Linux 615 Device Mapper Brings Inline Crypto Passthrough For DM-Stripe – Phoronix
Published on: 2025-04-03
Intelligence Report: Linux 615 Device Mapper Brings Inline Crypto Passthrough For DM-Stripe – Phoronix
1. BLUF (Bottom Line Up Front)
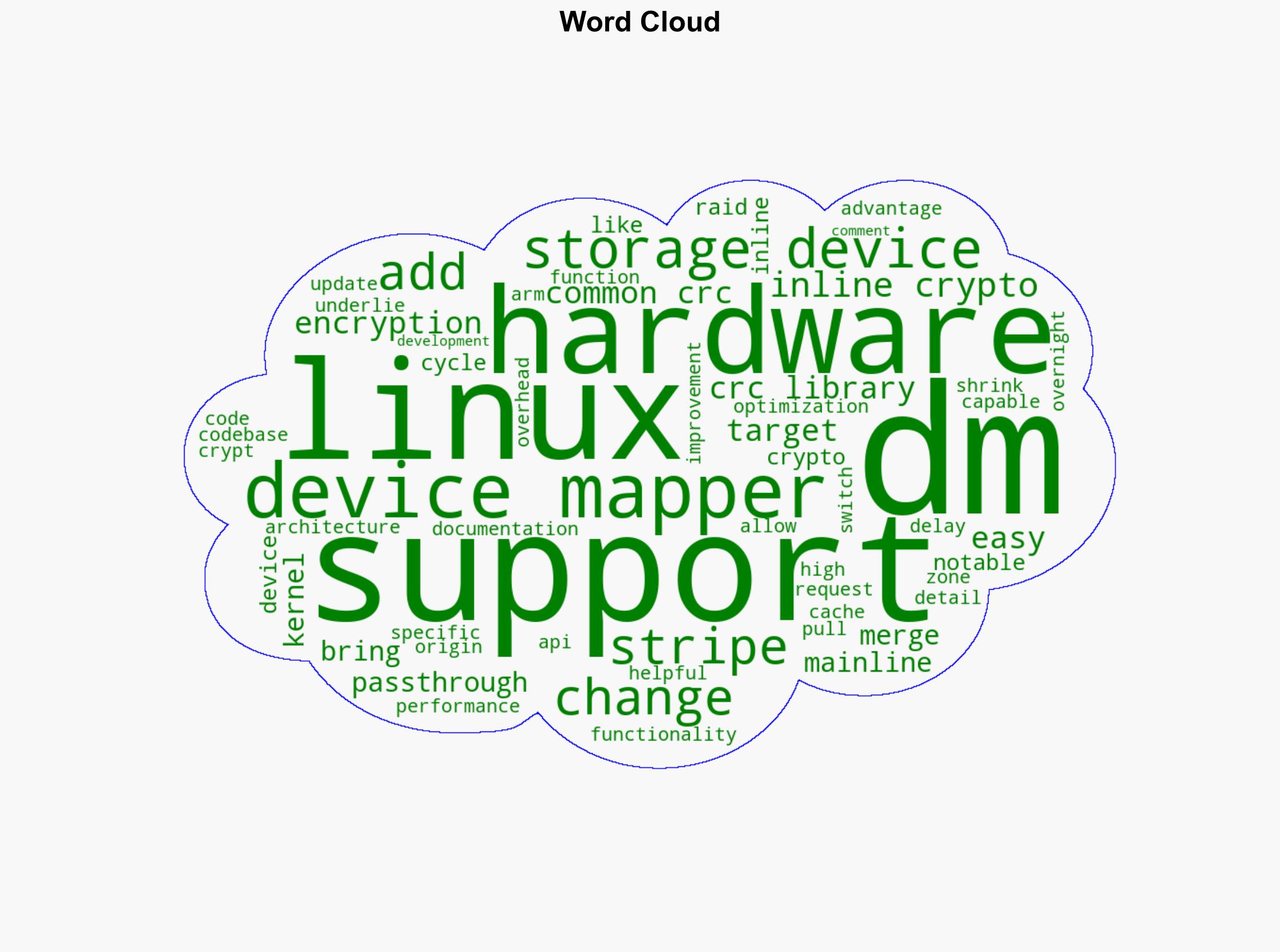
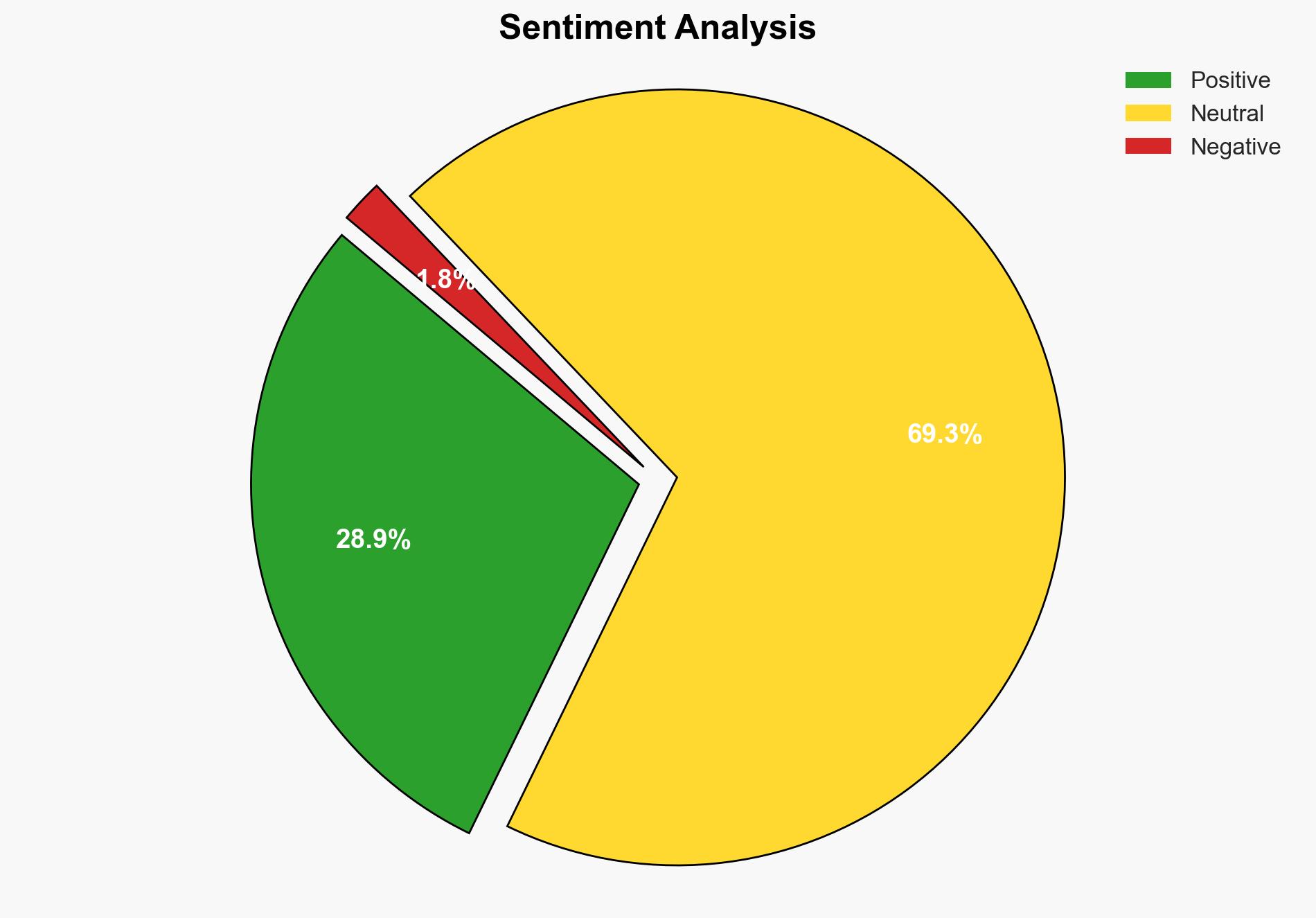
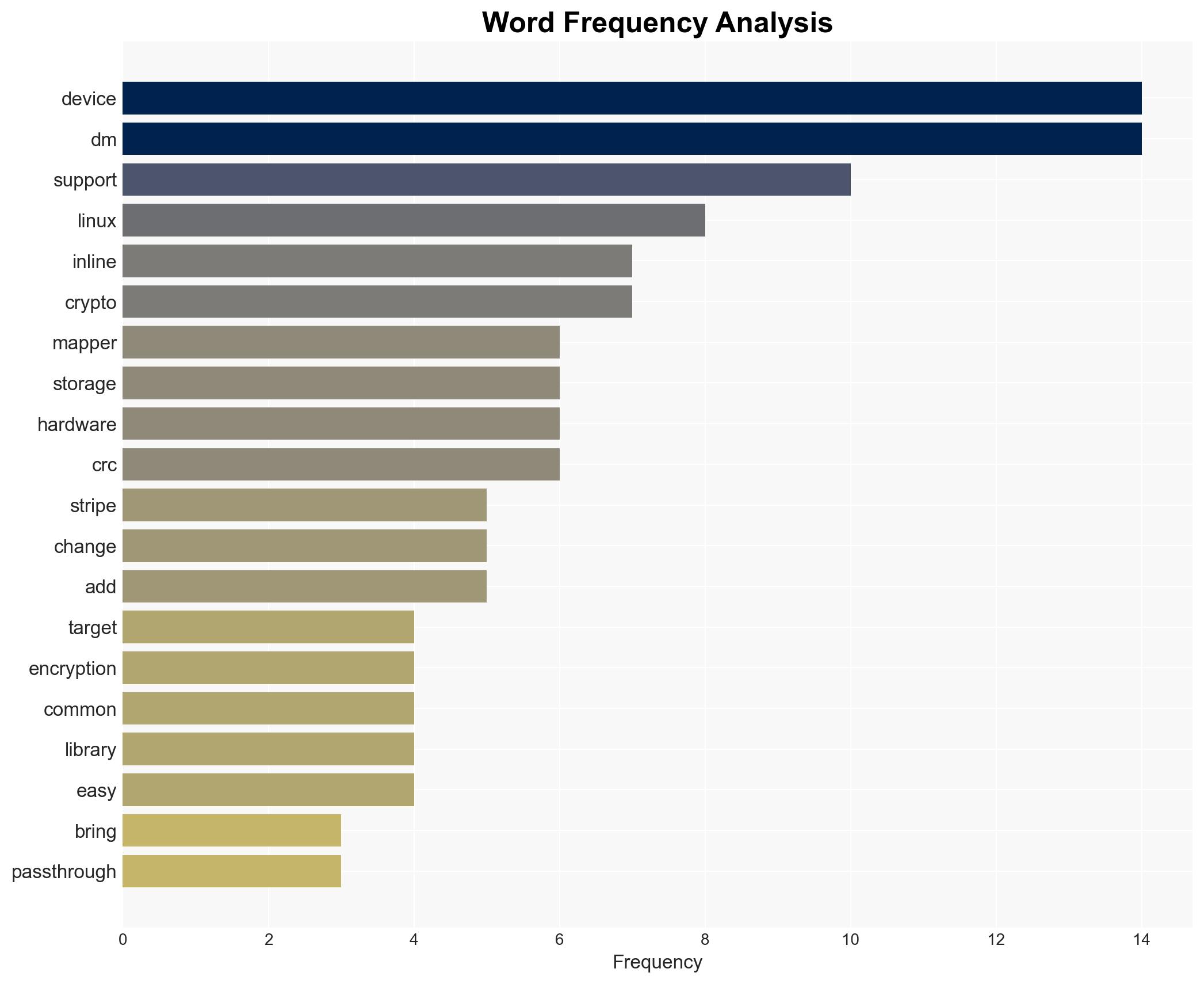
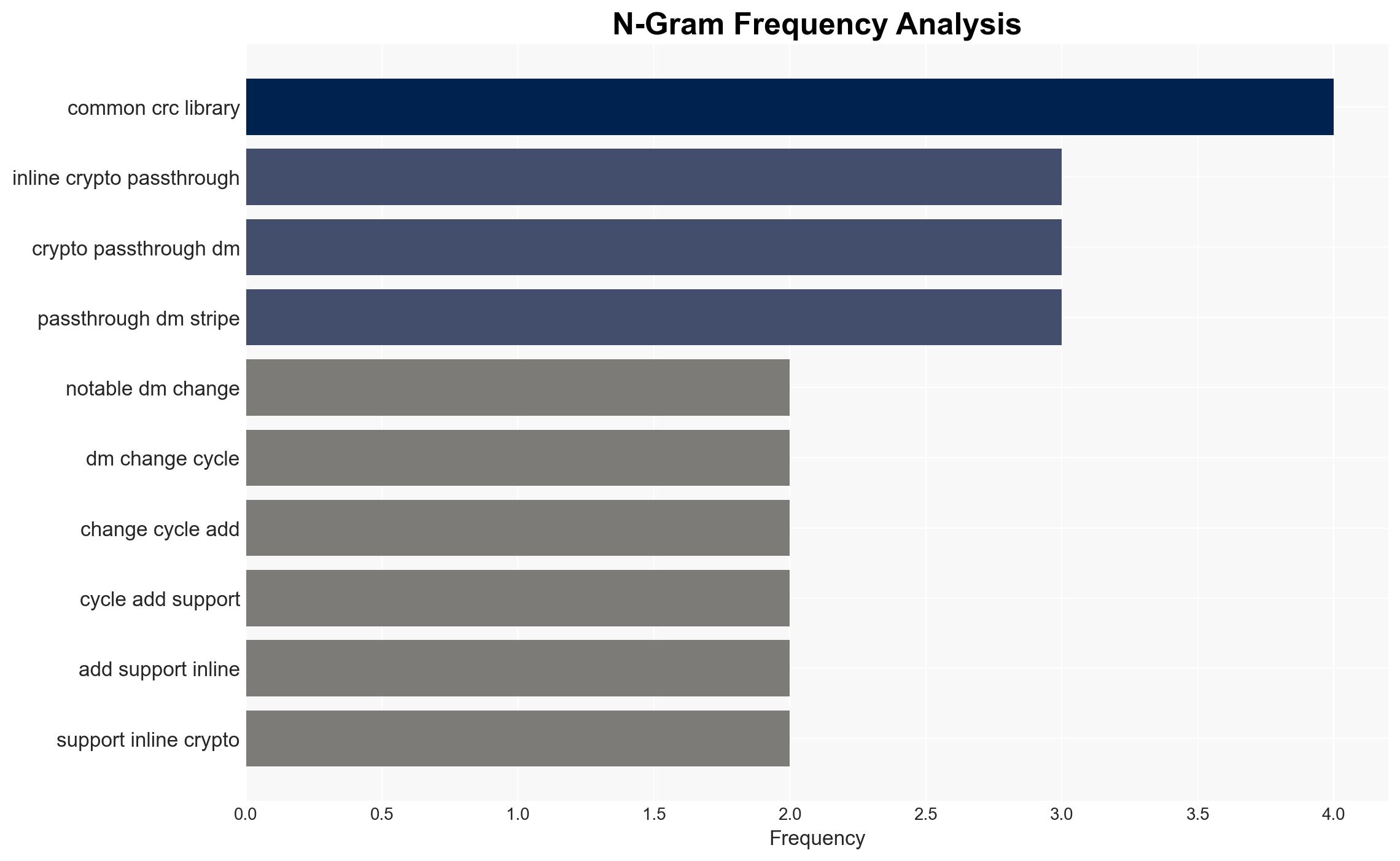
The latest update to the Linux kernel introduces a significant enhancement to the Device Mapper, specifically with the addition of inline crypto passthrough for DM-Stripe. This development is poised to enhance storage device security and performance, particularly benefiting systems with ARM hardware that support inline encryption. The integration of a common CRC library further optimizes performance by reducing overhead. These