LexisNexis reports data breach in Legal & Professional division, affecting limited customer records
Published on: 2026-03-04
AI-powered OSINT brief from verified open sources. Automated NLP signal extraction with human verification. See our Methodology and Why WorldWideWatchers.
Intelligence Report: LexisNexis confirms data breach at Legal Professional arm some customer records affected
1. BLUF (Bottom Line Up Front)
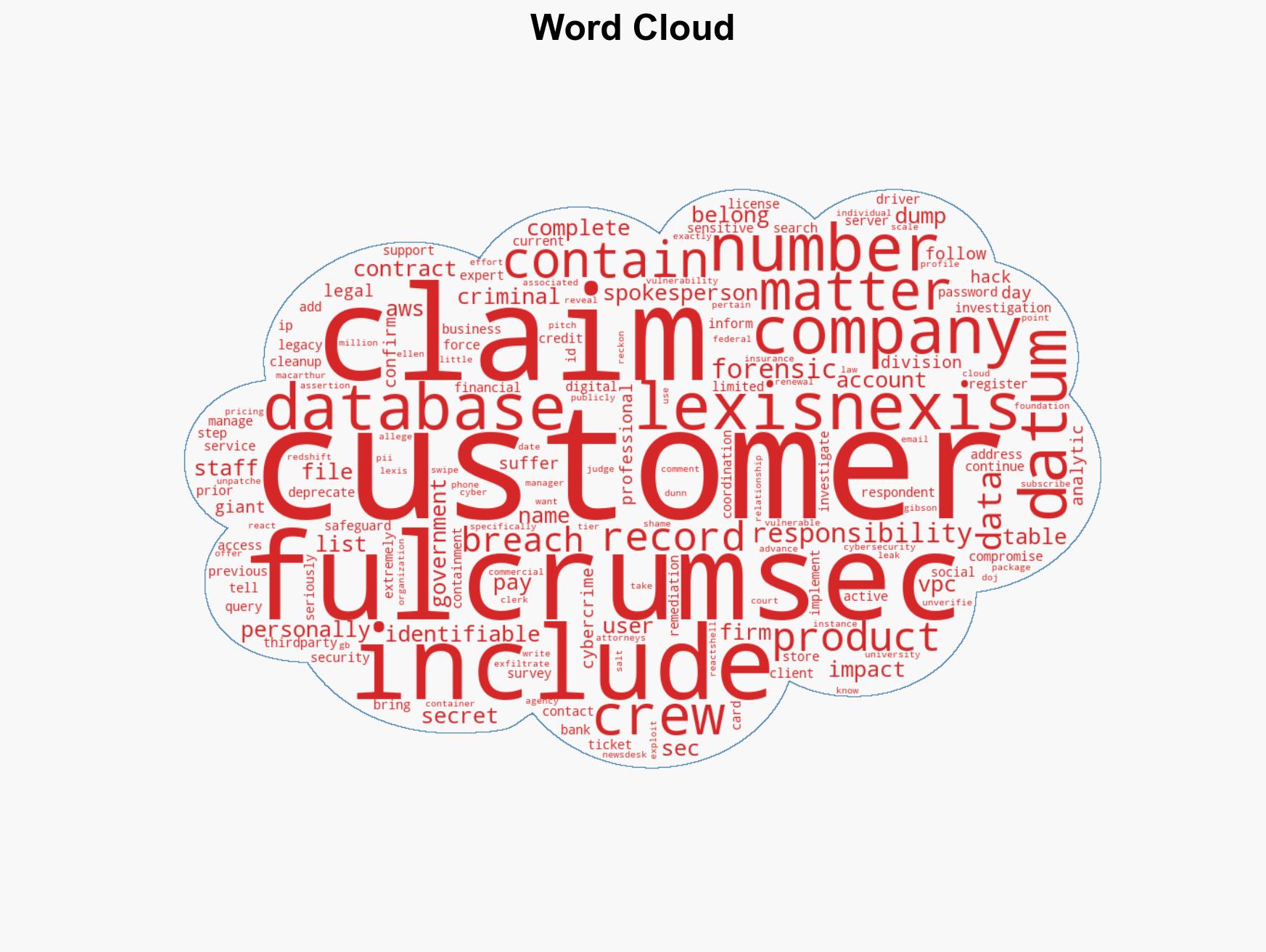
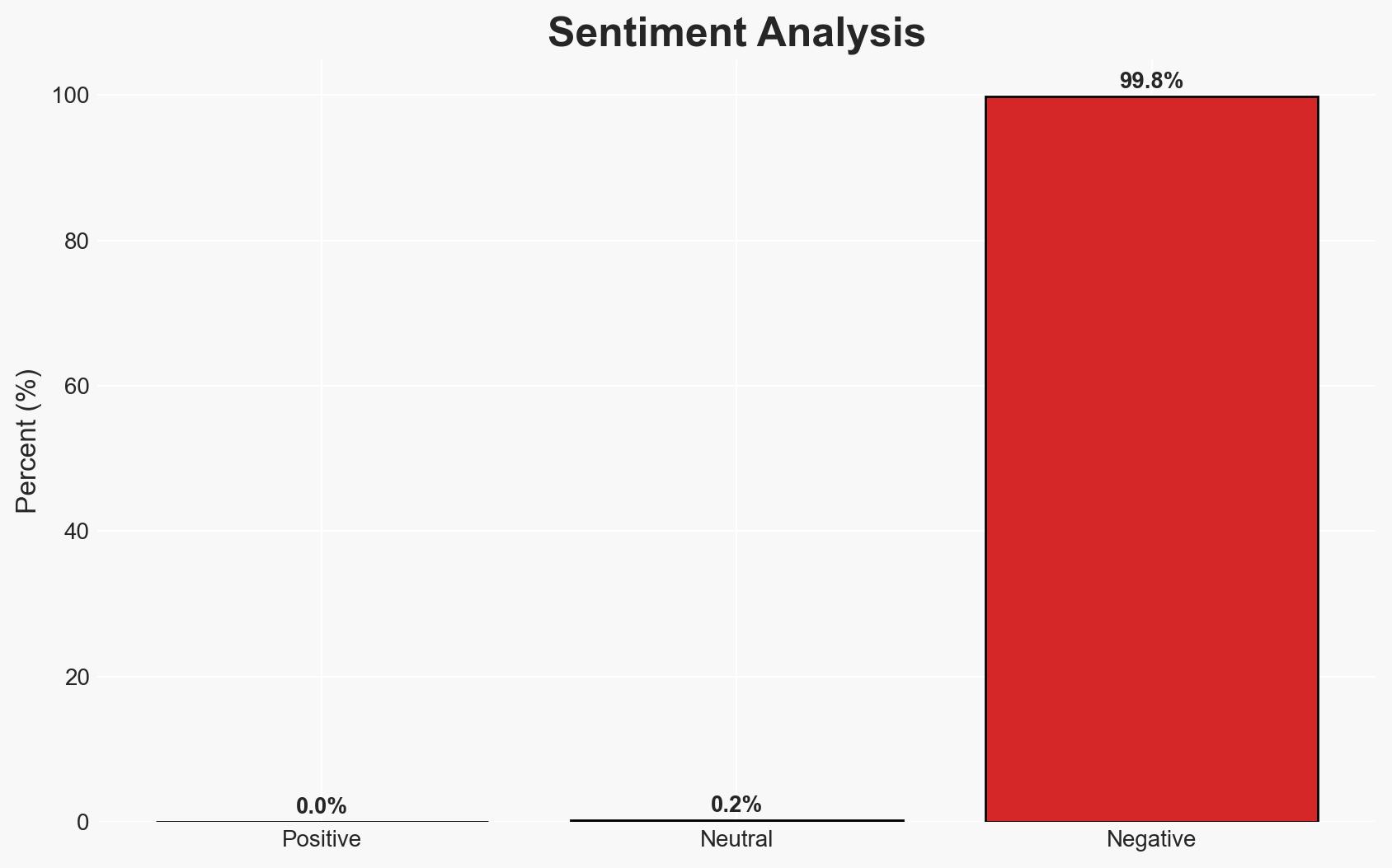
