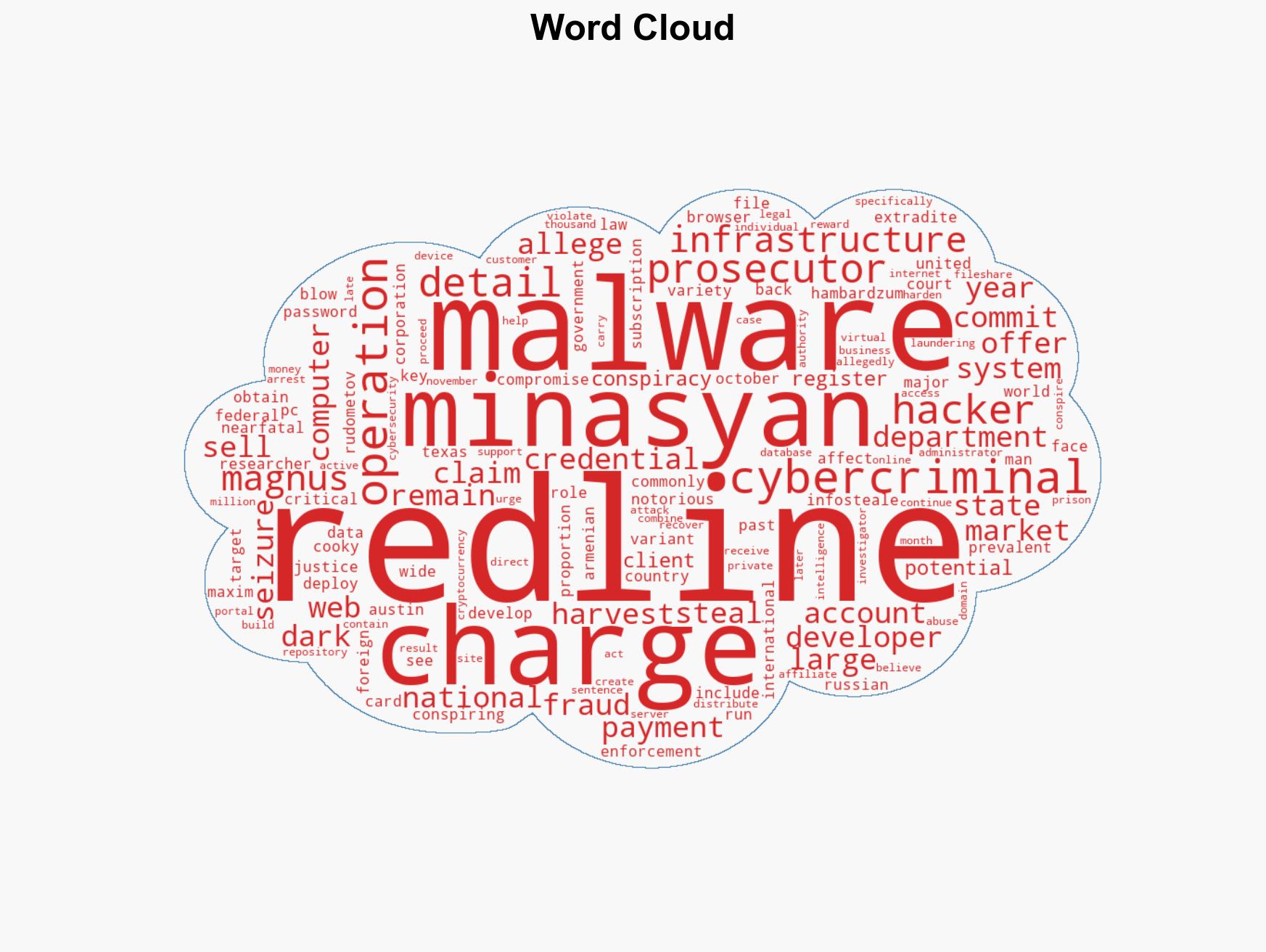
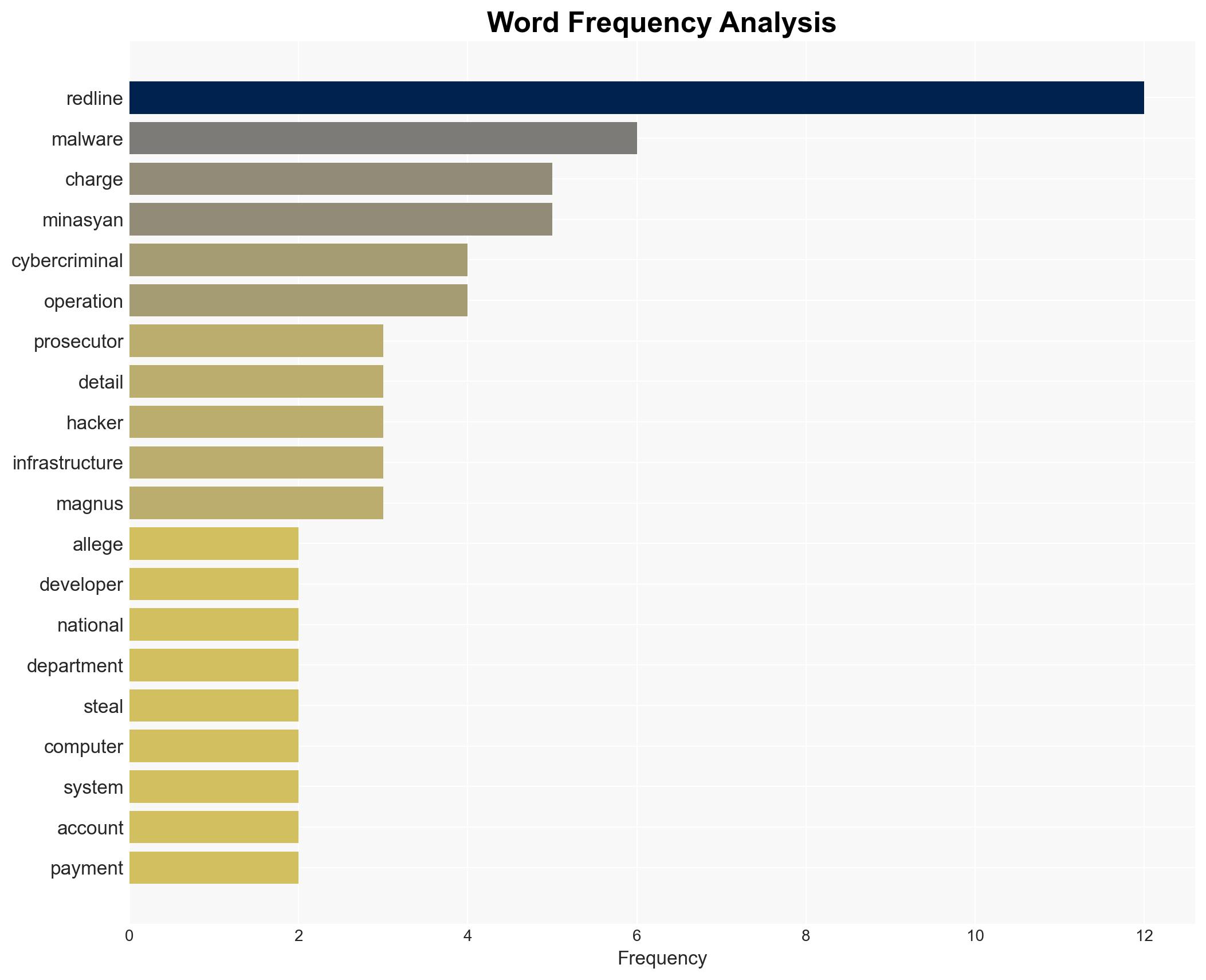
Key RedLine malware developer extradited to face charges in the U.S.
Published on: 2026-04-01
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: Alleged RedLine malware developer extradited to United States
1. BLUF (Bottom Line Up Front)
The extradition of Hambardzum Minasyan to the United States marks a significant step in the international effort to dismantle the RedLine malware network. This development is likely to disrupt ongoing cybercriminal activities associated with RedLine, though the malware remains operational. The arrest could lead to further insights into the network’s operations and collaborators. Overall confidence in these judgments is moderate due to existing information gaps regarding the full extent of the network.
2. Competing Hypotheses
- Hypothesis A: Minasyan’s arrest will significantly disrupt the RedLine malware network, leading to a decline in its operations. This is supported by the seizure of infrastructure and the arrest of key figures. However, the continued use of RedLine suggests resilient operational capabilities.
- Hypothesis B: The arrest will have limited impact on RedLine’s operations due to the decentralized nature of cybercriminal networks and the potential for other developers to continue its operations. The fact that RedLine is still active supports this hypothesis.
- Assessment: Hypothesis B is currently better supported, as RedLine remains active despite recent law enforcement actions. Indicators such as the emergence of new developers or continued high-volume data theft could further support this judgment.
3. Key Assumptions and Red Flags
- Assumptions: Minasyan played a central role in RedLine’s operations; law enforcement actions will deter other cybercriminals; the infrastructure seizure significantly impacted RedLine’s capabilities.
- Information Gaps: The full extent of Minasyan’s network and collaborators; the current operational status of RedLine; the identity and roles of other key figures involved.
- Bias & Deception Risks: Potential over-reliance on law enforcement sources; confirmation bias towards the effectiveness of international operations; possibility of misinformation from cybercriminals to mislead investigators.
4. Implications and Strategic Risks
This development could lead to increased international collaboration against cybercrime, but also provoke adaptive responses from cybercriminals. The geopolitical context may influence the willingness of certain states to cooperate fully.
- Political / Geopolitical: Potential strain on US-Armenia relations if perceived as targeting Armenian nationals; increased pressure on Russia to extradite cybercriminals.
- Security / Counter-Terrorism: Possible short-term reduction in RedLine-related threats; however, cybercriminals may shift tactics or targets.
