LexisNexis acknowledges data breach as hackers release 2GB of legacy files from compromised servers
Published on: 2026-03-03
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: LexisNexis confirms data breach as hackers leak stolen files
1. BLUF (Bottom Line Up Front)
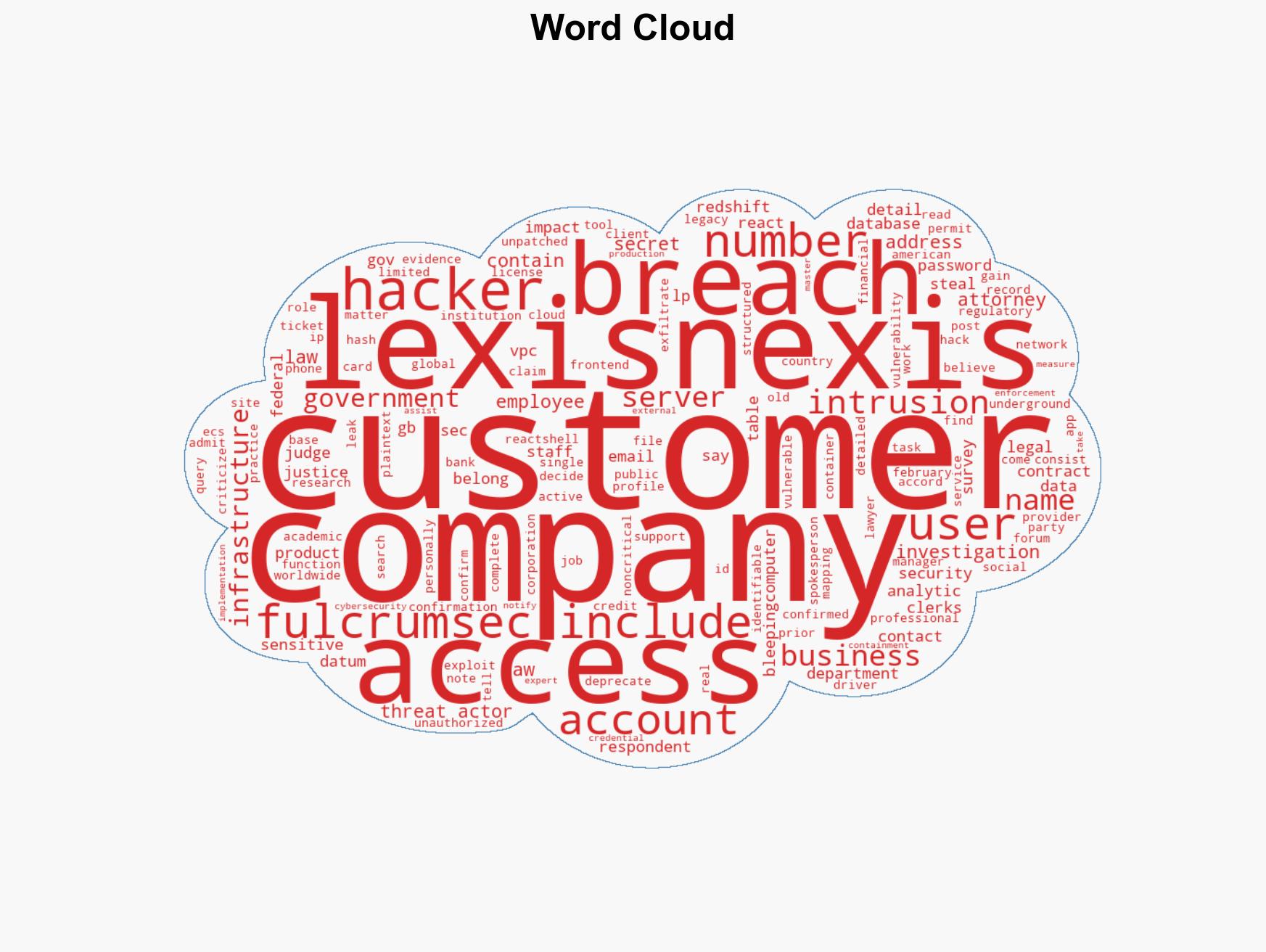
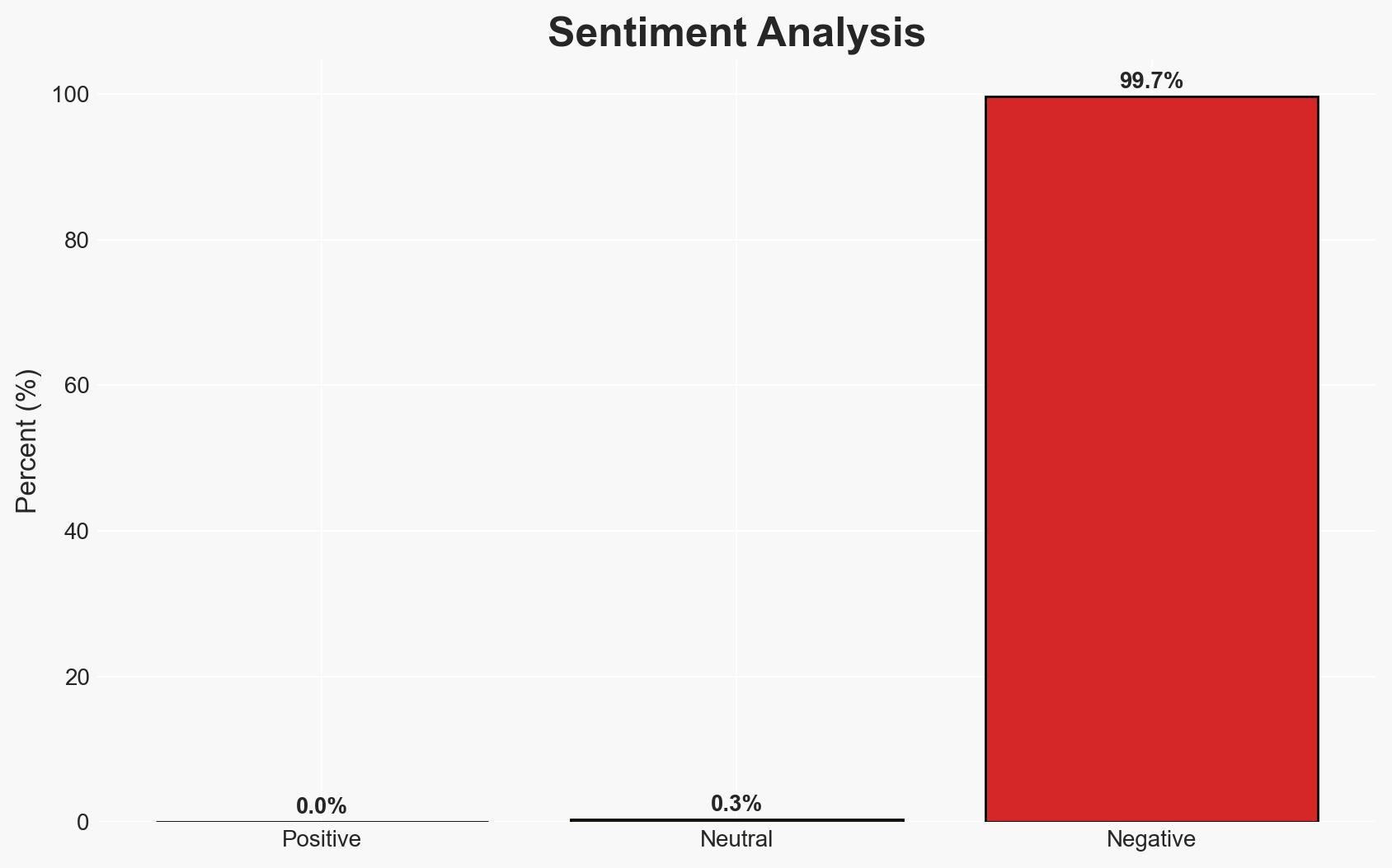
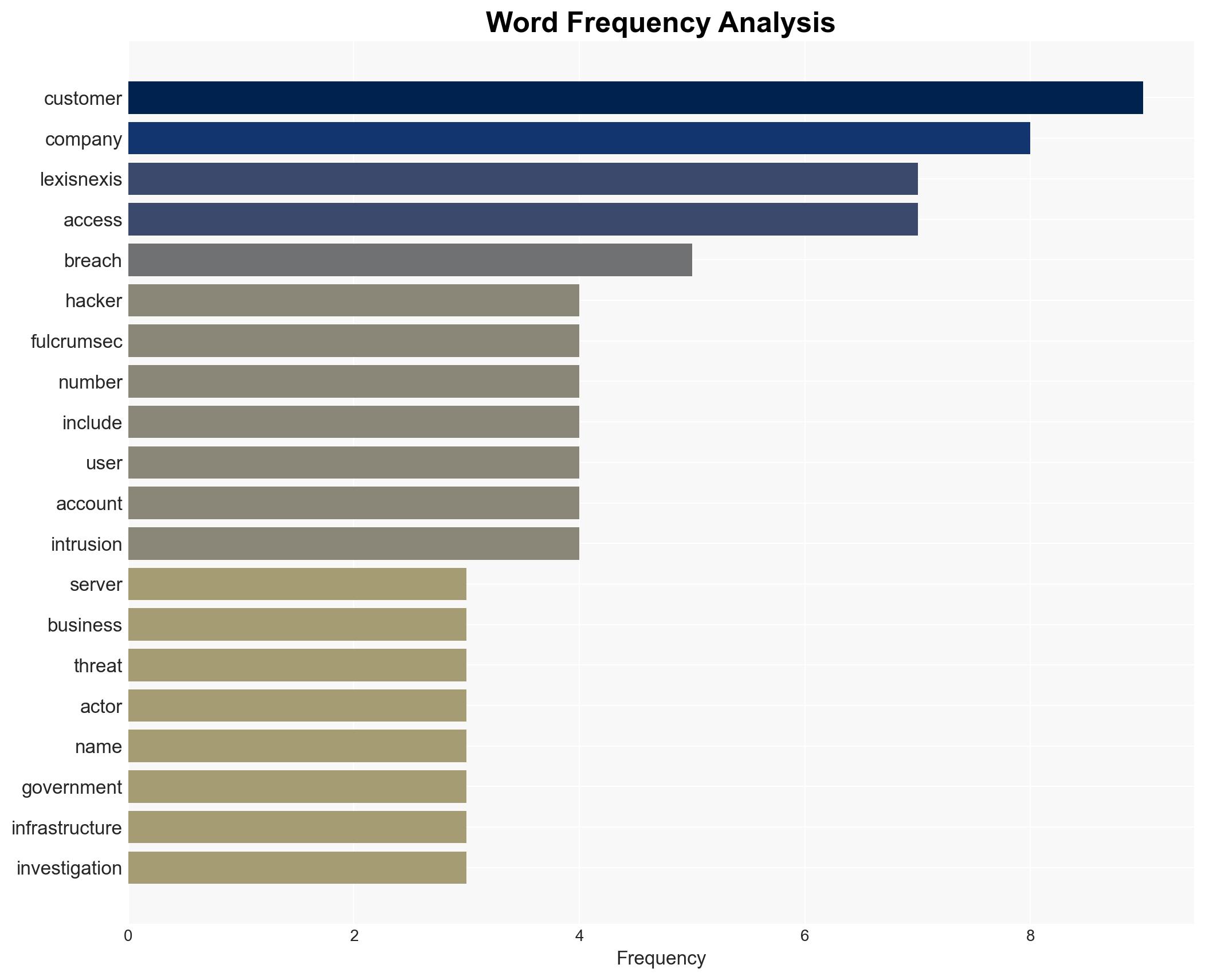
The LexisNexis data breach, attributed to the hacker group FulcrumSec, exposed legacy data from the company’s AWS infrastructure, affecting a limited number of users, including U.S. government employees. The breach exploited a known vulnerability, React2Shell, in an unpatched application. While the breach appears contained, the exposure of government-related data presents moderate security risks. Overall confidence in this assessment is moderate due to incomplete information on the breach’s full scope and potential impacts.
2. Competing Hypotheses
- Hypothesis A: The breach was opportunistic, targeting outdated systems with known vulnerabilities. Supporting evidence includes the use of a known vulnerability and the focus on legacy data. Contradicting evidence includes the specific targeting of .gov email addresses, suggesting a more strategic intent.
