Joint Task Force neutralizes over 20 ISWAP insurgents during coordinated attack in Yobe State
Published on: 2026-03-13
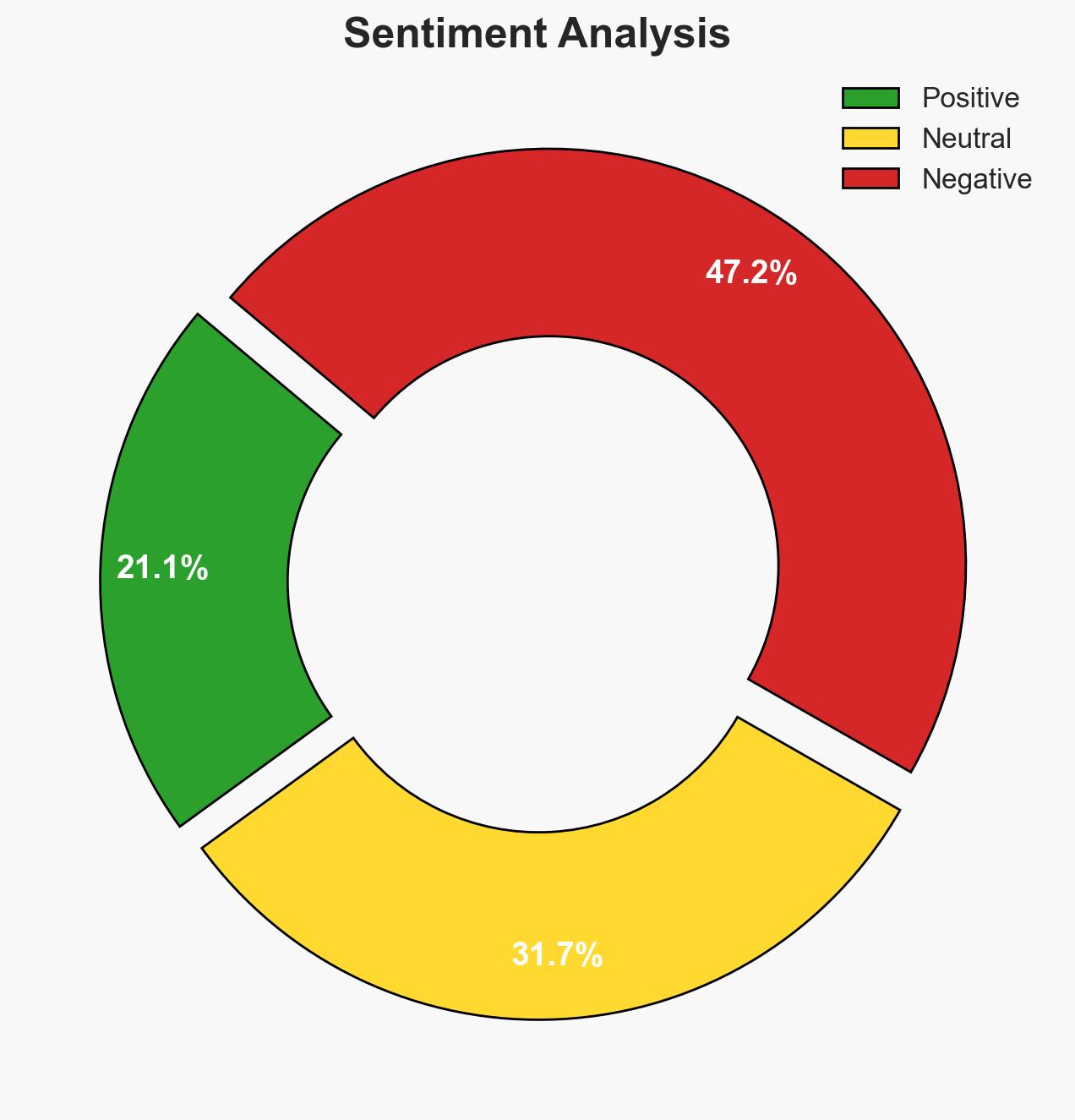
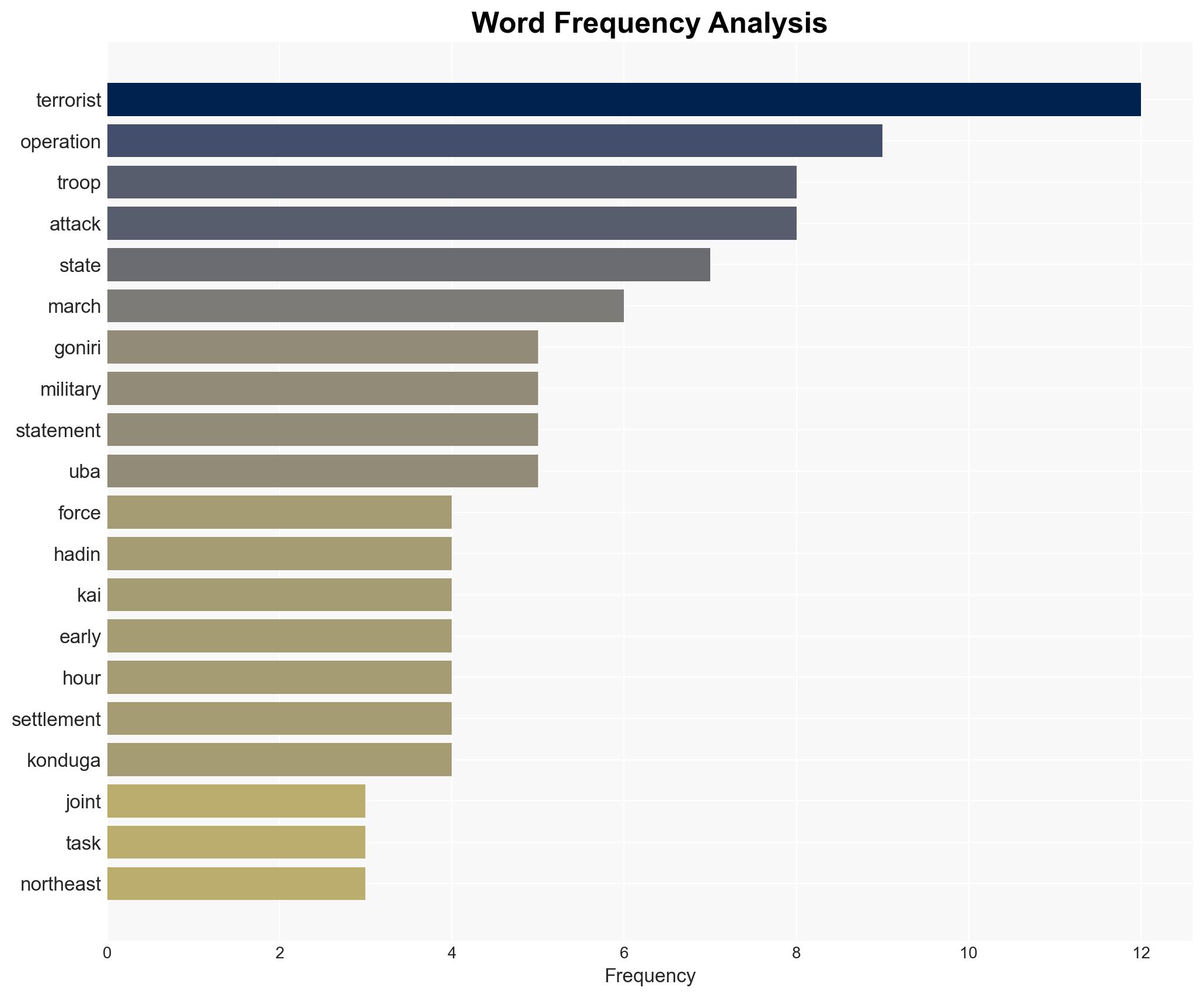
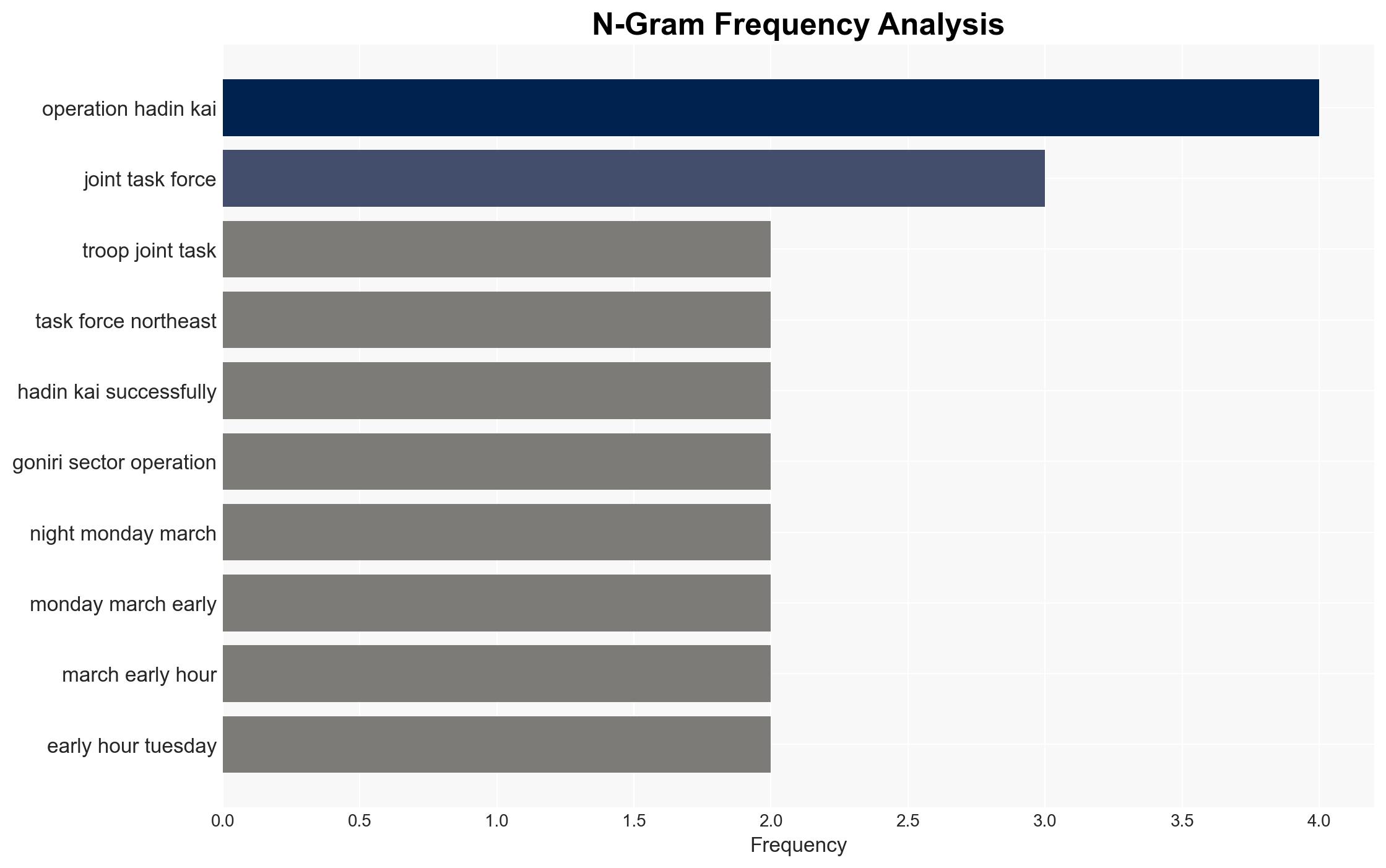
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Troops kill over 20 insurgents in Yobe ISWAP attack
1. BLUF (Bottom Line Up Front)
The Joint Task Force under Operation Hadin Kai successfully repelled an ISWAP attack in Yobe State, resulting in over 20 insurgent casualties. This development underscores the ongoing threat posed by ISWAP in the region and highlights the effectiveness of current military operations. The overall confidence level in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The attack was a strategic attempt by ISWAP to regain territorial control and demonstrate operational capability. Supporting evidence includes the coordinated nature of the assault and the involvement of a senior commander. Contradicting evidence is the rapid and effective military response, suggesting ISWAP’s capabilities may be overstated.
