on app security.
- Medium-Term Posture (1–12 months): Develop resilience measures for app security, enhance partnerships with tech firms for better threat intelligence, and invest in counter-propaganda capabilities.
- Scenario Outlook:
- Best: De-escalation through diplomatic engagement, leading to improved cybersecurity collaborations.
- Worst: Escalation to military conflict, widespread distrust in digital communications.
- Most-Likely: Continued cyber and psychological operations with periodic escalations, requiring ongoing vigilance and response.
6. Key Individuals and Entities
- Hamid Kashfi, security researcher and DarkCell founder
- Lukasz Olejnik, independent consultant and author
- BadeSaba app developers (Not clearly identifiable from open sources in this snippet)
7. Thematic Tags
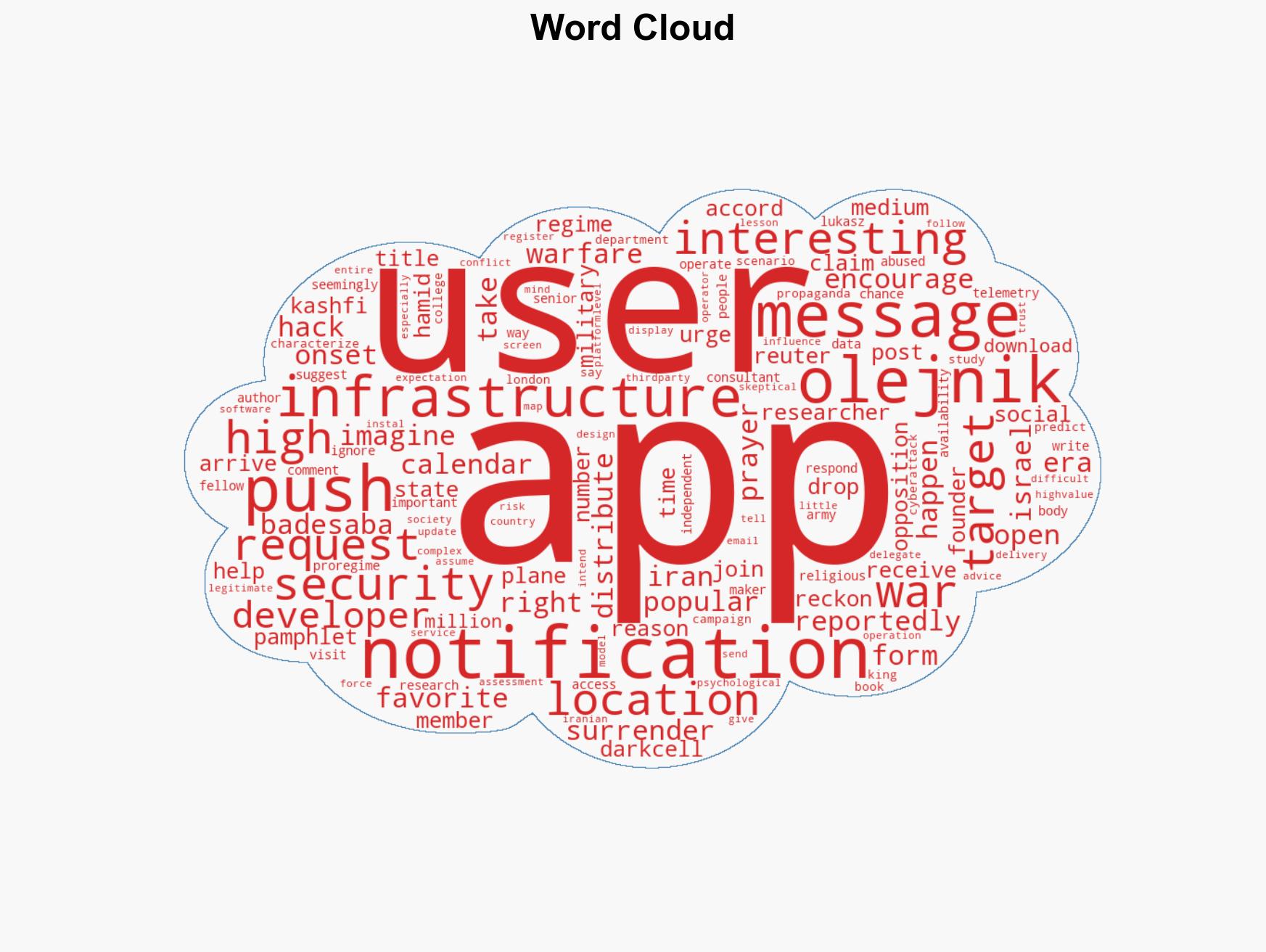
cybersecurity, cyber-operations, psychological-warfare, Iran-Israel relations, app-security, digital-infrastructure, propaganda, military-morale
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Forecast futures under uncertainty via probabilistic logic.
- Narrative Pattern Analysis: Deconstruct and track propaganda or influence narratives.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us