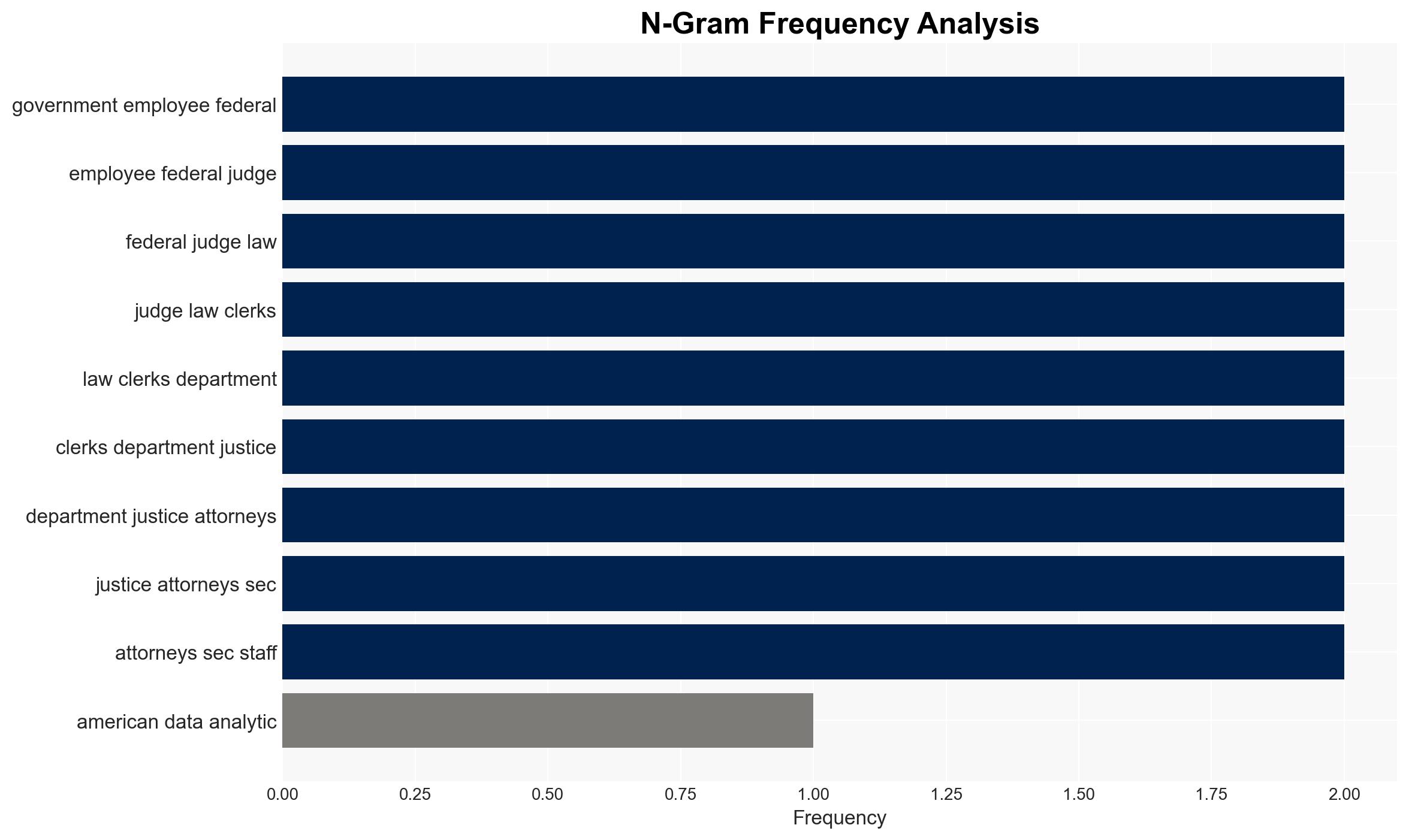
- Hypothesis B: The breach was a targeted operation aimed at gathering intelligence on U.S. government entities. Supporting evidence includes the specific mention of .gov email addresses and the detailed mapping of the AWS infrastructure. Contradicting evidence is the lack of sensitive personal or financial data in the stolen files.
- Assessment: Hypothesis B is currently better supported due to the targeted nature of the data exfiltrated, particularly involving government-related accounts. Indicators that could shift this judgment include further evidence of data misuse or additional breaches targeting similar entities.
3. Key Assumptions and Red Flags
- Assumptions: The breach is fully contained; no sensitive data was accessed; FulcrumSec’s claims are accurate.
- Information Gaps: Full extent of data accessed, potential secondary breaches, and the exact timeline of the breach.