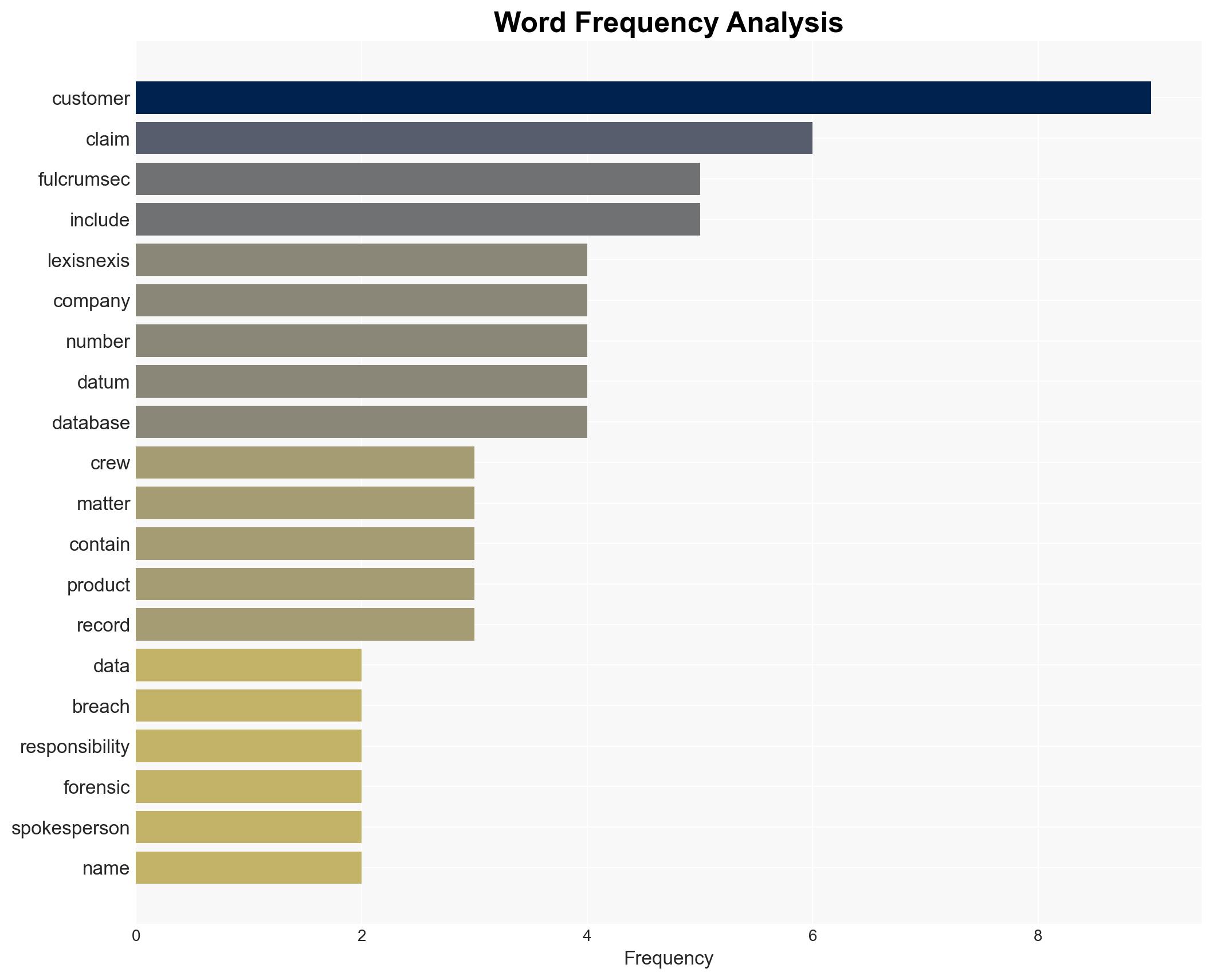
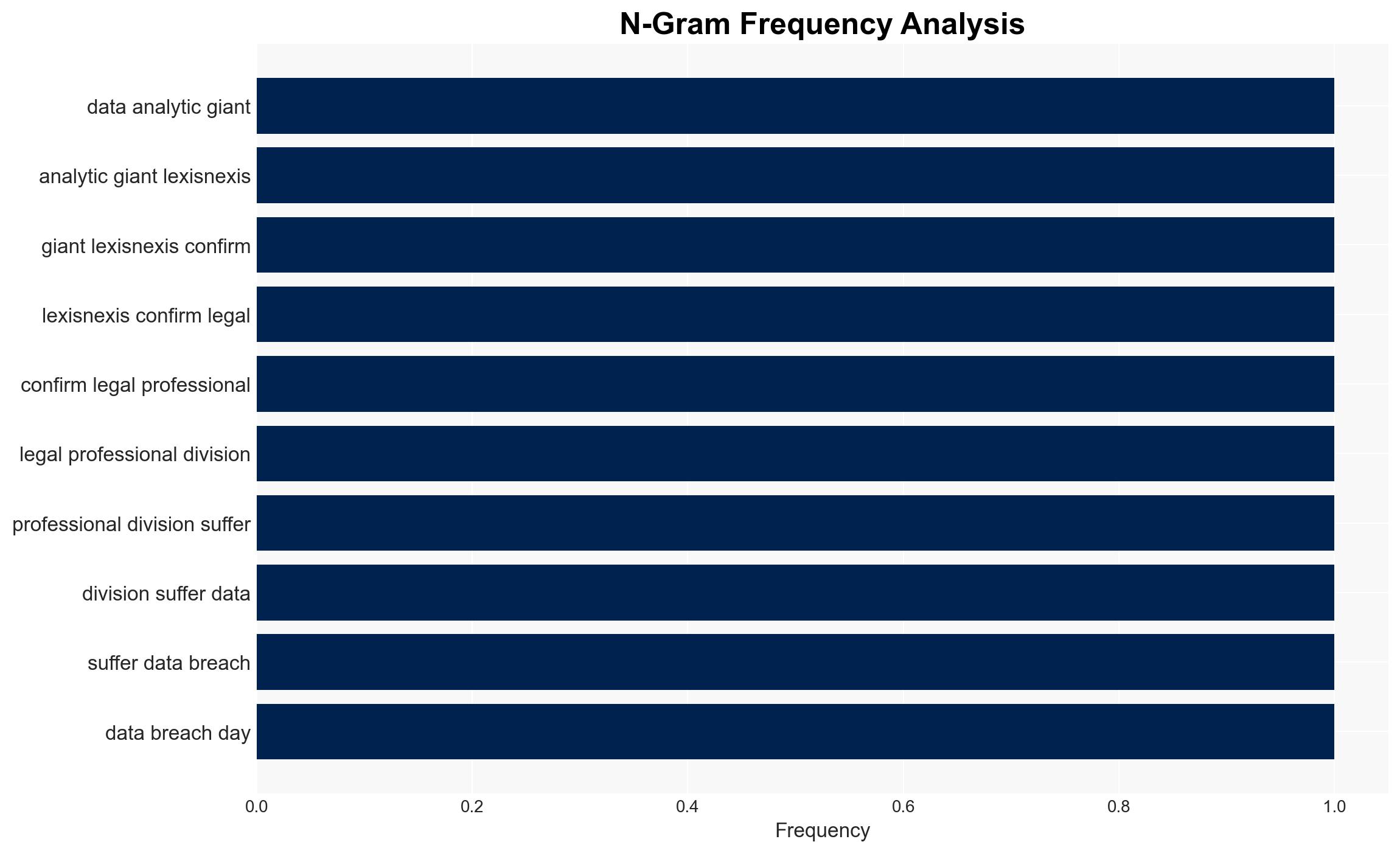
The LexisNexis Legal & Professional division experienced a data breach, reportedly involving legacy data and some customer records. The breach was claimed by the Fulcrumsec cybercrime group, which alleges significant data exfiltration. Current evidence suggests the breach is contained, with no critical sensitive information compromised. Overall confidence in this assessment is moderate.