changes are expected to improve the efficiency and security of storage solutions, making them more robust against potential cyber threats.
2. Detailed Analysis
The following structured analytic techniques have been applied for this analysis:
General Analysis
The integration of inline crypto passthrough into the DM-Stripe component of the Linux Device Mapper represents a strategic enhancement in data security and system performance. By enabling hardware encryption directly on storage devices, this update leverages ARM hardware capabilities to provide a more secure data environment. The switch to a common CRC library facilitates architecture-specific optimizations, which can significantly reduce computational overhead. This development aligns with broader trends in cybersecurity, emphasizing the importance of encryption and efficient data processing.
3. Implications and Strategic Risks
The introduction of inline crypto passthrough in the Linux kernel has several implications:
- National Security: Enhanced encryption capabilities can protect sensitive data from unauthorized access, bolstering national cybersecurity defenses.
- Regional Stability: As more systems adopt these security measures, the risk of data breaches and cyber attacks could decrease, contributing to regional stability.
- Economic Interests: Improved data security and performance can lead to increased trust in digital infrastructure, potentially boosting economic growth in technology sectors.
4. Recommendations and Outlook
Recommendations:
- Encourage the adoption of the latest Linux kernel update across critical infrastructure to enhance data security.
- Invest in training for IT professionals to effectively implement and manage these new security features.
- Consider regulatory measures to mandate encryption standards for sensitive data storage.
Outlook:
Best-case scenario: Widespread adoption of the updated Linux kernel leads to a significant reduction in data breaches and cyber threats.
Worst-case scenario: Delays in adoption or implementation issues could limit the effectiveness of these security enhancements, leaving systems vulnerable.
Most likely outcome: Gradual integration of the new features will improve security and performance over time, with incremental benefits realized across sectors.
5. Key Individuals and Entities
The report does not mention specific individuals or organizations by name, focusing instead on the broader implications and strategic importance of the Linux kernel update.