- Hypothesis B: The attack was an opportunistic strike by ISWAP to exploit perceived vulnerabilities in military defenses. Supporting evidence includes the timing and multi-directional approach. However, the presence of surveillance and rapid reinforcement contradicts this, indicating preparedness by the military.
- Assessment: Hypothesis A is currently better supported due to the structured nature of the attack and the involvement of a high-ranking insurgent leader, indicating a strategic intent. Indicators such as increased frequency of attacks or changes in ISWAP leadership could shift this judgment.
3. Key Assumptions and Red Flags
- Assumptions: ISWAP retains operational capability in the region; military intelligence and surveillance are reliable; local support for ISWAP is limited.
- Information Gaps: Detailed intelligence on ISWAP’s current strength and recruitment levels; local civilian sentiment towards ISWAP and military operations.
- Bias & Deception Risks: Potential bias in military reporting to emphasize success; risk of ISWAP misinformation campaigns to exaggerate their capabilities.
4. Implications and Strategic Risks
This development could lead to increased military engagements in the region, affecting stability and security dynamics. The ongoing threat from ISWAP necessitates sustained military vigilance and strategic planning.
- Political / Geopolitical: Potential for increased regional cooperation against ISWAP; risk of political pressure on military operations.
- Security / Counter-Terrorism: Possible escalation in insurgent attacks; need for enhanced intelligence and surveillance capabilities.
- Cyber / Information Space: ISWAP may leverage digital platforms for propaganda; importance of countering misinformation.
- Economic / Social: Continued instability could deter investment and development; risk of displacement and humanitarian challenges.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance surveillance and intelligence-sharing; conduct community engagement to counter ISWAP influence.
- Medium-Term Posture (1–12 months): Strengthen regional military alliances; invest in counter-insurgency training and technology.
- Scenario Outlook: Best: ISWAP capabilities are significantly degraded; Worst: ISWAP regains strength and expands operations; Most-Likely: Continued sporadic attacks with military maintaining control. Triggers include changes in ISWAP leadership or regional alliances.