- Bias & Deception Risks: Potential bias in LexisNexis’s public statements minimizing breach impact; FulcrumSec’s motivations and claims may be exaggerated or deceptive.
4. Implications and Strategic Risks
This breach could lead to increased scrutiny on data security practices within companies handling sensitive information, especially those serving government clients. The incident may also prompt regulatory reviews and policy changes concerning data protection.
- Political / Geopolitical: Potential diplomatic tensions if foreign actors are implicated or if government data is misused.
- Security / Counter-Terrorism: Increased risk of targeted phishing or cyber-espionage against exposed individuals.
- Cyber / Information Space: Highlighting vulnerabilities in cloud infrastructure and the need for robust patch management.
- Economic / Social: Possible reputational damage to LexisNexis, impacting client trust and market position.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a comprehensive security audit of LexisNexis systems, enhance monitoring for misuse of exposed data, and engage with affected government entities for damage assessment.
- Medium-Term Posture (1–12 months): Strengthen partnerships with cybersecurity firms, invest in advanced threat detection capabilities, and develop a robust incident response plan.
- Scenario Outlook:
- Best Case: Breach contained with no significant misuse of data, leading to improved security protocols.
- Worst Case: Data used in targeted attacks against government entities, leading to broader security implications.
- Most Likely: Limited misuse of data with increased regulatory scrutiny on data protection practices.
6. Key Individuals and Entities
- LexisNexis Legal & Professional
- FulcrumSec (threat actor group)
- U.S. government employees (affected users)
- Federal judges and law clerks (affected users)
- U.S. Department of Justice attorneys (affected users)
- U.S. SEC staff (affected users)
7. Thematic Tags
cybersecurity, data breach, government data, cloud security, vulnerability exploitation, information security, threat actors
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
- Network Influence Mapping: Map influence relationships to assess actor impact.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us