Kaspersky Refutes Links Between Coruna iPhone Exploit Kit and Alleged NSA Operations
Published on: 2026-03-04
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Kaspersky dismisses claims Coruna iPhone exploit kit is connected to NSA-linked operation
1. BLUF (Bottom Line Up Front)
The Coruna iPhone exploit kit’s origins remain contested, with Kaspersky disputing claims of NSA involvement. The most likely hypothesis is that Coruna is a product of a complex, multi-actor environment involving both state and non-state actors. This affects international cybersecurity dynamics, particularly between the US, Russia, and China. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
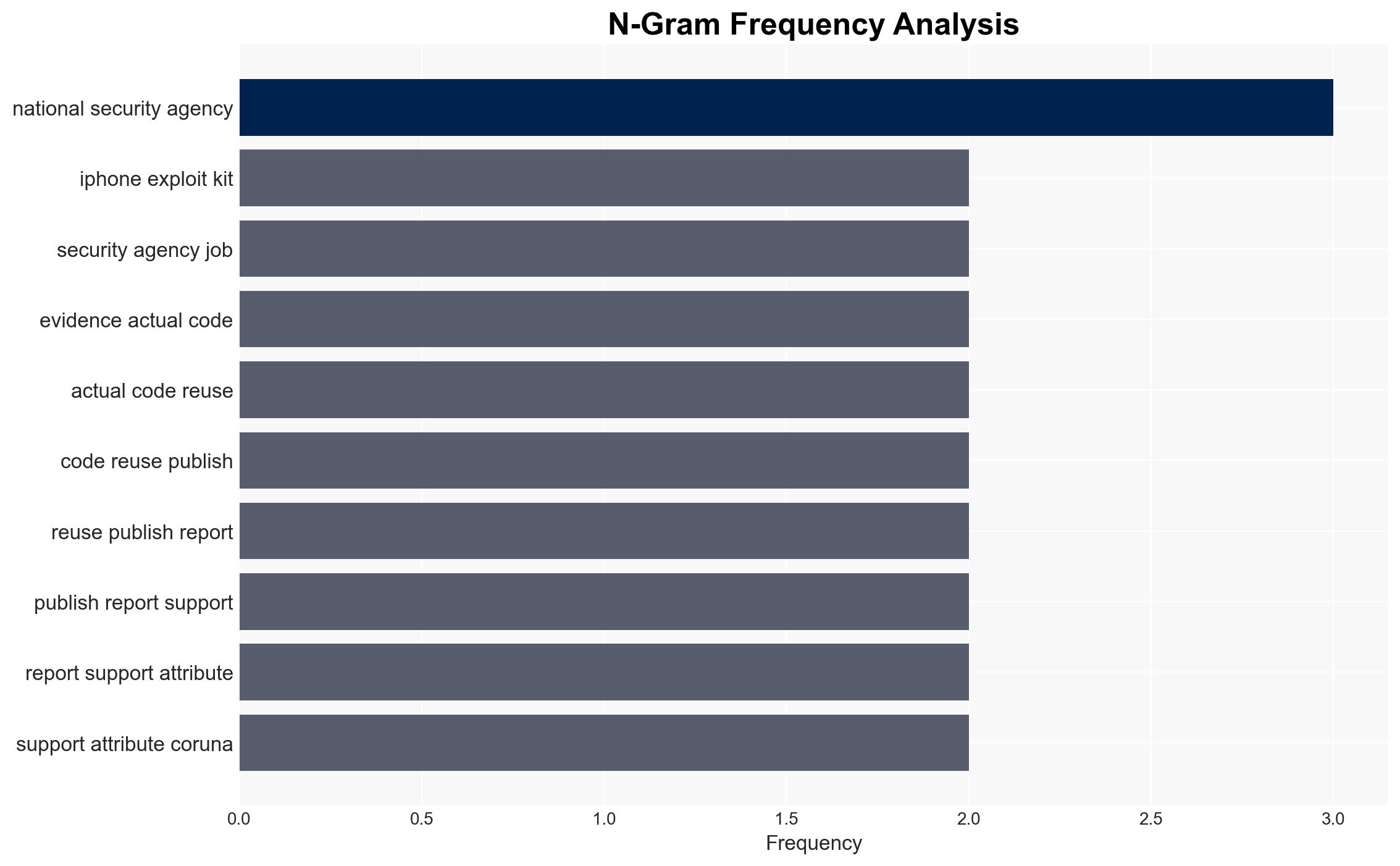
- Hypothesis A: Coruna was developed by the NSA or a US-affiliated entity. This is supported by the sophistication of the exploit and similarities to known US cyber tools. However, Kaspersky’s analysis finds no direct code reuse, creating uncertainty.
- Hypothesis B: Coruna is the result of a broader market for sophisticated cyber tools, involving multiple actors, including state-sponsored and commercial entities. This is supported by the diversity of users and targets, as well as the lack of direct evidence linking it to the NSA.