6. Key Individuals and Entities
- Abu Yusu, Munzir of Dursula (deceased ISWAP commander)
- Lt Col Sani Uba, Media Information Officer, Joint Task Force
- Operation Hadin Kai, Joint Task Force, North-East
7. Thematic Tags
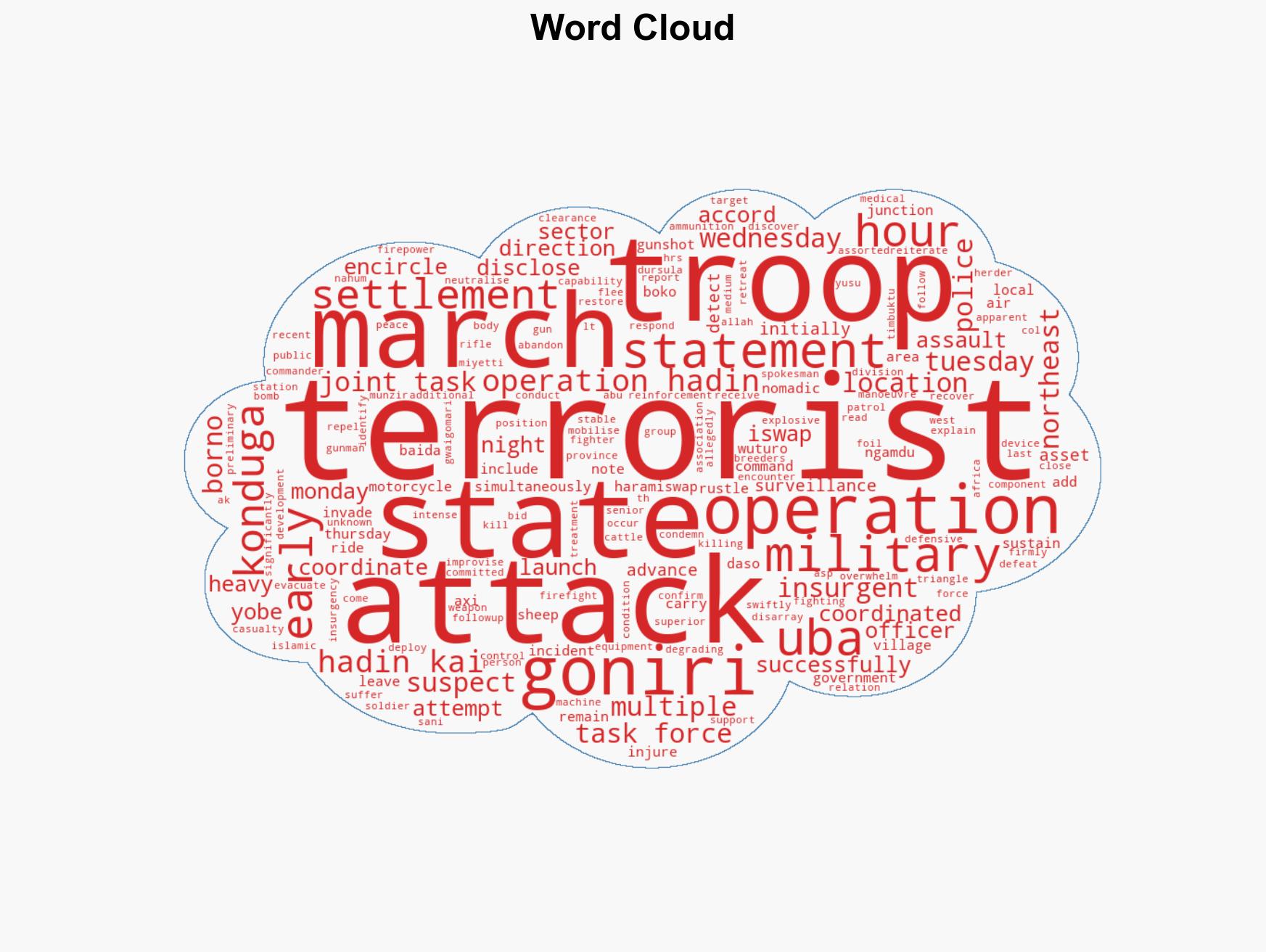
Counter-Terrorism, ISWAP, military operations, regional security, intelligence, insurgency, Yobe State
Structured Analytic Techniques Applied
- ACH 2.0: Reconstruct likely threat actor intentions via hypothesis testing and structured refutation.
- Indicators Development: Track radicalization signals and propaganda patterns to anticipate operational planning.
- Narrative Pattern Analysis: Analyze spread/adaptation of ideological narratives for recruitment/incitement signals.
Explore more:
Counter-Terrorism Briefs ·
Daily Summary ·
Support us