Ivanti VPN customers targeted via unrecognized RCE vulnerability CVE-2025-22457 – Help Net Security
Published on: 2025-04-03
Intelligence Report: Ivanti VPN Customers Targeted via Unrecognized RCE Vulnerability CVE-2025-22457 – Help Net Security
1. BLUF (Bottom Line Up Front)
An unrecognized remote code execution (RCE) vulnerability, CVE-2025-22457, has been identified in Ivanti VPN products, exploited by a suspected Chinese APT group. This vulnerability poses significant risks to organizations using Ivanti Connect Secure and Pulse Connect Secure appliances. Immediate action is required to mitigate potential threats and secure vulnerable systems.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
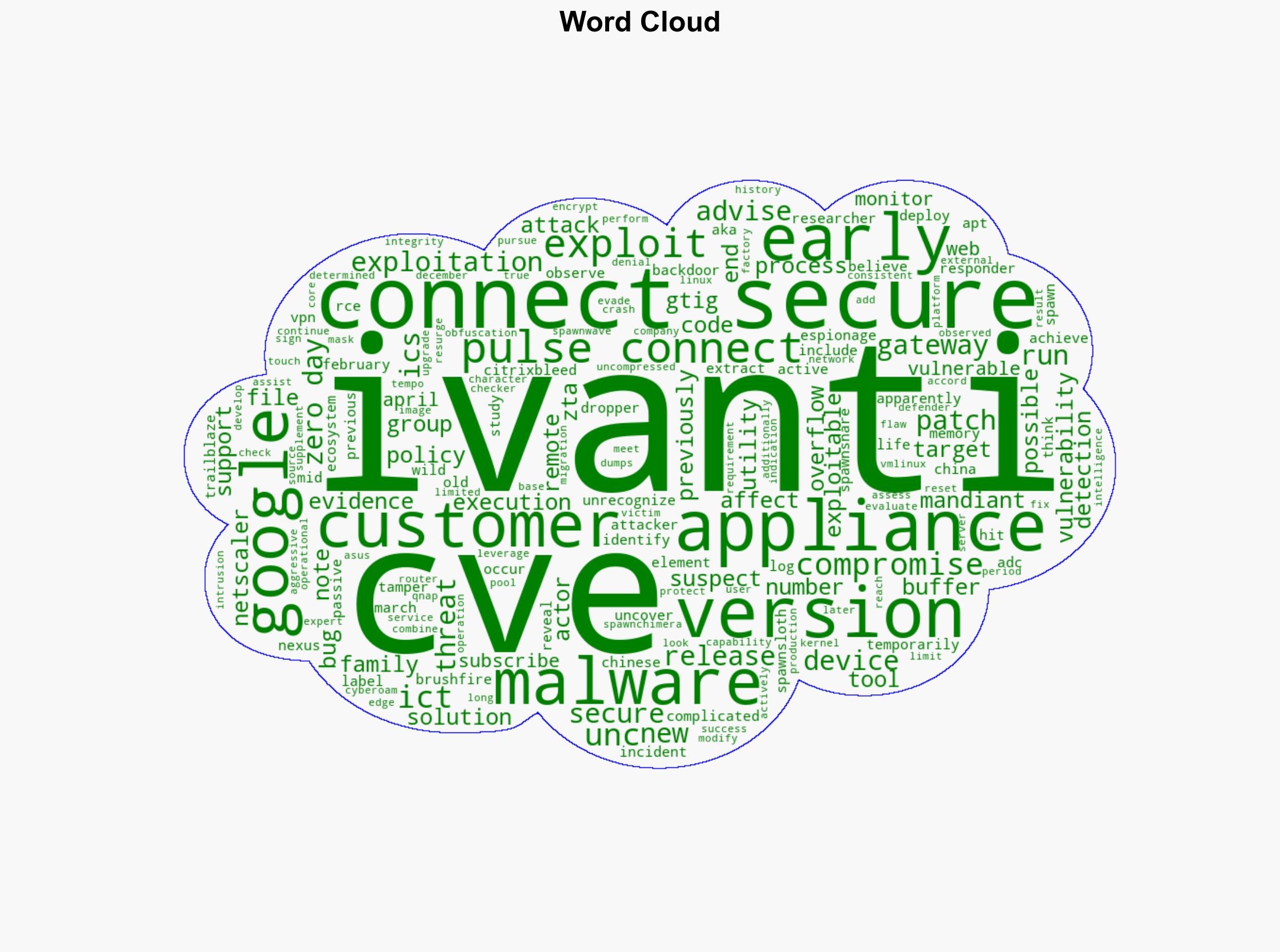
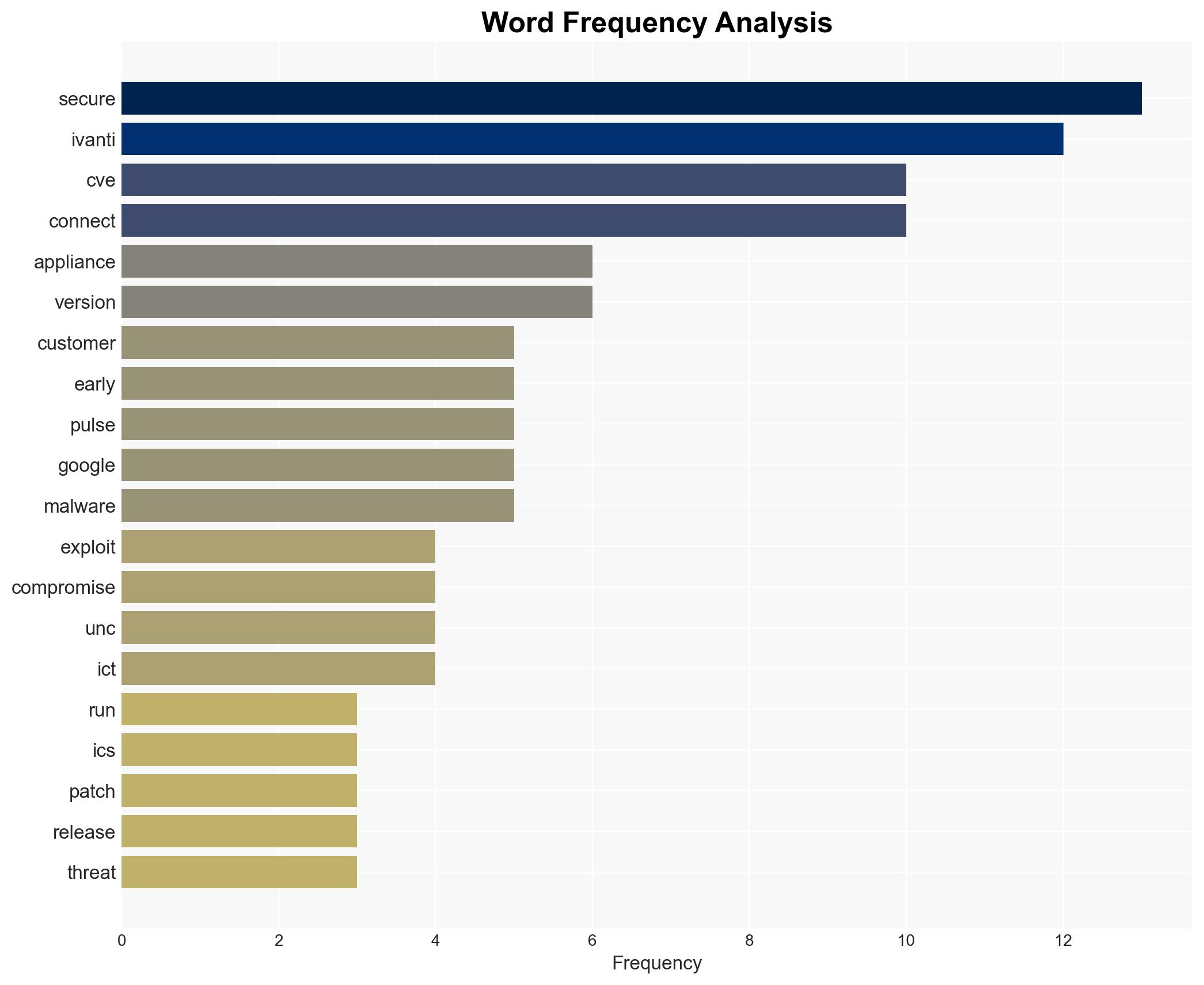
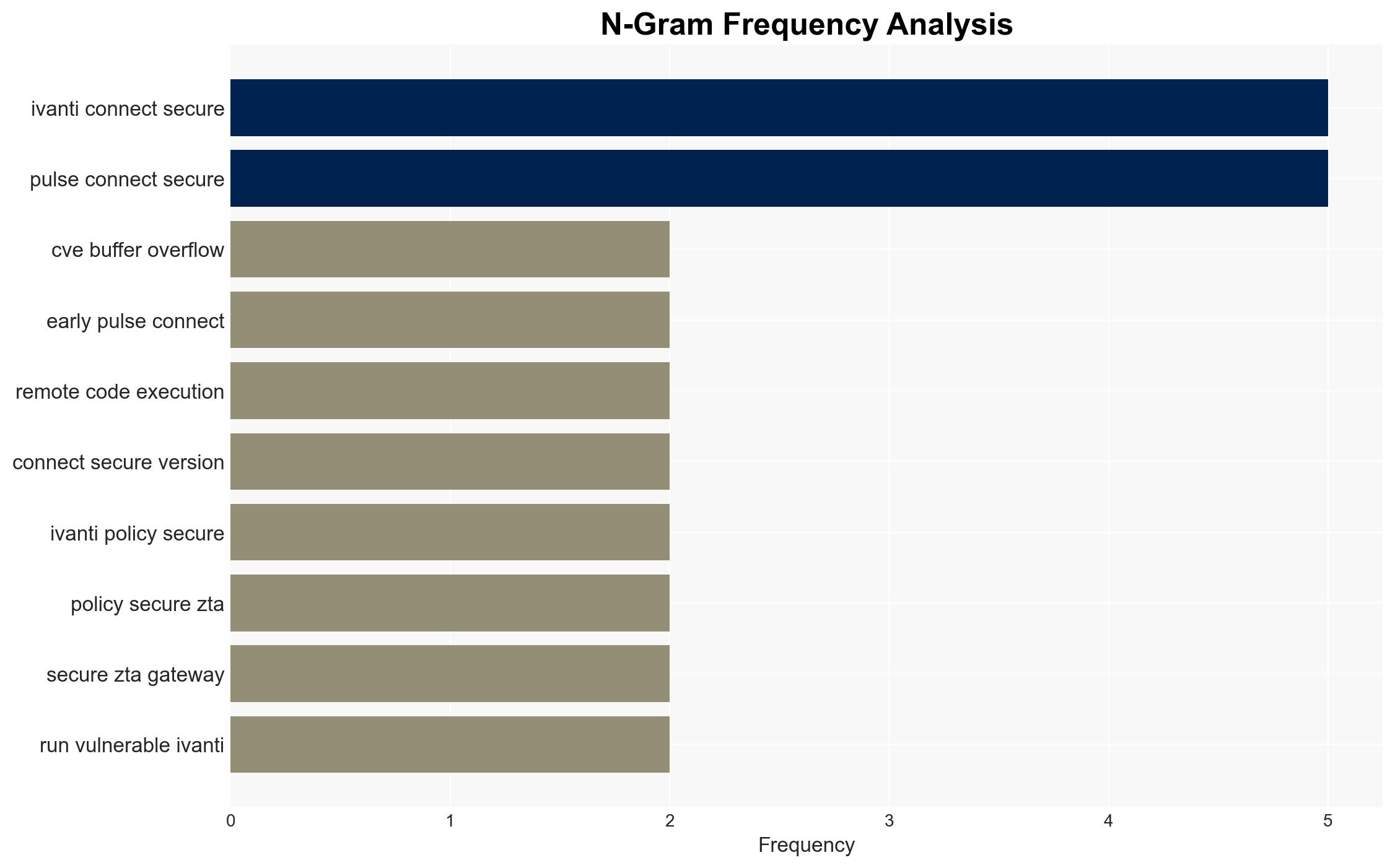