- Assessment: Hypothesis B is currently better supported due to the lack of conclusive evidence directly linking Coruna to the NSA and the observed use by various groups. Key indicators that could shift this judgment include new evidence of code reuse or direct attribution to a specific state actor.
3. Key Assumptions and Red Flags
- Assumptions: The analysis assumes that Kaspersky’s technical assessments are accurate and unbiased, that the market for zero-days is active and diverse, and that GTIG’s findings are comprehensive.
- Information Gaps: Detailed technical analysis of Coruna’s code, comprehensive attribution data, and insights into the exploit’s distribution channels are missing.
- Bias & Deception Risks: Potential bias in Kaspersky’s dismissal due to geopolitical interests; risk of deception in attributing the exploit to a specific actor without conclusive evidence.
4. Implications and Strategic Risks
The Coruna exploit kit’s development and deployment could exacerbate tensions among major cyber powers and influence global cybersecurity policies.
- Political / Geopolitical: Increased suspicion and potential retaliatory cyber operations between the US, Russia, and China.
- Security / Counter-Terrorism: Heightened threat environment due to potential misuse by non-state actors and cybercriminals.
- Cyber / Information Space: Escalation in cyber arms race and proliferation of sophisticated exploit kits.
- Economic / Social: Potential economic impacts from compromised systems and increased cybersecurity costs for affected nations and companies.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of Coruna-related activities, strengthen international cyber cooperation, and issue advisories to mitigate potential threats.
- Medium-Term Posture (1–12 months): Develop resilience measures, invest in cyber defense capabilities, and pursue diplomatic engagements to address cyber norms.
- Scenario Outlook:
- Best: International cooperation leads to effective mitigation and attribution, reducing the exploit’s impact.
- Worst: Escalation of cyber conflicts and widespread exploitation of Coruna by malicious actors.
- Most-Likely: Continued use of Coruna by diverse actors, with periodic attribution debates and incremental improvements in defenses.
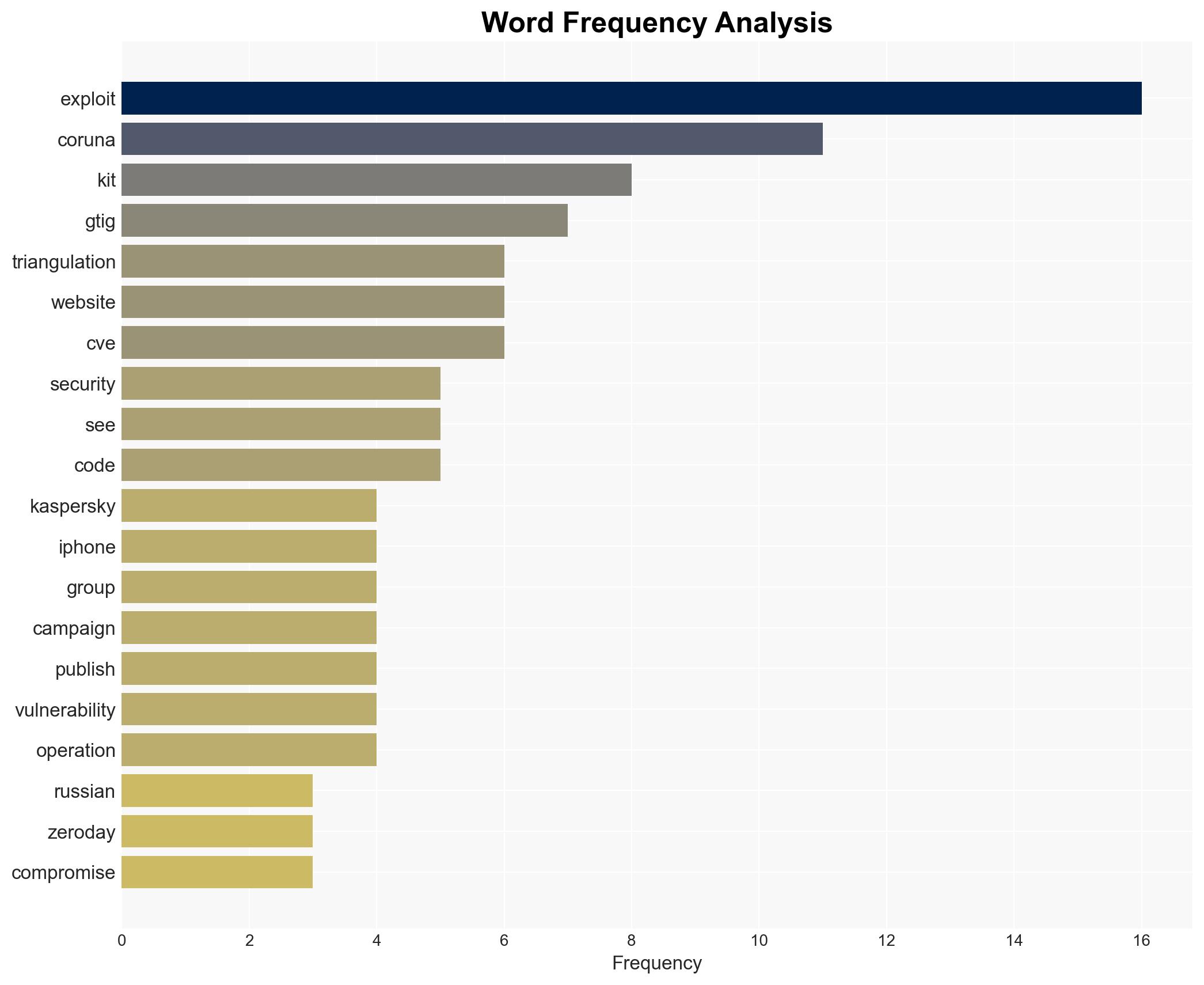
6. Key Individuals and Entities
- Google Threat Intelligence Group (GTIG)
- Kaspersky
- Rocky Cole, iVerify
- Boris Larin, Kaspersky GReAT
- National Security Agency (NSA)
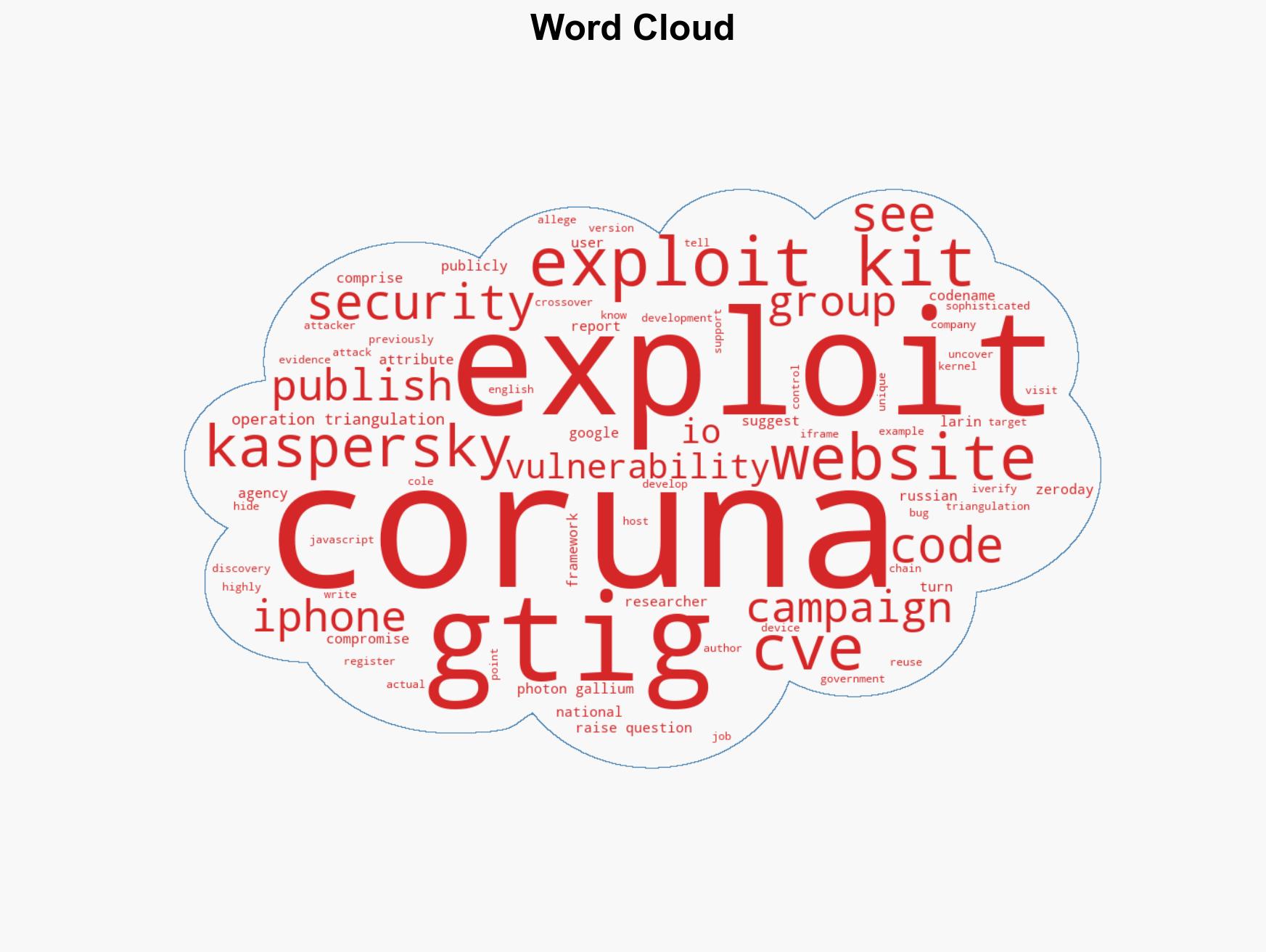
7. Thematic Tags
cybersecurity, cyber-espionage, state-sponsored hacking, zero-day market, international relations, cyber defense, information security
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us