2. Competing Hypotheses
- Hypothesis A: The breach was limited in scope, affecting only legacy data with minimal impact on sensitive information. LexisNexis’s containment efforts were effective, and the breach does not pose a significant ongoing threat. Supporting evidence includes LexisNexis’s statement on the limited nature of the breach and the types of data affected. Key uncertainties include the full extent of data accessed and the accuracy of Fulcrumsec’s claims.
- Hypothesis B: The breach was more extensive than reported, potentially involving sensitive information and affecting current operational data. Fulcrumsec’s claims of accessing significant data, including government-related profiles, suggest a larger impact. Contradicting evidence includes the lack of verification of Fulcrumsec’s claims and LexisNexis’s assertion of limited data exposure.
- Assessment: Hypothesis A is currently better supported due to LexisNexis’s detailed response and lack of verified evidence supporting Fulcrumsec’s broader claims. Indicators that could shift this judgment include independent verification of Fulcrumsec’s data claims or new evidence of broader data exposure.
3. Key Assumptions and Red Flags
- Assumptions: LexisNexis’s containment measures are effective; Fulcrumsec’s claims are exaggerated; the breach does not involve critical sensitive data.
- Information Gaps: Verification of Fulcrumsec’s claims, full scope of data accessed, and potential impacts on affected individuals and entities.
- Bias & Deception Risks: Potential bias in LexisNexis’s public statements to minimize reputational damage; possible exaggeration by Fulcrumsec to enhance their perceived capabilities.
4. Implications and Strategic Risks
This development could affect LexisNexis’s reputation and customer trust, with potential regulatory scrutiny. It may also embolden cybercriminal groups if Fulcrumsec’s claims are perceived as credible.
- Political / Geopolitical: Increased scrutiny on data protection practices within legal and government sectors.
- Security / Counter-Terrorism: Potential targeting of legal and governmental data by other cybercriminal groups.
- Cyber / Information Space: Highlighting vulnerabilities in cloud services and the need for robust cybersecurity measures.
- Economic / Social: Potential financial impact on LexisNexis due to loss of customer trust and possible legal actions.
5. Recommendations and Outlook
- Immediate Actions (0–30 days): Conduct a thorough independent audit of the breach; enhance monitoring of affected systems; engage with affected customers transparently.
- Medium-Term Posture (1–12 months): Strengthen cybersecurity protocols; develop partnerships with cybersecurity firms; enhance data protection training for staff.
- Scenario Outlook: Best: Breach contained with minimal impact. Worst: Broader data exposure confirmed, leading to significant reputational and financial damage. Most-Likely: Limited breach with moderate reputational impact, prompting improved cybersecurity measures.
6. Key Individuals and Entities
- LexisNexis Legal & Professional division
- Fulcrumsec cybercrime group
- Not clearly identifiable from open sources in this snippet for specific individuals
7. Thematic Tags
cybersecurity, data breach, legal sector, cloud vulnerabilities, cybercrime
Structured Analytic Techniques Applied
- Adversarial Threat Simulation: Model and simulate actions of cyber adversaries to anticipate vulnerabilities and improve resilience.
- Indicators Development: Detect and monitor behavioral or technical anomalies across systems for early threat detection.
- Bayesian Scenario Modeling: Quantify uncertainty and predict cyberattack pathways using probabilistic inference.
Explore more:
Cybersecurity Briefs ·
Daily Summary ·
Support us