The vulnerability, CVE-2025-22457, is a buffer overflow bug that was previously thought non-exploitable. It has been exploited to compromise Ivanti Connect Secure appliances. The threat actor, suspected to have a nexus with China, has been identified as using complex processes to achieve remote code execution. Mandiant and Google researchers have revealed active exploitation in the wild, with the attackers deploying a new malware family, including Trailblaze and Brushfire. The exploitation has been ongoing since mid-March, with attackers leveraging obfuscation techniques to mask their operations.
3. Implications and Strategic Risks
The exploitation of CVE-2025-22457 presents significant risks to national security, regional stability, and economic interests. The vulnerability affects critical infrastructure, potentially allowing unauthorized access to sensitive data and systems. The continued exploitation by a sophisticated threat actor increases the likelihood of widespread disruption and data breaches.
4. Recommendations and Outlook
Recommendations:
- Organizations using Ivanti Connect Secure and Pulse Connect Secure should immediately upgrade to the latest supported versions to mitigate the vulnerability.
- Implement enhanced monitoring and anomaly detection to identify potential compromises.
- Consider regulatory measures to enforce timely patch management and vulnerability disclosure.
Outlook:
In the best-case scenario, rapid patch deployment and enhanced security measures will mitigate the threat. In the worst-case scenario, continued exploitation could lead to significant data breaches and operational disruptions. The most likely outcome involves a combination of successful mitigations and ongoing targeted attacks by the threat actor.
5. Key Individuals and Entities
The report mentions significant individuals and organizations involved in the analysis and response to the vulnerability. These include Mandiant and Google researchers, who have provided critical insights into the exploitation patterns and threat actor activities.