- Cyber / Information Space: Continued threat from RedLine; potential for copycat malware or new variants to emerge.
- Economic / Social: Ongoing risk to businesses and individuals from data theft; potential economic impact from compromised systems.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Enhance monitoring of RedLine activity; engage with international partners to track and disrupt remaining network elements.
- Medium-Term Posture (1–12 months): Strengthen cybersecurity frameworks; develop partnerships with private sector for intelligence sharing; invest in cyber defense capabilities.
- Scenario Outlook:
- Best: Successful dismantling of RedLine network, leading to decreased cyber threats.
- Worst: Emergence of more sophisticated malware variants, increasing cyber risks.
- Most-Likely: Continued RedLine activity with periodic disruptions from law enforcement.
6. Key Individuals and Entities
- Hambardzum Minasyan – Alleged RedLine developer
- Maxim Rudometov – Alleged RedLine developer, at large
- US Department of Justice
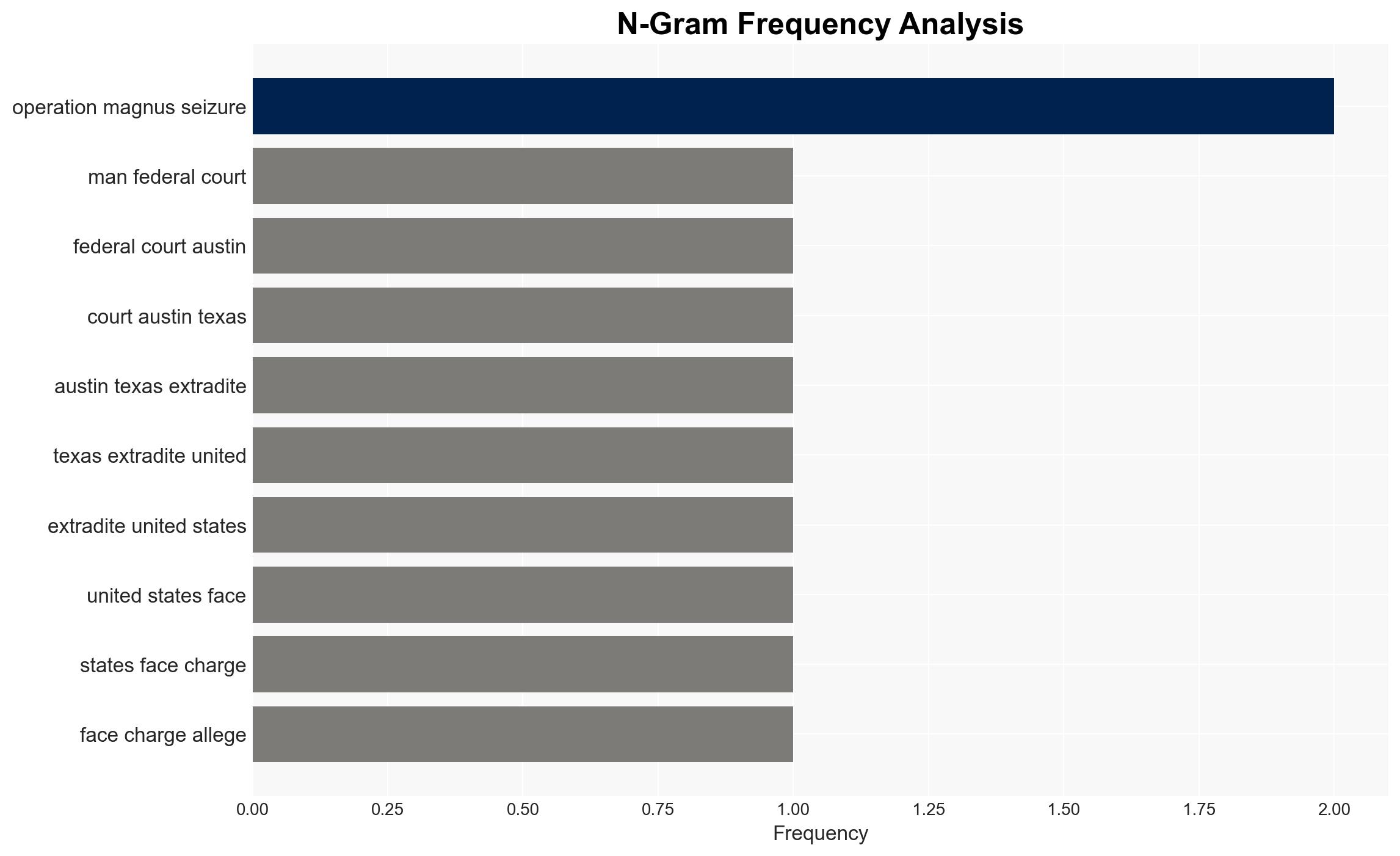
- International law enforcement agencies involved in “Operation Magnus”
7. Thematic Tags
cybersecurity, cybercrime, malware, international cooperation, law enforcement, RedLine, extradition
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us